Cybersecurity is an infinite journey in a digital landscape that never ceases to change. According to Ponemon Institute1, "only 59% of organizations say their cybersecurity strategy has changed over the past two years." This stagnation in strategy adaptation can be traced back to several key issues.
- Talent Retention Challenges: The cybersecurity field is rapidly advancing, requiring a skilled and knowledgeable workforce. However, organizations face a critical shortage of such talent, making it difficult to keep strategies agile and relevant.
- Leadership Focus: Often, the attention of leadership teams is divided across various priorities, and cybersecurity may not be at the forefront. This can result in strategies becoming outdated and less effective.
- Board Engagement: Adequate board support is essential for strategy evolution. A lack of comprehensive understanding of cybersecurity issues at the board level can lead to insufficient resources and support for strategic updates.
- Organizational Silos: When cybersecurity is treated as a separate entity, rather than an integral part of overall business strategy, which it often is, it creates silos. This approach hinders the development of cohesive and adaptable cybersecurity strategies.
This tendency to operate cybersecurity as a siloed function is due to its specialized nature and the rapid pace of technological and threat evolution. What's more, each component - managed SOC, managed risk, and managed strategy - typically functions independently due to their unique expertise and operational focus:
- Managed SOC: Focuses on immediate threat detection and response, and is usually segregated from broader strategic and risk management discussions.
- Managed Risk: Deals with threat assessment and mitigation; it's proactive and analytical nature can isolate it from the day-to-day operations of the SOC.
- Managed Strategy: Focuses on long-term planning and alignment with business goals, but might not intersect directly with the day-to-day operational or risk assessment aspects.
To address these challenges, it's essential for organizations to adopt a more integrated approach. Breaking down the silos between managed SOC, risk management, and strategic planning is key to ensuring that cybersecurity strategies are dynamic and responsive to the ever-changing digital landscape.
Why the Current State of Cybersecurity Demands a Unified Approach
When SecOps, risk management, and cybersecurity strategy are not in sync, your organization's defense system is left vulnerable. This lack of cohesion heightens the risk of cyberattacks and exacerbates your organization's vulnerabilities in an already risky digital environment.
This misalignment often starts with disjointed tools and processes, where an unintegrated technology stack creates gaps in threat detection and response. According to Ponemon Institute2, security teams in are using on average 45 tools to manage their security posture, making it increasingly difficult to keep up with alerts and potential threats.
Beyond a disparate tech stack, misalignment issues often extend to the strategic level. When your cybersecurity strategy is not in line with your broader business objectives or risk appetite, friction will exist. For example, an overly cautious risk management approach stifles business growth by imposing excessive security measures that deter innovation. Conversely, a risk appetite that's too low can also restrict your business' ability to expand and evolve. Considering this, it's essential to strike a balance where your cybersecurity strategy safeguards your operations without impeding the potential for growth and innovation.
Similarly, when considering the risks associated with a disjointed cybersecurity approach, the importance of preparedness for inevitable breaches is heightened. While your organization may implement robust cybersecurity prevention tactics, the absence of a comprehensive response plan leaves a significant vulnerability. This lack of cohesion often results in delayed reactions to cyber incidents, thereby exacerbating their impact and disruption.
In addition, a disjointed approach increases the risk of cyberattacks and leads to misallocation of resources, often diverting attention away from critical vulnerabilities. This inefficiency in managing cybersecurity resources can significantly slow down response times, compounding the potential operational, financial, and reputational damage from cyber incidents.
