本文仅限学习交流,请勿用于非法以及商业用途,由于时间和水平有限,文中错漏之处在所难免,敬请各位大佬多多批评指正。
目录:
一、线上买菜场景简述
二、风控在业务中的应用
三、产品整体框架
四、初始化分析
五、反爬签名流程
六、设备指纹分析
七、算法还原
八、总结
一、线上买菜场景简述
1、分析说明
1. 产品基本信息
产品名称:ppp买菜(匿称);
产品版本:5.25.0;
Slogan:30分钟送达,新鲜送得快;
所处行业:生鲜电商;
2. 设备环境
机型:iPhone 7;
系统:IOS 13.4;
工具: IDA7.6 Frida;
2、简单流程梳理
一次完整的线上买菜过程都经过了哪些环节呢?大致流程是从供应商送货到仓或到店,再由零售商售卖,最终到用户手里,这样便完成了一次买菜,如图1-1所示:
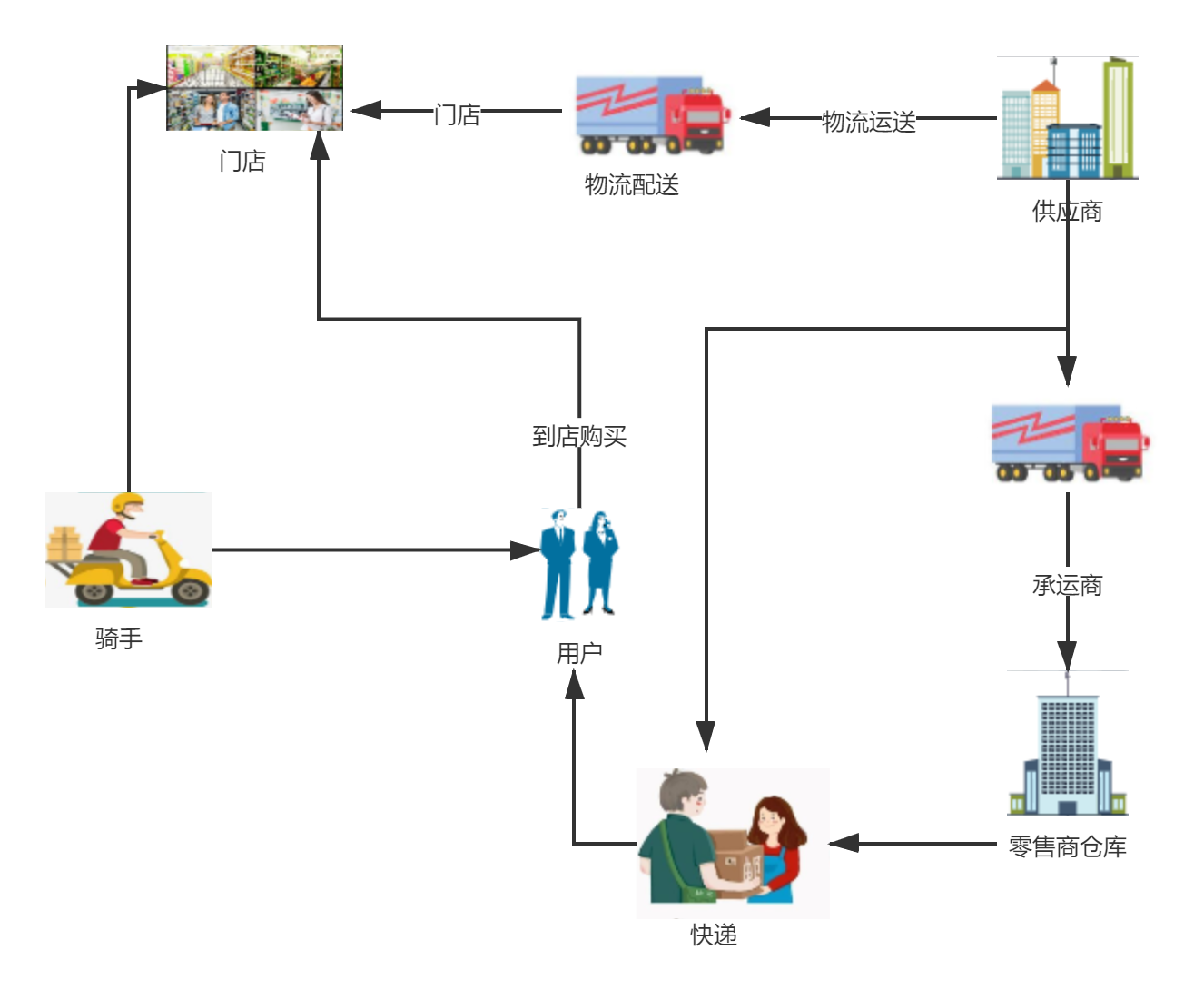
图1-1
上图的业务流程从供应商送货到仓或到店,再由零售商售卖,最终可以多种方式到用户手里,完成了一次买菜的过程。
二、反作弊风控在业务中的应用
1、APP推广拉新
还记得在2020年的下半年时候,当时生鲜电商的社区团购大战非常火爆,各种买菜APP蜂拥而入,砸钱、抢流量,你争我抢玩得不亦乐乎。
不夸张地说,我记得当时最常见的情形是,你随便在小区溜达一圈,就能碰见穿着各种颜色制服的地推工作人员,追赶着小哥哥小姐姐下载APP给送福利,下载完APP后注册登录APP买菜。
2、存在的风险
