
2023-6-12 07:9:28 Author: sandflysecurity.com(查看原文) 阅读量:3 收藏
Product Update
- Date
- June 11, 2023
- Author
- The Sandfly Security Team
Sandfly 4.5.0 has received a massive capability upgrade with a new expression language syntax. This new upgrade greatly expands how our agentless threat hunting and incident response modules can be used to protect Linux.
Sandfly 4.5.0 upgrade includes:
New expression language syntax allows rapid and wider creation of custom threat hunting sandflies for customers.
All built-in modules have been reviewed and depth of coverage for Linux threats broadened.
We have expanded our CPU support to cover IBM POWER8, 9 and 10 processors.
This update has important changes for customers using existing custom sandflies. Please see the section on upgrading custom sandflies for more details.
Sandfly Expression Language Syntax
Today, we introduce a new expression language syntax based on the expr package in Go. The expression language syntax allows customers to more rapidly create new modules using any of the Linux forensic parameters collected by Sandfly.
For instance, if you wanted to do a simple search for a process SHA512 hash in the past you would do the following:
...
"process": {
"hash": {
"sha512": [
"sha512_hash_here",
"another_hash_here"
]
},
...Under the new expression language syntax the form changes to:
...
"rules": [
"process.hash.sha512 matches '^(sha512_hash_here|another_hash_here)$'"
]
...The new syntax allows combining of multiple data fields with conventional logic operators (and, or, not), plus comparisons of integer and floating point fields (<, >, ==, !=). Additionally, it includes full regex support and the ability to use logic operators for negation, conditional checks, and much more.
Further, you can search inside forensic array data such as SSH keys found by Sandfly, user details, file and process attributes, and other critical Linux forensic data. For example, below we are searching for any SSH key using older ssh-rsa values as part of a security policy sweep:
...
"rules": [
"any(user.ssh.authorized_keys.data, {.type matches '^ssh-rsa$'})"
]
...Expression Language Syntax