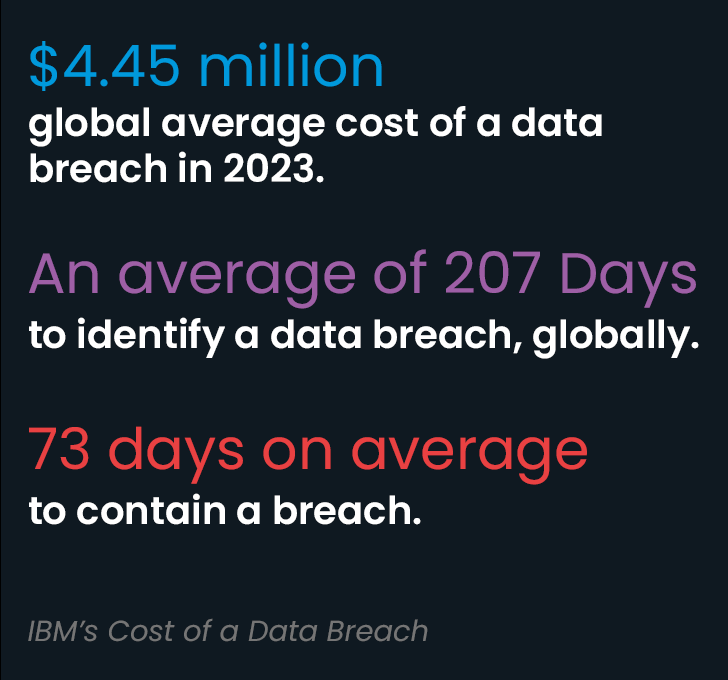
The findings from IBM's Cost of a Data Breach report highlight this:
- The global average cost of a data breach in 2023 was $4.45 million.
- It takes an average of 207 days to identify a data breach, globally.
- The average time to contain a breach was 73 days.
- Breaches with identification and containment times under 200 days cost organizations $3.93 million. Those over 200 days cost $4.95 million—a difference of 23%.
To effectively mitigate these risks, it's crucial to integrate strong preventative measures with a robust and well-coordinated response strategy, ensuring a cohesive defense against cyber threats.
Ultimately, strengthening your organization's defense against these threats requires aligning your SecOps, risk management, and cybersecurity strategy. This alignment ensures a defense system that is resilient, responsive, and effectively tailored to address a broad spectrum of cyber threats. Achieving this harmony is essential for a robust cybersecurity posture, safeguarding your organization in the modern digital world.
Address Cyber Threats with One Ecosystem
To address these challenges effectively, it is imperative to move beyond a traditional technology-centric view and embrace a holistic cybersecurity approach. This paradigm shift is pivotal, emphasizing that the true strength of your organization's cybersecurity framework is not just in the technologies employed, but in their seamless integration with managed risk, managed strategy, and robust SecOps.
The essence of Manage Risk lies in its proactive nature—it's not just about reacting to threats as they occur, but actively managing potential vulnerabilities and exposures to prevent incidents before they happen. It encompasses a broad range of activities aimed at understanding and preparing for the landscape of possible risks. This includes implementing security awareness training and phishing simulations to manage human risks, as well as engaging in advanced phishing remediation techniques. On the technical side, managed risk involves conducting thorough vulnerability assessments and penetration tests, alongside breach and attack simulations. Ultimately, the insights gleaned from Managed Risk are used to inform the development of your cybersecurity strategy.
Managed Strategy is about balancing risks with business growth. This involves developing a comprehensive plan in collaboration with seasoned cybersecurity experts, like a vCISO, that outlines how your organization will address cybersecurity threats, compliance gaps, and business risks, now and in the future. This includes setting clear objectives, determining resource allocation, and creating and testing policies and procedures. A managed strategy ensures that every aspect of your organization's cybersecurity efforts are intentional, coordinated, and aligned with the overall business goals.
A managed Security Operations Center is at the heart of this ecosystem. It functions as the operational nerve center, where real-time monitoring, analysis, and response to cyber threats occur. By integrating managed risk and strategy into the SOC, your organization ensures that the insights gained from risk management inform the strategic planning and operational responses. This integration enables a more agile, responsive, and effective cybersecurity posture.
