A python script to automatically coerce a Windows server to authenticate on an arbitrary machine through 9 methods.
Features
- Automatically detects open SMB pipes on the remote machine.
- Calls one by one all the vulnerable RPC functions to coerce the server to authenticate on an arbitrary machine.
- Analyze mode with
--analyze, which only lists the vulnerable protocols and functions listening, without performing a coerced authentication. - Perform coerce attack on a list of targets from a file with
--targets-file - Coerce to a WebDAV target with
--webdav-hostand--webdav-port
Usage
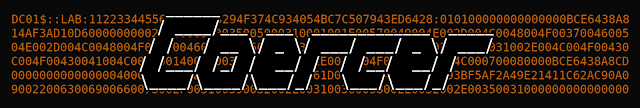
$ ./Coercer.py -h ______
/ ____/___ ___ _____________ _____
/ / / __ \/ _ \/ ___/ ___/ _ \/ ___/
/ /___/ /_/ / __/ / / /__/ __/ / v1.6
\____/\____/\___/_/ \___/\___/_/ by @podalirius_
usage: Coercer.py [-h] [-u USERNAME] [-p PASSWORD] [-d DOMAIN] [--hashes [LMHASH]:NTHASH] [--no-pass] [-v] [-a] [-k] [--dc-ip ip address] [-l LISTENER] [-wh WEBDAV_HOST] [-wp WEBDAV_PORT]
(-t TARGET | -f TARGETS_FILE) [--target-ip ip address]
Automatic windows authentication coercer over various RPC calls.
options:
-h, --help show this help message and exit
-u USERNAME, --username USERNAME
Username to authenticate to the endpoint.
-p PASSWORD, --password PASSWORD
Password to authenticate to the endpoint. (if omitted, it will be asked unless -no-pass is specified)
-d DOMAIN, --domain DOMAIN
Windows domain name to authenticate to the endpoint.
--hashes [LMHASH]:NTHASH
NT/LM hashes (LM hash can be empty)
--no-pass Don't ask for password (useful for -k)
-v, --verbose Verbose mode (default: False)
-a, --analyze Analyze mode (default: Attack mode)
-k, --kerberos Use Kerberos authentication. Grabs credentials from ccache file (KRB5CCNAME) based on target parameters. If valid credentials cannot be found, it will use the ones specified in the
command line
--dc-ip ip address IP Address of the domain controller. If omitted it will use the domain part (FQDN) specified in the target parameter
-t TARGET, --target TARGET
IP address or hostname of the target machine
-f TARGETS_FILE, --targets-file TARGETS_FILE
IP address or hostname of the target machine
--target-ip ip address
IP Address of the target machine. If omitted it will use whatever was specified as target. This is useful when target is the NetBIOS name or Kerberos name and you cannot resolve it
-l LISTENER, --listener LISTENER
IP address or hostname of the listener machine
-wh WEBDAV_HOST, --webdav-host WEBDAV_HOST
WebDAV IP of the server to authenticate to.
-wp WEBDAV_PORT, --webdav-port WEBDAV_PORT
WebDAV port of the server to authenticate to.
Example output
In attack mode (without --analyze option) you get the following output:
After all the RPC calls, you get plenty of authentications in Responder:
Contributing
Pull requests are welcome. Feel free to open an issue if you want to add other features.
Credits
- @tifkin_ and @elad_shamir for finding and implementing PrinterBug on MS-RPRN
- @topotam77 for finding and implementing PetitPotam on MS-EFSR
- @topotam77 for finding and @_nwodtuhs for implementing ShadowCoerce on MS-FSRVP
- @filip_dragovic for finding and implementing DFSCoerce on MS-DFSNM