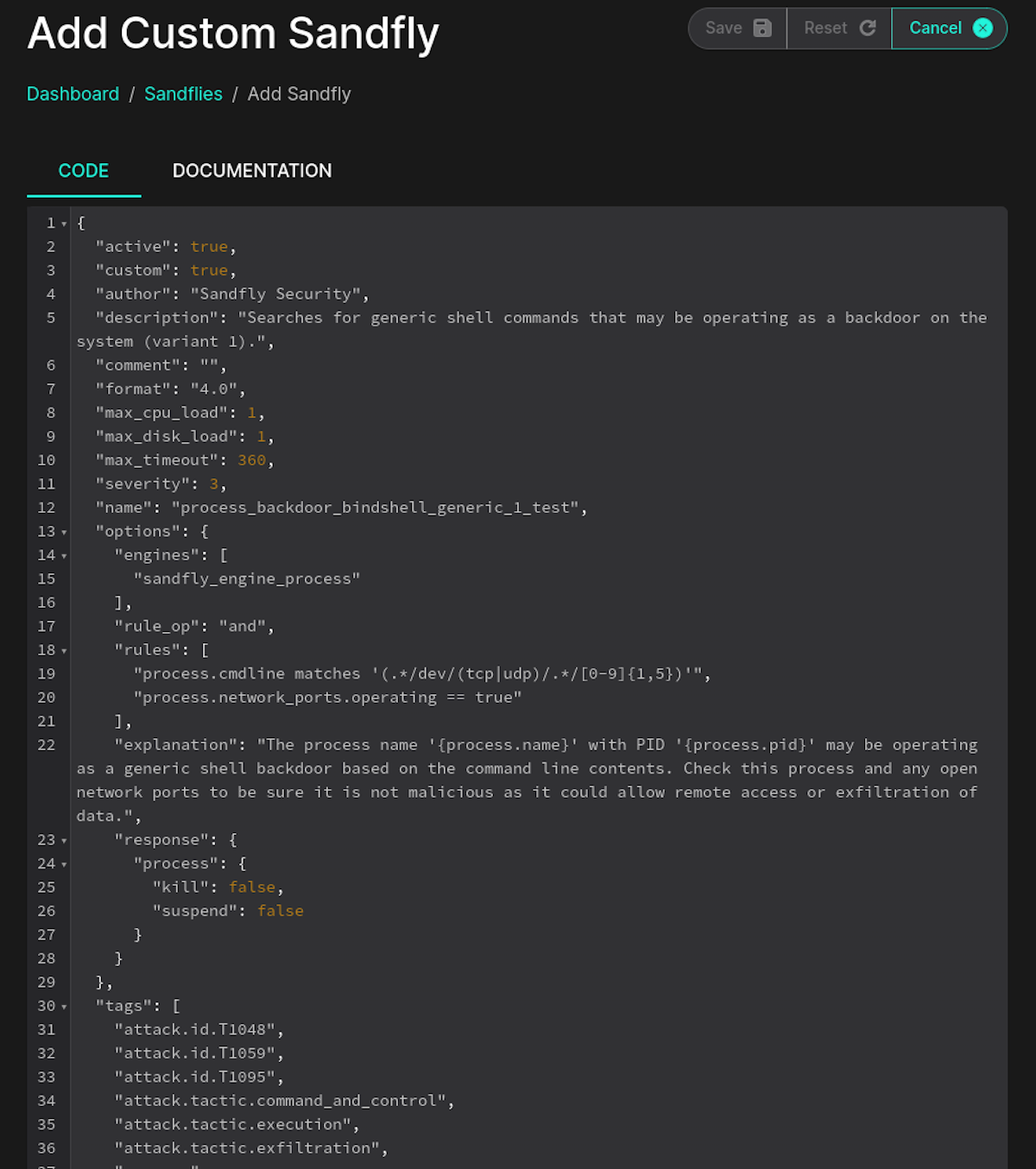
The expression language syntax is covered in our online documentation:
Custom Sandfly Options and Keywords
Sandfly forensic keyword names and types are defined here:
Expanded Coverage for Linux Threats
During the expression syntax upgrade we took the time to expand many Linux threat hunting modules internally. We are now able to spot more kinds of attacks against Linux and modules have been upgraded to find wider threat variants.
IMPORTANT: Old Custom Sandflies Disabled
While the new syntax is very powerful, it is not backwards compatible with the old format sandflies you may have created. There is no direct path to upgrade these older modules so during the upgrade they will be disabled. If you have created custom sandflies, you will need to upgrade them individually.
Licensed customers can contact customer support and we will do the conversion for you free of charge. Please contact us and we will instruct you on exporting your existing custom modules and how to send them to us so we can port them for you quickly.
IBM POWER Processor Support

For this upgrade we also added in support for POWER8, 9 and 10 processors. Customers running on IBM hardware using Linux now have full Sandfly support. Sandfly is committed to having the broadest and deepest security coverage of Linux on the market. We support more modern, legacy, and embedded systems than any other company. Sandfly works on the following CPUs today with no modifications:
Intel
AMD
Arm
MIPS
POWER
Customers running Sandfly across multiple architectures and distributions receive identical Linux security coverage:
Process, file, directory, user, and log file attack detection.
Security policy sweeps.
Advanced attacker and stealth rootkit detection.
SSH key tracking and threat detection.
User password auditing.
Rapid agentless threat hunting.
Sandfly supports modern and legacy systems up to a decade+ old both on-prem and in the cloud. We also run on many embedded devices, including difficult to monitor network edge gear often targeted by advanced adversaries. Sandfly gives extensive coverage without the risk of deploying endpoint agents on Linux.
