
2023-4-27 06:22:24 Author: www.sentinelone.com(查看原文) 阅读量:34 收藏
SentinelOne is delighted to introduce Purple AI, a generative AI dedicated to threat-hunting, analysis and response. Purple AI uses a variety of models both open source and proprietary and aims to increase the organization’s efficiency by arming security analysts with an AI engine that can help identify, analyze and mitigate threats using conversational prompts and interactive dialog.
In this post, we explain how Purple AI will drive SOC team efficiency and efficacy in threat hunting, analysis and response and illustrate this powerful new feature with example use cases.

Threat Hunting Made Simple with Conversational AI
When it comes to threat hunting, building the right query to get effective results is not an easy task. It requires the analyst to understand what patterns to look for and be familiar with the query syntax at hand in order to translate a seemingly simple question into something the system can understand.
With Purple AI, analysts can now get rapid, accurate and detailed responses to any question, in any language, that otherwise would have required hours of research and multiple queries – not to mention years of analyst experience – to obtain an answer.
The Known Knowns
Purple AI allows threat hunters to ask questions about specific, known threats and get fast answers without needing to create manual queries around indicators of compromise.
For example, the analyst could use a prompt such as “Is my environment infected with SmoothOperator?”, or “Do I have any indicators of SmoothOperator on my endpoints?” to hunt for a specific named threat.
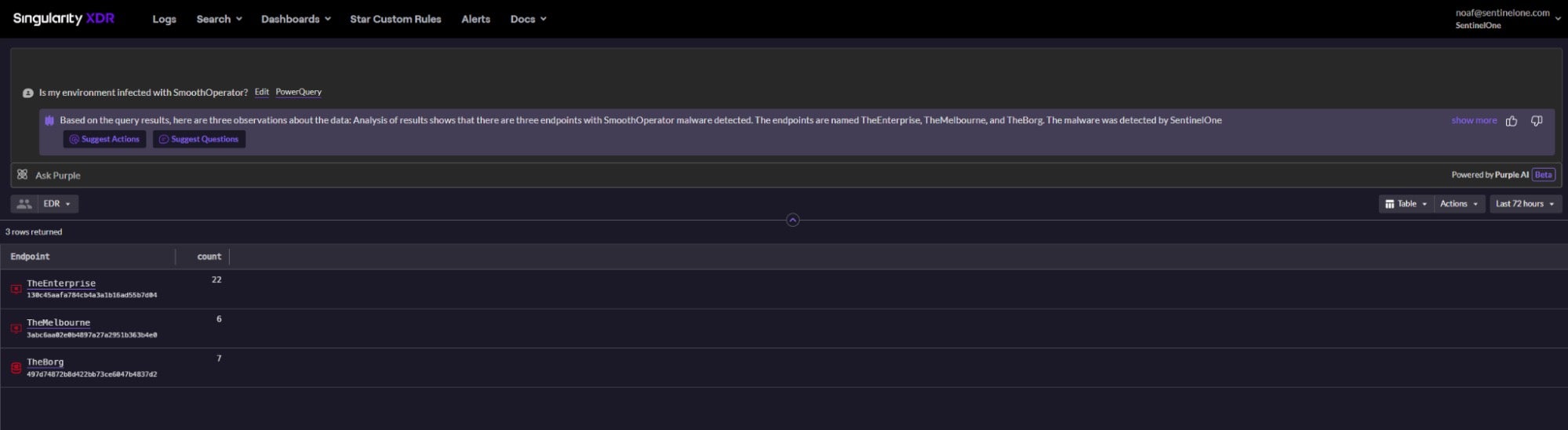
In response, Purple AI delivers a table of results along with context-aware insights based on the observed behavior and identified anomalies within the returned data. Suggested follow up questions and best next actions are also provided. In the case of the SmoothOperator example, a hunter might, for instance, receive the following summary:
“Analysis of results shows that there are three endpoints with the SmoothOperator malware detected, all from the same company site. The data shows that the malware has infected both desktop and server endpoints. This indicates that there may be a larger-scale attack underway, and it is important to investigate further to determine the extent of the infection.
