
目录:
一、行业背景
二、Anti-Bot简介
三、Anti-Bot安全SDK SGAVMP逆向分析
四、总结
一、行业背景
爬虫最早源于搜索引擎,它是一种按照一定的规则,自动从互联网上抓取信息数据的脚本程序,“爬虫本身不生产数据,它只是数据的搬运工”。
搜索引擎是善意的爬虫,它爬取网站的所有页面,提供给其他用户进行快速搜索和访问,给网站带来流量。为此,行业还达成了Robots君子协议,让互联网上的搜索与被搜索和谐相处。
原本双赢的局面,很快就被一些人破坏了,大量“变异”的爬虫很快充斥网络,通过模拟正常用户活动和行为,大肆进行数据窃取、资源占用、刷量刷单、薅羊毛等违法违规操作。
当前大多数业务都转移到了移动端,爬虫一般通过逆向分析APP并自行构造参数对非公开接口进行数据爬取或提交,获取对方本不愿意被大量获取的数据,并有可能给对方服务器性能造成极大损耗,尤其是近年来大数据成熟应用,吸引了许多公司肆意非法爬取其他公司的数据,竞对之间的监控等,确实形成了一定的侵害和威胁。
二、Anti-Bot简介
2.1、产品简介
阿里云爬虫风险管理(Anti-Bot Service,简称Anti-Bot)针对原生App端提供安全SDK解决方案。为App提供可信通信、防机器脚本滥刷等安全防护,有效识别高风险手机、猫池、牧场等特征。
App端安全SDK方案集成了阿里巴巴集团多年来对抗黑灰产、羊毛党的经验和技术积累。只要App集成Anti-Bot安全SDK后,App将获得与天猫、淘宝、支付宝等App端相同的可信通信技术能力,并可共享阿里巴巴集团多年对抗黑灰产、羊毛党所积累的恶意设备指纹库,从根本上解决App端的安全问题。
2.2、应用场景
Anti-Bot提供的App端安全SDK方案解决以下原生App端的安全问题:
恶意注册、撞库、暴力破解
针对App的大流量CC攻击
短信/验证码接口被刷
薅羊毛、抢红包
恶意秒杀限时限购商品
恶意查票、刷票(例如,机票、酒店等场景)
价值资讯爬取(例如,价格、征信、融资、小说等内容)
机器批量投票
灌水、恶意评论
2.3、防护总览:
当成功接入防护后,可以在爬虫风险管理控制台进行SDK防护配置,通过具体的防护规则过滤恶意爬虫流量。如图1所示:

图1
三、Anti-Bot安全SDK SGAVMP逆向分析
3.1、SDK文件与接口配置
Anti-Bot SDK包含以下文件,图2所示:

图2
SDK对外提供了两个接口:
初始化SDK:
接口定义:+ (BOOL) initialize
接口描述:
功能:初始化SDK
参数:无
返回值:BOOL类型。初始化成功返回YES,失败返回NO
签名请求数据:
接口定义:+ (NSData*) avmpSign: (NSInteger) signType input: (NSData*) input
接口描述:
功能:使用avmp技术对input的数据进行签名处理,并返回签名串
返回值:NSData*类型,返回签名串
3.2、整体框架介绍
主要分为两个接口,initialize和avmpSign接口对数据进行计算签名,再将签名与数据发送到服务器。服务器通过解析wToken进行风险识别、拦截恶意请求,然后将合法请求转发回源站。签名流程如图3所示:
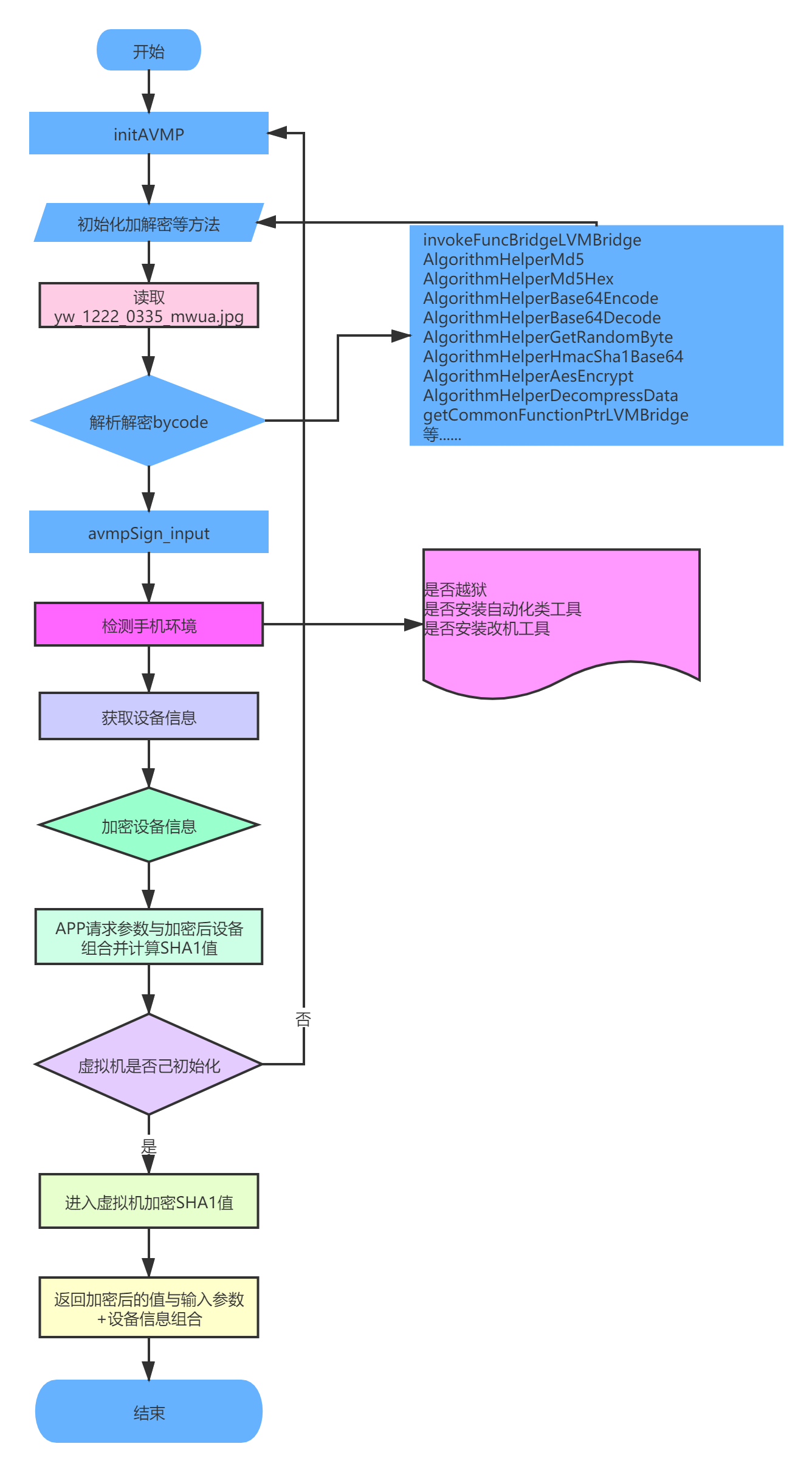
图3
3.3、通用反逆向技巧
反IDA的F5插件
主要通过动态计算函数调用地址方式反IDA F5使之失效,中间插入无效指令,基本模板如下:
__text:0000000100C14C14 loc_100C14C14 __text:0000000100C14C14 26 01 00 98 LDRSW X6, =unk_FFFFFE6C __text:0000000100C14C18 C6 74 01 D1 SUB X6, X6, #0x5D __text:0000000100C14C1C C6 EC 02 91 ADD X6, X6, #0xBB __text:0000000100C14C20 E6 03 26 AA MVN X6, X6 __text:0000000100C14C24 04 01 80 B9 LDRSW X4, [X8] __text:0000000100C14C28 C6 00 04 CB SUB X6, X6, X4 __text:0000000100C14C2C 42 00 06 8B ADD X2, X2, X6 __text:0000000100C14C30 E8 03 80 D2 MOV X8, #0x1F __text:0000000100C14C34 40 00 1F D6 BR X2 __text:0000000100C14C34 __text:0000000100C14C34 __text:0000000100C14C34 __text:0000000100C14C38 6C FE FF FF off_100C14C38 DCD unk_FFFFFE6C __text:0000000100C14C3C 52 B6 3B 46 DCD 0x463BB652 __text:0000000100C14C40 3E DCB 0x3E ; > __text:0000000100C14C41 1E DCB 0x1E __text:0000000100C14C42 41 DCB 0x41 ; A __text:0000000100C14C43 2D DCB 0x2D ; - __text:0000000100C14C44 6E DCB 0x6E ; n __text:0000000100C14C45 8F DCB 0x8F __text:0000000100C14C46 48 DCB 0x48 ; H __text:0000000100C14C47 CE DCB 0xCE __text:0000000100C14C48 31 DCB 0x31 ; 1 __text:0000000100C14C49 96 DCB 0x96 __text:0000000100C14C4A DC DCB 0xDC __text:0000000100C14C4B 73 DCB 0x73 ; s __text:0000000100C14C4C 0F DCB 0xF __text:0000000100C14C4D 66 DCB 0x66 ; f __text:0000000100C14C4E 64 DCB 0x64 ; d __text:0000000100C14C4F 9A DCB 0x9A ================================================================================= __text:0000000100BD5264 __text:0000000100BD5264 loc_100BD5264 __text:0000000100BD5264 E9 00 00 98 LDRSW X9, =0xFFFFFFD6 __text:0000000100BD5268 E9 03 29 AA MVN X9, X9 __text:0000000100BD526C 40 01 80 B9 LDRSW X0, [X10] __text:0000000100BD5270 29 01 00 8B ADD X9, X9, X0 __text:0000000100BD5274 08 01 09 8B ADD X8, X8, X9 __text:0000000100BD5278 6A 07 80 D2 MOV X10, #0x3B __text:0000000100BD527C 00 01 1F D6 BR X8 __text:0000000100BD527C ; End of function sub_100BD5210 __text:0000000100BD527C __text:0000000100BD527C __text:0000000100BD5280 D6 FF FF FF dword_100BD5280 DCD 0xFFFFFFD6 __text:0000000100BD5284 B8 0D AC 94 DCD 0x94AC0DB8 __text:0000000100BD5288 FF DCB 0xFF __text:0000000100BD5289 99 DCB 0x99 __text:0000000100BD528A AD DCB 0xAD __text:0000000100BD528B 81 DCB 0x81 __text:0000000100BD528C 34 DCB 0x34 ; 4 __text:0000000100BD528D FE DCB 0xFE __text:0000000100BD528E 48 DCB 0x48 ; H __text:0000000100BD528F FC DCB 0xFC __text:0000000100BD5290 6E DCB 0x6E ; n __text:0000000100BD5291 F5 DCB 0xF5 __text:0000000100BD5292 45 DCB 0x45 ; E __text:0000000100BD5293 F3 DCB 0xF3
加解字符串
每一个字符串常量都通过加密,使用时才解密,解密代码如下:
_text:000000010133EDAC 08 24 40 29 LDP W8, W9, [X0] __text:000000010133EDB0 41 02 00 B4 CBZ X1, loc_10133EDF8 __text:000000010133EDB4 __text:000000010133EDB4 loc_10133EDB4 ; CODE XREF: Dec+48↓j __text:000000010133EDB4 08 05 00 11 ADD W8, W8, #1 __text:000000010133EDB8 08 1D 00 12 AND W8, W8, #0xFF __text:000000010133EDBC 0A 20 00 91 ADD X10, X0, #8 __text:000000010133EDC0 4B 49 68 38 LDRB W11, [X10,W8,UXTW] __text:000000010133EDC4 29 01 0B 0B ADD W9, W9, W11 __text:000000010133EDC8 29 1D 00 12 AND W9, W9, #0xFF __text:000000010133EDCC 4C 49 69 38 LDRB W12, [X10,W9,UXTW] __text:000000010133EDD0 4C 49 28 38 STRB W12, [X10,W8,UXTW] __text:000000010133EDD4 4B 49 29 38 STRB W11, [X10,W9,UXTW] __text:000000010133EDD8 4D 14 40 38 LDRB W13, [X2],#1 __text:000000010133EDDC 8B 01 0B 0B ADD W11, W12, W11 __text:000000010133EDE0 6B 1D 00 12 AND W11, W11, #0xFF __text:000000010133EDE4 4A 49 6B 38 LDRB W10, [X10,W11,UXTW] __text:000000010133EDE8 4A 01 0D 4A EOR W10, W10, W13 __text:000000010133EDEC 6A 14 00 38 STRB W10, [X3],#1 __text:000000010133EDF0 21 04 00 F1 SUBS X1, X1, #1 __text:000000010133EDF4 01 FE FF 54 B.NE loc_10133EDB4 __text:000000010133EDF8 __text:000000010133EDF8 loc_10133EDF8 ; CODE XREF: Dec+4↑j __text:000000010133EDF8 08 24 00 29 STP W8, W9, [X0] __text:000000010133EDFC C0 03 5F D6 RET
加解密算法
根据传入不同类型的参数走不同的解密算法,switch跳转到对应的加解密算法,这些算法是在VMP外的通用算法,只要跳出虚拟机做加解密都会执行到这个地方,我已经对每一个算法重命名,代码如下:
__text:0000000104CA719C F4 4F BE A9 STP X20, X19, [SP,#-0x10+var_10]! __text:0000000104CA71A0 FD 7B 01 A9 STP X29, X30, [SP,#0x10+var_s0] __text:0000000104CA71A4 FD 43 00 91 ADD X29, SP, #0x10 __text:0000000104CA71A8 F3 03 01 AA MOV X19, X1 __text:0000000104CA71AC E9 03 00 AA MOV X9, X0 __text:0000000104CA71B0 0A 92 92 52+MOV W10, #0xD9490 __text:0000000104CA71B0 AA 01 A0 72 __text:0000000104CA71B8 08 64 90 52+MOV W8, #0xC8320 __text:0000000104CA71B8 88 01 A0 72 __text:0000000104CA71C0 68 02 00 B9 STR W8, [X19] __text:0000000104CA71C4 69 08 00 B4 CBZ X9, def_100B6F20C ; jumptable 0000000100B6F20C default case __text:0000000104CA71C4 ; jumptable 0000000104CA720C default case, cases 4-15,19 __text:0000000104CA71C8 28 11 40 F9 LDR X8, [X9,#0x20] __text:0000000104CA71CC 88 00 00 B4 CBZ X8, loc_104CA71DC __text:0000000104CA71D0 21 05 40 B9 LDR W1, [X9,#4] __text:0000000104CA71D4 3F 6C 00 71 CMP W1, #0x1B __text:0000000104CA71D8 69 00 00 54 B.LS loc_104CA71E4 __text:0000000104CA71DC __text:0000000104CA71DC loc_104CA71DC ; CODE XREF: Algorithm_type+30↑j __text:0000000104CA71DC 00 00 80 D2 MOV X0, #0 __text:0000000104CA71E0 3C 00 00 14 B def_100B6F20C ; jumptable 0000000100B6F20C default case __text:0000000104CA71E0 ; jumptable 0000000104CA720C default case, cases 4-15,19 __text:0000000104CA71E4 ; --------------------------------------------------------------------------- __text:0000000104CA71E4 __text:0000000104CA71E4 loc_104CA71E4 ; CODE XREF: Algorithm_type+3C↑j __text:0000000104CA71E4 00 00 80 D2 MOV X0, #0 __text:0000000104CA71E8 0A B0 8D 52+MOV W10, #0xD6D80 __text:0000000104CA71E8 AA 01 A0 72 __text:0000000104CA71F0 2B 0C 00 51 SUB W11, W1, #3 ; switch 24 cases __text:0000000104CA71F4 7F 5D 00 71 CMP W11, #0x17 __text:0000000104CA71F8 C8 06 00 54 B.HI def_100B6F20C ; jumptable 0000000100B6F20C default case __text:0000000104CA71F8 ; jumptable 0000000104CA720C default case, cases 4-15,19 __text:0000000104CA71FC 2C 07 00 10 ADR X12, jpt_100B6F20C __text:0000000104CA7200 1F 20 03 D5 NOP __text:0000000104CA7204 8B 79 AB B8 LDRSW X11, [X12,X11,LSL#2] __text:0000000104CA7208 6B 01 0C 8B ADD X11, X11, X12 __text:0000000104CA720C 60 01 1F D6 BR X11 ; switch jump __text:0000000104CA7210 ; --------------------------------------------------------------------------- __text:0000000104CA7210 __text:0000000104CA7210 loc_104CA7210 ; CODE XREF: Algorithm_type+70↑j __text:0000000104CA7210 ; DATA XREF: __text:_cvReleaseMatND+4681BC↓o ... __text:0000000104CA7210 20 01 40 B9 LDR W0, [X9] ; jumptable 0000000100B6F20C cases 16-18 __text:0000000104CA7210 ; jumptable 0000000104CA720C cases 16-18 __text:0000000104CA7214 22 09 40 B9 LDR W2, [X9,#8] __text:0000000104CA7218 23 11 41 A9 LDP X3, X4, [X9,#0x10] __text:0000000104CA721C E5 03 08 AA MOV X5, X8 __text:0000000104CA7220 E6 03 13 AA MOV X6, X19 __text:0000000104CA7224 14 E6 00 94 BL Aes_Dec_data ; AES加密解 __text:0000000104CA7228 20 05 00 B5 CBNZ X0, loc_104CA72CC __text:0000000104CA722C 2A 00 00 14 B loc_104CA72D4 __text:0000000104CA7230 ; --------------------------------------------------------------------------- __text:0000000104CA7230 __text:0000000104CA7230 loc_104CA7230 ; CODE XREF: Algorithm_type+70↑j __text:0000000104CA7230 ; DATA XREF: __text:jpt_100B6F20C↓o __text:0000000104CA7230 20 0D 40 F9 LDR X0, [X9,#0x18] ; jumptable 0000000100B6F20C case 3 __text:0000000104CA7230 ; jumptable 0000000104CA720C case 3 __text:0000000104CA7234 E1 03 08 AA MOV X1, X8 __text:0000000104CA7238 81 5E FF 97 BL DecString_3 ; 解密字符串 __text:0000000104CA723C 80 04 00 B5 CBNZ X0, loc_104CA72CC __text:0000000104CA7240 25 00 00 14 B loc_104CA72D4 __text:0000000104CA7244 ; --------------------------------------------------------------------------- __text:0000000104CA7244 __text:0000000104CA7244 loc_104CA7244 ; CODE XREF: Algorithm_type+70↑j __text:0000000104CA7244 ; DATA XREF: __text:_cvReleaseMatND+4681CC↓o __text:0000000104CA7244 20 01 40 B9 LDR W0, [X9] ; jumptable 0000000100B6F20C case 20 __text:0000000104CA7244 ; jumptable 0000000104CA720C case 20 __text:0000000104CA7248 E1 03 08 AA MOV X1, X8 __text:0000000104CA724C 7B 40 FF 97 BL DecComper_0 ; 解压缩 __text:0000000104CA7250 E0 03 00 B5 CBNZ X0, loc_104CA72CC __text:0000000104CA7254 20 00 00 14 B loc_104CA72D4 __text:0000000104CA7258 ; --------------------------------------------------------------------------- __text:0000000104CA7258 __text:0000000104CA7258 loc_104CA7258 ; CODE XREF: Algorithm_type+70↑j __text:0000000104CA7258 ; DATA XREF: __text:_cvReleaseMatND+4681D0↓o __text:0000000104CA7258 20 01 40 B9 LDR W0, [X9] ; jumptable 0000000100B6F20C case 21 __text:0000000104CA7258 ; jumptable 0000000104CA720C case 21 __text:0000000104CA725C E1 03 08 AA MOV X1, X8 __text:0000000104CA7260 E2 03 13 AA MOV X2, X19 __text:0000000104CA7264 C0 C7 00 94 BL base64_1 ; base64加解密 __text:0000000104CA7268 20 03 00 B5 CBNZ X0, loc_104CA72CC __text:0000000104CA726C 1A 00 00 14 B loc_104CA72D4 __text:0000000104CA7270 ; --------------------------------------------------------------------------- __text:0000000104CA7270 __text:0000000104CA7270 loc_104CA7270 ; CODE XREF: Algorithm_type+70↑j __text:0000000104CA7270 ; DATA XREF: __text:_cvReleaseMatND+4681D4↓o __text:0000000104CA7270 E0 03 08 AA MOV X0, X8 ; jumptable 0000000100B6F20C case 22 __text:0000000104CA7270 ; jumptable 0000000104CA720C case 22 __text:0000000104CA7274 91 81 00 94 BL Md5 ; MD5算法 __text:0000000104CA7278 A0 02 00 B5 CBNZ X0, loc_104CA72CC __text:0000000104CA727C 16 00 00 14 B loc_104CA72D4 __text:0000000104CA7280 ; --------------------------------------------------------------------------- __text:0000000104CA7280 __text:0000000104CA7280 loc_104CA7280 ; CODE XREF: Algorithm_type+70↑j __text:0000000104CA7280 ; DATA XREF: __text:_cvReleaseMatND+4681D8↓o __text:0000000104CA7280 20 0D 40 F9 LDR X0, [X9,#0x18] ; jumptable 0000000100B6F20C case 23 __text:0000000104CA7280 ; jumptable 0000000104CA720C case 23 __text:0000000104CA7284 E1 03 08 AA MOV X1, X8 __text:0000000104CA7288 4D 56 00 94 BL sub_104CBCBBC __text:0000000104CA728C 00 02 00 B5 CBNZ X0, loc_104CA72CC __text:0000000104CA7290 11 00 00 14 B loc_104CA72D4 __text:0000000104CA7294 ; --------------------------------------------------------------------------- __text:0000000104CA7294 __text:0000000104CA7294 loc_104CA7294 ; CODE XREF: Algorithm_type+70↑j __text:0000000104CA7294 ; DATA XREF: __text:_cvReleaseMatND+4681DC↓o __text:0000000104CA7294 E0 03 08 AA MOV X0, X8 ; jumptable 0000000100B6F20C case 24 __text:0000000104CA7294 ; jumptable 0000000104CA720C case 24 __text:0000000104CA7298 0D 3A 00 94 BL Sha1 ; SHA1算法 __text:0000000104CA729C 80 01 00 B5 CBNZ X0, loc_104CA72CC __text:0000000104CA72A0 0D 00 00 14 B loc_104CA72D4 __text:0000000104CA72A4 ; --------------------------------------------------------------------------- __text:0000000104CA72A4 __text:0000000104CA72A4 loc_104CA72A4 ; CODE XREF: Algorithm_type+70↑j __text:0000000104CA72A4 ; DATA XREF: __text:_cvReleaseMatND+4681E0↓o __text:0000000104CA72A4 E0 03 08 AA MOV X0, X8 ; jumptable 0000000100B6F20C case 25 __text:0000000104CA72A4 ; jumptable 0000000104CA720C case 25 __text:0000000104CA72A8 AB 6B FF 97 BL sub_104C82154 __text:0000000104CA72AC 00 01 00 B5 CBNZ X0, loc_104CA72CC __text:0000000104CA72B0 09 00 00 14 B loc_104CA72D4 __text:0000000104CA72B4 ; --------------------------------------------------------------------------- __text:0000000104CA72B4 __text:0000000104CA72B4 loc_104CA72B4 ; CODE XREF: Algorithm_type+70↑j __text:0000000104CA72B4 ; DATA XREF: __text:_cvReleaseMatND+4681E4↓o __text:0000000104CA72B4 20 01 40 B9 LDR W0, [X9] ; jumptable 0000000100B6F20C case 26 __text:0000000104CA72B4 ; jumptable 0000000104CA720C case 26 __text:0000000104CA72B8 21 09 40 B9 LDR W1, [X9,#8] __text:0000000104CA72BC E2 03 08 AA MOV X2, X8 __text:0000000104CA72C0 E3 03 13 AA MOV X3, X19 __text:0000000104CA72C4 D1 F3 FF 97 BL sub_104CA4208 __text:0000000104CA72C8 60 00 00 B4 CBZ X0, loc_104CA72D4 __text:0000000104CA72CC __text:0000000104CA72CC loc_104CA72CC ; CODE XREF: Algorithm_type+8C↑j __text:0000000104CA72CC ; Algorithm_type+A0↑j ... __text:0000000104CA72CC 0A 00 80 52 MOV W10, #0 __text:0000000104CA72D0 __text:0000000104CA72D0 def_100B6F20C ; CODE XREF: Algorithm_type+28↑j __text:0000000104CA72D0 ; Algorithm_type+44↑j ... __text:0000000104CA72D0 6A 02 00 B9 STR W10, [X19] ; jumptable 0000000100B6F20C default case __text:0000000104CA72D0 ; jumptable 0000000104CA720C default case, cases 4-15,19 __text:0000000104CA72D4 __text:0000000104CA72D4 loc_104CA72D4 ; CODE XREF: Algorithm_type+90↑j __text:0000000104CA72D4 ; Algorithm_type+A4↑j ... __text:0000000104CA72D4 FD 7B 41 A9 LDP X29, X30, [SP,#0x10+var_s0] __text:0000000104CA72D8 F4 4F C2 A8 LDP X20, X19, [SP+0x10+var_10],#0x20 __text:0000000104CA72DC C0 03 5F D6 RET
3.4、签名流程分析