By weaving together these elements—managed risk, managed strategy, and a managed SOC—into a single, cohesive ecosystem, organizations are better equipped to anticipate, prepare for, and adeptly respond to the diverse and ever-evolving range of cyber threats. This approach to cybersecurity program management is not just a strategic advantage but a fundamental necessity for ensuring a secure and fortified digital presence in today's cyber landscape.
See how your organization compares against industry standards. Asses your security posture with our Cybersecurity Checklist. Download now.
6 Benefits of Unifying SecOps, Risk Management, and Managed Strategy
1. Cost-Effective Resource Allocation
The integration of SOC management, risk management, and managed strategy leads to strategic allocation of both human and technology resources in cybersecurity. This approach reduces redundancies, ensuring efficient use of investments in personnel and security infrastructure. On the human side, this consolidation fosters better internal team coordination and communication, aligning everyone towards common cybersecurity goals and enhancing overall efficiency, while also augmenting your team with highly-specialized resources, enabling your team to focus on more strategic initiatives.
From a technological standpoint, unifying your cybersecurity program components helps prevent the overlapping of tools and systems, reducing complexity and associated costs. Enhanced threat detection and response capabilities from this streamlined approach also significantly limit financial impacts from cyber incidents. IBM's report underscores this, noting that organizations with lower security system complexity faced an average data breach cost of $3.84 million in 2023, compared to $5.28 million for those with more complex systems, marking a significant increase of 31.6%. This data highlights the cost-effectiveness of a unified cybersecurity strategy.
2. Informed Decision-Making
At the core of an integrated cybersecurity strategy lies the principle of data-driven decision-making. However, currently, organizations often deal with cybersecurity assessments that lack a robust foundation in data analysis. This disconnect between data and decision-making drives the need for integration. By seamlessly merging every component of your cybersecurity program into one ecosystem, decisions become grounded in comprehensive data analysis, enabling you to quantify risks in terms of financial and operational impact and empowering you to make informed decisions using metrics to determine the true business impact.
3. Swift Incident Response
The speed of response to security incidents is crucial, but because many organizations have a disjointed system in place, delayed responses and increased vulnerabilities are inevitable. This disconnection often results in ineffective alert triage, a proliferation of duplicate alerts, and a lack of prioritization - all of which exacerbate the operational, financial, and reputational impact of cyber incidents.
The solution lies in an integrated cybersecurity strategy that aligns SecOps with risk management, streamlining the response process for more effective alert triage, minimizing duplicate alerts, and implementing a risk-based approach to prioritizing alerts. Such an integrated approach enables swift and efficient responses, significantly reducing the impact of cyber incidents and safeguarding organizational assets and reputation, ultimately ensuring business continuity and strengthening stakeholder trust in an increasingly dynamic digital environment.
4. Enhanced, Proactive Threat Detection
A unified, risk-based approach to threat detection involves a transformative shift from traditional siloed practices to a cohesive strategy. Traditionally, disjointed security operations and risk management led to fragmented threat detection and reactive responses to security threats. The integration of these functions acts as a unifying force, bringing previously disconnected data sources and threat intelligence under a single dashboard.
This allows for the correlation of data that was once isolated, providing organizations with a comprehensive 360-degree view of the threat landscape. Additionally, advanced technologies like AI and machine learning enhance this approach by analyzing data, identifying patterns, and enhancing predictive capabilities. The result is a strengthened cybersecurity posture with improved threat detection and mitigation, actively reducing risks and safeguarding organizational assets and reputation in a dynamic digital landscape.
5. Streamlined Compliance Management
Organizations face the significant challenge of keeping up with complex regulatory compliance requirements. Traditionally, fragmented approaches in SecOps management, risk, and strategy have led to cumbersome compliance processes and increased risks of non-compliance, along with potential legal and financial consequences. A more effective solution is found in adopting an integrated cybersecurity approach. By aligning SecOps with risk management and incorporating expert guidance through managed strategy, organizations can navigate the compliance landscape more effectively.
