https://twitter.com/Y4tacker/status/1580193254665920513?s=20&t=mq9URhmKSa7xADbSY4r2fw
看到了这个推特,于是自己看了一眼。
1.9有一个script的标签
org.apache.commons.text.lookup.InterpolatorStringLookup#lookup
切出来key标签script
org.apache.commons.text.lookup.ScriptStringLookup#lookup
调用ScriptEngineManager执行代码。
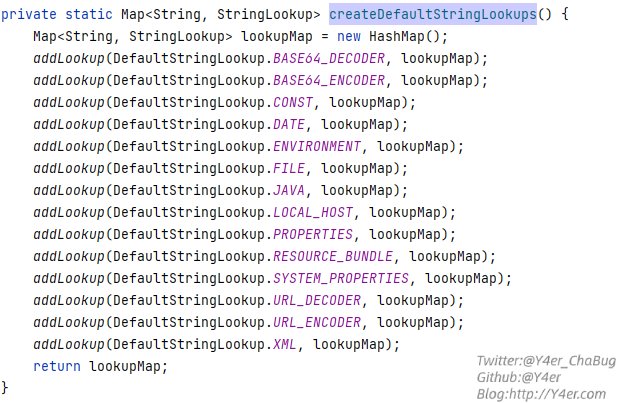
1.10.0修复在addDefaultStringLookups添加默认lookup时不再添加script、url、dns标签
在org.apache.commons.text.lookup.StringLookupFactory.DefaultStringLookupsHolder#createDefaultStringLookups
| |
文笔垃圾,措辞轻浮,内容浅显,操作生疏。不足之处欢迎大师傅们指点和纠正,感激不尽。