The data shows that the malware has been detected multiple times on some of the infected devices. For example, the malware has been detected twenty two times on the endpoint named “TheEnterprise”, where it was last observed a few hours ago. This suggests that the malware is persistent and that it has been active on the infected devices for some time.”
The hunter can then follow up with additional questions suggested by Purple or manually typed by the user, such as:
“Have there been any persistent events on the endpoint ‘TheEnterprise’?”
“Are there any known vulnerabilities on the affected machines?”
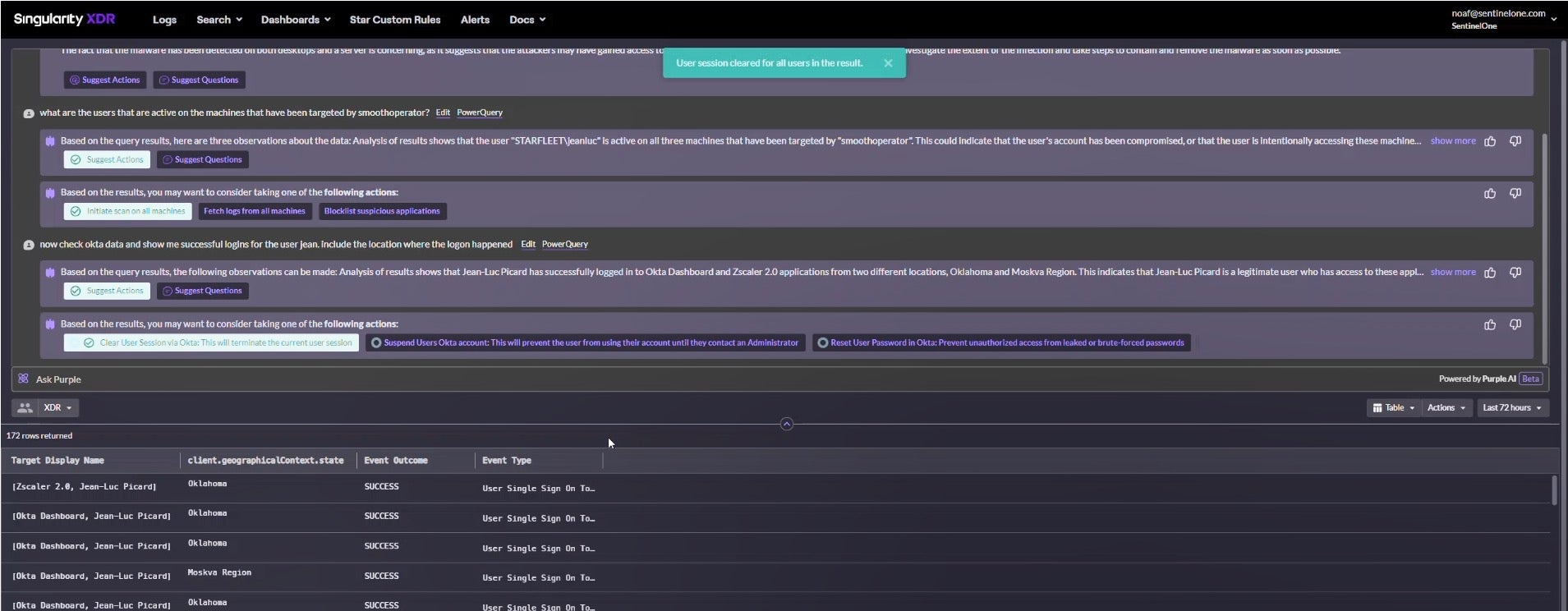
“Show me the users that are active on the affected machines, check their Okta data for successful logins and include the location where the logon happened.”
The system will then automatically return results, alongside a summary of the identified behavior and recommend the next best investigation questions and response actions.
