CVE-2020-14756
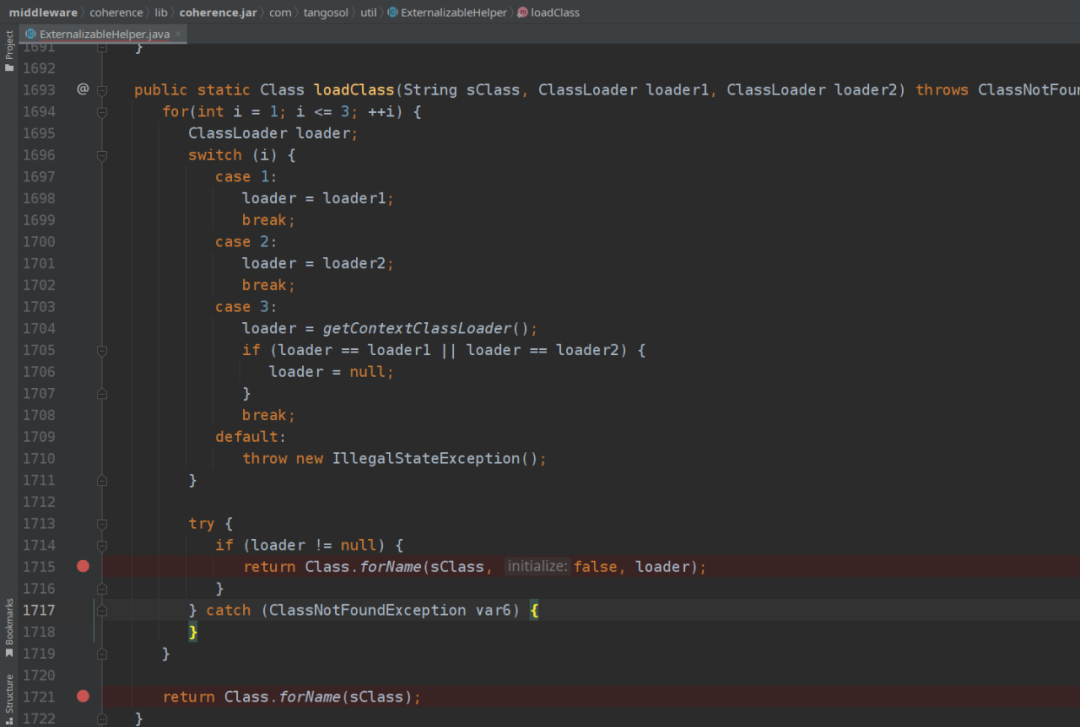
readObject到Class.forName的路子:readUnsignedByte读到的nType为9或10时会进入readXmlSerializable或readExternalizableLite分支。loadClass方法加载类,最终由Class.forName获取类并返回。• readXmlSerializable方法获取类后继续进行XML解析,是另一个XXE漏洞。
readExternalizableLite方法获取类后继续调用readExternal反序列化,不受黑名单限制,进而引出两个问题:1. ExternalizableHelper自身没有实现Serializable接口,一定有什么地方调用它的readObject2. loadClass加载后强转为了ExternalizableLite类型,它哪些满足readExternal参数要求的子类可以被用作sink
PermissionInfo#readExternal会调用ExternalizableHelper#readCollection进而调用readObject作为链首。TopNAggregator$PartialResult及其父类SortedBag:readExternal方法会调用父类的instantiateInternalMap方法将comparator封装进TreeMap,随后在add方法中调用map.put时就会触发compare,进而连上以前的链尾。与PriorityQueue的作用相同,只是绕这么一圈过掉了黑名单。PermissionInfo#writeExternal按照以前的套路一步步构造payload打出去就行。extract:95, MvelExtractor (com.tangosol.coherence.rest.util.extractor)extract:112, ReflectionExtractor (com.tangosol.util.extractor)
extract:105, ChainedExtractor (com.tangosol.util.extractor)
// extract:96, MultiExtractor (com.tangosol.util.extractor)
compare:143, AbstractExtractor (com.tangosol.util.extractor)
compare:416, SortedBag$WrapperComparator (com.tangosol.util)
compare:1295, TreeMap (java.util)
put:538, TreeMap (java.util)
add:152, SortedBag (com.tangosol.util)
add:270, TopNAggregator$PartialResult (com.tangosol.util.aggregator)
readExternal:299, TopNAggregator$PartialResult (com.tangosol.util.aggregator)
readExternalizableLite:2345, ExternalizableHelper (com.tangosol.util)
readObjectInternal:2661, ExternalizableHelper (com.tangosol.util)
readObject:2606, ExternalizableHelper (com.tangosol.util)
readCollection:2131, ExternalizableHelper (com.tangosol.util)
readExternal:190, PermissionInfo (com.tangosol.net.security)
readExternalData:2118, ObjectInputStream (java.io)
readOrdinaryObject:2067, ObjectInputStream (java.io)
readObject0:1573, ObjectInputStream (java.io)
AttributeHolder作为链首,主要是writeExternal的逻辑友好,不用重写构造起来更加方便。ClassLoader.defineClass的路子:com.tangosol.internal.util.invoke.RemoteConstructor#readResolve会触发newInstance并调用com.tangosol.internal.util.invoke.RemotableSupport#realize。ClassLoader.defineClass,可以看到关键是最开始传入RemoteConstructor构造方法的ClassDefinition对象。ClassDefinition构造方法的ClassIdentity对象。ClassIdentity构造函数会将包名、类名、以及md5哈希分别存入三个属性,上文中RemotableSupport加载字节码时,会以这个getName方法获取到的类名为准。1. 将要加载的类喂给 ClassIdentity构造函数2. ClassDefinition构造函数接收第一步创建的ClassIdentity对象、以及要加载的类字节码3. RemoteConstructor构造函数接收第二步创建的ClassDefinition对象、以及要加载的类构造函数的参数类型数组
ClassIdentity构造函数把传给ClassLoader.defineClass的类名作了变化,我们也要对字节码中的类名作相应的格式变化,用asm或者javassist或者手动创建类对象都行。defineClass:181, RemotableSupport (com.tangosol.internal.util.invoke)