+[ConstantFunctions initAVMP]
解密内存中图片得解密yw_1222_0335_mwua.jpg图片的密钥
invokeFuncBridgeLVMBridge->Aes_Dec_data->AlgorithmHelperDecompressData,AES解密解压,解密后内容如下:
00000001440EC800 0D 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 00000001440EC810 00 00 00 00 01 00 00 00 00 00 00 00 00 00 00 00 ................ 00000001440EC820 00 00 00 00 00 00 00 00 13 00 00 00 40 00 00 00 [email protected] 00000001440EC830 64 65 76 69 63 65 5F 70 72 69 6E 74 5F 72 65 73 device_print_res 00000001440EC840 5F 6B 31 73 57 34 66 75 36 6A 38 72 78 65 76 47 _k1sW4fu6j8rxevG 00000001440EC850 7A 63 39 55 62 4C 53 30 5A 4A 79 43 32 4F 6E 56 zc9UbLS0ZJyC2OnV 00000001440EC860 61 46 68 51 52 44 71 4E 4B 6F 50 58 35 59 6B 49 aFhQRDqNKoPX5YkI 00000001440EC870 69 45 74 67 6D 41 42 70 64 33 77 54 31 48 37 6C iEtgmABpd3wT1H7l 00000001440EC880 4D 78 34 01 00 00 00 00 00 00 00 00 00 00 00 00 Mx4............. 00000001440EC890 00 00 00 00 00 00 00 02 00 00 00 10 00 00 00 6E ...............n 00000001440EC8A0 63 62 32 64 34 72 32 32 66 39 49 62 7A 54 76 39 cb2d4r22f9IbzTv9 00000001440EC8B0 6D 01 00 00 00 00 00 00 00 00 00 00 00 00 00 00 m............... 00000001440EC8C0 00 00 00 00 00 13 00 00 00 20 00 00 00 6A 61 71 ......... ...jaq 00000001440EC8D0 5F 76 65 72 69 66 69 63 61 74 69 6F 6E 5F 6B 31 _verification_k1 00000001440EC8E0 30 66 63 62 34 38 63 33 31 39 65 63 33 65 65 35 0fcb48c319ec3ee5 00000001440EC8F0 61 31 61 62 33 37 30 65 34 33 32 31 62 32 66 33 a1ab370e4321b2f3 00000001440EC900 01 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 00000001440EC910 00 00 00 00 07 00 00 00 10 00 00 00 69 6E 6E 65 ............inne 00000001440EC920 72 6B 31 41 73 57 6A 64 67 6F 31 39 36 64 4B 32 rk1AsWjdgo196dK2 00000001440EC930 31 59 76 01 00 00 00 00 00 00 00 00 00 00 00 00 1Yv............. 00000001440EC940 00 00 00 00 00 00 00 0D 00 00 00 20 00 00 00 64 ........... ...d 00000001440EC950 79 75 70 64 61 74 65 5F 34 32 37 32 30 65 62 62 yupdate_42720ebb 00000001440EC960 63 63 63 66 65 65 31 38 64 37 61 64 31 61 65 62 cccfee18d7ad1aeb 00000001440EC970 63 35 62 31 33 35 66 66 61 39 30 36 01 00 00 00 c5b135ffa906.... 00000001440EC980 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 00000001440EC990 11 00 00 00 20 00 00 00 64 79 75 70 64 61 74 65 .... ...dyupdate 00000001440EC9A0 5F 32 33 34 33 39 34 36 38 32 61 64 62 32 33 62 _234394682adb23b 00000001440EC9B0 38 63 65 33 31 36 61 34 61 37 38 34 34 66 34 66 8ce316a4a7844f4f 00000001440EC9C0 37 64 30 61 31 36 62 36 30 02 00 00 00 00 00 00 7d0a16b60....... 00000001440EC9D0 00 00 00 00 00 00 00 00 00 00 00 00 00 10 00 00 ................ 00000001440EC9E0 00 40 00 00 00 77 62 5F 73 63 5F 69 6E 74 5F 72 [email protected]_sc_int_r 00000001440EC9F0 65 73 5F 6B 31 34 70 63 61 42 56 68 77 65 52 79 es_k14pcaBVhweRy 00000001440ECA00 38 6F 46 54 6D 43 43 52 68 4B 6D 55 43 53 56 6A 8oFTmCCRhKmUCSVj 00000001440ECA10 72 35 73 46 71 65 6D 69 57 50 4F 73 69 71 6B 33 r5sFqemiWPOsiqk3 00000001440ECA20 65 4E 6B 56 53 58 6C 49 61 39 61 6D 52 44 62 74 eNkVSXlIa9amRDbt 00000001440ECA30 75 56 59 44 39 03 00 00 00 00 00 00 00 00 00 00 uVYD9........... 00000001440ECA40 00 00 00 00 00 00 00 00 00 0B 00 00 00 40 00 00 [email protected] 00000001440ECA50 00 6E 6F 74 5F 63 6F 6E 76 65 72 74 34 70 63 61 .not_convert4pca 00000001440ECA60 42 56 68 77 65 52 79 38 6F 46 54 6D 43 43 52 68 BVhweRy8oFTmCCRh 00000001440ECA70 4B 6D 55 43 53 56 6A 72 35 73 46 71 65 6D 69 57 KmUCSVjr5sFqemiW 00000001440ECA80 50 4F 73 69 71 6B 33 65 4E 6B 56 53 58 6C 49 61 POsiqk3eNkVSXlIa 00000001440ECA90 39 61 6D 52 44 62 74 75 56 59 44 39 03 00 00 00 9amRDbtuVYD9.... 00000001440ECAA0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 00000001440ECAB0 08 00 00 00 10 00 00 00 77 68 69 74 65 5F 69 76 ........white_iv 00000001440ECAC0 36 7A 69 38 74 65 79 34 33 32 38 54 63 55 68 31 6zi8tey4328TcUh1 00000001440ECAD0 07 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 00000001440ECAE0 00 00 00 00 0D 00 00 00 04 00 00 00 77 75 61 5F ............wua_ 00000001440ECAF0 6B 65 79 5F 69 6E 64 65 78 48 48 6E 42 07 00 00 key_indexHHnB... 00000001440ECB00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 00000001440ECB10 00 04 00 00 00 24 00 00 00 48 48 6E 42 66 31 39 .....$...HHnBf19 00000001440ECB20 62 37 62 63 37 2D 30 61 66 65 2D 34 30 30 34 2D b7bc7-0afe-4004- 00000001440ECB30 62 62 33 39 2D 38 38 39 32 61 35 30 66 64 66 35 bb39-8892a50fdf5 00000001440ECB40 31 07 00 00 00 00 00 00 00 00 00 00 00 00 00 00 1............... 00000001440ECB50 00 00 00 00 00 04 00 00 00 24 00 00 00 30 30 30 .........$...000 00000001440ECB60 30 35 38 31 37 31 35 34 64 2D 35 64 63 35 2D 34 05817154d-5dc5-4 00000001440ECB70 34 33 32 2D 38 62 34 31 2D 62 31 34 38 36 37 36 432-8b41-b148676 00000001440ECB80 62 33 38 30 66 03 00 00 00 00 00 00 00 00 00 00 b380f........... 00000001440ECB90 00 00 00 00 00 00 00 00 00 0B 00 00 00 10 00 00 ................ 00000001440ECBA0 00 73 67 63 69 70 68 65 72 5F 69 76 6A 31 32 39 .sgcipher_ivj129 00000001440ECBB0 63 79 32 73 62 73 6D 31 6E 6D 34 61 5B 5D 30 30 cy2sbsm1nm4a[]00 00000001440ECBC0 33 30 38 31 38 39 30 32 38 31 38 31 30 30 38 34 3081890281810084 00000001440ECBD0 30 36 31 32 35 66 33 36 39 66 64 65 32 37 32 30 06125f369fde2720 00000001440ECBE0 66 37 32 36 34 39 32 33 61 36 33 64 63 34 38 65 f7264923a63dc48e 00000001440ECBF0 31 32 34 33 63 31 64 39 37 38 33 65 64 34 34 64 1243c1d9783ed44d 00000001440ECC00 38 63 32 37 36 36 30 32 64 32 64 35 37 30 30 37 8c276602d2d57007 00000001440ECC10 33 64 39 32 63 31 35 35 62 38 31 64 35 38 39 39 3d92c155b81d5899 00000001440ECC20 65 39 61 38 61 39 37 65 30 36 33 35 33 61 63 34 e9a8a97e06353ac4 00000001440ECC30 62 30 34 34 64 30 37 63 61 33 65 32 33 33 33 36 b044d07ca3e23336 00000001440ECC40 37 37 64 31 39 39 65 30 39 36 39 63 39 36 34 38 77d199e0969c9648 00000001440ECC50 39 66 36 33 32 33 65 64 35 33 36 38 65 31 37 36 9f6323ed5368e176 00000001440ECC60 30 37 33 31 37 30 34 34 30 32 64 30 31 31 32 63 0731704402d0112c 00000001440ECC70 30 30 32 63 63 64 30 39 61 30 36 64 32 37 39 34 002ccd09a06d2794 00000001440ECC80 36 32 36 39 61 34 33 38 66 65 34 62 30 32 31 36 6269a438fe4b0216 00000001440ECC90 62 37 31 38 62 36 35 38 65 65 64 39 64 31 36 35 b718b658eed9d165 00000001440ECCA0 30 32 33 66 32 34 63 36 64 64 61 65 63 30 61 66 023f24c6ddaec0af 00000001440ECCB0 36 66 34 37 61 64 61 38 33 30 36 61 64 30 63 34 6f47ada8306ad0c4 00000001440ECCC0 66 30 66 63 64 38 30 64 39 62 36 39 31 31 30 32 f0fcd80d9b691102 00000001440ECCD0 30 33 30 31 30 30 30 31 00 FF FF FF FF FF FF FF 03010001
-[SecurityGuardOpenAVMPGeneric createAVMPInstance:byteCodeName:]
打开图片文件fopen AirAsiaMobile.appp/yw_1222_0335_mwua.jpg
解析图片,定位到密文开始数据,部分数据如下:
开始数据,大小000000000000A2C0, 000000014558C000 11 DF 5F D4 DB 75 B8 03 85 04 B3 42 A3 54 01 91 000000014558C010 0F 58 78 B9 35 7D 2E B9 86 EF E8 E0 14 AA AF 6B
上面解密出来的数据做为解密密钥前0x10字节,解密图片数据。
00308189028181008406125f369fde2720f7264923a63dc48e1243c1d9783ed44d8c276602d2d570073d92c155b81d5899e9a8a97e06353ac4b044d07ca3e2333677d199e0969c96489f6323ed5368e1760731704402d0112c002ccd09a06d27946269a438fe4b0216b718b658eed9d165023f24c6ddaec0af6f47ada8306ad0c4f0fcd80d9b69110203010001
invokeFuncBridgeLVMBridge->Aes_Dec_data解密4次后得到数据,部分数据如下:
解密后开始数据 大小000000000000A28E 000000014558C000 78 9C EC BD 0F 7C 1C 57 7D 2F FA 9B D9 95 34 5A 000000014558C010 AF E5 91 AD 98 B5 FC 6F E5 28 C9 DA 38 66 FC 27
上面解密数据的AES解密算法
__text:0000000104CE0954 loc_104CE0954 ; CODE XREF: Aes_Dec+EC↑j __text:0000000104CE0954 15 00 80 52 MOV W21, #0 __text:0000000104CE0958 88 12 40 B9 LDR W8, [X20,#0x10] __text:0000000104CE095C 1F 41 00 71 CMP W8, #0x10 __text:0000000104CE0960 E3 07 00 54 B.CC loc_104CE0A5C __text:0000000104CE0964 97 0E 40 F9 LDR X23, [X20,#0x18] __text:0000000104CE0968 B7 07 00 B4 CBZ X23, loc_104CE0A5C __text:0000000104CE096C 98 22 40 B9 LDR W24, [X20,#0x20] __text:0000000104CE0970 78 07 00 34 CBZ W24, loc_104CE0A5C __text:0000000104CE0974 96 16 40 F9 LDR X22, [X20,#0x28] __text:0000000104CE0978 36 07 00 B4 CBZ X22, loc_104CE0A5C __text:0000000104CE097C 9A 32 40 B9 LDR W26, [X20,#0x30] __text:0000000104CE0980 FA 06 00 34 CBZ W26, loc_104CE0A5C __text:0000000104CE0984 48 0F 00 12 AND W8, W26, #0xF __text:0000000104CE0988 A8 06 00 35 CBNZ W8, loc_104CE0A5C __text:0000000104CE098C BB 03 02 D1 SUB X27, X29, #-var_80 __text:0000000104CE0990 88 06 40 F9 LDR X8, [X20,#8] ; 异或密钥 __text:0000000104CE0994 68 00 00 B4 CBZ X8, loc_104CE09A0 __text:0000000104CE0998 00 01 C0 3D LDR Q0, [X8] __text:0000000104CE099C 60 07 80 3D STR Q0, [X27,#0x10] __text:0000000104CE09A0 __text:0000000104CE09A0 loc_104CE09A0 ; CODE XREF: Aes_Dec+1B0↑j __text:0000000104CE09A0 E0 63 00 91 ADD X0, SP, #0x6A0+var_688 ; void * __text:0000000104CE09A4 81 40 80 52 MOV W1, #0x204 ; size_t __text:0000000104CE09A8 21 60 06 94 BL _bzero __text:0000000104CE09AC E0 63 00 91 ADD X0, SP, #0x6A0+var_688 __text:0000000104CE09B0 E2 03 18 AA MOV X2, X24 __text:0000000104CE09B4 E1 03 17 AA MOV X1, X23 __text:0000000104CE09B8 25 25 FE 97 BL InitAeskey ; 初始化密钥 __text:0000000104CE09BC 57 7F 04 53 LSR W23, W26, #4 __text:0000000104CE09C0 BF 7F 38 A9 STP XZR, XZR, [X29,#var_80] __text:0000000104CE09C4 97 03 00 34 CBZ W23, loc_104CE0A34 __text:0000000104CE09C8 18 00 80 52 MOV W24, #0 __text:0000000104CE09CC BC C3 01 D1 SUB X28, X29, #-var_70 __text:0000000104CE09D0 F5 03 13 AA MOV X21, X19 __text:0000000104CE09D4 __text:0000000104CE09D4 loc_104CE09D4 ; CODE XREF: Aes_Dec+240↓j __text:0000000104CE09D4 C0 02 C0 3D LDR Q0, [X22] __text:0000000104CE09D8 60 03 80 3D STR Q0, [X27] __text:0000000104CE09DC E0 63 00 91 ADD X0, SP, #0x6A0+var_688 __text:0000000104CE09E0 E1 03 15 AA MOV X1, X21 __text:0000000104CE09E4 E2 03 16 AA MOV X2, X22 __text:0000000104CE09E8 4B 29 FE 97 BL AES_Dec ; X0:初始化后密钥,x1:返回,X2:原始数据 __text:0000000104CE09EC 08 00 80 D2 MOV X8, #0 __text:0000000104CE09F0 __text:0000000104CE09F0 loc_104CE09F0 ; CODE XREF: Aes_Dec+224↓j __text:0000000104CE09F0 89 6B 68 38 LDRB W9, [X28,X8] ; 异或密钥 __text:0000000104CE09F4 AA 6A 68 38 LDRB W10, [X21,X8] ; 加密后数据 __text:0000000104CE09F8 49 01 09 4A EOR W9, W10, W9 ; 异或加密 __text:0000000104CE09FC A9 6A 28 38 STRB W9, [X21,X8] __text:0000000104CE0A00 08 05 00 91 ADD X8, X8, #1 __text:0000000104CE0A04 1F 41 00 F1 CMP X8, #0x10 __text:0000000104CE0A08 41 FF FF 54 B.NE loc_104CE09F0 ; 异或密钥 __text:0000000104CE0A0C 60 03 C0 3D LDR Q0, [X27] __text:0000000104CE0A10 60 07 80 3D STR Q0, [X27,#0x10] __text:0000000104CE0A14 D6 42 00 91 ADD X22, X22, #0x10 __text:0000000104CE0A18 B5 42 00 91 ADD X21, X21, #0x10 __text:0000000104CE0A1C 18 07 00 11 ADD W24, W24, #1 __text:0000000104CE0A20 1F 03 17 6B CMP W24, W23 __text:0000000104CE0A24 81 FD FF 54 B.NE loc_104CE09D4 __text:0000000104CE0A28 __text:0000000104CE0A28 loc_104CE0A28 ; CODE XREF: Aes_Dec+16C↑j __text:0000000104CE0A28 41 6F 1C 12 AND W1, W26, #0xFFFFFFF0 __text:0000000104CE0A2C 81 00 00 35 CBNZ W1, loc_104CE0A3C __text:0000000104CE0A30 0A 00 00 14 B loc_104CE0A58 __text:0000000104CE0A34 ; --------------------------------------------------------------------------- __text:0000000104CE0A34 __text:0000000104CE0A34 loc_104CE0A34 ; CODE XREF: Aes_Dec+144↑j __text:0000000104CE0A34 ; Aes_Dec+1E0↑j __text:0000000104CE0A34 01 00 80 52 MOV W1, #0 __text:0000000104CE0A38 01 01 00 34 CBZ W1, loc_104CE0A58 __text:0000000104CE0A3C __text:0000000104CE0A3C loc_104CE0A3C ; CODE XREF: Aes_Dec+248↑j __text:0000000104CE0A3C 82 1E 40 F9 LDR X2, [X20,#0x38] __text:0000000104CE0A40 E4 03 1C 32 MOV W4, #0x10 __text:0000000104CE0A44 E0 03 13 AA MOV X0, X19 ; void * __text:0000000104CE0A48 B7 80 FF 97 BL memcpy_0 ; 拷贝加密后数据 __text:0000000104CE0A4C F5 03 00 AA MOV X21, X0 __text:0000000104CE0A50 99 00 00 B5 CBNZ X25, loc_104CE0A60 __text:0000000104CE0A54 8C FF FF 17 B loc_104CE0884
解压解密后数据,部分数据如下:
开始 0000000146400010 大小 000000000001CD20 0000000146400010 00 00 00 00 63 6F 6D 2E 74 65 73 74 02 00 00 00 ....com.test.... 0000000146400020 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 0000000146400030 07 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 0000000146400040 00 00 00 00 0D 00 00 00 04 00 00 00 77 75 61 5F ............wua_ 0000000146400050 6B 65 79 5F 69 6E 64 65 78 4B 49 55 52 07 00 00 key_indexKIUR... 0000000146400060 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 0000000146400070 00 04 00 00 00 24 00 00 00 4B 49 55 52 66 31 37 .....$...KIURf17 0000000146400080 39 65 66 33 63 2D 63 34 33 63 2D 34 34 31 62 2D 9ef3c-c43c-441b- 0000000146400090 62 31 61 35 2D 35 66 38 62 62 36 63 39 65 66 34 b1a5-5f8bb6c9ef4 00000001464000A0 38 5B 5D 30 30 33 30 38 31 38 39 30 32 38 31 38 8[]0030818902818 00000001464000B0 31 30 30 38 34 30 36 31 32 35 66 33 36 39 66 64 1008406125f369fd 00000001464000C0 65 32 37 32 30 66 37 32 36 34 39 32 33 61 36 33 e2720f7264923a63 00000001464000D0 64 63 34 38 65 31 32 34 33 63 31 64 39 37 38 33 dc48e1243c1d9783 00000001464000E0 65 64 34 34 64 38 63 32 37 36 36 30 32 64 32 64 ed44d8c276602d2d 00000001464000F0 35 37 30 30 37 33 64 39 32 63 31 35 35 62 38 31 570073d92c155b81 0000000146400100 64 35 38 39 39 65 39 61 38 61 39 37 65 30 36 33 d5899e9a8a97e063 0000000146400110 35 33 61 63 34 62 30 34 34 64 30 37 63 61 33 65 53ac4b044d07ca3e 0000000146400120 32 33 33 33 36 37 37 64 31 39 39 65 30 39 36 39 2333677d199e0969 0000000146400130 63 39 36 34 38 39 66 36 33 32 33 65 64 35 33 36 c96489f6323ed536 0000000146400140 38 65 31 37 36 30 37 33 31 37 30 34 34 30 32 64 8e1760731704402d 0000000146400150 30 31 31 32 63 30 30 32 63 63 64 30 39 61 30 36 0112c002ccd09a06 0000000146400160 64 32 37 39 34 36 32 36 39 61 34 33 38 66 65 34 d27946269a438fe4 0000000146400170 62 30 32 31 36 62 37 31 38 62 36 35 38 65 65 64 b0216b718b658eed 0000000146400180 39 64 31 36 35 30 32 33 66 32 34 63 36 64 64 61 9d165023f24c6dda 0000000146400190 65 63 30 61 66 36 66 34 37 61 64 61 38 33 30 36 ec0af6f47ada8306 00000001464001A0 61 64 30 63 34 66 30 66 63 64 38 30 64 39 62 36 ad0c4f0fcd80d9b6 00000001464001B0 39 31 31 30 32 30 33 30 31 30 30 30 31 01 00 00 9110203010001... 00000001464001C0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 00000001464001D0 00 06 01 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 00000001464001E0 00 03 00 00 00 0B 00 00 00 28 CB 01 00 62 63 5F .........(...bc_ 00000001464001F0 73 67 63 69 70 68 65 72 01 00 01 00 D0 07 00 00 sgcipher........ 0000000146400200 01 00 00 00 05 00 00 00 1E 46 00 00 29 40 27 49 .........F..)@'I 0000000146400210 49 49 49 49 6A 71 00 00 FC 7B 70 02 48 61 13 78 IIIIjq...{p.Ha.x 0000000146400220 88 41 13 78 C8 21 13 78 08 02 13 78 48 E3 12 78 .A.x...x...xH...
解压函数
__text:0000000104C77660 ; 解压缩 __text:0000000104C77660 ; Attributes: bp-based frame __text:0000000104C77660 __text:0000000104C77660 decompression ; CODE XREF: decompression_1+38↑p __text:0000000104C77660 __text:0000000104C77660 var_A0= -0xA0 __text:0000000104C77660 var_98= -0x98 __text:0000000104C77660 var_90= -0x90 __text:0000000104C77660 var_88= -0x88 __text:0000000104C77660 var_80= -0x80 __text:0000000104C77660 var_78= -0x78 __text:0000000104C77660 var_60= -0x60 __text:0000000104C77660 var_50= -0x50 __text:0000000104C77660 var_30= -0x30 __text:0000000104C77660 var_20= -0x20 __text:0000000104C77660 var_10= -0x10 __text:0000000104C77660 var_s0= 0 __text:0000000104C77660 __text:0000000104C77660 FF C3 02 D1 SUB SP, SP, #0xB0 __text:0000000104C77664 F8 5F 07 A9 STP X24, X23, [SP,#0xA0+var_30] __text:0000000104C77668 F6 57 08 A9 STP X22, X21, [SP,#0xA0+var_20] __text:0000000104C7766C F4 4F 09 A9 STP X20, X19, [SP,#0xA0+var_10] __text:0000000104C77670 FD 7B 0A A9 STP X29, X30, [SP,#0xA0+var_s0] __text:0000000104C77674 FD 83 02 91 ADD X29, SP, #0xA0 __text:0000000104C77678 F4 03 02 AA MOV X20, X2 __text:0000000104C7767C F8 03 01 AA MOV X24, X1 __text:0000000104C77680 F5 03 00 AA MOV X21, X0 __text:0000000104C77684 13 00 80 D2 MOV X19, #0 __text:0000000104C77688 16 00 80 12 MOV W22, #0xFFFFFFFF __text:0000000104C7768C 95 01 00 B4 CBZ X21, loc_104C776BC __text:0000000104C77690 78 01 00 B4 CBZ X24, loc_104C776BC __text:0000000104C77694 FF 7F 04 A9 STP XZR, XZR, [SP,#0xA0+var_60] __text:0000000104C77698 FF 2B 00 F9 STR XZR, [SP,#0xA0+var_50] __text:0000000104C7769C 41 15 00 B0+ADRL X1, 0x104F20483 ; version __text:0000000104C7769C 21 0C 12 91 __text:0000000104C776A4 E2 0B 1C 32 MOV W2, #0x70 ; 'p' ; stream_size __text:0000000104C776A8 E0 03 00 91 MOV X0, SP ; strm __text:0000000104C776AC C9 06 08 94 BL _inflateInit_ __text:0000000104C776B0 80 01 00 34 CBZ W0, loc_104C776E0 __text:0000000104C776B4 13 00 80 D2 MOV X19, #0 __text:0000000104C776B8 __text:0000000104C776B8 loc_104C776B8 ; CODE XREF: decompression+94↓j __text:0000000104C776B8 16 00 80 12 MOV W22, #0xFFFFFFFF __text:0000000104C776BC __text:0000000104C776BC loc_104C776BC ; CODE XREF: decompression+2C↑j __text:0000000104C776BC ; decompression+30↑j ... __text:0000000104C776BC E0 03 13 AA MOV X0, X19 ; void * __text:0000000104C776C0 1E D3 00 94 BL free __text:0000000104C776C4 E0 03 16 AA MOV X0, X22 __text:0000000104C776C8 FD 7B 4A A9 LDP X29, X30, [SP,#0xA0+var_s0] __text:0000000104C776CC F4 4F 49 A9 LDP X20, X19, [SP,#0xA0+var_10] __text:0000000104C776D0 F6 57 48 A9 LDP X22, X21, [SP,#0xA0+var_20] __text:0000000104C776D4 F8 5F 47 A9 LDP X24, X23, [SP,#0xA0+var_30] __text:0000000104C776D8 FF C3 02 91 ADD SP, SP, #0xB0 __text:0000000104C776DC C0 03 5F D6 RET __text:0000000104C776E0 ; --------------------------------------------------------------------------- __text:0000000104C776E0 __text:0000000104C776E0 loc_104C776E0 ; CODE XREF: decompression+50↑j __text:0000000104C776E0 17 17 18 0B ADD W23, W24, W24,LSL#5 __text:0000000104C776E4 E0 03 17 AA MOV X0, X23 __text:0000000104C776E8 A3 D2 00 94 BL malloc_0 __text:0000000104C776EC F3 03 00 AA MOV X19, X0 __text:0000000104C776F0 F8 0B 00 B9 STR W24, [SP,#0xA0+var_98] __text:0000000104C776F4 38 FE FF 34 CBZ W24, loc_104C776B8 __text:0000000104C776F8 18 00 80 52 MOV W24, #0 __text:0000000104C776FC 16 00 80 12 MOV W22, #0xFFFFFFFF __text:0000000104C77700 __text:0000000104C77700 loc_104C77700 ; CODE XREF: decompression+11C↓j __text:0000000104C77700 68 1E 40 F9 LDR X8, [X19,#0x38] __text:0000000104C77704 E0 03 13 AA MOV X0, X19 __text:0000000104C77708 00 01 3F D6 BLR X8 __text:0000000104C7770C E8 0B 40 F9 LDR X8, [SP,#0xA0+var_90] __text:0000000104C77710 A8 02 08 8B ADD X8, X21, X8 __text:0000000104C77714 E8 03 00 F9 STR X8, [SP,#0xA0+var_A0] __text:0000000104C77718 68 02 40 F9 LDR X8, [X19] __text:0000000104C7771C E8 0F 00 F9 STR X8, [SP,#0xA0+var_88] __text:0000000104C77720 68 0E 40 B9 LDR W8, [X19,#0xC] __text:0000000104C77724 E8 23 00 B9 STR W8, [SP,#0xA0+var_80] __text:0000000104C77728 E0 03 00 91 MOV X0, SP ; strm __text:0000000104C7772C 01 00 80 52 MOV W1, #0 ; flush __text:0000000104C77730 9F 06 08 94 BL _inflate __text:0000000104C77734 1F 04 00 71 CMP W0, #1 __text:0000000104C77738 68 02 00 54 B.HI loc_104C77784 __text:0000000104C7773C E9 0B 40 B9 LDR W9, [SP,#0xA0+var_98] __text:0000000104C77740 E8 03 17 AA MOV X8, X23 __text:0000000104C77744 69 00 00 35 CBNZ W9, loc_104C77750 __text:0000000104C77748 E8 2B 40 B9 LDR W8, [SP,#0xA0+var_78] __text:0000000104C7774C 08 03 08 0B ADD W8, W24, W8 __text:0000000104C77750 __text:0000000104C77750 loc_104C77750 ; CODE XREF: decompression+E4↑j __text:0000000104C77750 68 0A 00 B9 STR W8, [X19,#8] __text:0000000104C77754 88 2E 40 F9 LDR X8, [X20,#0x58] __text:0000000104C77758 E0 03 14 AA MOV X0, X20 __text:0000000104C7775C E1 03 13 AA MOV X1, X19 __text:0000000104C77760 00 01 3F D6 BLR X8 __text:0000000104C77764 E0 03 00 91 MOV X0, SP ; strm __text:0000000104C77768 94 06 08 94 BL _inflateEnd __text:0000000104C7776C 80 FA FF 35 CBNZ W0, loc_104C776BC __text:0000000104C77770 16 00 80 52 MOV W22, #0 __text:0000000104C77774 E8 0B 40 B9 LDR W8, [SP,#0xA0+var_98] __text:0000000104C77778 18 03 17 4B SUB W24, W24, W23 __text:0000000104C7777C 28 FC FF 35 CBNZ W8, loc_104C77700 __text:0000000104C77780 CF FF FF 17 B loc_104C776BC __text:0000000104C77784 ; --------------------------------------------------------------------------- __text:0000000104C77784 __text:0000000104C77784 loc_104C77784 ; CODE XREF: decompression+D8↑j __text:0000000104C77784 F6 03 00 AA MOV X22, X0 __text:0000000104C77788 CD FF FF 17 B loc_104C776BC
解析解压后的数据定位到bycode,根据标记bc_sgcipher定位后面的为bycode,部分数据如下:
开始数据,大小000000000001CB28 0000000146400000 01 00 01 00 D0 07 00 00 01 00 00 00 05 00 00 00 0000000146400010 1E 46 00 00 29 40 27 49 49 49 49 49 6A 71 00 00 0000000146400020 FC 7B 70 02 48 61 13 78 88 41 13 78 C8 21 13 78 0000000146400030 08 02 13 78 48 E3 12 78 88 C3 12 78 08 A4 12 78 0000000146400040 48 84 12 78 88 64 12 78 C8 44 12 78 08 25 12 78
3.5、虚拟机分析
+[JAQAVMPSignature avmpSign:input:]
客户端向服务器端发送数据时,需要调用avmpSign接口对整个body数据进行签名处理,所得到的签名串就是wToken。进入VM前对输入参数进行处理,对输入参数进行异或加密,代码如下:
__text:0000000104D9667C E0 7B C1 A8 LDP X0, X30, [SP],#0x10 ; 加密数据-进入VM __text:0000000104D96680 A8 83 5A F8 LDUR X8, [X29,#-0x58] __text:0000000104D96684 09 01 40 F9 LDR X9, [X8] __text:0000000104D96688 EA 07 7D B2 MOV X10, #0x18 __text:0000000104D9668C AB 03 56 F8 LDUR X11, [X29,#-0xA0] __text:0000000104D96690 6A 7D 0A 9B MUL X10, X11, X10 __text:0000000104D96694 AC 83 5E F8 LDUR X12, [X29,#-0x18] __text:0000000104D96698 8A 01 0A 8B ADD X10, X12, X10 __text:0000000104D9669C 4A 41 00 91 ADD X10, X10, #0x10 __text:0000000104D966A0 41 01 40 B9 LDR W1, [X10] __text:0000000104D966A4 A0 83 5D F8 LDUR X0, [X29,#-0x28] __text:0000000104D966A8 EA 3F 00 F9 STR X10, [SP,#0x78] __text:0000000104D966AC 20 01 3F D6 BLR X9 __text:0000000104D966B0 03 00 80 92 MOV X3, #0xFFFFFFFFFFFFFFFF __text:0000000104D966B4 E8 43 40 F9 LDR X8, [SP,#0x80] __text:0000000104D966B8 01 01 40 F9 LDR X1, [X8] __text:0000000104D966BC E9 3F 40 F9 LDR X9, [SP,#0x78] __text:0000000104D966C0 22 01 80 B9 LDRSW X2, [X9] __text:0000000104D966C4 E0 3B 00 F9 STR X0, [SP,#0x70] __text:0000000104D966C8 4F 88 03 94 BL ___memcpy_chk __text:0000000104D966CC A8 03 5A F8 LDUR X8, [X29,#-0x60] __text:0000000104D966D0 09 01 40 F9 LDR X9, [X8] __text:0000000104D966D4 EA 3F 40 F9 LDR X10, [SP,#0x78] __text:0000000104D966D8 42 01 40 B9 LDR W2, [X10] __text:0000000104D966DC AB 83 5D F8 LDUR X11, [X29,#-0x28] __text:0000000104D966E0 E0 37 00 F9 STR X0, [SP,#0x68] __text:0000000104D966E4 E0 03 0B AA MOV X0, X11 __text:0000000104D966E8 E1 3B 40 F9 LDR X1, [SP,#0x70] __text:0000000104D966EC 20 01 3F D6 BLR X9 ; 加密input数据R1 __text:0000000104D966F0 A8 03 5B F8 LDUR X8, [X29,#-0x50] __text:0000000104D966F4 09 01 40 F9 LDR X9, [X8] __text:0000000104D966F8 EA 3B 40 F9 LDR X10, [SP,#0x70] __text:0000000104D966FC 49 01 09 CB SUB X9, X10, X9 __text:0000000104D96700 E2 03 09 AA MOV X2, X9 __text:0000000104D96704 A0 83 5D F8 LDUR X0, [X29,#-0x28] __text:0000000104D96708 E0 7B BF A9 STP X0, X30, [SP,#-0x10]! __text:0000000104D9670C 40 00 00 18 LDR W0, =1 __text:0000000104D96710 73 FE FF 97 BL loc_104D960DC __text:0000000104D96710 ; --------------------------------------------------------------------------- __text:0000000104D96714 01 00 00 00 dword_104D96714 DCD 1 __text:0000000104D96718 ; --------------------------------------------------------------------------- __text:0000000104D96718 