In the examples above, the final question might have resulted in a suggestion to trigger one or more of a combination of actions like “clear user session”, “suspend user`s Okta account”, “force Password reset”, “network quarantine all affected endpoints”, “create a rule to notify users on similar activity identified on other endpoints”, “collect recent security logs from affected machines” and more.
With a single click of a button the analyst can then trigger one or multiple actions, while continuing the conversation and analysis with Purple.
Purple runs on every piece of information within the SentinelOne Security DataLake and enables one-click response via the various SentinelOne XDR integrations. Every question asked by the analyst is executed against the right source or a combination of sources behind the scenes, without the user needing to be familiar with the various data sources or the way their data is ingested. For instance, analysts may ask:
“Are there any ec2 instances running xmrig?”
“Are there any disconnected linux machines of type server or any kubernetes node in my network?”
The analyst can then trigger E/XDR actions like the following:
“Scan all affected EC2 instances, to confirm that no residual artifacts remain on any of the instances that were involved in the incident.”
Or
“Add the detected coinminer software to the SentinelOne Blocklist, preventing it from being re-downloaded, or running on any other endpoints.”
The Unknown Unknowns
In other cases, however, threat hunters may not know what they are looking for. By leveraging the capabilities and speed of Purple AI to intelligently utilize internal and external resources, users can ask questions about suspicious activity they may have not been able to define themselves.
For instance, they might ask Purple AI to:
“Search for all instances of processes attempting to access sensitive data or files and investigate the source of these access attempts”
Or
“Search for all command-line tools commonly used by attackers and investigate if they are being used in suspicious ways.”
Analysts can also leverage Purple to ask questions like “how can I identify X”? For instance:
“How do I look for a possible webshell?”
Or
“How can I search for LOLBins?”
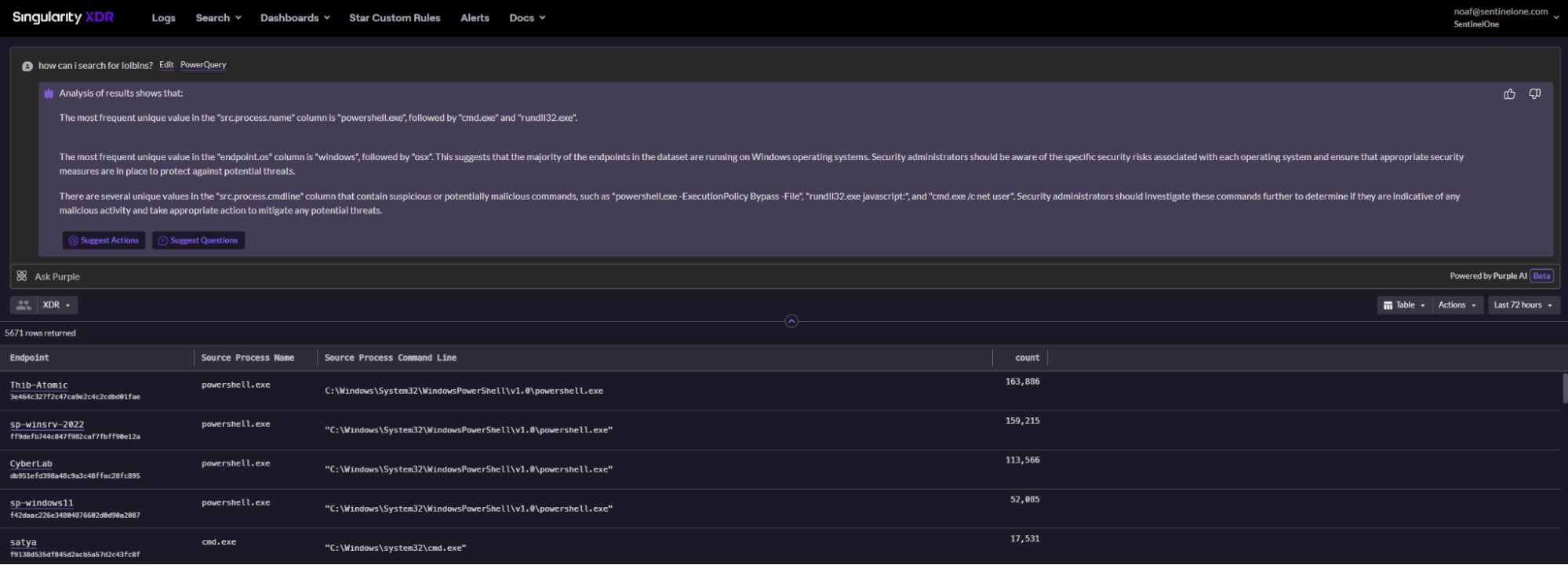
The above might seem simple, but without Purple AI, the task of translating vague terms like “sensitive data”, “commonly used” or “suspicious way” into patterns and then syntax of a query language that could return useful results is an extremely challenging task.