realize:137, RemotableSupport (com.tangosol.internal.util.invoke)
newInstance:120, RemoteConstructor (com.tangosol.internal.util.invoke)
readResolve:231, RemoteConstructor (com.tangosol.internal.util.invoke)
invoke0:-1, NativeMethodAccessorImpl (sun.reflect)
invoke:62, NativeMethodAccessorImpl (sun.reflect)
invoke:43, DelegatingMethodAccessorImpl (sun.reflect)
invoke:498, Method (java.lang.reflect)
invokeReadResolve:1260, ObjectStreamClass (java.io)
readOrdinaryObject:2078, ObjectInputStream (java.io)
readObject0:1573, ObjectInputStream (java.io)ExternalizableHelper#readExternalizableLite中loadClass后,判断输入流属于ObjectInputStream就进入检查流程。这就是把找一条非ObjectInputStream输入流就能绕过写在脸上了。extract:95, MvelExtractor (com.tangosol.coherence.rest.util.extractor)extract:112, ReflectionExtractor (com.tangosol.util.extractor)
extract:105, ChainedExtractor (com.tangosol.util.extractor)
// extract:96, MultiExtractor (com.tangosol.util.extractor)
compare:79, AbstractExtractor (com.tangosol.util.extractor)
compare:416, SortedBag$WrapperComparator (com.tangosol.util)
compare:1295, TreeMap (java.util)
put:538, TreeMap (java.util)
add:152, SortedBag (com.tangosol.util)
add:268, TopNAggregator$PartialResult (com.tangosol.util.aggregator)
readExternal:297, TopNAggregator$PartialResult (com.tangosol.util.aggregator)
readExternalizableLite:2265, ExternalizableHelper (com.tangosol.util)
readObjectInternal:2579, ExternalizableHelper (com.tangosol.util)
deserializeInternal:3098, ExternalizableHelper (com.tangosol.util)
fromBinary:334, ExternalizableHelper (com.tangosol.util)
getKey:56, SimpleBinaryEntry (com.tangosol.internal.util)
toString:153, SimpleBinaryEntry (com.tangosol.internal.util)
equals:392, XString (com.sun.org.apache.xpath.internal.objects)
equals:3415, Base (com.tangosol.util)
put:213, LiteMap (com.tangosol.util)
readMap:1900, ExternalizableHelper (com.tangosol.util)
readExternal:190, ConditionalPutAll (com.tangosol.util.processor)
readExternalizableLite:2265, ExternalizableHelper (com.tangosol.util)
readObjectInternal:2579, ExternalizableHelper (com.tangosol.util)
readObject:2524, ExternalizableHelper (com.tangosol.util)
readObject:2502, ExternalizableHelper (com.tangosol.util)
readExternal:406, AttributeHolder (com.tangosol.coherence.servlet)
readExternal:371, AttributeHolder (com.tangosol.coherence.servlet)
readExternalData:2118, ObjectInputStream (java.io)
readOrdinaryObject:2067, ObjectInputStream (java.io)
readObject0:1573, ObjectInputStream (java.io)
参考链接
1.https://www.kingkk.com/2020/08/CVE-2020-14644%E5%88%86%E6%9E%90%E4%B8%8Egadget%E7%9A%84%E4%B8%80%E4%BA%9B%E6%80%9D%E8%80%83
2.https://xz.aliyun.com/t/9068
如有侵权请联系:admin#unsafe.sh