This unified approach streamlines compliance through improved reporting, enhanced data correlation, and centralized log storage. It also allows for adapting swiftly to changing laws and standards under the guidance of seasoned experts. As a result, organizations not only simplify their compliance processes but also significantly reduce the risk of legal and financial repercussions, ensuring operational continuity and maintaining their reputation in a complex regulatory environment.
6. Continuous Progress
In the field of cybersecurity, stagnation equates to vulnerability. However, businesses often struggle to keep up with the rate of change and find themselves facing the daunting reality that failing to advance means becoming more susceptible to threats. The key to overcoming this lies in adopting a holistic strategy that encompasses SecOps management, risk management, and a robust cybersecurity framework.
This approach, blending skilled personnel, efficient processes, and advanced technology, is crucial for effectively countering threats and facilitating growth. By embracing this path of continuous improvement and adaptation, organizations can build stronger resilience against the dynamic nature of cyber threats, positioning themselves to confidently navigate future challenges and achieve lasting business success.
Adapt and Build a Resilient Cybersecurity Program
According to Gartner, "The only way to deal effectively with the evolving risks of digitalization and increasing cyber threats is to institute a continuous security program." Implementing a complete cybersecurity program is a journey that involves several strategic steps and key personnel. By following a comprehensive roadmap, organizations can systematically integrate their SecOps, risk management, and cybersecurity strategies, thereby building a resilient, adaptive cybersecurity posture.
3 Steps to Develop Your Cybersecurity Program
1. Strategic Alignment and Planning
- Establish clear cybersecurity goals aligned with business objectives.
- Integrate security controls into the organizational strategy.
- Support all business aspects with robust security measures.
- Create a risk prioritization framework to identify critical threats.
- Develop a tailored security architecture based on business needs and risk profile.
2. Risk-Centric Action and Deployment
- Design an efficient team structure for cybersecurity strategy implementation.
- Deploy necessary tools and technologies for plan execution.
- Translate strategic plans into actionable steps.
- Allocate resources strategically to high-risk areas.
- Ensure continuous monitoring and management of security systems.
3. Continuous Recalibration and Optimization
- Maintain accountability across all organizational levels.
- Enhance incident response capabilities for swift threat response.
- Foster a cybersecurity-aware culture and educate employees and stakeholders.
- Regularly evaluate and communicate the program's effectiveness to key stakeholders.
- Adjust and refine strategies based on ongoing assessments.
- Align cybersecurity measures with evolving business environments and threat landscapes.
Start the process of recalibrating your security program. Validate your existing cybersecurity controls with a Complimentary Security Workshop. Request a Workshop today.
Future Trends in Cybersecurity
As we look towards the future, the landscape of cybersecurity is set to be shaped by emerging technologies like AI, machine learning, quantum computing, and the Internet of Things (IoT). These technological advancements, particularly the sophisticated capabilities of AI and machine learning, bring both new opportunities and challenges in cybersecurity. They underscore the critical need for an integrated cybersecurity strategy that is adaptive and forward-looking. This strategy must not only address current security concerns but also be agile enough to anticipate and respond to the complex threats that come with these advanced technologies. Embracing an integrated approach is not just a requirement for today but a fundamental imperative for the future, essential for navigating the evolving threats and harnessing the full potential of the digital age.
The integration of SOC management, risk management, and managed cybersecurity strategy is not just beneficial; it's a critical need for modern organizations. This convergence paves the way for a resilient, cost-effective, and future-proof cybersecurity posture, equipping businesses like yours to effectively confront both current and future cybersecurity challenges.
For more information about moving beyond your traditional tech stack, explore ArmorPoint's solutions and experience the power of a unified approach to cybersecurity program management.
References:
1 Ponemon Institute. (2022). The State of Cybersecurity and Third-Party Remote Access Risk.
2Ponemon Institute. (2020). 2020 Cyber Resilient Organization Study.
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.



.png)