烧大把的钱把流量吸引过来,这个过程中会有黑灰产人员通过非法的技术手段,伪造新增用户并从中获利的行为,如果只是把流量吸引过来不考虑质量的话,会增加大量的企业无效成本。怎么识别出有效的流量与虚假流量,需要一个完善的风控体系与制定有效的策略找出高质量流量,然后把这些流量留下来。
接下来为了提高用户的购买频率,实现反复转化,就出现了各种红包、优惠券活动吸引用户提高打开APP频率与购买频率。这个环节中就会有各种薅羊毛的人群出现,同样需要完善的风控体系与制定有效的策略来最大程度地甄别风险。
活动流程大致如图2-1所示:
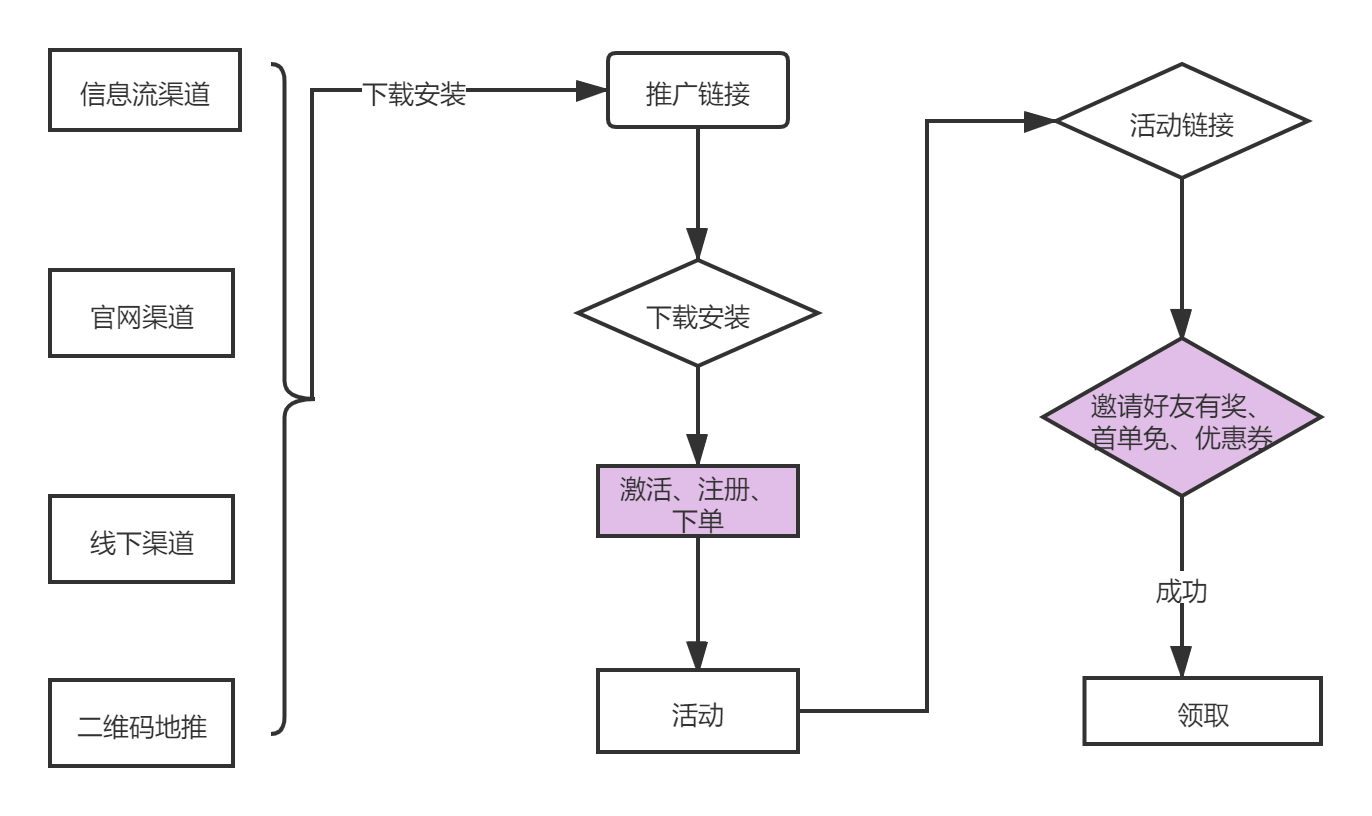
图2-1
三、产品整体框架
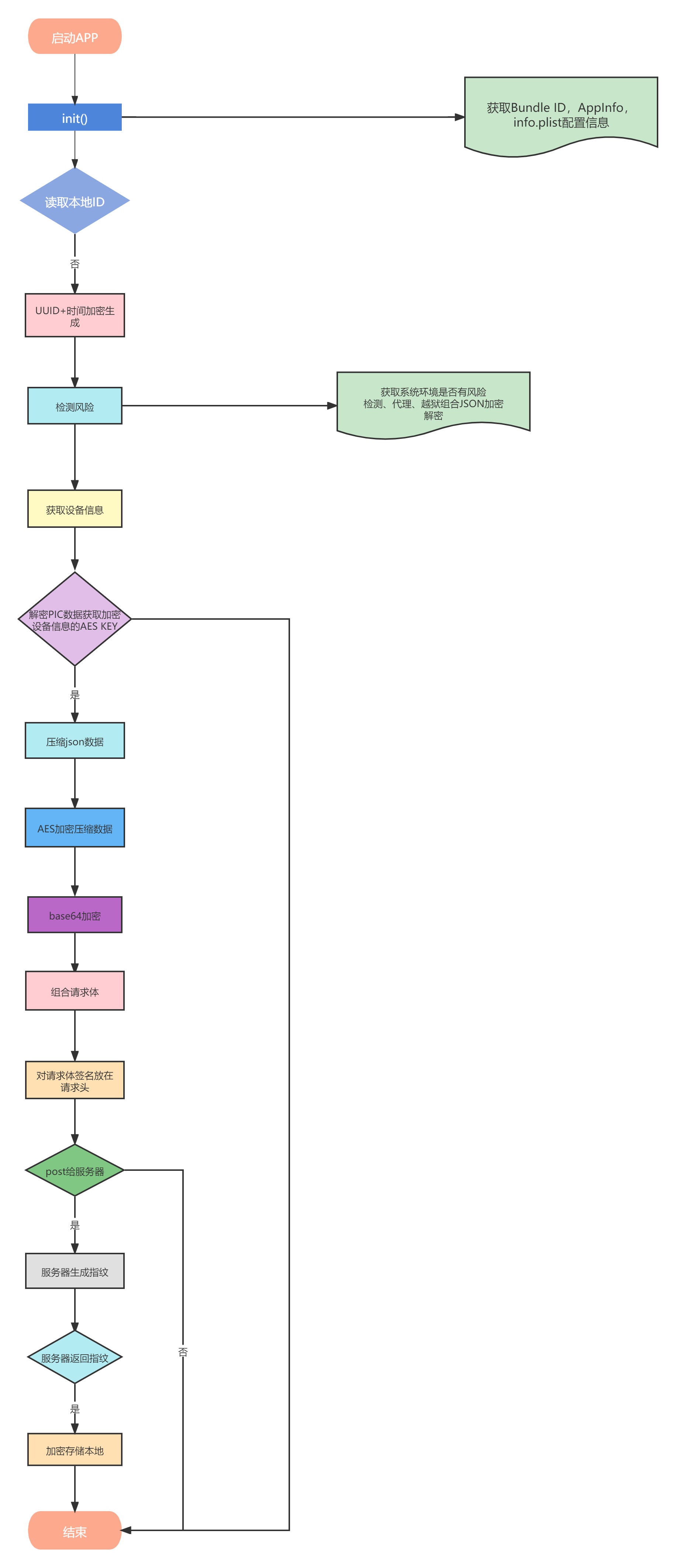
3.1、从初化到获取设备指纹整个框架如图3-1与3-2所示:
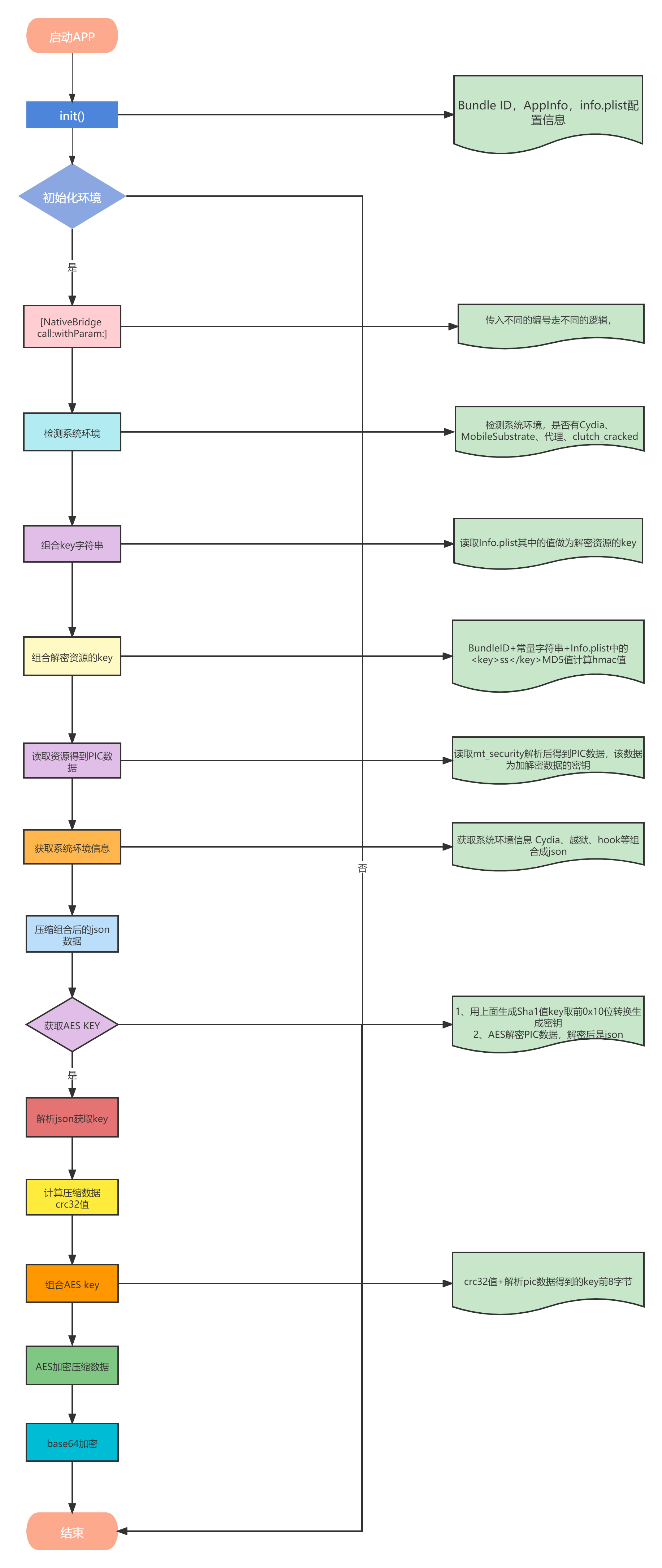
图3-1
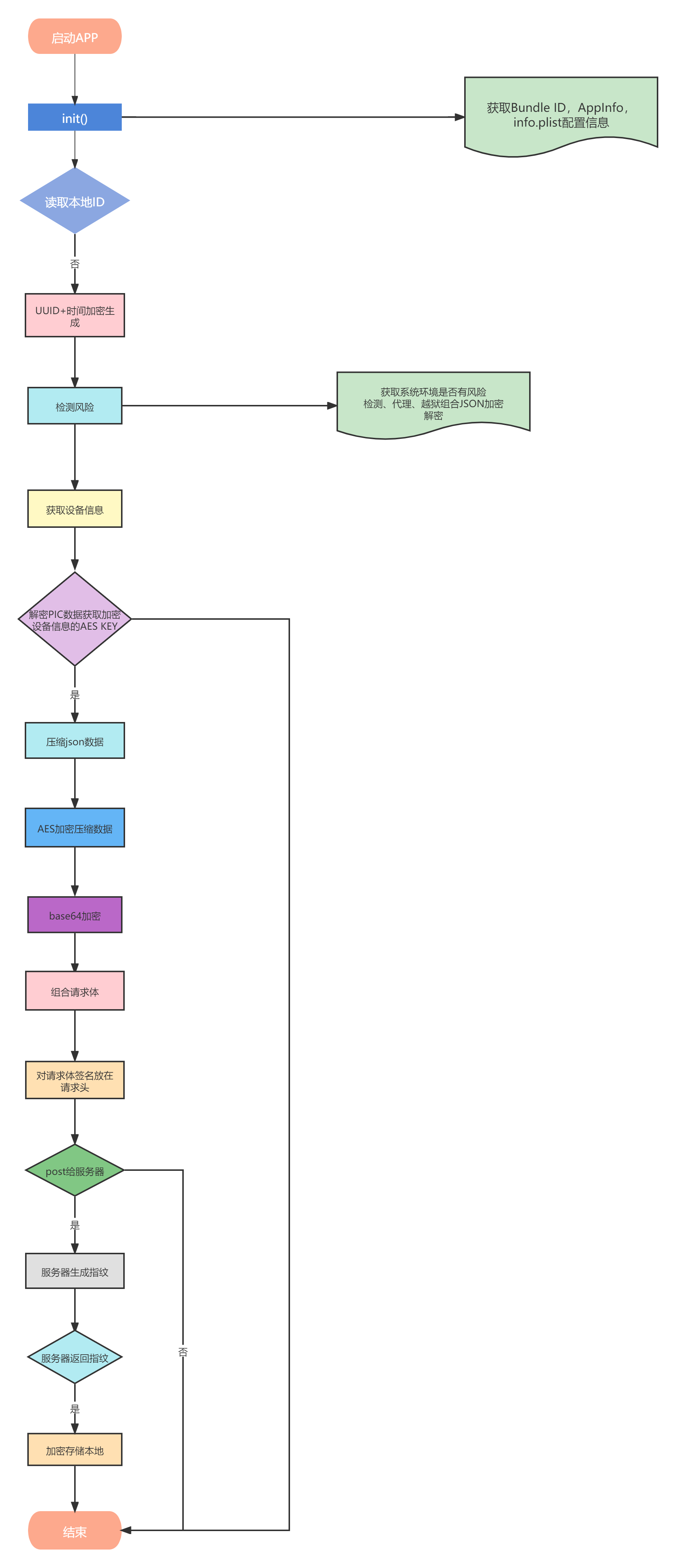
图3-2
下面将围绕框架进行详细分析与算法还原。
四、初始化分析
4.1、代码混淆
在正式进行代码分析之前还是很必要交代一下我分析过程中发现的代码混淆,方便后继分析代码做准备。
反F5:大致模板如下:
__text:0000000103743850 FF C3 00 D1 SUB SP, SP, #0x30 ; '0'
__text:0000000103743854 E0 7B 01 A9 STP X0, X30, [SP,#0x10]
__text:0000000103743858 05 00 00 94 BL sub_10374386C ; 跳到方法返回值
__text:000000010374385C 