Threat Analysis Made Simple
It is well-known that alert fatigue is one of the biggest challenges facing the modern security operations center (SOC). Most security teams receive more security alerts than they can possibly investigate and address. The issue is clear: the security problem is a data problem. Information only becomes knowledge once we apply meaningful linkages between multiple points of information, assembling the contextualized data into actionable results.
Purple AI, on top of its ability to help security teams ask complex threat hunting questions and run operational commands to manage the entire enterprise environment using natural language, also significantly simplifies the threat investigation process.
Purple’s understanding of ingested data as well as the cyber security domain allows it to quickly determine the chain of events and then to summarize a potentially complex situation to the analyst. The powerful combination of SentinelOne’s patented Storylines technology and Purple AI allows analysts to not only quickly find all events associated with a given activity but also get a summary of these events and their suspicion level in no time.
Within seconds, Purple will provide insights on the identified behavior alongside recommendations, thus reducing the need to manually analyze and stitch together diverse events into one contextual story. This vastly improves analysts’ efficiency, allowing them to investigate and triage a far greater number of alerts in significantly less time.
Purple AI In Action
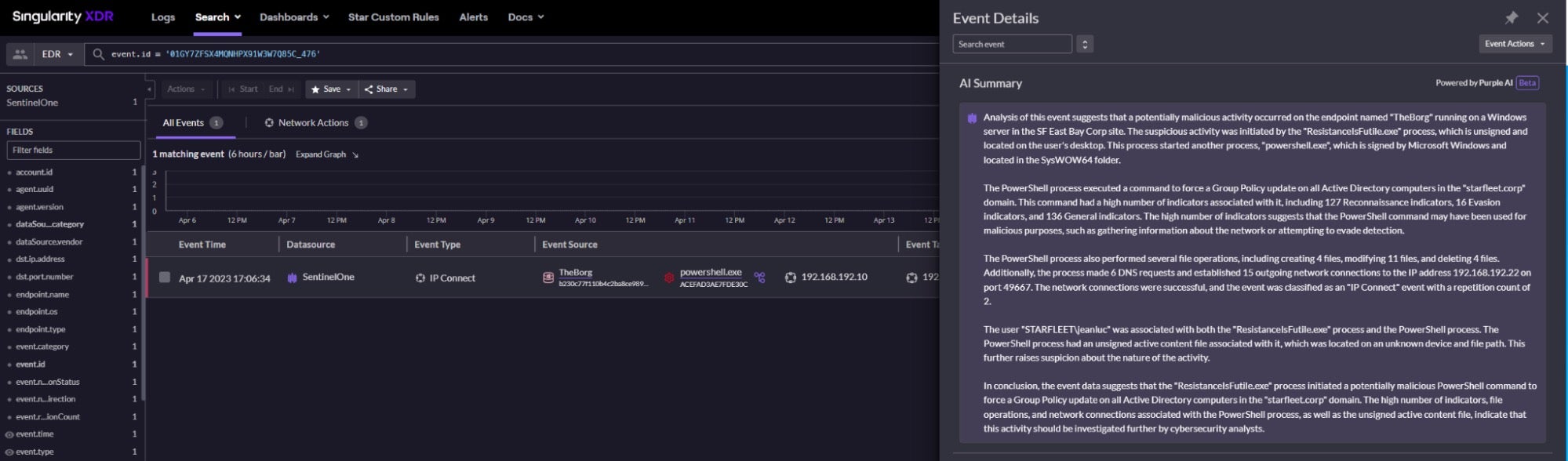
Below is an example summary created for a threat identified by the SentinelOne Singularity platform.
