2023-11-17 04:49:2 Author: securityaffairs.com(查看原文) 阅读量:21 收藏
Zimbra zero-day exploited to steal government emails by four groups
Pierluigi Paganini
November 16, 2023

Google TAG revealed that threat actors exploited a Zimbra Collaboration Suite zero-day (CVE-2023-37580) to steal emails from governments.
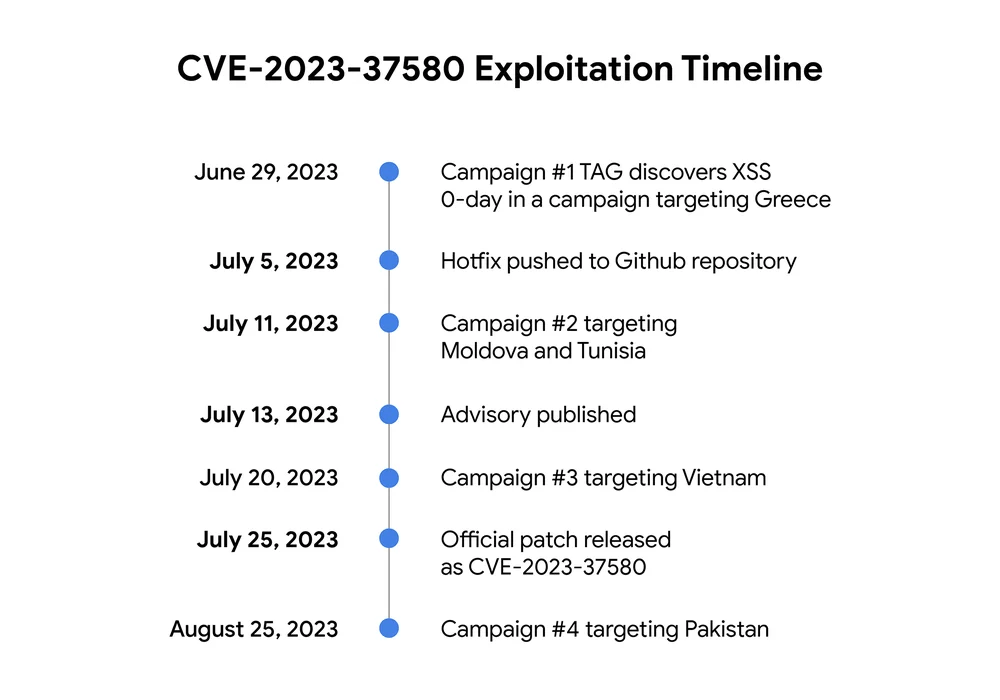
Google Threat Analysis Group (TAG) researchers revealed that a zero-day vulnerability, tracked as CVE-2023-37580 (CVSS score: 6.1), in the Zimbra Collaboration email software was exploited by four different threat actors to steal email data, user credentials, and authentication tokens from government organizations.
The experts observed that most of the attacks took place after the public disclosure of the patch for this vulnerability.
The vulnerability is a reflected cross-site scripting (XSS) issue that resides in the Zimbra Classic Web Client, it impacts Zimbra Collaboration (ZCS) 8 before 8.8.15 Patch 41. Zimbra addressed the vulnerability CVE-2023-37580 in July 2023.
Google TAG researcher Clément Lecigne discovered the zero-day in June while investigating targeted attacks against Zimbra’s email server.
“TAG observed three threat groups exploiting the vulnerability prior to the release of the official patch, including groups that may have learned about the bug after the fix was initially made public on Github. TAG discovered a fourth campaign using the XSS vulnerability after the official patch was released.” reads the advisory published by Google TAG. “Three of these campaigns began after the hotfix was initially made public highlighting the importance of organizations applying fixes as quickly as possible.”
Three of the campaigns observed by Google exploited the vulnerability prior to the release of the fix, while the fourth threat actor launched its campaign a month after the patches were published.
The first campaign aimed at a government organization in Greece, threat actors sent emails containing exploit urls to their targets. Upon clicking the link during a logged-in Zimbra session, the url loaded a framework detailed by security firm Volexity in February 2022. The framework allows attackers to exploit the XSS issue to steal users’ mail data, such as emails and attachments and to set up an auto-forwarding rule to hijack the incoming messages to an attacker-controlled email address.
A second threat actor exploited the vulnerability since July 11 before the official patch became available on July 25. The attackers targeted government organizations in Moldova and Tunisia, the experts noticed that each url contained a unique official email address for specific organizations in those governments. TAG researchers linked the campaign to the Russia-linked APT group Winter Vivern (UNC4907).
A third unidentified group exploited the vulnerability to steal credentials belonging to a government organization in Vietnam.
“In this case, the exploit url pointed to a script that displayed a phishing page for users’ webmail credentials and posted stolen credentials to a url hosted on an official government domain that the attackers likely compromised.” continues the report.
The fourth campaign was observed in August 2023, threat actors exploited the vulnerability in an attack against a government organization in Pakistan. The exploit was used to steal the Zimbra authentication token.

“The discovery of at least four campaigns exploiting CVE-2023-37580, three campaigns after the bug first became public, demonstrates the importance of organizations applying fixes to their mail servers as soon as possible. These campaigns also highlight how attackers monitor open-source repositories to opportunistically exploit vulnerabilities where the fix is in the repository, but not yet released to users.” concludes the report. “The actors behind Campaign #2 began exploiting the bug after the fix was pushed to Github, but before Zimbra publicly released the advisory with remediation advice.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Google TAG)
如有侵权请联系:admin#unsafe.sh