iOS Forensic Toolkit 7.60 brings gapless low-level 2022-8-25 14:55:34 Author: blog.elcomsoft.com(查看原文) 阅读量:37 收藏
iOS Forensic Toolkit 7.60 brings gapless low-level extraction support for several iOS versions from iOS 15.2 up to and including iOS 15.3.1, adding full file system extraction support for Apple devices based on Apple A11-A15 and M1 chips.
What’s it all about
Low-level extraction is commonly used by forensic specialists to obtain digital evidence not otherwise accessible via the lighter and simpler logical acquisition process. Elcomsoft pioneered agent-based low-level extraction, utilizing a lightweight app for accessing the file system and establishing a communication channel between the expert’s computer and the device being extracted. Once sideloaded onto the device, the extraction agent applies an exploit to obtain superuser privileges and gain low-level access to the file system.
Prior to this update, iOS Forensic Toolkit could perform low-level extraction of most iPhone and iPad models running iOS 9 through iOS 15-15.1.1, delivering full file system extraction and keychain decryption. In this release, we are once again extending the range of supported iOS builds, now covering iOS 15.2 through iOS 15.3.1 on Apple A11-A15 and M1 based devices. With this update, we made it possible to perform full file system extraction of iOS 9.0 through 15.3.1 for all compatible iPhone and iPad models.
Benefits of agent-based extraction
There are several extraction methods of varying complexity and compatibility. Logical acquisition is the most compatible and the easiest to use yet returning the least amount of data. Low-level extraction delivers tangible extras such as location data, comprehensive device usage stats, as well as all sandboxed app data including communication histories in the most secure messaging apps.
Low-level extraction come in multiple flavors, checkm8 being the cleanest and jailbreaks being the most obtrusive of the pack. Agent-based acquisition is second best to checkm8, delivering robust file system extraction for all Apple devices running a compatible version of iOS. Agent-based extraction comes as close to being forensically sound as possible, only installing a lightweight app and not altering any user data.
What makes a certain iOS version ‘compatible’ with the agent? The extraction agent obtains the required level of privileges by exploiting one of the known vulnerabilities in iOS kernel. To do this, the app packs a number of kernel-level exploits and uses one or another to escape its sandbox and access the file system. Such exploits require time and effort to find and to implement, while Apple actively patches known vulnerabilities in iOS updates. This is why the latest versions of iOS are generally immune to exploits developed for earlier builds (although we know of several exceptions).
Breaking iOS 15.2-15.3.1
Unlike checkm8-based extraction, which exploits a boot loader-level vulnerability only available on legacy devices, the extraction agent relies on kernel exploits. These exploits enable the extraction agent to escape the sandbox and gain low-level access to the file system and establish a communication channel between the iPhone and the computer.
Apple actively resists low-level extraction attempts, making it more difficult to sideload apps. Today, sideloading only works reliably in macOS. We are working on improving the process.
iOS 15.2 introduced a new memory protection mechanism that makes it more difficult to apply the exploit. While in this release we can only extract the file system, we are working on keychain decryption as well.