86 A5 23 4F SSHLL2 V6.2D, V12.4S, #3
__text:0000000103743860 B1 FB A7 9B UMSUBL X17, W29, W7, X30
__text:0000000103743864 D2 76 2F F9 STR X18, [X22,#0x5EE8]
__text:0000000103743868 7F 16 04 FA DCB 0x7F, 0x16, 4, 0xFA ; 混淆数据
__text:000000010374386C
__text:000000010374386C
__text:000000010374386C
__text:000000010374386C
__text:000000010374386C
__text:000000010374386C sub_10374386C ;
__text:000000010374386C 80 01 00 10 ADR X0, dword_10374389C ;方法返回值
__text:0000000103743870 FE 03 00 AA MOV X30, X0 ; 方法返回值给返回寄存器
__text:0000000103743874 FF C3 00 91 ADD SP, SP, #0x30 ; '0'
__text:0000000103743878 C0 03 5F D6 RET
原理是通过动态赋值给x30实现跳转,X30链接寄存器(LR),用于保存子程序的返回地址。通篇都是这样的代码混淆方式,基本不怎么影响分析或脚本直接清除。
动态调试时如图4-1所示:
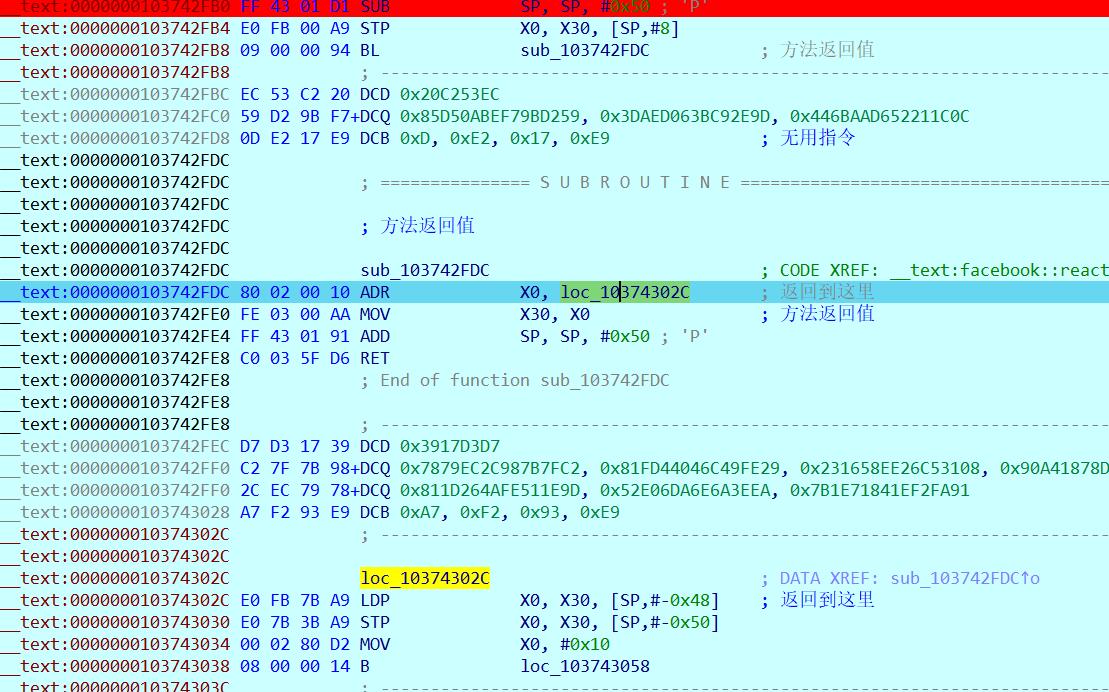
图4-1
字符串加解密:
__text:000000010180C0C0 DecStrng_sub_1036F80C0
__text:000000010180C0C0
__text:000000010180C0C0 7F 04 00 71 CMP W3, #1
__text:000000010180C0C4 0B 06 00 54 B.LT locret_10180C184
__text:000000010180C0C8 E9 03 03 2A MOV W9, W3
__text:000000010180C0CC 7F 40 00 71 CMP W3, #0x10
__text:000000010180C0D0 43 04 00 54 B.CC loc_10180C158
__text:000000010180C0D4 08 00 09 8B ADD X8, X0, X9
__text:000000010180C0D8 2A 00 09 8B ADD X10, X1, X9
__text:000000010180C0DC 5F 01 00 EB CMP X10, X0
__text:000000010180C0E0 00 81 41 FA CCMP X8, X1, #0, HI
__text:000000010180C0E4 A8 03 00 54 B.HI loc_10180C158
__text:000000010180C0E8 2A 6D 7C 92 AND X10, X9, #0xFFFFFFF0
