Mexican users have been targeted with tax-themed phishing lures at least since November 2023 to distribute a previously undocumented Windows malware called TimbreStealer.
Cisco Talos, which discovered the activity, described the authors as skilled and that the "threat actor has previously used similar tactics, techniques and procedures (TTPs) to distribute a banking trojan known as Mispadu in September 2023.
Besides employing sophisticated obfuscation techniques to sidestep detection and ensure persistence, the phishing campaign makes use of geofencing to single out users in Mexico, returning an innocuous blank PDF file instead of the malicious one if the payload sites are contacted from other locations.
Some of the notable evasive maneuvers include leveraging custom loaders and direct system calls to bypass conventional API monitoring, in addition to utilizing Heaven's Gate to execute 64-bit code within a 32-bit process, an approach that was also recently adopted by HijackLoader.
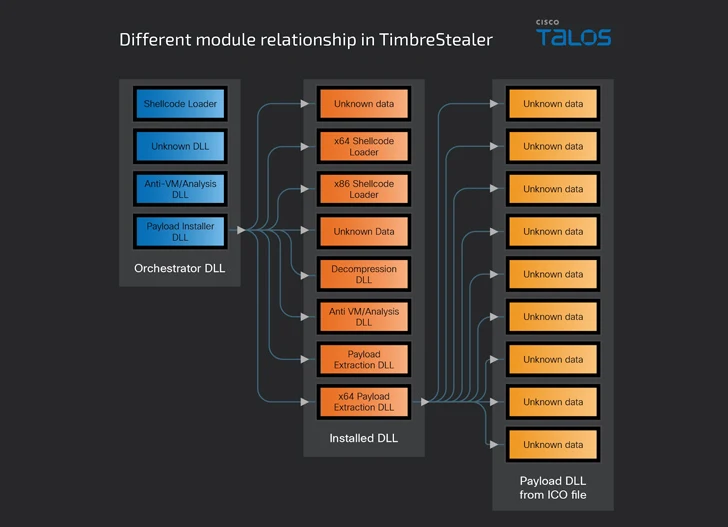
The malware comes with several embedded modules for orchestration, decryption, and protection of the main binary, while also running a series of checks to determine if it's running a sandbox environment, the system language is not Russian, and the timezone is within a Latin American region.
The orchestrator module also looks for files and registry keys to double-check that the machine hasn't been previously infected, before launching a payload installer component that displays a benign decoy file to the user, as it ultimately triggers the execution of TimbreStealer's primary payload.
The payload is designed to harvest a wide range of data, including credential information from different folders, system metadata, and the URLs accessed, look for files matching specific extensions, and verify the presence of remote desktop software.
Cisco Talos said it identified overlaps with a Mispadu spam campaign observed in September 2023, although the target industries of TimbreStealer are varied and with a focus on manufacturing and transportation sectors.
The disclosure comes amid the emergence of a new version of another information stealer called Atomic (aka AMOS), which is capable of gathering data from Apple macOS systems such as local user account passwords, credentials from Mozilla Firefox and Chromium-based browsers, crypto wallet information, and files of interest, using an unusual combination of Python and Apple Script code.
"The new variant drops and uses a Python script to stay covert," Bitdefender researcher Andrei Lapusneanu said, noting the Apple Script block for collecting sensitive files from the victim's computer exhibits a "significantly high level of similarity" with the RustDoor backdoor.
It also follows the emergence of new stealer malware families such as XSSLite, which was released as part of a malware development competition hosted by the XSS forum, even as existing strains like Agent Tesla and Pony (aka Fareit or Siplog) continued to be used for information theft and subsequent sale on stealer logs marketplaces like Exodus.
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.