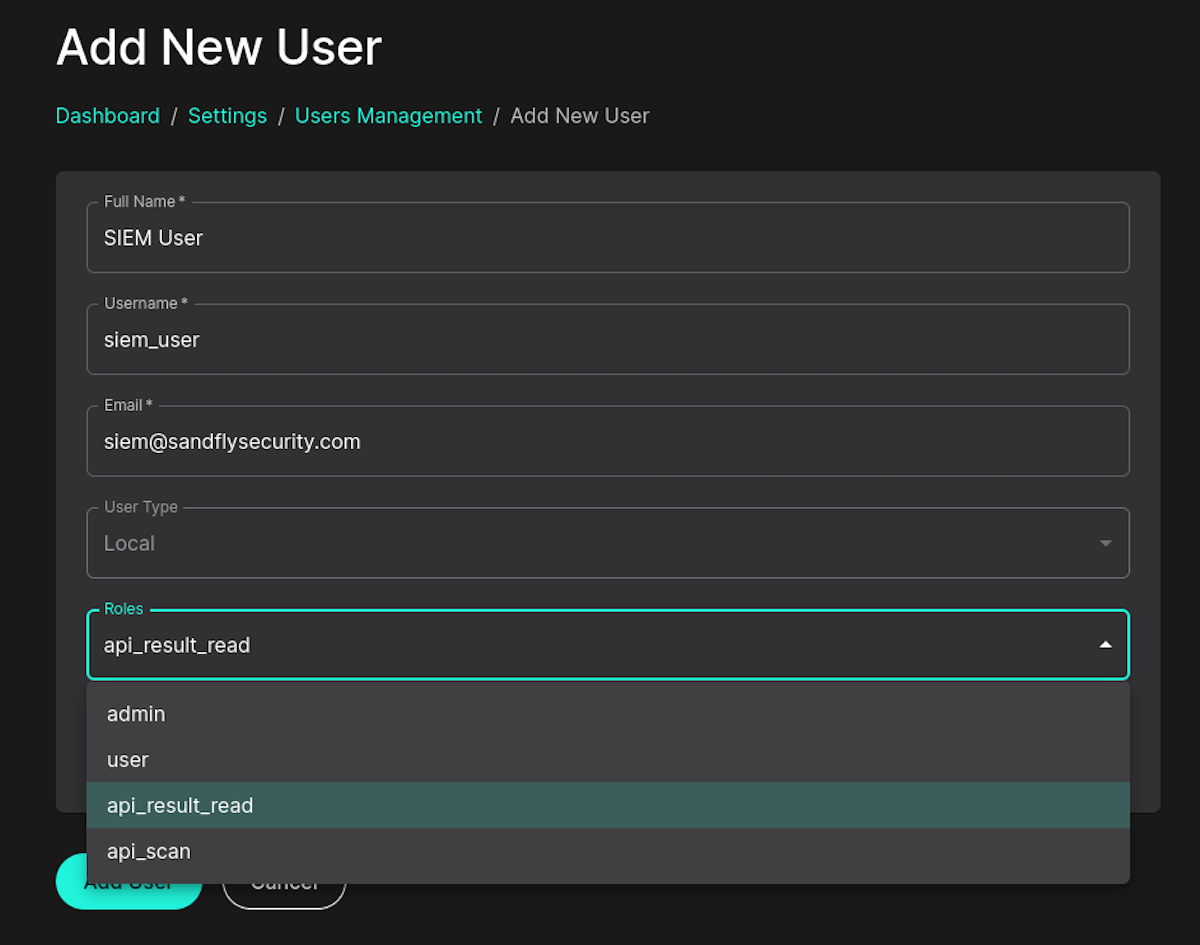
New Read Only and Scan Only User Roles
We have added in new roles for users to restrict access to read only and scan only modes. This allows a SIEM user that can only read results without ability to initiate any other actions. Likewise, a SOAR tool can be given access to initiate threat scans without the ability to modify or see unrelated data from the API.
Get a Free License Today
All Sandfly users get the upgraded and expanded expression language syntax modules. Licensed customers get the ability to create custom modules on the fly for rapid and immediate threat hunting.
Upgrading Sandfly
Sandfly 4.5.0 represents a significant upgrade with powerful new expression syntax that we will be leveraging for exciting new features we will be announcing shortly. All customers are encouraged to upgrade. We are here to help with any questions.
Customers wishing to upgrade can follow the instructions here:
If you have any questions, please reach out to us.
Thank you for using Sandfly.
如有侵权请联系:admin#unsafe.sh