An unknown threat actor has been observed publishing typosquat packages to the Python Package Index (PyPI) repository for nearly six months with an aim to deliver malware capable of gaining persistence, stealing sensitive data, and accessing cryptocurrency wallets for financial gain.
The 27 packages, which masqueraded as popular legitimate Python libraries, attracted thousands of downloads, Checkmarx said in a new report. A majority of the downloads originated from the U.S., China, France, Hong Kong, Germany, Russia, Ireland, Singapore, the U.K., and Japan.
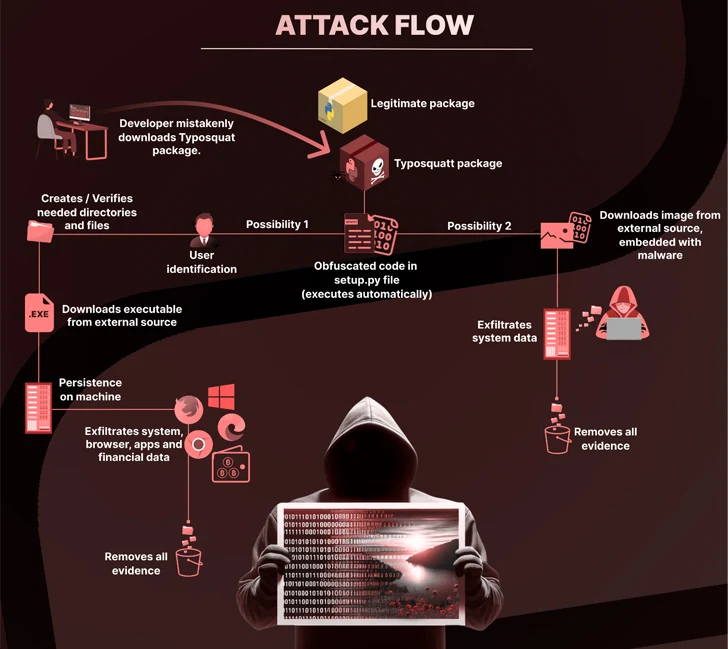
"A defining characteristic of this attack was the utilization of steganography to hide a malicious payload within an innocent-looking image file, which increased the stealthiness of the attack," the software supply chain security firm said.
Some of the packages are pyefflorer, pyminor, pyowler, pystallerer, pystob, and pywool, the last of which was planted on May 13, 2023.
A common denominator to these packages is the use of the setup.py script to include references to other malicious packages (i.e., pystob and pywool) that deploy a Visual Basic Script (VBScript) in order to download and execute a file named "Runtime.exe" to achieve persistence on the host.
Embedded within the binary is a compiled file that's capable of gathering information from web browsers, cryptocurrency wallets, and other applications.
An alternate attack chain observed by Checkmarx is said to have hidden the executable code within a PNG image ("uwu.png"), which is subsequently decoded and run to extract the public IP address and the universally unique identifier (UUID) of the affected system.
Pystob and Pywool, in particular, were published under the guise of tools for API management, only to exfiltrate the data to a Discord webhook and attempt to maintain persistence by placing the VBS file in the Windows startup folder.
"This campaign serves as another stark reminder of the ever-present threats that exist in today's digital landscape, particularly in areas where collaboration and open exchange of code are foundational," Checkmarx said.
The development comes as ReversingLabs uncovered a new wave of protestware npm packages that "hide scripts broadcasting messages of peace related to the conflicts in Ukraine and in Israel and the Gaza Strip."
One of the packages, named @snyk/sweater-comb (version 2.1.1), determines the geographic location of the host, and if it's found to be Russia, displays a message criticizing the "unjustified invasion" of Ukraine through another module called "es5-ext."
Another package, e2eakarev, has the description "free palestine protest package" in the package.json file, and carries out similar checks to see if the IP address resolves to Israel, and if so, log what's described as a "harmless protest message" that urges developers to raise awareness about the Palestinian struggle.
It's not just threat actors infiltrating open-source ecosystems. Earlier this week, GitGuardian revealed the presence of 3,938 total unique secrets across 2,922 PyPI projects, of which 768 unique secrets were found to be valid.
This includes AWS keys, Azure Active Directory API keys, GitHub OAuth app keys, Dropbox keys, SSH keys, and credentials associated with MongoDB, MySQL, PostgreSQL, Coinbase, and Twilio.
What's more, many of these secrets were leaked more than once, spanning multiple release versions, bringing the total number of occurrences to 56,866.
"Exposing secrets in open-source packages carries significant risks for developers and users alike," GitGuardian's Tom Forbes said. "Attackers can exploit this information to gain unauthorized access, impersonate package maintainers, or manipulate users through social engineering tactics."
The continuous wave of attacks targeting the software supply chain has also prompted the U.S. government to issue new guidance this month for software developers and suppliers to maintain and provide awareness about software security.
"It is recommended that acquisition organizations assign supply chain risk assessments to their buying decisions given the recent high profile software supply chain incidents," the Cybersecurity and Infrastructure Security Agency (CISA), National Security Agency (NSA), and the Office of the Director of National Intelligence (ODNI) said.
"Software developers and suppliers should improve their software development processes and reduce the risk of harm to not just employees and shareholders, but also to their users."
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.