E0 7B C1 A8 LDP X0, X30, [SP],#0x10 __text:0000000104D9671C A1 03 1E B8 STUR W1, [X29,#-0x20] __text:0000000104D96720 A0 83 1D F8 STUR X0, [X29,#-0x28] __text:0000000104D96724 A4 43 1D B8 STUR W4, [X29,#-0x2C] __text:0000000104D96728 A8 83 1C F8 STUR X8, [X29,#-0x38] __text:0000000104D9672C A9 03 1C F8 STUR X9, [X29,#-0x40] __text:0000000104D96730 AA C3 1B B8 STUR W10, [X29,#-0x44] __text:0000000104D96734 80 01 00 54 B.EQ loc_104D96764 __text:0000000104D96738 08 00 80 D2 MOV X8, #0 __text:0000000104D9673C A9 83 5D F8 LDUR X9, [X29,#-0x28] __text:0000000104D96740 2A E1 01 91 ADD X10, X9, #0x78 ; 'x' __text:0000000104D96744 2B 81 02 91 ADD X11, X9, #0xA0 __text:0000000104D96748 AC 03 5C F8 LDUR X12, [X29,#-0x40] __text:0000000104D9674C 8D 61 02 91 ADD X13, X12, #0x98 __text:0000000104D96750 AD 03 1B F8 STUR X13, [X29,#-0x50] __text:0000000104D96754 AA 83 1A F8 STUR X10, [X29,#-0x58] __text:0000000104D96758 AB 03 1A F8 STUR X11, [X29,#-0x60] __text:0000000104D9675C A8 83 19 F8 STUR X8, [X29,#-0x68] __text:0000000104D96760 B9 FE FF 17 B loc_104D96244 __text:0000000104D96764 ; --------------------------------------------------------------------------- __text:0000000104D96764 __text:0000000104D96764 loc_104D96764 ; CODE XREF: __text:void std::__1::__tree_right_rotate<std::__1::__tree_node_base<void *> *>(std::__1::__tree_node_base<void *> *)+1D280↑j __text:0000000104D96764 ; __text:void std::__1::__tree_right_rotate<std::__1::__tree_node_base<void *> *>(std::__1::__tree_node_base<void *> *)+1D6E8↑j __text:0000000104D96764 A8 83 5D F8 LDUR X8, [X29,#-0x28] __text:0000000104D96768 09 19 40 F9 LDR X9, [X8,#0x30] __text:0000000104D9676C E0 03 08 AA MOV X0, X8 __text:0000000104D96770 A1 03 5E B8 LDUR W1, [X29,#-0x20] __text:0000000104D96774 20 01 3F D6 BLR X9 ; 进入VM __text:0000000104D96778 A1 43 5D B8 LDUR W1, [X29,#-0x2C]
要签名的请求体数据
00000001464203E0 64 61 74 61 3D 25 32 46 73 4B 34 48 57 6C 46 38 data=%2FsK4HWlF8 00000001464203F0 64 75 70 66 31 46 6A 46 6B 74 46 25 32 42 69 59 dupf1FjFktF%2BiY 0000000146420400 5A 56 73 77 75 47 34 76 42 75 41 68 41 43 4C 58 ZVswuG4vBuAhACLX 0000000146420410 51 4C 6F 4D 38 66 6E 79 55 6B 6B 71 64 47 43 31 QLoM8fnyUkkqdGC1 0000000146420420 51 6E 34 43 6C 4D 61 4B 7A 25 30 44 25 30 41 52 Qn4ClMaKz%0D%0AR 0000000146420430 54 25 32 42 66 46 65 72 58 54 32 71 6F 6F 34 5A T%2BfFerXT2qoo4Z 0000000146420440 41 31 33 76 72 6D 46 4A 72 78 61 44 47 48 44 50 A13vrmFJrxaDGHDP 0000000146420450 41 41 67 37 54 55 64 6F 53 41 41 55 69 33 41 6C AAg7TUdoSAAUi3Al 0000000146420460 6B 65 33 38 25 32 46 76 79 65 25 32 46 25 32 42 ke38%2Fvye%2F%2B 0000000146420470 4D 25 32 42 68 74 25 32 46 4C 7A 25 30 44 25 30 M%2Bht%2FLz%0D%0 0000000146420480 41 56 6C 6F 6D 66 61 75 4D 72 30 51 49 51 58 41 AVlomfauMr0QIQXA 0000000146420490 35 4D 78 69 76 6C 30 45 45 47 34 50 59 46 51 75 5Mxivl0EEG4PYFQu 00000001464204A0 73 6A 5A 6C 72 34 47 4A 5A 66 4E 54 4A 4F 6A 48 sjZlr4GJZfNTJOjH 00000001464204B0 52 6F 6F 35 62 51 6C 41 59 71 42 31 49 6F 70 30 Roo5bQlAYqB1Iop0 00000001464204C0 4A 25 30 44 25 30 41 48 6D 51 6A 43 61 32 4D 43 J%0D%0AHmQjCa2MC 00000001464204D0 42 6C 77 37 65 25 32 46 31 37 36 43 56 47 79 41 Blw7e%2F176CVGyA 00000001464204E0 79 57 6F 38 38 50 39 59 54 57 63 46 25 32 42 53 yWo88P9YTWcF%2BS 00000001464204F0 4D 31 62 34 64 35 35 76 25 32 46 48 68 64 59 41 M1b4d55v%2FHhdYA 0000000146420500 79 42 41 36 69 32 33 61 44 6D 74 48 79 25 30 44 yBA6i23aDmtHy%0D 0000000146420510 25 30 41 61 31 35 76 72 63 25 32 46 44 4D 6C 42 %0Aa15vrc%2FDMlB 0000000146420520 76 6A 79 49 6E 71 4D 76 48 4D 58 4A 43 47 39 44 vjyInqMvHMXJCG9D 0000000146420530 4E 4F 30 7A 6A 66 7A 43 4E 72 46 42 33 33 6B 51 NO0zjfzCNrFB33kQ 0000000146420540 56 39 58 72 44 73 50 79 42 52 64 4D 67 57 38 38 V9XrDsPyBRdMgW88 0000000146420550 61 49 37 64 50 25 30 44 25 30 41 47 44 66 51 46 aI7dP%0D%0AGDfQF 0000000146420560 6F 4B 32 71 41 50 34 39 68 79 50 4F 77 33 49 44 oK2qAP49hyPOw3ID 0000000146420570 46 56 33 72 73 62 39 55 30 6B 39 25 32 46 30 25 FV3rsb9U0k9%2F0% 0000000146420580 32 42 77 50 63 34 45 56 25 32 42 70 25 32 42 30 2BwPc4EV%2Bp%2B0 0000000146420590 25 32 46 75 58 6E 47 75 61 58 59 57 6B 69 52 50 %2FuXnGuaXYWkiRP 00000001464205A0 52 71 54 39 6A 25 30 44 25 30 41 67 6F 52 79 39 RqT9j%0D%0AgoRy9 00000001464205B0 33 6E 34 43 37 51 55 64 25 32 42 65 33 33 30 56 3n4C7QUd%2Be330V 00000001464205C0 4C 68 50 74 46 6D 47 5A 5A 39 6F 6F 6F 7A 50 53 LhPtFmGZZ9ooozPS 00000001464205D0 55 4E 4E 45 70 64 61 56 46 31 77 43 6E 66 42 54 UNNEpdaVF1wCnfBT 00000001464205E0 69 74 45 25 32 46 4B 4E 50 25 32 46 46 25 32 46 itE%2FKNP%2FF%2F 00000001464205F0 52 54 25 32 42 25 30 44 25 30 41 57 61 54 6C 41 RT%2B%0D%0AWaTlA 0000000146420600 5A 73 71 30 64 52 54 6F 41 69 4D 54 52 49 45 68 Zsq0dRToAiMTRIEh 0000000146420610 75 45 6D 4A 4C 72 42 70 4F 4D 43 73 74 54 25 32 uEmJLrBpOMCstT%2 0000000146420620 46 33 6E 4A 6C 78 68 59 4D 4B 41 6D 30 44 5A 59 F3nJlxhYMKAm0DZY 0000000146420630 57 53 6D 31 54 65 68 70 70 75 6F 4E 4A 25 30 44 WSm1TehppuoNJ%0D 0000000146420640 25 30 41 35 64 5A 51 64 36 49 51 75 6C 65 51 63 %0A5dZQd6IQuleQc 0000000146420650 46 71 4B 4A 39 42 31 46 46 52 63 49 41 69 39 35 FqKJ9B1FFRcIAi95 0000000146420660 33 57 65 33 78 6E 6F 32 37 4C 68 55 4E 56 47 4B 3We3xno27LhUNVGK 0000000146420670 34 44 49 79 4E 71 6A 39 36 48 4B 79 63 34 63 78 4DIyNqj96HKyc4cx 0000000146420680 32 4A 7A 25 30 44 25 30 41 52 4C 4E 52 52 44 56 2Jz%0D%0ARLNRRDV 0000000146420690 41 4E 46 49 47 43 72 47 6F 25 32 46 56 44 42 31 ANFIGCrGo%2FVDB1 00000001464206A0 38 64 76 41 41 36 4D 68 66 63 45 6B 4D 41 6E 55 8dvAA6MhfcEkMAnU 00000001464206B0 63 55 41 66 45 36 62 33 4B 74 58 71 56 42 4A 44 cUAfE6b3KtXqVBJD 00000001464206C0 61 73 36 73 62 44 33 50 43 70 70 00 00 00 00 00 as6sbD3PCpp
当参数准备好后将进入VM,代码如下:
__text:0000000104D89A38 E0 7B C1 A8 LDP X0, X30, [SP+arg_0],#0x10 __text:0000000104D89A3C FC 6F BD A9 STP X28, X27, [SP,#-0x10+var_20]! __text:0000000104D89A40 F4 4F 01 A9 STP X20, X19, [SP,#0x20+var_10] __text:0000000104D89A44 FD 7B 02 A9 STP X29, X30, [SP,#0x20+arg_0] __text:0000000104D89A48 FD 83 00 91 ADD X29, SP, #0x20+arg_0 __text:0000000104D89A4C FF C3 0C D1 SUB SP, SP, #0x330 __text:0000000104D89A50 08 00 80 D2 MOV X8, #0 __text:0000000104D89A54 09 00 80 12 MOV W9, #0xFFFFFFFF __text:0000000104D89A58 AA 83 02 D1 SUB X10, X29, #0xA0 ; 分配空间 __text:0000000104D89A5C AB 93 02 D1 SUB X11, X29, #0xA4 ; 分配空间 __text:0000000104D89A60 E2 03 0A AA MOV X2, X10 __text:0000000104D89A64 0C E0 02 91 ADD X12, X0, #0xB8 __text:0000000104D89A68 0D 5C 40 F9 LDR X13, [X0,#0xB8] __text:0000000104D89A6C 0E AC 83 D2 MOV X14, #0x1D60 __text:0000000104D89A70 AE 01 0E 8B ADD X14, X13, X14 __text:0000000104D89A74 A9 61 1D B9 STR W9, [X13,#0x1D60] __text:0000000104D89A78 BF C3 15 B8 STUR WZR, [X29,#-0xA4] __text:0000000104D89A7C AF 49 40 F9 LDR X15, [X13,#0x90] __text:0000000104D89A80 B0 4D 40 F9 LDR X16, [X13,#0x98] __text:0000000104D89A84 B1 81 42 39 LDRB W17, [X13,#0xA0] __text:0000000104D89A88 23 1E 00 53 UXTB W3, W17 __text:0000000104D89A8C 64 20 03 2A ORR W4, W3, W3,LSL#8 __text:0000000104D89A90 85 3C 10 53 LSL W5, W4, #0x10 __text:0000000104D89A94 E6 03 01 AA MOV X6, X1 __text:0000000104D89A98 C6 7C 40 D3 UBFX X6, X6, #0, #0x20 ; ' ' __text:0000000104D89A9C A7 45 40 F9 LDR X7, [X13,#0x88] __text:0000000104D89AA0 F3 03 7E B2 MOV X19, #4 __text:0000000104D89AA4 C6 7C 13 9B MUL X6, X6, X19 __text:0000000104D89AA8 E6 00 06 8B ADD X6, X7, X6 __text:0000000104D89AAC C1 00 40 B9 LDR W1, [X6] __text:0000000104D89AB0 B4 AD 40 B9 LDR W20, [X13,#0xAC] __text:0000000104D89AB4 94 22 00 51 SUB W20, W20, #8 __text:0000000104D89AB8 46 F1 00 91 ADD X6, X10, #0x3C ; '<' __text:0000000104D89ABC B4 C3 19 B8 STUR W20, [X29,#-0x64] __text:0000000104D89AC0 B4 83 19 B8 STUR W20, [X29,#-0x68] __text:0000000104D89AC4 4A D1 00 91 ADD X10, X10, #0x34 ; '4' __text:0000000104D89AC8 A9 43 19 B8 STUR W9, [X29,#-0x6C] __text:0000000104D89ACC A0 03 15 F8 STUR X0, [X29,#-0xB0] __text:0000000104D89AD0 A5 C3 14 B8 STUR W5, [X29,#-0xB4] __text:0000000104D89AD4 A1 83 14 B8 STUR W1, [X29,#-0xB8] __text:0000000104D89AD8 AA 03 14 F8 STUR X10, [X29,#-0xC0] __text:0000000104D89ADC A6 83 13 F8 STUR X6, [X29,#-0xC8] __text:0000000104D89AE0 AE 03 13 F8 STUR X14, [X29,#-0xD0] __text:0000000104D89AE4 A2 83 12 F8 STUR X2, [X29,#-0xD8] __text:0000000104D89AE8 AC 03 12 F8 STUR X12, [X29,#-0xE0] __text:0000000104D89AEC AD 83 11 F8 STUR X13, [X29,#-0xE8] __text:0000000104D89AF0 AB 03 11 F8 STUR X11, [X29,#-0xF0] __text:0000000104D89AF4 AF 83 10 F8 STUR X15, [X29,#-0xF8] __text:0000000104D89AF8 B0 03 10 F8 STUR X16, [X29,#-0x100] __text:0000000104D89AFC F1 4F 02 B9 STR W17, [SP,#0x350+xorkey1] __text:0000000104D89B00 E3 4B 02 B9 STR W3, [SP,#0x350+xorkey2] __text:0000000104D89B04 E4 47 02 B9 STR W4, [SP,#0x350+var_10C] __text:0000000104D89B08 E8 1F 01 F9 STR X8, [SP,#0x350+var_118] __text:0000000104D89B0C __text:0000000104D89B0C loc_104D89B0C ; CODE XREF: VM2+128↓j __text:0000000104D89B0C E8 1F 41 F9 LDR X8, [SP,#0x350+var_118] __text:0000000104D89B10 E9 0F 40 B2 MOV X9, #0xF __text:0000000104D89B14 EA 0B 7F B2 MOV X10, #0xE __text:0000000104D89B18 4A 01 08 CB SUB X10, X10, X8 __text:0000000104D89B1C 0B AC 83 D2 MOV X11, #0x1D60 __text:0000000104D89B20 AC 83 51 F8 LDUR X12, [X29,#-0xE8] __text:0000000104D89B24 8B 01 0B 8B ADD X11, X12, X11 __text:0000000104D89B28 ED 03 7E B2 MOV X13, #4 __text:0000000104D89B2C 4A 7D 0D 9B MUL X10, X10, X13 __text:0000000104D89B30 6A 01 0A 8B ADD X10, X11, X10 __text:0000000104D89B34 4E 01 40 B9 LDR W14, [X10] __text:0000000104D89B38 29 01 08 CB SUB X9, X9, X8 __text:0000000104D89B3C 0A AC 83 D2 MOV X10, #0x1D60 __text:0000000104D89B40 8A 01 0A 8B ADD X10, X12, X10 __text:0000000104D89B44 EB 03 7E B2 MOV X11, #4 __text:0000000104D89B48 29 7D 0B 9B MUL X9, X9, X11 __text:0000000104D89B4C 49 01 09 8B ADD X9, X10, X9 __text:0000000104D89B50 2E 01 00 B9 STR W14, [X9] __text:0000000104D89B54 08 05 00 91 ADD X8, X8, #1 __text:0000000104D89B58 1F 3D 00 F1 CMP X8, #0xF __text:0000000104D89B5C E8 1F 01 F9 STR X8, [SP,#0x350+var_118] __text:0000000104D89B60 61 FD FF 54 B.NE loc_104D89B0C __text:0000000104D89B64 A8 83 02 D1 SUB X8, X29, #0xA0 __text:0000000104D89B68 A9 C3 54 B8 LDUR W9, [X29,#-0xB4] __text:0000000104D89B6C EA 47 42 B9 LDR W10, [SP,#0x350+var_10C] __text:0000000104D89B70 2B 01 0A 2A ORR W11, W9, W10 __text:0000000104D89B74 AC 83 54 B8 LDUR W12, [X29,#-0xB8] __text:0000000104D89B78 AD 03 53 F8 LDUR X13, [X29,#-0xD0] __text:0000000104D89B7C AC 01 00 B9 STR W12, [X13] __text:0000000104D89B80 08 C1 00 91 ADD X8, X8, #0x30 ; '0' __text:0000000104D89B84 2E 7D 10 13 ASR W14, W9, #0x10 __text:0000000104D89B88 8F B3 83 D2 MOV X15, #0x1D9C __text:0000000104D89B8C B0 83 51 F8 LDUR X16, [X29,#-0xE8] __text:0000000104D89B90 0F 02 0F 8B ADD X15, X16, X15 __text:0000000104D89B94 EB 37 02 B9 STR W11, [SP,#0x350+xorkey] __text:0000000104D89B98 EC 33 02 B9 STR W12, [SP,#0x350+var_120] __text:0000000104D89B9C E8 17 01 F9 STR X8, [SP,#0x350+ZF] __text:0000000104D89BA0 EE 27 02 B9 STR W14, [SP,#0x350+var_12C] __text:0000000104D89BA4 EF 0F 01 F9 STR X15, [SP,#0x350+var_138] __text:0000000104D89BA8 __text:0000000104D89BA8 loc_104D89BA8 ; CODE XREF: VM2+293C↓j __text:0000000104D89BA8 E8 33 42 B9 LDR W8, [SP,#0x350+var_120] ; VM分发器 __text:0000000104D89BAC A9 83 50 F8 LDUR X9, [X29,#-0xF8] ; bycode地址 __text:0000000104D89BB0 2A 59 68 B8 LDR W10, [X9,W8,UXTW#2] ; index __text:0000000104D89BB4 EB 03 0A AA MOV X11, X10 __text:0000000104D89BB8 4A 15 00 12 AND W10, W10, #0x3F __text:0000000104D89BBC EC 03 0A AA MOV X12, X10 __text:0000000104D89BC0 4A FD 00 71 SUBS W10, W10, #0x3F ; switch 64 cases __text:0000000104D89BC4 E8 17 02 B9 STR W8, [SP,#0x350+var_13C] ; bycodeindex __text:0000000104D89BC8 EB 13 02 B9 STR W11, [SP,#0x350+var_140] __text:0000000104D89BCC EC 07 01 F9 STR X12, [SP,#0x350+var_148] __text:0000000104D89BD0 EA 07 02 B9 STR W10, [SP,#0x350+var_14C] __text:0000000104D89BD4 28 31 01 54 B.HI Handle_13_16_21_29_45_53_61_index ; jumptable 0000000100C51BEC default case __text:0000000104D89BD4 ; jumptable 0000000104D89BEC default case, cases 13,16,21,29,45,53,61 __text:0000000104D89BD8 08 00 00 F0+ADRL X8, 0x104D8C3E0 __text:0000000104D89BD8 08 81 0F 91 __text:0000000104D89BE0 E9 07 41 F9 LDR X9, [SP,#0x350+var_148] __text:0000000104D89BE4 0A 79 A9 B8 LDRSW X10, [X8,X9,LSL#2] ; x8为hander表首地址 __text:0000000104D89BE8 48 01 08 8B ADD X8, X10, X8 __text:0000000104D89BEC 00 01 1F D6 BR X8 ; switch jump
该VM的Handle有70个左右,下面Handle表,有部分Handle己经根据功能命名了,如下:
_text:0000000104D8C3E0 E0 D9 FF FF jpt_100C51BEC DCD Handle_0_LSL - 0x104D8C3E0 ; jump table for switch statement __text:0000000104D8C3E4 10 D8 FF FF DCD Handle_1_9_17_25_33_41_49_57 - 0x104D8C3E0 ; jumptable 0000000100C51BEC cases 1,9,17,25,33,41,49,57 __text:0000000104D8C3E4 ; jumptable 0000000104D89BEC cases 1,9,17,25,33,41,49,57 __text:0000000104D8C3E8 E8 DD FF FF DCD Handle_2_2_CallFunc - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 2 __text:0000000104D8C3E8 ; jumptable 0000000104D89BEC case 2 __text:0000000104D8C3EC 54 EC FF FF DCD Handle_3_0 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 3 __text:0000000104D8C3EC ; jumptable 0000000104D89BEC case 3 __text:0000000104D8C3F0 98 F6 FF FF DCD Handle_4_MUL_ADD - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 4 __text:0000000104D8C3F0 ; jumptable 0000000104D89BEC case 4 __text:0000000104D8C3F4 64 E4 FF FF DCD Handle_5_1 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 5 __text:0000000104D8C3F4 ; jumptable 0000000104D89BEC case 5 __text:0000000104D8C3F8 40 EB FF FF DCD Handle_6_0 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 6 __text:0000000104D8C3F8 ; jumptable 0000000104D89BEC case 6 __text:0000000104D8C3FC DC F2 FF FF DCD Handle_7_0 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 7 __text:0000000104D8C3FC ; jumptable 0000000104D89BEC case 7 __text:0000000104D8C400 74 FC FF FF DCD Handle_8_EOR - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 8 __text:0000000104D8C400 ; jumptable 0000000104D89BEC case 8 __text:0000000104D8C404 10 D8 FF FF DCD Handle_1_9_17_25_33_41_49_57 - 0x104D8C3E0 ; jumptable 0000000100C51BEC cases 1,9,17,25,33,41,49,57 __text:0000000104D8C404 ; jumptable 0000000104D89BEC cases 1,9,17,25,33,41,49,57 __text:0000000104D8C408 1C F1 FF FF DCD Handle_10 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 10 __text:0000000104D8C408 ; jumptable 0000000104D89BEC case 10 __text:0000000104D8C40C 88 ED FF FF DCD Handle_11 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 11 __text:0000000104D8C40C ; jumptable 0000000104D89BEC case 11 __text:0000000104D8C410 74 F3 FF FF DCD Handle_12_F - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 12 __text:0000000104D8C410 ; jumptable 0000000104D89BEC case 12 __text:0000000104D8C414 18 FE FF FF DCD Handle_13_16_21_29_45_53_61_index - 0x104D8C3E0 ; jumptable 0000000100C51BEC default case __text:0000000104D8C414 ; jumptable 0000000104D89BEC default case, cases 13,16,21,29,45,53,61 __text:0000000104D8C418 BC EB FF FF DCD Handle_14 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 14 __text:0000000104D8C418 ; jumptable 0000000104D89BEC case 14 __text:0000000104D8C41C 44 FB FF FF DCD Handle_15 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 15 __text:0000000104D8C41C ; jumptable 0000000104D89BEC case 15 __text:0000000104D8C420 18 FE FF FF DCD Handle_13_16_21_29_45_53_61_index - 0x104D8C3E0 ; jumptable 0000000100C51BEC default case __text:0000000104D8C420 ; jumptable 0000000104D89BEC default case, cases 13,16,21,29,45,53,61 __text:0000000104D8C424 10 D8 FF FF DCD Handle_1_9_17_25_33_41_49_57 - 0x104D8C3E0 ; jumptable 0000000100C51BEC cases 1,9,17,25,33,41,49,57 __text:0000000104D8C424 ; jumptable 0000000104D89BEC cases 1,9,17,25,33,41,49,57 __text:0000000104D8C428 78 F1 FF FF DCD Handle_18 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 18 __text:0000000104D8C428 ; jumptable 0000000104D89BEC case 18 __text:0000000104D8C42C 04 EA FF FF DCD Handle_19 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 19 __text:0000000104D8C42C ; jumptable 0000000104D89BEC case 19 __text:0000000104D8C430 84 D9 FF FF DCD Handle_20 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 20 __text:0000000104D8C430 ; jumptable 0000000104D89BEC case 20 __text:0000000104D8C434 18 FE FF FF DCD Handle_13_16_21_29_45_53_61_index - 0x104D8C3E0 ; jumptable 0000000100C51BEC default case __text:0000000104D8C434 ; jumptable 0000000104D89BEC default case, cases 13,16,21,29,45,53,61 __text:0000000104D8C438 D4 EC FF FF DCD Handle_22 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 22 __text:0000000104D8C438 ; jumptable 0000000104D89BEC case 22 __text:0000000104D8C43C 28 F5 FF FF DCD Handle_23 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 23 __text:0000000104D8C43C ; jumptable 0000000104D89BEC case 23 __text:0000000104D8C440 C4 DC FF FF DCD Handle_24_AND_EOR - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 24 __text:0000000104D8C440 ; jumptable 0000000104D89BEC case 24 __text:0000000104D8C444 10 D8 FF FF DCD Handle_1_9_17_25_33_41_49_57 - 0x104D8C3E0 ; jumptable 0000000100C51BEC cases 1,9,17,25,33,41,49,57 __text:0000000104D8C444 ; jumptable 0000000104D89BEC cases 1,9,17,25,33,41,49,57 __text:0000000104D8C448 CC DD FF FF DCD Handle_26 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 26 __text:0000000104D8C448 ; jumptable 0000000104D89BEC case 26 __text:0000000104D8C44C 10 F2 FF FF DCD Handle_27 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 27 __text:0000000104D8C44C ; jumptable 0000000104D89BEC case 27 __text:0000000104D8C450 A8 DB FF FF DCD Handle_28 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 28 __text:0000000104D8C450 ; jumptable 0000000104D89BEC case 28 __text:0000000104D8C454 18 FE FF FF DCD Handle_13_16_21_29_45_53_61_index - 0x104D8C3E0 ; jumptable 0000000100C51BEC default case __text:0000000104D8C454 ; jumptable 0000000104D89BEC default case, cases 13,16,21,29,45,53,61 __text:0000000104D8C458 94 E1 FF FF DCD Handle_30 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 30 __text:0000000104D8C458 ; jumptable 0000000104D89BEC case 30 __text:0000000104D8C45C B8 D8 FF FF DCD Handle_31 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 31 __text:0000000104D8C45C ; jumptable 0000000104D89BEC case 31 __text:0000000104D8C460 98 FD FF FF DCD Handle_32_LSR - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 32 __text:0000000104D8C460 ; jumptable 0000000104D89BEC case 32 __text:0000000104D8C464 10 D8 FF FF DCD Handle_1_9_17_25_33_41_49_57 - 0x104D8C3E0 ; jumptable 0000000100C51BEC cases 1,9,17,25,33,41,49,57 __text:0000000104D8C464 ; jumptable 0000000104D89BEC cases 1,9,17,25,33,41,49,57 __text:0000000104D8C468 60 DA FF FF DCD Handle_34 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 34 __text:0000000104D8C468 ; jumptable 0000000104D89BEC case 34 __text:0000000104D8C46C 80 E0 FF FF DCD Handle_35 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 35 __text:0000000104D8C46C ; jumptable 0000000104D89BEC case 35 __text:0000000104D8C470 C8 F5 FF FF DCD Handle_36_isZF - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 36 __text:0000000104D8C470 ; jumptable 0000000104D89BEC case 36 __text:0000000104D8C474 C0 EE FF FF DCD Handle_37 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 37 __text:0000000104D8C474 ; jumptable 0000000104D89BEC case 37 __text:0000000104D8C478 54 DF FF FF DCD Handle_38 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 38 __text:0000000104D8C478 ; jumptable 0000000104D89BEC case 38 __text:0000000104D8C47C 90 F4 FF FF DCD Handle_39 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 39 __text:0000000104D8C47C ; jumptable 0000000104D89BEC case 39 __text:0000000104D8C480 DC FB FF FF DCD Handle_40_genOffset - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 40 __text:0000000104D8C480 ; jumptable 0000000104D89BEC case 40 __text:0000000104D8C484 10 D8 FF FF DCD Handle_1_9_17_25_33_41_49_57 - 0x104D8C3E0 ; jumptable 0000000100C51BEC cases 1,9,17,25,33,41,49,57 __text:0000000104D8C484 ; jumptable 0000000104D89BEC cases 1,9,17,25,33,41,49,57 __text:0000000104D8C488 44 EE FF FF DCD Handle_42_ORR - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 42 __text:0000000104D8C488 ; jumptable 0000000104D89BEC case 42 __text:0000000104D8C48C 3C EF FF FF DCD Handle_43 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 43 __text:0000000104D8C48C ; jumptable 0000000104D89BEC case 43 __text:0000000104D8C490 B8 EF FF FF DCD Handle_44_getValue - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 44 __text:0000000104D8C490 ; jumptable 0000000104D89BEC case 44 __text:0000000104D8C494 18 FE FF FF DCD Handle_13_16_21_29_45_53_61_index - 0x104D8C3E0 ; jumptable 0000000100C51BEC default case __text:0000000104D8C494 ; jumptable 0000000104D89BEC default case, cases 13,16,21,29,45,53,61 __text:0000000104D8C498 18 E1 FF FF DCD Handle_46 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 46 __text:0000000104D8C498 ; jumptable 0000000104D89BEC case 46 __text:0000000104D8C49C 10 DB FF FF DCD Handle_47 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 47 __text:0000000104D8C49C ; jumptable 0000000104D89BEC case 47 __text:0000000104D8C4A0 AC F7 FF FF DCD Handle_48_JMP - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 48 __text:0000000104D8C4A0 ; jumptable 0000000104D89BEC case 48 __text:0000000104D8C4A4 10 D8 FF FF DCD Handle_1_9_17_25_33_41_49_57 - 0x104D8C3E0 ; jumptable 0000000100C51BEC cases 1,9,17,25,33,41,49,57 __text:0000000104D8C4A4 ; jumptable 0000000104D89BEC cases 1,9,17,25,33,41,49,57 __text:0000000104D8C4A8 64 DD FF FF DCD Handle_50 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 50 __text:0000000104D8C4A8 ; jumptable 0000000104D89BEC case 50 __text:0000000104D8C4AC BC DE FF FF DCD Handle_51 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 51 __text:0000000104D8C4AC ; jumptable 0000000104D89BEC case 51 __text:0000000104D8C4B0 14 F4 FF FF DCD Handle_52_EOR - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 52 __text:0000000104D8C4B0 ; jumptable 0000000104D89BEC case 52 __text:0000000104D8C4B4 18 FE FF FF DCD Handle_13_16_21_29_45_53_61_index - 0x104D8C3E0 ; jumptable 0000000100C51BEC default case __text:0000000104D8C4B4 ; jumptable 0000000104D89BEC default case, cases 13,16,21,29,45,53,61 __text:0000000104D8C4B8 9C EA FF FF DCD Handle_54 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 54 __text:0000000104D8C4B8 ; jumptable 0000000104D89BEC case 54 __text:0000000104D8C4BC 00 F6 FF FF DCD Handle_55 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 55 __text:0000000104D8C4BC ; jumptable 0000000104D89BEC case 55 __text:0000000104D8C4C0 0C F7 FF FF DCD Handle_56 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 56 __text:0000000104D8C4C0 ; jumptable 0000000104D89BEC case 56 __text:0000000104D8C4C4 10 D8 FF FF DCD Handle_1_9_17_25_33_41_49_57 - 0x104D8C3E0 ; jumptable 0000000100C51BEC cases 1,9,17,25,33,41,49,57 __text:0000000104D8C4C4 ; jumptable 0000000104D89BEC cases 1,9,17,25,33,41,49,57 __text:0000000104D8C4C8 D8 DF FF FF DCD Handle_58 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 58 __text:0000000104D8C4C8 ; jumptable 0000000104D89BEC case 58 __text:0000000104D8C4CC 60 F0 FF FF DCD Handle_59 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 59 __text:0000000104D8C4CC ; jumptable 0000000104D89BEC case 59 __text:0000000104D8C4D0 4C DC FF FF DCD Handle_60 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 60 __text:0000000104D8C4D0 ; jumptable 0000000104D89BEC case 60 __text:0000000104D8C4D4 18 FE FF FF DCD Handle_13_16_21_29_45_53_61_index - 0x104D8C3E0 ; jumptable 0000000100C51BEC default case __text:0000000104D8C4D4 ; jumptable 0000000104D89BEC default case, cases 13,16,21,29,45,53,61 __text:0000000104D8C4D8 78 E9 FF FF DCD Handle_62 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 62 __text:0000000104D8C4D8 ; jumptable 0000000104D89BEC case 62 __text:0000000104D8C4DC F0 FC FF FF DCD Handle_63 - 0x104D8C3E0 ; jumptable 0000000100C51BEC case 63 __text:0000000104D8C4DC ; jumptable 0000000104D89BEC case 63 __text:0000000104D8C4E0 F0 F6 FF FF jpt_100C53BCC DCD Handle_0 - 0x104D8C4E0 ; jump table for switch statement __text:0000000104D8C4E4 44 F7 FF FF DCD Handle_1 - 0x104D8C4E0 ; jumptable 0000000100C53BCC case 1 __text:0000000104D8C4E4 ; jumptable 0000000104D8BBCC case 1 __text:0000000104D8C4E8 98 F7 FF FF DCD Handle_2 - 0x104D8C4E0 ; jumptable 0000000100C53BCC case 2 __text:0000000104D8C4E8 ; jumptable 0000000104D8BBCC case 2 __text:0000000104D8C4EC EC F7 FF FF DCD Handle_3 - 0x104D8C4E0 ; jumptable 0000000100C53BCC case 3 __text:0000000104D8C4EC ; jumptable 0000000104D8BBCC case 3 __text:0000000104D8C4F0 40 F8 FF FF DCD Handle_4_Cmp - 0x104D8C4E0 ; jumptable 0000000100C53BCC case 4 __text:0000000104D8C4F0 ; jumptable 0000000104D8BBCC