__text:000000010180C0EC 68 04 03 0B ADD W8, W3, W3,LSL#1
__text:000000010180C0F0 08 01 02 0B ADD W8, W8, W2
__text:000000010180C0F4 6B 0C 00 12 AND W11, W3, #0xF
__text:000000010180C0F8 6B 09 0B 4B SUB W11, W11, W11,LSL#2
__text:000000010180C0FC 08 01 0B 0B ADD W8, W8, W11
__text:000000010180C100 40 0C 01 0E DUP V0.8B, W2
__text:000000010180C104 8B 8C 00 D0 ADRP X11, #qword_10299E470@PAGE
__text:000000010180C108 61 39 42 FD LDR D1, [X11,#qword_10299E470@PAGEOFF]
__text:000000010180C10C 00 84 21 0E ADD V0.8B, V0.8B, V1.8B
__text:000000010180C110 2B 20 00 91 ADD X11, X1, #8
__text:000000010180C114 0C 20 00 91 ADD X12, X0, #8
__text:000000010180C118 01 E7 00 0F MOVI V1.8B, #0x18
__text:000000010180C11C 02 E6 01 0F MOVI V2.8B, #0x30 ; '0'
__text:000000010180C120 ED 03 0A AA MOV X13, X10
__text:000000010180C124
__text:000000010180C124 loc_10180C124
__text:000000010180C124 03 84 21 0E ADD V3.8B, V0.8B, V1.8B
__text:000000010180C128 64 95 7F 6D LDP D4, D5, [X11,#-8]
__text:000000010180C12C 84 1C 20 2E EOR V4.8B, V4.8B, V0.8B
__text:000000010180C130 A3 1C 23 2E EOR V3.8B, V5.8B, V3.8B
__text:000000010180C134 84 8D 3F 6D STP D4, D3, [X12,#-8]
__text:000000010180C138 00 84 22 0E ADD V0.8B, V0.8B, V2.8B
__text:000000010180C13C 6B 41 00 91 ADD X11, X11, #0x10
__text:000000010180C140 8C 41 00 91 ADD X12, X12, #0x10
__text:000000010180C144 AD 41 00 F1 SUBS X13, X13, #0x10
__text:000000010180C148 E1 FE FF 54 B.NE loc_10180C124
__text:000000010180C14C 5F 01 09 EB CMP X10, X9
__text:000000010180C150 81 00 00 54 B.NE loc_10180C160
__text:000000010180C154 0C 00 00 14 B locret_10180C184
__text:000000010180C158
__text:000000010180C158
__text:000000010180C158 loc_10180C158
__text:000000010180C158
__text:000000010180C158 0A 00 80 D2 MOV X10, #0
__text:000000010180C15C E8 03 02 AA MOV X8, X2
__text:000000010180C160
__text:000000010180C160 loc_10180C160
__text:000000010180C160 2B 00 0A 8B ADD X11, X1, X10
__text:000000010180C164 0C 00 0A 8B ADD X12, X0, X10
__text:000000010180C168 29 01 0A CB SUB X9, X9, X10
__text:000000010180C16C
__text:000000010180C16C loc_10180C16C
__text:000000010180C16C