Analysis of this event suggests that a potentially malicious activity occurred on the endpoint named “TheBorg” running on a Windows server in the SF East Bay Corp site. The suspicious activity was initiated by the “ResistanceIsFutile.exe” process, which is unsigned and located on the user’s desktop. This process started another process, “powershell.exe”, which is signed by Microsoft Windows and located in the SysWOW64 folder.
Notice that Purple AI first indicates whether any malicious activity had been seen and where. This is important for the analyst to understand how widespread the attack is. In this example, all malicious activity had been identified on a single site. The user can then choose to drill down further to get detailed analysis of the identified activity if required.
Purple next provides detailed analysis of the events, indicating the behaviors that made SentinelOne classify the behavior as malicious.
The PowerShell process executed a command to force a Group Policy update on all Active Directory computers in the “starfleet.corp” domain. This command had a high number of indicators associated with it, including 127 Reconnaissance indicators, 16 Evasion indicators, and 136 General indicators. The high number of indicators suggests that the PowerShell command may have been used for malicious purposes, such as gathering information about the network or attempting to evade detection.
In this case, a PowerShell process forced a group policy update, which triggered various indicators like Reconnaissance & Evasion. Purple then presents aggregations on the activity made by the suspicious process:
The PowerShell process also performed several file operations, including creating 4 files, modifying 11 files, and deleting 4 files. Additionally, the process made 6 DNS requests and established 15 outgoing network connections to the IP address 192.168.192.22 on port 49667. The network connections were successful, and the event was classified as an “IP Connect” event with a repetition count of 2.
Purple will then move on to provide additional information on the entities associated with the malicious process, like users or files. Suspicious behaviors or attributes associated with these entities will be highlighted as well.
The user “STARFLEET\jeanluc” was associated with both the “ResistanceIsFutile.exe” process and the PowerShell process. The PowerShell process had an unsigned active content file associated with it, which was located on an unknown device and file path. This further raises suspicion about the nature of the activity.
Finally, Purple summarizes the activity, highlighting the malicious entities involved, and provides a conclusion along with recommended next steps.
In conclusion, the event data suggests that the “ResistanceIsFutile.exe” process initiated a potentially malicious PowerShell command to force a Group Policy update on all Active Directory computers in the “starfleet.corp” domain. The high number of indicators, file operations, and network connections associated with the PowerShell process, as well as the unsigned active content file, indicate that this activity should be investigated further by cybersecurity analysts.”
Now in possession of an accurate analysis with a high level of detail, the analyst is rapidly able to copy and paste the insights generated by Purple into a threat analysis report, or initiate further mitigation and incident response steps.
Conclusion
Purple AI is an integrated generative AI that allows threat hunters and SOC team analysts to leverage the power of LLMs (large language models) from within the SentinelOne console to identify and respond to attacks faster and easier. Using natural language conversational prompts and responses, even less-experienced or resourced security teams can rapidly expose suspicious and malicious behaviors that hitherto were only possible to discover with highly-trained analysts dedicating many hours of effort.
Purple AI will be delivered as part of SentinelOne’s threat-hunting experience and is available in limited preview today. Contact us for more information or to request a demo.
如有侵权请联系:admin#unsafe.sh