case 4 __text:0000000104D8C4F4 94 F8 FF FF DCD Handle_5_CMP - 0x104D8C4E0 ; jumptable 0000000100C53BCC case 5 __text:0000000104D8C4F4 ; jumptable 0000000104D8BBCC case 5 __text:0000000104D8C4F8 E8 F8 FF FF DCD Handle_6_CmpIndex - 0x104D8C4E0 ; jumptable 0000000100C53BCC case 6 __text:0000000104D8C4F8 ; jumptable 0000000104D8BBCC case 6 __text:0000000104D8C4FC 3C F9 FF FF DCD Handle_7_Cmp - 0x104D8C4E0 ; jumptable 0000000100C53BCC case 7 __text:0000000104D8C4FC ; jumptable 0000000104D8BBCC case 7 __text:0000000104D8C500 90 F9 FF FF DCD Handle_8_0_CmpEnd - 0x104D8C4E0 ; jumptable 0000000100C53BCC case 8 __text:0000000104D8C500 ; jumptable 0000000104D8BBCC case 8 __text:0000000104D8C504 E4 F9 FF FF DCD Handle_9_CmpIndex - 0x104D8C4E0 ; jumptable 0000000100C53BCC case 9 __text:0000000104D8C504 ; jumptable 0000000104D8BBCC case 9 __text:0000000104D8C508 4C E6 FF FF jpt_100C528F8 DCD Handle_0_0 - 0x104D8C508 ; jump table for switch statement __text:0000000104D8C50C 84 E5 FF FF DCD Handle_1_0 - 0x104D8C508 ; jumptable 0000000100C528F8 case 1 __text:0000000104D8C50C ; jumptable 0000000104D8A8F8 case 1 __text:0000000104D8C510 9C E5 FF FF DCD Handle_2_0 - 0x104D8C508 ; jumptable 0000000100C528F8 case 2 __text:0000000104D8C510 ; jumptable 0000000104D8A8F8 case 2 __text:0000000104D8C514 7C E4 FF FF DCD Handle_3_1 - 0x104D8C508 ; jumptable 0000000100C528F8 case 3 __text:0000000104D8C514 ; jumptable 0000000104D8A8F8 case 3 __text:0000000104D8C518 9C E7 FF FF DCD Handle_4_1 - 0x104D8C508 ; jumptable 0000000100C528F8 case 4 __text:0000000104D8C518 ; jumptable 0000000104D8A8F8 case 4 __text:0000000104D8C51C D8 E4 FF FF DCD Handle_5_0 - 0x104D8C508 ; jumptable 0000000100C528F8 case 5 __text:0000000104D8C51C ; jumptable 0000000104D8A8F8 case 5 __text:0000000104D8C520 9C E6 FF FF DCD Handle_6_1 - 0x104D8C508 ; jumptable 0000000100C528F8 case 6 __text:0000000104D8C520 ; jumptable 0000000104D8A8F8 case 6 __text:0000000104D8C524 90 E5 FF FF DCD Handle_7_1 - 0x104D8C508 ; jumptable 0000000100C528F8 case 7 __text:0000000104D8C524 ; jumptable 0000000104D8A8F8 case 7 __text:0000000104D8C528 8C E6 FF FF DCD Handle_8_1 - 0x104D8C508 ; jumptable 0000000100C528F8 case 8 __text:0000000104D8C528 ; jumptable 0000000104D8A8F8 case 8 __text:0000000104D8C52C B8 E3 FF FF DCD Handle_9_0 - 0x104D8C508 ; jumptable 0000000100C528F8 default case __text:0000000104D8C52C ; jumptable 0000000104D8A8F8 default case, case 9 __text:0000000104D8C530 DC E6 FF FF DCD Handle_10_0 - 0x104D8C508 ; jumptable 0000000100C528F8 case 10 __text:0000000104D8C530 ; jumptable 0000000104D8A8F8 case 10 __text:0000000104D8C534 F4 E3 FF FF DCD Handle_11_0 - 0x104D8C508 ; jumptable 0000000100C528F8 case 11 __text:0000000104D8C534 ; jumptable 0000000104D8A8F8 case 11 __text:0000000104D8C538 80 E0 FF FF jpt_100C525B4 DCD Handle_0_1 - 0x104D8C538 ; jump table for switch statement __text:0000000104D8C53C C0 E0 FF FF DCD Handle_1_1 - 0x104D8C538 ; jumptable 0000000100C525B4 case 1 __text:0000000104D8C53C ; jumptable 0000000104D8A5B4 case 1 __text:0000000104D8C540 00 E1 FF FF DCD Handle_2_1 - 0x104D8C538 ; jumptable 0000000100C525B4 case 2 __text:0000000104D8C540 ; jumptable 0000000104D8A5B4 case 2 __text:0000000104D8C544 40 E1 FF FF DCD Handle_3_2 - 0x104D8C538 ; jumptable 0000000100C525B4 case 3 __text:0000000104D8C544 ; jumptable 0000000104D8A5B4 case 3 __text:0000000104D8C548 80 E1 FF FF DCD Handle_4_2 - 0x104D8C538 ; jumptable 0000000100C525B4 case 4 __text:0000000104D8C548 ; jumptable 0000000104D8A5B4 case 4 __text:0000000104D8C54C C0 E1 FF FF DCD Handle_5_2 - 0x104D8C538 ; jumptable 0000000100C525B4 case 5 __text:0000000104D8C54C ; jumptable 0000000104D8A5B4 case 5 __text:0000000104D8C550 00 E2 FF FF DCD Handle_6_2 - 0x104D8C538 ; jumptable 0000000100C525B4 case 6 __text:0000000104D8C550 ; jumptable 0000000104D8A5B4 case 6 __text:0000000104D8C554 40 E2 FF FF DCD Handle_7_2 - 0x104D8C538 ; jumptable 0000000100C525B4 case 7 __text:0000000104D8C554 ; jumptable 0000000104D8A5B4 case 7 __text:0000000104D8C558 80 E2 FF FF DCD Handle_8_2 - 0x104D8C538 ; jumptable 0000000100C525B4 case 8 __text:0000000104D8C558 ; jumptable 0000000104D8A5B4 case 8 __text:0000000104D8C55C C0 E2 FF FF DCD Handle_9_1 - 0x104D8C538 ; jumptable 0000000100C525B4 case 9
VMP中再次异或加密input数据,基本流程如下:
Handle_44_getValue //取数据
__text:0000000103453398 Handle_44_getValue ; CODE XREF: VM2+1B4↑j __text:0000000103453398 ; DATA XREF: __text:void std::__1::__tree_right_rotate<std::__1::__tree_node_base<void *> *>(std::__1::__tree_node_base<void *> *)+13444↓o __text:0000000103453398 A0 93 02 D1 SUB X0, X29, #0xA4 ; jumptable 0000000100C51BEC case 44 __text:0000000103453398 ; jumptable 0000000103451BEC case 44 __text:000000010345339C A8 83 02 D1 SUB X8, X29, #0xA0 __text:00000001034533A0 E9 13 42 B9 LDR W9, [SP,#0x350+var_140] __text:00000001034533A4 2A 7D 06 53 LSR W10, W9, #6 __text:00000001034533A8 4A 11 00 12 AND W10, W10, #0x1F __text:00000001034533AC 2B 7D 0B 53 LSR W11, W9, #0xB __text:00000001034533B0 2C 7D 1B 53 LSR W12, W9, #0x1B __text:00000001034533B4 ED 03 0C AA MOV X13, X12 __text:00000001034533B8 AD 7D 40 D3 UBFX X13, X13, #0, #0x20 ; ' ' __text:00000001034533BC EE 03 7E B2 MOV X14, #4 __text:00000001034533C0 AD 7D 0E 9B MUL X13, X13, X14 __text:00000001034533C4 0D 01 0D 8B ADD X13, X8, X13 __text:00000001034533C8 AC 01 40 B9 LDR W12, [X13] ; Handle_40计算的值,偏移值 __text:00000001034533CC ED 03 0C AA MOV X13, X12 __text:00000001034533D0 AE 03 50 F8 LDUR X14, [X29,#-0x100] __text:00000001034533D4 CD 01 0D 8B ADD X13, X14, X13 __text:00000001034533D8 6B 3D 10 53 LSL W11, W11, #0x10 __text:00000001034533DC 6B 7D 10 13 ASR W11, W11, #0x10 __text:00000001034533E0 EF 03 0B AA MOV X15, X11 __text:00000001034533E4 EF 7D 40 93 SXTW X15, W15 __text:00000001034533E8 AD 01 0F 8B ADD X13, X13, X15 __text:00000001034533EC AB 01 40 39 LDRB W11, [X13] ; 取异或后sha1值 __text:00000001034533F0 EC 4F 42 B9 LDR W12, [SP,#0x350+xorkey1] __text:00000001034533F4 6B 01 0C 4A EOR W11, W11, W12 ; xor __text:00000001034533F8 6B 1D 00 12 AND W11, W11, #0xFF __text:00000001034533FC 6B 1D 00 53 UXTB W11, W11 __text:0000000103453400 ED 03 0A AA MOV X13, X10 __text:0000000103453404 AD 7D 40 D3 UBFX X13, X13, #0, #0x20 ; ' ' __text:0000000103453408 EF 03 7E B2 MOV X15, #4 __text:000000010345340C AD 7D 0F 9B MUL X13, X13, X15 __text:0000000103453410 08 01 0D 8B ADD X8, X8, X13 __text:0000000103453414 0B 01 00 B9 STR W11, [X8] __text:0000000103453418 A8 83 53 F8 LDUR X8, [X29,#-0xC8] __text:000000010345341C 03 01 40 B9 LDR W3, [X8] __text:0000000103453420 E1 03 0A AA MOV X1, X10 __text:0000000103453424 A2 83 51 F8 LDUR X2, [X29,#-0xE8] __text:0000000103453428 98 04 00 94 BL sub_103454688 __text:000000010345342C E9 17 42 B9 LDR W9, [SP,#0x350+var_13C] __text:0000000103453430 2A 05 00 11 ADD W10, W9, #1 __text:0000000103453434 E0 B7 00 B9 STR W0, [SP,#0x350+var_29C] __text:0000000103453438 EA D3 01 B9 STR W10, [SP,#0x350+var_180] __text:000000010345343C 90 03 00 14 B loc_10345427C ; case返回 index
Handle_52_EOR //异或加密
__text:00000001034537F4 Handle_52_EOR ; CODE XREF: VM2+1B4↑j __text:00000001034537F4 ; DATA XREF: __text:void std::__1::__tree_right_rotate<std::__1::__tree_node_base<void *> *>(std::__1::__tree_node_base<void *> *)+13464↓o __text:00000001034537F4 A8 83 02 D1 SUB X8, X29, #0xA0 ; jumptable 0000000100C51BEC case 52 __text:00000001034537F4 ; jumptable 0000000103451BEC case 52 __text:00000001034537F8 E9 13 42 B9 LDR W9, [SP,#0x350+var_140] __text:00000001034537FC 2A 7D 06 53 LSR W10, W9, #6 __text:0000000103453800 4A 11 00 12 AND W10, W10, #0x1F __text:0000000103453804 2B 7D 0B 53 LSR W11, W9, #0xB __text:0000000103453808 2C 7D 1B 53 LSR W12, W9, #0x1B __text:000000010345380C ED 03 0A AA MOV X13, X10 __text:0000000103453810 AD 7D 40 D3 UBFX X13, X13, #0, #0x20 ; ' ' __text:0000000103453814 EE 03 7E B2 MOV X14, #4 __text:0000000103453818 AD 7D 0E 9B MUL X13, X13, X14 __text:000000010345381C 0D 01 0D 8B ADD X13, X8, X13 __text:0000000103453820 AA 01 40 B9 LDR W10, [X13] ; 取Handle_44加密后的sha1值 __text:0000000103453824 EF 4B 42 B9 LDR W15, [SP,#0x350+xorkey2] __text:0000000103453828 4A 01 0F 4A EOR W10, W10, W15 __text:000000010345382C ED 03 0C AA MOV X13, X12 __text:0000000103453830 AD 7D 40 D3 UBFX X13, X13, #0, #0x20 ; ' ' __text:0000000103453834 EE 03 7E B2 MOV X14, #4 __text:0000000103453838 AD 7D 0E 9B MUL X13, X13, X14 __text:000000010345383C 08 01 0D 8B ADD X8, X8, X13 __text:0000000103453840 0C 01 40 B9 LDR W12, [X8] __text:0000000103453844 6B 3D 10 53 LSL W11, W11, #0x10 __text:0000000103453848 8B 41 8B 0B ADD W11, W12, W11,ASR#16 __text:000000010345384C E8 03 0B AA MOV X8, X11 __text:0000000103453850 08 7D 40 D3 UBFX X8, X8, #0, #0x20 ; ' ' __text:0000000103453854 AD 03 50 F8 LDUR X13, [X29,#-0x100] __text:0000000103453858 A8 01 08 8B ADD X8, X13, X8 __text:000000010345385C 0A 01 00 39 STRB W10, [X8] ; 存sha1值与存其它值 __text:0000000103453860 EA 17 42 B9 LDR W10, [SP,#0x350+var_13C] __text:0000000103453864 4B 05 00 11 ADD W11, W10, #1 __text:0000000103453868 EB D3 01 B9 STR W11, [SP,#0x350+var_180] __text:000000010345386C 84 02 00 14 B loc_10345427C ; case返回 index
Handle_13_16_21_29_45_53_61_index //index++
__text:00000001034541F8 Handle_13_16_21_29_45_53_61_index ; CODE XREF: VM2+19C↑j __text:00000001034541F8 ; VM2+1B4↑j __text:00000001034541F8 ; DATA XREF: ... __text:00000001034541F8 A0 93 02 D1 SUB X0, X29, #0xA4 ; jumptable 0000000100C51BEC default case __text:00000001034541F8 ; jumptable 0000000103451BEC default case, cases 13,16,21,29,45,53,61 __text:00000001034541FC A8 83 02 D1 SUB X8, X29, #0xA0 __text:0000000103454200 E9 13 42 B9 LDR W9, [SP,#0x350+var_140] __text:0000000103454204 2A 7D 06 53 LSR W10, W9, #6 __text:0000000103454208 4A 11 00 12 AND W10, W10, #0x1F __text:000000010345420C 2B 7D 0B 53 LSR W11, W9, #0xB __text:0000000103454210 6B 11 00 12 AND W11, W11, #0x1F __text:0000000103454214 EC 03 0B AA MOV X12, X11 __text:0000000103454218 8C 7D 40 D3 UBFX X12, X12, #0, #0x20 ; ' ' __text:000000010345421C ED 03 7E B2 MOV X13, #4 __text:0000000103454220 8C 7D 0D 9B MUL X12, X12, X13 __text:0000000103454224 0C 01 0C 8B ADD X12, X8, X12 __text:0000000103454228 8B 01 40 B9 LDR W11, [X12] __text:000000010345422C 6B 41 49 0B ADD W11, W11, W9,LSR#16 ; index++ __text:0000000103454230 EC 03 0A AA MOV X12, X10 __text:0000000103454234 8C 7D 40 D3 UBFX X12, X12, #0, #0x20 ; ' ' __text:0000000103454238 ED 03 7E B2 MOV X13, #4 __text:000000010345423C 8C 7D 0D 9B MUL X12, X12, X13 __text:0000000103454240 08 01 0C 8B ADD X8, X8, X12 __text:0000000103454244 0B 01 00 B9 STR W11, [X8] __text:0000000103454248 A8 83 53 F8 LDUR X8, [X29,#-0xC8] __text:000000010345424C 03 01 40 B9 LDR W3, [X8] __text:0000000103454250 E1 03 0A AA MOV X1, X10 __text:0000000103454254 A2 83 51 F8 LDUR X2, [X29,#-0xE8] __text:0000000103454258 0C 01 00 94 BL sub_103454688 __text:000000010345425C E9 17 42 B9 LDR W9, [SP,#0x350+var_13C] __text:0000000103454260 2A 05 00 11 ADD W10, W9, #1 __text:0000000103454264 E0 3B 00 B9 STR W0, [SP,#0x350+var_318] __text:0000000103454268 EA D3 01 B9 STR W10, [SP,#0x350+var_180] __text:000000010345426C 04 00 00 14 B loc_10345427C ; case返回 index
Handle_9_CmpIndex //判断是否结束
__text:0000000103453EC4 Handle_9_CmpIndex ; CODE XREF: VM2+2194↑j __text:0000000103453EC4 ; DATA XREF: __text:void std::__1::__tree_right_rotate<std::__1::__tree_node_base<void *> *>(std::__1::__tree_node_base<void *> *)+134B8↓o __text:0000000103453EC4 A8 83 02 D1 SUB X8, X29, #0xA0 ; jumptable 0000000100C53BCC case 9 __text:0000000103453EC4 ; jumptable 0000000103453BCC case 9 __text:0000000103453EC8 E0 57 40 B9 LDR W0, [SP,#0x350+var_2FC] __text:0000000103453ECC E9 03 00 AA MOV X9, X0 __text:0000000103453ED0 29 7D 40 D3 UBFX X9, X9, #0, #0x20 ; ' ' __text:0000000103453ED4 EA 03 7E B2 MOV X10, #4 __text:0000000103453ED8 29 7D 0A 9B MUL X9, X9, X10 __text:0000000103453EDC 09 01 09 8B ADD X9, X8, X9 __text:0000000103453EE0 2B 01 40 B9 LDR W11, [X9] ; 取总index __text:0000000103453EE4 E1 53 40 B9 LDR W1, [SP,#0x350+var_300] __text:0000000103453EE8 E9 03 01 AA MOV X9, X1 __text:0000000103453EEC 29 7D 40 D3 UBFX X9, X9, #0, #0x20 ; ' ' __text:0000000103453EF0 EA 03 7E B2 MOV X10, #4 __text:0000000103453EF4 29 7D 0A 9B MUL X9, X9, X10 __text:0000000103453EF8 08 01 09 8B ADD X8, X8, X9 __text:0000000103453EFC 0C 01 40 B9 LDR W12, [X8] ; 取当前index __text:0000000103453F00 7F 01 0C 6B CMP W11, W12 ; 判断是否结束 __text:0000000103453F04 EB 07 9F 1A CSET W11, NE __text:0000000103453F08 6B 01 00 12 AND W11, W11, #1 __text:0000000103453F0C E8 17 41 F9 LDR X8, [SP,#0x350+ZF] __text:0000000103453F10 0B 01 00 B9 STR W11, [X8] __text:0000000103453F14 __text:0000000103453F14 def_100C53BCC ; CODE XREF: VM2+217C↑j __text:0000000103453F14 ; VM2+21E8↑j ... __text:0000000103453F14 E8 17 42 B9 LDR W8, [SP,#0x350+var_13C] ; jumptable 0000000100C53BCC default case __text:0000000103453F14 ; jumptable 0000000103453BCC default case __text:0000000103453F18 09 05 00 11 ADD W9, W8, #1 __text:0000000103453F1C E9 D3 01 B9 STR W9, [SP,#0x350+var_180] ; index++ __text:0000000103453F20 D7 00 00 14 B loc_10345427C ; case返回 index
循环0x2EB次后加密完成,部分数据如下:
0000000146420AF0 AF AA BF AA F6 EE F9 8D B8 80 FF 83 9C A7 8D F3 0000000146420B00 AF BE BB AD FA 8D A1 8D A0 BF 8D EE F9 89 A2 92 0000000146420B10 91 9D B8 BC BE 8C FF BD 89 BE 8A A3 8A 88 87 93 0000000146420B20 9A 87 A4 86 F3 AD A5 B2 9E A0 A0 BA AF 8C 88 FA 0000000146420B30 9A A5 FF 88 A7 86 AA 80 B1 EE FB 8F EE FB 8A 99 0000000146420B40 9F EE F9 89 AD 8D AE B9 93 9F F9 BA A4 A4 FF 91 0000000146420B50 8A FA F8 BD B9 A6 8D 81 B9 B3 AA 8F 8C 83 8F 9B
其中Handle_2_2_CallFunc会调用外面函数获取手环境信息、设备信息与解密方法,代码如下:
_text:0000000104D8A1C8 Handle_2_2_CallFunc ; CODE XREF: VM2+1B4↑j __text:0000000104D8A1C8 ; DATA XREF: __text:void std::__1::__tree_right_rotate<std::__1::__tree_node_base<void *> *>(std::__1::__tree_node_base<void *> *)+1339C↓o __text:0000000104D8A1C8 A8 83 02 D1 SUB X8, X29, #0xA0 ; jumptable 0000000100C51BEC case 2 __text:0000000104D8A1C8 ; jumptable 0000000104D89BEC case 2 __text:0000000104D8A1CC E9 13 42 B9 LDR W9, [SP,#0x350+var_140] __text:0000000104D8A1D0 2A 7D 06 53 LSR W10, W9, #6 __text:0000000104D8A1D4 4A 11 00 12 AND W10, W10, #0x1F __text:0000000104D8A1D8 AB 83 53 F8 LDUR X11, [X29,#-0xC8] __text:0000000104D8A1DC 6C 01 40 B9 LDR W12, [X11] __text:0000000104D8A1E0 AD 03 52 F8 LDUR X13, [X29,#-0xE0] __text:0000000104D8A1E4 AE 01 40 F9 LDR X14, [X13] __text:0000000104D8A1E8 CC 3D 00 B9 STR W12, [X14,#0x3C] __text:0000000104D8A1EC EF 03 0A AA MOV X15, X10 __text:0000000104D8A1F0 EF 7D 40 D3 UBFX X15, X15, #0, #0x20 ; ' ' __text:0000000104D8A1F4 F0 03 7E B2 MOV X16, #4 __text:0000000104D8A1F8 EF 7D 10 9B MUL X15, X15, X16 __text:0000000104D8A1FC 08 01 0F 8B ADD X8, X8, X15 __text:0000000104D8A200 0A 01 40 B9 LDR W10, [X8] __text:0000000104D8A204 5F 01 04 71 CMP W10, #0x100 __text:0000000104D8A208 EE CF 00 F9 STR X14, [SP,#0x350+var_1B8] __text:0000000104D8A20C EA 97 01 B9 STR W10, [SP,#0x350+var_1BC] __text:0000000104D8A210 A2 01 00 54 B.CS loc_104D8A244 __text:0000000104D8A214 E8 97 41 B9 LDR W8, [SP,#0x350+var_1BC] __text:0000000104D8A218 E9 03 08 AA MOV X9, X8 __text:0000000104D8A21C 29 7D 40 D3 UBFX X9, X9, #0, #0x20 ; ' ' __text:0000000104D8A220 EA CF 40 F9 LDR X10, [SP,#0x350+var_1B8] __text:0000000104D8A224 4B 01 03 91 ADD X11, X10, #0xC0 __text:0000000104D8A228 EC 03 7D B2 MOV X12, #8 __text:0000000104D8A22C 29 7D 0C 9B MUL X9, X9, X12 __text:0000000104D8A230 69 01 09 8B ADD X9, X11, X9 __text:0000000104D8A234 29 01 40 F9 LDR X9, [X9] __text:0000000104D8A238 A0 03 55 F8 LDUR X0, [X29,#-0xB0] __text:0000000104D8A23C 20 01 3F D6 BLR X9 ; __text:0000000104D8A240 0C 08 00 14 B loc_104D8C270 __text:0000000104D8A244 ; --------------------------------------------------------------------------- __text:0000000104D8A244 __text:0000000104D8A244 loc_104D8A244 ; CODE XREF: VM2+7D8↑j __text:0000000104D8A244 E8 CF 40 F9 LDR X8, [SP,#0x350+var_1B8] __text:0000000104D8A248 09 01 23 91 ADD X9, X8, #0x8C0 __text:0000000104D8A24C E9 C7 00 F9 STR X9, [SP,#0x350+var_1C8] __text:0000000104D8A250 __text:0000000104D8A250 loc_104D8A250 ; CODE XREF: VM2+860↓j __text:0000000104D8A250 E8 C7 40 F9 LDR X8, [SP,#0x350+var_1C8] __text:0000000104D8A254 09 09 40 B9 LDR W9, [X8,#8] __text:0000000104D8A258 EA 97 41 B9 LDR W10, [SP,#0x350+var_1BC] __text:0000000104D8A25C 3F 01 0A 6B CMP W9, W10 __text:0000000104D8A260 E8 C3 00 F9 STR X8, [SP,#0x350+var_1D0] __text:0000000104D8A264 C1 00 00 54 B.NE loc_104D8A27C __text:0000000104D8A268 E8 C3 40 F9 LDR X8, [SP,#0x350+var_1D0] __text:0000000104D8A26C 09 01 40 F9 LDR X9, [X8] __text:0000000104D8A270 A0 03 55 F8 LDUR X0, [X29,#-0xB0] __text:0000000104D8A274 20 01 3F D6 BLR X9 ; 调用外部方法 __text:0000000104D8A278 FE 07 00 14 B loc_104D8C270 __text:0000000104D8A27C ; --------------------------------------------------------------------------- __text:0000000104D8A27C __text:0000000104D8A27C loc_104D8A27C ; CODE XREF: VM2+82C↑j __text:0000000104D8A27C A8 00 80 52 MOV W8, #5 __text:0000000104D8A280 E9 C3 40 F9 LDR X9, [SP,#0x350+var_1D0] __text:0000000104D8A284 2A 0D 40 F9 LDR X10, [X9,#0x18] __text:0000000104D8A288 EB 03 0A AA MOV X11, X10 __text:0000000104D8A28C EB C7 00 F9 STR X11, [SP,#0x350+var_1C8] __text:0000000104D8A290 E8 7F 01 B9 STR W8, [SP,#0x350+var_1D4] __text:0000000104D8A294 AA 09 01 B4 CBZ X10, loc_104D8C3C8 __text:0000000104D8A298 EE FF FF 17 B loc_104D8A250
外面函数检测越狱,主要检测是否有如下文件:
/Applications/Cydia.app
/Library/MobileSubstrate/MobileSubstrate.dylib
/bin/bash
/usr/sbin/sshd
/etc/apt
/usr/bin/cycript
/usr/bin/gdbhd
外面函数检测是否有自动化与改机类工具,主要检测是否有如下文件:
/Applications/TouchElf.app
/Applications/AutoTouch.app
/Applications/TouchSprite.app
/Applications/handjingling.app
/Library/MobileSubstrate/DynamicLibraries/iGrimace.dylib
/Library/MobileSubstrate/DynamicLibraries/iGrimace.plist
/Applications/iGrimace.app
/Library/MobileSubstrate/DynamicLibraries/NZT.dylib
/Library/MobileSubstrate/DynamicLibraries/NZT.plist
/Applications/NZT.app
/Library/MobileSubstrate/DynamicLibraries/txyfakegps.dylib
/Library/MobileSubstrate/DynamicLibraries/txyfakegps.plist
/Applications/tianxiayou.app
/Library/MobileSubstrate/DynamicLibraries/txytweak.dylib
/Library/MobileSubstrate/DynamicLibraries/txytweak.plist
/Applications/TianXiaYou.app
/Library/MobileSubstrate/DynamicLibraries/OTRLocation.dylib
/Library/MobileSubstrate/DynamicLibraries/OTRLocation.plist
/Applications/OTRLocation.app
/Library/MobileSubstrate/DynamicLibraries/altweak.dylib
/Library/MobileSubstrate/DynamicLibraries/altweak.plist
/Applications/anylocation.app
/User/iGrimace
外面函数获取设备信息,获取电池、屏幕、IDFA、IDFV等:
__text:0000000103336DF8 D4 29 08 94 BL _objc_retainAutoreleasedReturnValue __text:0000000103336DFC F7 03 00 AA MOV X23, X0 __text:0000000103336E00 B7 03 00 B4 CBZ X23, loc_103336E74 __text:0000000103336E04 48 3F 00 D0 ADRP X8, #[email protected] __text:0000000103336E08 18 65 41 F9 LDR X24, [X8,#[email protected]] __text:0000000103336E0C E0 03 17 AA MOV X0, X23 ; void * __text:0000000103336E10 E1 03 15 AA MOV X1, X21 ; char * __text:0000000103336E14 E2 03 18 AA MOV X2, X24 __text:0000000103336E18 BA 29 08 94 BL _objc_msgSend __text:0000000103336E1C C0 02 00 34 CBZ W0, loc_103336E74 __text:0000000103336E20 E0 03 17 AA MOV X0, X23 ; void * __text:0000000103336E24 E1 03 16 AA MOV X1, X22 ; char * __text:0000000103336E28 E2 03 18 AA MOV X2, X24 __text:0000000103336E2C B5 29 08 94 BL _objc_msgSend __text:0000000103336E30 C6 29 08 94 BL _objc_retainAutoreleasedReturnValue __text:0000000103336E34 F5 03 00 AA MOV X21, X0 __text:0000000103336E38 B5 01 00 B4 CBZ X21, loc_103336E6C __text:0000000103336E3C 28 3F 00 B0 ADRP X8, #[email protected] __text:0000000103336E40 01 6D 43 F9 LDR X1, [X8,#[email protected]] ; char * __text:0000000103336E44 E0 03 15 AA MOV X0, X21 ; void * __text:0000000103336E48 AE 29 08 94 BL _objc_msgSend __text:0000000103336E4C 00 01 00 B4 CBZ X0, loc_103336E6C
获取完成后的设备信息如下:
0000000283EB25B0 31 00 31 00 31 36 30 39 38 32 36 33 37 30 32 34 1.1.160982637024 0000000283EB25C0 38 35 31 30 3A 34 32 37 34 00 00 00 00 45 36 38 8510:4274....E68 0000000283EB25D0 36 38 34 46 30 2D 37 35 37 33 2D 34 45 42 43 2D 684F0-7573-4EBC- 0000000283EB25E0 39 39 42 44 2D 41 30 33 44 35 34 42 34 46 34 35 99BD-A03D54B4F45 0000000283EB25F0 37 00 00 44 31 30 41 50 00 69 50 68 6F 6E 65 00 7..D10AP.iPhone. 0000000283EB2600 41 70 70 6C 65 00 63 6F 6D 2E 61 69 72 61 73 69 Apple.com.airasi 0000000283EB2610 61 2E 6D 6F 62 69 6C 65 2E 32 37 33 32 5A 57 58 a.mobile.2732ZWX 0000000283EB2620 38 58 39 00 36 32 36 00 35 2E 34 2E 36 32 00 00 8X9.626.5.4.62.. 0000000283EB2630 00 00 61 43 52 4C 4F 6E 59 4C 56 69 64 65 4F 47 ..aCRLOnYLVideOG 0000000283EB2640 67 30 4B 55 4D 2B 4C 56 78 63 4D 30 30 46 62 6B g0KUM+LVxcM00Fbk 0000000283EB2650 31 4A 4C 42 38 76 51 6A 46 50 42 43 45 3D 00 00 1JLB8vQjFPBCE=.. 0000000283EB2660 32 37 33 32 5A 57 58 38 58 39 00 30 00 00 00 00 2732ZWX8X9.0....
异或加密设备信息:
__text:00000001034EAA8C E0 7B C1 A8 LDP X0, X30, [SP],#0x10 __text:00000001034EAA90 6B 01 09 8B ADD X11, X11, X9 __text:00000001034EAA94 6D 01 40 39 LDRB W13, [X11] __text:00000001034EAA98 AC 01 0C 4A EOR W12, W13, W12 ; 异或加密设备信息,密钥DB __text:00000001034EAA9C E0 7B BF A9 STP X0, X30, [SP,#-0x10]! __text:00000001034EAAA0 40 00 00 18 LDR W0, =0x3A __text:00000001034EAAA4 FF FC FF 97 BL loc_1034E9EA0
加密后设备信息数据
0000000283EB25B0 21 71 21 71 21 47 20 48 28 43 26 42 27 41 22 45 !q!q!G H(C&B'A"E 0000000283EB25C0 28 44 21 41 2A 45 22 46 24 71 10 71 10 34 26 49 (D!A*E"F$q.q.4&I 0000000283EB25D0 26 49 24 37 20 5C 27 44 27 42 3D 45 55 33 53 5C &I$7 \'D'B=EU3S\ 0000000283EB25E0 29 48 52 35 3D 30 20 42 54 44 24 33 24 37 24 44 )HR5=0 BTD$3$7$D 0000000283EB25F0 27 71 10 35 21 41 51 21 10 18 40 19 7F 1F 75 71 'q.5[email protected] 0000000283EB2600 51 01 60 1D 75 71 73 1E 7D 5F 71 18 62 10 63 18 Q.`.uqs.}_q.b.c. 0000000283EB2610 71 5F 7D 1E 72 18 7C 14 3E 43 27 42 22 2B 47 29 q_}.r.|.>C'B"+G) 0000000283EB2620 28 29 29 71 26 43 26 71 25 5F 24 5F 26 43 10 71 ())q&C&q%_$_&C.q 0000000283EB2630 10 71 71 32 42 3D 5F 1F 49 3D 46 18 74 14 5F 36 .qq2B=_.I=F.t._6 0000000283EB2640 77 41 5B 24 5D 5A 5C 27 68 12 5D 41 20 37 72 1A wA[$]Z\'h.]A 7r. 0000000283EB2650 21 3B 5C 33 28 07 41 1B 56 21 52 32 55 4C 10 71 !;\3(.A.V!R2UL.q 0000000283EB2660 22 46 23 43 4A 26 48 49 48 48 10 41 10 00 00 00 "F#CJ&HIHH.A....
对异或加密后的数据进行压缩,压缩函数同上,压缩后数据如下:
0000000110836060 78 9C 15 CE BB 6E C2 30 18 40 61 98 58 2D 84 2A x..λ [email protected]* 0000000110836070 03 2A C4 C1 D8 09 5D 2A 52 C8 80 82 B0 9D 8B 83 .*....]*RȀ ..... 0000000110836080 58 C2 6D A0 46 46 74 E9 FA 73 11 0B 88 87 E6 05 X...FFt......... 0000000110836090 00 7D E3 59 0E A0 12 AD 3F 3E 60 B9 40 F0 62 08 .}......?>`[email protected] 00000001108360A0 BC 64 8E F6 14 93 5C B8 89 17 13 D1 4B DC 94 BE .d...........ܔ . 00000001108360B0 EB 0F CB 59 4E 43 C7 F0 98 CB 28 59 05 0B E3 EB ...YNC.....Y.... 00000001108360C0 F9 20 FA 76 E4 32 A6 01 0D 69 CC 01 0D 88 28 08 . .v.....i....(. 00000001108360D0 C2 93 FA BD 7D 86 A2 BC FB 3C C3 B1 75 B3 80 F7 ....}....<ñ u... 00000001108360E0 E8 0F 83 BD B5 0E F8 5A 1B 2B 2E DD AF CC F7 7C .......Z.+.ݯ ..| 00000001108360F0 1F 98 62 D0 B5 D4 32 F5 7E 80 BE 8C 6C 3B 8F 52 ..bе .......l;.R 0000000110836100 7C AA D9 E1 45 FC D2 ED C6 F0 FF EA 56 38 E1 A1 |...E........... 0000000110836110 41 46 26 F0 2A A2 B9 26 F3 FE 6A 86 C0 4D 3B 6A AF&....&......;j 0000000110836120 CA 74 AE 35 12 E8 09 FC A9 31 D5 00 00 00 00 00 ...5.....1......
计算AES加密密钥
取值AirAsiaMobile.appp/yw_1222_0335_mwua.jpg中解密出来的值“f179ef3c-c43c-441b-b1a5-5f8bb6c9ef48”并计算md5。
AlgorithmHelperMd5Hex->AlgorithmHelperHexString->AlgorithmHelperHexStringExt
得到md5:b5f852c906a38b590f69190b935abdf6取md5字符串前16字节做为密钥“b5f852c906a38b59”。
AES加密后数据如下:
000000013DFBB290 A8 23 C9 F2 B0 B4 DB D2 1C A8 AE BD 30 A0 BA 23 .#..........0..# 000000013DFBB2A0 AD 4F 88 99 CD C0 DC B0 56 0F B8 E3 53 F1 24 E8 .O....ܰ V.....$. 000000013DFBB2B0 E1 9D 00 79 66 FE 16 29 DE 31 AF 53 C7 B7 ED 14 ...yf..)...SǷ .. 000000013DFBB2C0 B8 48 01 71 6E 85 E4 76 73 01 81 D5 67 86 F0 C5 .H.qn........... 000000013DFBB2D0 8F 09 B5 46 D6 7D 64 80 AE 05 5F 08 BD 69 E6 6F ...F..d..._..i.. 000000013DFBB2E0 73 C7 BE 9A CA F6 CE CE 89 40 AB 31 24 37 FB 85 sǾ [email protected]1$7.. 000000013DFBB2F0 0F 1E FD 9E 6B 31 9B 10 EA 40 1C F0 52 D1 D4 B5 ....k1.......... 000000013DFBB300 A6 C8 93 38 93 3F B8 F4 C1 31 E5 0A 90 E0 AF 6D .ȓ 8.?.......... 000000013DFBB310 B1 42 85 C8 C8 F3 19 FF 15 90 D6 D1 85 0A 2B 79 .B............+y 000000013DFBB320 6F EF 0E E4 5C AF C7 34 29 19 23 FE DF FF 41 06 o...\...).#...A. 000000013DFBB330 13 1F 3F CC B5 EF 23 ED 94 43 41 E4 8B 54 97 3F ..?̵ ....CA....? 000000013DFBB340 86 80 B7 3A 41 A4 7A AC CB 6F 01 CE 84 45 BC 0B ...:A.z....΄ E.. 000000013DFBB350 01 2B 93 9C 97 65 91 FB A0 2E B5 A7 6D A5 DC 19 .+...e......m... 000000013DFBB360 B4 79 FC B2 87 7C 82 3E 7E 44 6B CA B0 A3 B6 E4 .y...|.>~Dkʰ ...