Using the extraction agent
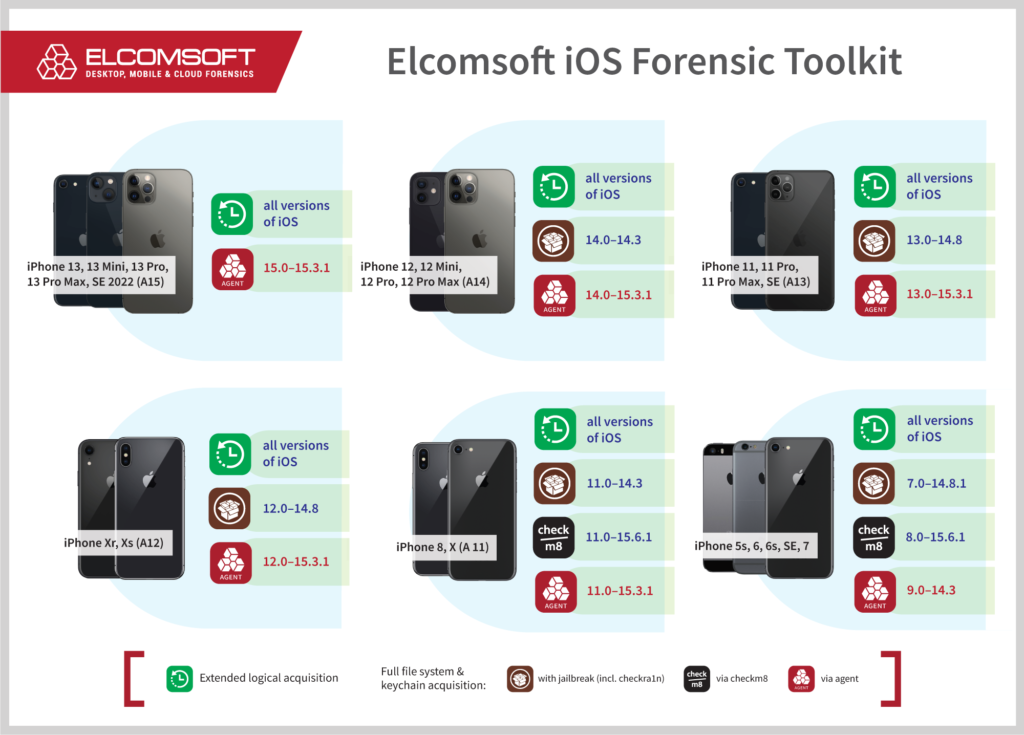
You’ll need a supported iPhone or iPad device running a compatible version of iOS. Please refer to the following picture for the matrix of supported device models and iOS versions:
Using an Apple ID registered in Apple’s Developer Program is strongly recommended for installing the agent as it alleviates the need to open Internet access on the device. A workaround is available to Mac users. Comprehensive instructions on How to Sideload the Extraction Agen are available in our blog.
Low-level extraction in iOS Forensic Toolkit 7.60
To extract the file system and decrypt the keychain from an iOS device without a jailbreak, follow these steps.
1 INSTALL - Install acquisition agent on device 2 KEYCHAIN - Acquire device keychain 3 FILE SYSTEM - Acquire device file system (as TAR archive) 4 FILE SYSTEM (USER) - Acquire user files only (as TAR archive) 5 UNINSTALL - Uninstall acquisition agent on device
Detailed instructions:
- Connect the iPhone to your computer. Pair the device (establish trusted relationship) by confirming the prompt on the iPhone and entering the screen lock passcode.
- Launch iOS Forensic Toolkit 7.60 or newer.
- On the computer, sideload the extraction agent by using the 1 INSTALL command in iOS Forensic Toolkit.
- On the iPhone, launch the extraction agent by tapping its icon.
Windows: developer account required. Use app-specific password.
macOS: developer account not required but strongly recommended. - If supported, extract the keychain with 2 KEYCHAIN.
- Extract file system image (full file system or data partition) with 4 FILE SYSTEM (USER). We recommend extracting the data partition only; the full image (3) may be usable e.g. to check the system partition for persistent malware.
- On the iPhone, uninstall the extraction agent in a regular way or by using the 5 UNINSTALL command.
You may now disconnect the iPhone and start analyzing the data
Low-level extraction in iOS Forensic Toolkit 8.0 Beta
iOS Forensic Toolkit 8.0 features a new, command-line driven user interface, and employs a whole different set of commands compared to EIFT 7.x. To perform agent-based extraction in EIFT 8, follow these steps.
To install the extraction agent onto the device, connect and pair the device to the computer. Then, in the EIFT folder, run the following commands:
- Connect and pair the device to the computer: ./EIFT_cmd normal pair
- Install extraction agent: ./EIFT_cmd agent install
You Will be prompted for Apple ID and password followed by two-factor authentication if the device is not trusted yet. - If a regular, on-developer Apple ID was used, you will have to verify the certificate on the device.
- Tap the app icon to launch the extraction agent.
- Type ./EIFT_cmd agent keychain -o keychain.xml to extract the keychain (supported versions of iOS only)
- Type ./EIFT_cmd agent tar -o data.tar to extract the full file system image. Important: use a unique file name, or the extraction will fail.
- Type ./EIFT_cmd agent uninstall to uninstall the agent.
REFERENCES:
![]()
Elcomsoft iOS Forensic Toolkit
Extract critical evidence from Apple iOS devices in real time. Gain access to phone secrets including passwords and encryption keys, and decrypt the file system image with or without the original passcode. Physical and logical acquisition options for all 64-bit devices running all versions of iOS.
Elcomsoft iOS Forensic Toolkit official web page & downloads »
如有侵权请联系:admin#unsafe.sh