对AES加密后的数据进行Base64加密,算法为AlgorithmHelperBase64Encode,加密后数据如下:
qCPJ8rC029IcqK69MKC6I61PiJnNwNywVg+441PxJOjhnQB5Zv4WKd4xr1PHt+0UuEgBcW6F5HZzAYHVZ4bwxY8JtUbWfWSArgVfCL1p5m9zx76ayvbOzolAqzEkN/uFDx79nmsxmxDqQBzwUtHUtabIkziTP7j0wTHlCpDgr22xQoXIyPMZ/xWQ1tGFCit5b+8O5FyvxzQpGSP+3/9BBhMfP8y17yPtlENB5ItUlz+GgLc6QaR6rMtvAc6ERbwLASuTnJdlkfugLrWnbaXcGbR5/LKHfII+fkRryrCjtuQ=
将输入参数与加密后设备数据组合:
KIUR_qCPJ8rC029IcqK69MKC6I61PiJnNwNywVg+441PxJOjhnQB5Zv4WKd4xr1PHt+0UuEgBcW6F5HZzAYHVZ4bwxY8JtUbWfWSArgVfCL1p5m9zx76ayvbOzolAqzEkN/uFDx79nmsxmxDqQBzwUtHUtabIkziTP7j0wTHlCpDgr22xQoXIyPMZ/xWQ1tGFCit5b+8O5FyvxzQpGSP+3/9BBhMfP8y17yPtlENB5ItUlz+GgLc6QaR6rMtvAc6ERbwLASuTnJdlkfugLrWnbaXcGbR5/LKHfII+fkRryrCjtuQ= data=%2FsK4HWlF8dupf1FjFktF%2BiYZVswuG4vBuAhACLXQLoM8fnyUkkqdGC1Qn4ClMaKz%0D%0ART%2BfFerXT2qoo4ZA13vrmFJrxaDGHDPAAg7TUdoSAAUi3Alke38%2Fvye%2F%2BM%2Bht%2FLz%0D%0AVlomfauMr0QIQXA5Mxivl0EEG4PYFQusjZlr4GJZfNTJOjHRoo5bQlAYqB1Iop0J%0D%0AHmQjCa2MCBlw7e%2F176CVGyAyWo88P9YTWcF%2BSM1b4d55v%2FHhdYAyBA6i23aDmtHy%0D%0Aa15vrc%2FDMlBvjyInqMvHMXJCG9DNO0zjfzCNrFB33kQV9XrDsPyBRdMgW88aI7dP%0D%0AGDfQFoK2qAP49hyPOw3IDFV3rsb9U0k9%2F0%2BwPc4EV%2Bp%2B0%2FuXnGuaXYWkiRPRqT9j%0D%0AgoRy93n4C7QUd%2Be330VLhPtFmGZZ9ooozPSUNNEpdaVF1wCnfBTitE%2FKNP%2FF%2FRT%2B%0D%0AWaTlAZsq0dRToAiMTRIEhuEmJLrBpOMCstT%2F3nJlxhYMKAm0DZYWSm1TehppuoNJ%0D%0A5dZQd6IQuleQcFqKJ9B1FFRcIAi953We3xno27LhUNVGK4DIyNqj96HKyc4cx2Jz%0D%0ARLNRRDVANFIGCrGo%2FVDB18dvAA6MhfcEkMAnUcUAfE6b3KtXqVBJDas6sbD3PCpp&KIUR_qCPJ8rC029IcqK69MKC6I61PiJnNwNywVg+441PxJOjhnQB5Zv4WKd4xr1PHt+0UuEgBcW6F5HZzAYHVZ4bwxY8JtUbWfWSArgVfCL1p5m9zx76ayvbOzolAqzEkN/uFDx79nmsxmxDqQBzwUtHUtabIkziTP7j0wTHlCpDgr22xQoXIyPMZ/xWQ1tGFCit5b+8O5FyvxzQpGSP+3/9BBhMfP8y17yPtlENB5ItUlz+GgLc6QaR6rMtvAc6ERbwLASuTnJdlkfugLrWnbaXcGbR5/LKHfII+fkRryrCjtuQ=&IMHW_i0013
计算输入组合后数据的sha1值:
a899c3c2bb7d94fcf2c9d32ff584eb696d183764
返回到VM中对SHA1值进行加密,APP调崩溃了,又重新来了一次,这次的SHA1值如下:
//原始值 0000000283E86640 BF 4F A3 E7 F7 D5 63 55 67 42 DD 0E 53 30 B8 4F 0000000283E86650 E4 C1 4B 2B //异或后值 000000011E3B1444 74 84 68 2C 3C 1E A8 9E AC 89 16 C5 000000011E3B1450 98 FB 73 84 2F 0A 80 E0
第一次加密分4个字节一组,总共5组,详细说下其中一组加密流程:
第4组(4字节) 原:53 30 B8 4F 密:98 FB 73 84
Handle_44_getValue //获取密文然后异或
0000000000000098 0000000000000053
Handle_0_LSL //逻辑左移0x18
0000000000000053 0000000053000000
Handle_24_AND_EOR //逻辑“异或” 00000000FFFFFFFF
0000000053000000 0000000053000000 00000000ACFFFFFF
重复上面Handle
Handle_44_getValue 00000000000000FB 0000000000000030 Handle_0_LSL(0x10) 0000000000000030 0000000000300000 Handle_24_AND_EOR 0000000000300000 0000000000300000 00000000FFCFFFFF Handle_24_AND_EOR 00000000FFCFFFFF 00000000ACFFFFFF 0000000053300000 Handle_24_AND_EOR 0000000053300000 0000000053300000 00000000ACCFFFFF Handle_44_getValue 0000000000000073 00000000000000B8 Handle_0_LSL(0x8) 00000000000000B8 000000000000B800 Handle_24_AND_EOR 000000000000B800 000000000000B800 00000000FFFF47FF Handle_24_AND_EOR 00000000ACCFFFFF 00000000FFFF47FF 000000005330B800 Handle_24_AND_EOR 000000005330B800 000000005330B800 00000000ACCF47FF Handle_44_getValue 0000000000000084 000000000000004F Handle_24_AND_EOR 000000000000004F 000000000000004F 00000000FFFFFFB0 Handle_24_AND_EOR 00000000ACCF47FF 00000000FFFFFFB0 000000005330B84F Handle_40_genOffset
Handle_8_EOR //逻辑异或
000000005330B84F 0000000098FB7384 存放计算的值 000000011E5AFF55 Handle_13_16_21_29_45_53_61_index //index++ Handle_9_CmpIndex //判断index Handle_36_isZF //判断比较真假,真为结束
加密完成后得到的数据如下:
2C 68 84 74 9E A8 1E 3C C5 16 89 AC 84 73 FB 98 E0 80 0A 2F
对加密后的值再次进行加密,循环0x100次,大致流程如下:
Handle_56 //取数据 000000007484682C 00000000BF4FA3E7 Handle_24_AND_EOR 00000000BF4FA3E7 00000000BF4FA3E7 0000000040B05C18 Handle_24_AND_EOR 0000000040B05C18 000000006742DD0E 00000000BFFFA3F7 Handle_24_AND_EOR 000000006742DD0E 000000006742DD0E 0000000098BD22F1 Handle_24_AND_EOR 0000000098BD22F1 00000000BF4FA3E7 0000000067F2DD1E Handle_24_AND_EOR 0000000067F2DD1E 00000000BFFFA3F7 00000000D80D7EE9 Handle_32_LSR(0x1f) 00000000D80D7EE9 0000000000000001 Handle_24_AND_EOR 0000000000000001 0000000000000001 00000000FFFFFFFE Handle_0_LSL(0x1) 00000000D80D7EE9 00000000B01AFDD2 Handle_24_AND_EOR 00000000B01AFDD2 00000000B01AFDD2 000000004FE5022D Handle_24_AND_EOR 000000004FE5022D 00000000FFFFFFFE 00000000B01AFDD3 Handle_8_EOR 00000000B01AFDD3 000000007BD13618 存 000000011E5AFF88 Handle_13_16_21_29_45_53_61_index Handle_9_CmpIndex Handle_36_isZF
下面是加密中使用到的几个关键的Handle:
__text:00000001034520A4 Handle_24_AND_EOR ; CODE XREF: VM2+1B4↑j __text:00000001034520A4 ; DATA XREF: __text:void std::__1::__tree_right_rotate<std::__1::__tree_node_base<void *> *>(std::__1::__tree_node_base<void *> *)+133F4↓o __text:00000001034520A4 A0 93 02 D1 SUB X0, X29, #0xA4 ; jumptable 0000000100C51BEC case 24 __text:00000001034520A4 ; jumptable 0000000103451BEC case 24 __text:00000001034520A8 A8 83 02 D1 SUB X8, X29, #0xA0 __text:00000001034520AC 09 00 80 12 MOV W9, #0xFFFFFFFF __text:00000001034520B0 EA 13 42 B9 LDR W10, [SP,#0x350+var_140] __text:00000001034520B4 4B 7D 06 53 LSR W11, W10, #6 __text:00000001034520B8 6B 11 00 12 AND W11, W11, #0x1F __text:00000001034520BC 4C 7D 0B 53 LSR W12, W10, #0xB __text:00000001034520C0 8C 11 00 12 AND W12, W12, #0x1F __text:00000001034520C4 4D 7D 10 53 LSR W13, W10, #0x10 __text:00000001034520C8 AD 11 00 12 AND W13, W13, #0x1F __text:00000001034520CC EE 03 0C AA MOV X14, X12 __text:00000001034520D0 CE 7D 40 D3 UBFX X14, X14, #0, #0x20 ; ' ' __text:00000001034520D4 EF 03 7E B2 MOV X15, #4 __text:00000001034520D8 CE 7D 0F 9B MUL X14, X14, X15 __text:00000001034520DC 0E 01 0E 8B ADD X14, X8, X14 __text:00000001034520E0 CC 01 40 B9 LDR W12, [X14] ; 取值 __text:00000001034520E4 EE 03 0D AA MOV X14, X13 __text:00000001034520E8 CE 7D 40 D3 UBFX X14, X14, #0, #0x20 ; ' ' __text:00000001034520EC EF 03 7E B2 MOV X15, #4 __text:00000001034520F0 CE 7D 0F 9B MUL X14, X14, X15 __text:00000001034520F4 0E 01 0E 8B ADD X14, X8, X14 __text:00000001034520F8 CD 01 40 B9 LDR W13, [X14] __text:00000001034520FC AC 01 0C 0A AND W12, W13, W12 ; 逻辑“与” __text:0000000103452100 89 01 09 4A EOR W9, W12, W9 ; 逻辑“异或” 00000000FFFFFFFF __text:0000000103452104 EE 03 0B AA MOV X14, X11 __text:0000000103452108 CE 7D 40 D3 UBFX X14, X14, #0, #0x20 ; ' ' __text:000000010345210C EF 03 7E B2 MOV X15, #4 __text:0000000103452110 CE 7D 0F 9B MUL X14, X14, X15 __text:0000000103452114 08 01 0E 8B ADD X8, X8, X14 __text:0000000103452118 09 01 00 B9 STR W9, [X8] __text:000000010345211C A8 83 53 F8 LDUR X8, [X29,#-0xC8] __text:0000000103452120 03 01 40 B9 LDR W3, [X8] __text:0000000103452124 E1 03 0B AA MOV X1, X11 __text:0000000103452128 A2 83 51 F8 LDUR X2, [X29,#-0xE8] __text:000000010345212C 57 09 00 94 BL sub_103454688 __text:0000000103452130 E9 17 42 B9 LDR W9, [SP,#0x350+var_13C] __text:0000000103452134 2A 05 00 11 ADD W10, W9, #1 __text:0000000103452138 E0 A3 01 B9 STR W0, [SP,#0x350+var_1B0] __text:000000010345213C EA D3 01 B9 STR W10, [SP,#0x350+var_180] __text:0000000103452140 4F 08 00 14 B loc_10345427C ; case返回 index
__text:0000000103451DC0 Handle_0_LSL ; CODE XREF: VM2+1B4↑j __text:0000000103451DC0 ; DATA XREF: __text:jpt_100C51BEC↓o __text:0000000103451DC0 A0 93 02 D1 SUB X0, X29, #0xA4 ; jumptable 0000000100C51BEC case 0 __text:0000000103451DC0 ; jumptable 0000000103451BEC case 0 __text:0000000103451DC4 A8 83 02 D1 SUB X8, X29, #0xA0 __text:0000000103451DC8 E9 13 42 B9 LDR W9, [SP,#0x350+var_140] __text:0000000103451DCC 2A 7D 06 53 LSR W10, W9, #6 __text:0000000103451DD0 4A 11 00 12 AND W10, W10, #0x1F __text:0000000103451DD4 2B 7D 0B 53 LSR W11, W9, #0xB __text:0000000103451DD8 6B 11 00 12 AND W11, W11, #0x1F __text:0000000103451DDC 2C 7D 10 53 LSR W12, W9, #0x10 __text:0000000103451DE0 8C 11 00 12 AND W12, W12, #0x1F __text:0000000103451DE4 ED 03 0B AA MOV X13, X11 __text:0000000103451DE8 AD 7D 40 D3 UBFX X13, X13, #0, #0x20 ; ' ' __text:0000000103451DEC EE 03 7E B2 MOV X14, #4 __text:0000000103451DF0 AD 7D 0E 9B MUL X13, X13, X14 __text:0000000103451DF4 0D 01 0D 8B ADD X13, X8, X13 __text:0000000103451DF8 AB 01 40 B9 LDR W11, [X13] ; 异或值 __text:0000000103451DFC 6B 21 CC 1A LSL W11, W11, W12 ; 逻辑左移 __text:0000000103451E00 ED 03 0A AA MOV X13, X10 __text:0000000103451E04 AD 7D 40 D3 UBFX X13, X13, #0, #0x20 ; ' ' __text:0000000103451E08 EE 03 7E B2 MOV X14, #4 __text:0000000103451E0C AD 7D 0E 9B MUL X13, X13, X14 __text:0000000103451E10 08 01 0D 8B ADD X8, X8, X13 __text:0000000103451E14 0B 01 00 B9 STR W11, [X8] __text:0000000103451E18 A8 83 53 F8 LDUR X8, [X29,#-0xC8] __text:0000000103451E1C 03 01 40 B9 LDR W3, [X8] __text:0000000103451E20 E1 03 0A AA MOV X1, X10 __text:0000000103451E24 A2 83 51 F8 LDUR X2, [X29,#-0xE8] __text:0000000103451E28 18 0A 00 94 BL sub_103454688 __text:0000000103451E2C E9 17 42 B9 LDR W9, [SP,#0x350+var_13C] __text:0000000103451E30 2A 05 00 11 ADD W10, W9, #1 __text:0000000103451E34 E0 CB 01 B9 STR W0, [SP,#0x350+var_188] __text:0000000103451E38 EA D3 01 B9 STR W10, [SP,#0x350+var_180] __text:0000000103451E3C 10 09 00 14 B loc_10345427C ; case返回 index
__text:0000000103454178 Handle_32_LSR ; CODE XREF: VM2+1B4↑j __text:0000000103454178 ; DATA XREF: __text:void std::__1::__tree_right_rotate<std::__1::__tree_node_base<void *> *>(std::__1::__tree_node_base<void *> *)+13414↓o __text:0000000103454178 A0 93 02 D1 SUB X0, X29, #0xA4 ; jumptable 0000000100C51BEC case 32 __text:0000000103454178 ; jumptable 0000000103451BEC case 32 __text:000000010345417C A8 83 02 D1 SUB X8, X29, #0xA0 __text:0000000103454180 E9 13 42 B9 LDR W9, [SP,#0x350+var_140] __text:0000000103454184 2A 7D 06 53 LSR W10, W9, #6 __text:0000000103454188 4A 11 00 12 AND W10, W10, #0x1F __text:000000010345418C 2B 7D 0B 53 LSR W11, W9, #0xB __text:0000000103454190 6B 11 00 12 AND W11, W11, #0x1F __text:0000000103454194 2C 7D 10 53 LSR W12, W9, #0x10 __text:0000000103454198 8C 11 00 12 AND W12, W12, #0x1F __text:000000010345419C ED 03 0B AA MOV X13, X11 __text:00000001034541A0 AD 7D 40 D3 UBFX X13, X13, #0, #0x20 ; ' ' __text:00000001034541A4 EE 03 7E B2 MOV X14, #4 __text:00000001034541A8 AD 7D 0E 9B MUL X13, X13, X14 __text:00000001034541AC 0D 01 0D 8B ADD X13, X8, X13 __text:00000001034541B0 AB 01 40 B9 LDR W11, [X13] ; 取值 __text:00000001034541B4 6B 25 CC 1A LSR W11, W11, W12 ; 逻辑右移 __text:00000001034541B8 ED 03 0A AA MOV X13, X10 __text:00000001034541BC AD 7D 40 D3 UBFX X13, X13, #0, #0x20 ; ' ' __text:00000001034541C0 EE 03 7E B2 MOV X14, #4 __text:00000001034541C4 AD 7D 0E 9B MUL X13, X13, X14 __text:00000001034541C8 08 01 0D 8B ADD X8, X8, X13 __text:00000001034541CC 0B 01 00 B9 STR W11, [X8] __text:00000001034541D0 A8 83 53 F8 LDUR X8, [X29,#-0xC8] __text:00000001034541D4 03 01 40 B9 LDR W3, [X8] __text:00000001034541D8 E1 03 0A AA MOV X1, X10 __text:00000001034541DC A2 83 51 F8 LDUR X2, [X29,#-0xE8] __text:00000001034541E0 2A 01 00 94 BL sub_103454688 __text:00000001034541E4 E9 17 42 B9 LDR W9, [SP,#0x350+var_13C] __text:00000001034541E8 2A 05 00 11 ADD W10, W9, #1 __text:00000001034541EC E0 3F 00 B9 STR W0, [SP,#0x350+var_314] __text:00000001034541F0 EA D3 01 B9 STR W10, [SP,#0x350+var_180] __text:00000001034541F4 22 00 00 14 B loc_10345427C ; case返回 index
__text:00000001034539A8 Handle_36_isZF ; CODE XREF: VM2+1B4↑j __text:00000001034539A8 ; DATA XREF: __text:void std::__1::__tree_right_rotate<std::__1::__tree_node_base<void *> *>(std::__1::__tree_node_base<void *> *)+13424↓o __text:00000001034539A8 E8 17 41 F9 LDR X8, [SP,#0x350+ZF] ; jumptable 0000000100C51BEC case 36 __text:00000001034539A8 ; jumptable 0000000103451BEC case 36 __text:00000001034539AC 09 01 40 B9 LDR W9, [X8] ; 取比较结果 __text:00000001034539B0 09 01 00 34 CBZ W9, loc_1034539D0 __text:00000001034539B4 E8 13 42 B9 LDR W8, [SP,#0x350+var_140] __text:00000001034539B8 09 7D 06 53 LSR W9, W8, #6 __text:00000001034539BC 29 5D 18 53 LSL W9, W9, #8 __text:00000001034539C0 EA 17 42 B9 LDR W10, [SP,#0x350+var_13C] __text:00000001034539C4 49 21 89 0B ADD W9, W10, W9,ASR#8 __text:00000001034539C8 E9 D3 01 B9 STR W9, [SP,#0x350+var_180] __text:00000001034539CC 2C 02 00 14 B loc_10345427C ; case返回 index __text:00000001034539D0 ; --------------------------------------------------------------------------- __text:00000001034539D0 __text:00000001034539D0 loc_1034539D0 ; CODE XREF: VM2+1F78↑j __text:00000001034539D0 E8 17 42 B9 LDR W8, [SP,#0x350+var_13C] __text:00000001034539D4 09 05 00 11 ADD W9, W8, #1 __text:00000001034539D8 E9 D3 01 B9 STR W9, [SP,#0x350+var_180] __text:00000001034539DC 28 02 00 14 B loc_10345427C ; case返回 index
最终计算得到一串字符与设备信息加密后数据进行组合得到签名值,整个过程就算完成了,然后将签名值发送给服务器端检验:
KIUR_qCPJ8rC029IcqK69MKC6I61PiJnNwNywVg+441PxJOjhnQB5Zv4WKd4xr1PHt+0UuEgBcW6F5HZzAYHVZ4bwxY8JtUbWfWSArgVfCL1p5m9zx76ayvbOzolAqzEkN/uFDx79nmsxmxDqQBzwUtHUtabIkziTP7j0wTHlCpDgr22xQoXIyPMZ/xWQ1tGFCit5b+8O5FyvxzQpGSP+3/9BBhMfP8y17yPtlENB5ItUlz+GgLc6QaR6rMtvAc6ERbwLASuTnJdlkfugLrWnbaXcGbR5/LKHfII+fkRryrCjtuQ=&IMHW_i00132727e9c9863a1c4ba523b5f9f5f793a11c9a2713
四、总结
由于时间原因,分析这个产品也是断断续续的进行,可能会存在很多没有分析清楚的地方,最后还是简单做一个总结,谈谈自己的一些简单看法,由于时间和水平有限,肯定会存在诸多不足,有不对的地方还请指正,下面谈谈我的看法:
优点:整体安全性比较高,在反IDA F5、逻辑混淆方面做得比较好,每个函数都贯穿始终,产品整体架构设计层次分明,从VMP初始化到VMP实际执行逻辑分层,有利于开发和维护。
从解密bycode到解释执行bycode都通过多层加密,我猜测是考虑到了性能原因,把大部分加解密操作放到了外部执行,把最后的sha1值放到VMP中进行加密处理,安全与性能取一个平衡点,不伤害用户体验的同时达到一定的安全性,毕竟像淘宝、支付宝这样的产品也有使用。
缺点:缺少一定的灵活性,比如bycode隐藏在图片中,当整个执行逻辑被成功分析清楚后难做即时补就措施,黑产特征在随时变化,本地的特征只要改下名字就可以过掉了。
欢迎关注公众号:

如有侵权请联系:admin#unsafe.sh