
2024-3-30 05:17:27 Author: www.tenable.com(查看原文) 阅读量:34 收藏


Frequently asked questions about CVE-2024-3094, a supply-chain attack responsible for a backdoor in XZ Utils, a widely used library found in multiple Linux distributions.
Background
The Tenable Security Response Team has put together this blog to answer Frequently Asked Questions (FAQ) regarding CVE-2024-3094, a backdoor in XZ Utils, a widely used compression library found in multiple Linux distributions.
FAQ
What is XZ Utils and what is the library used for?
XZ is a type of lossless data compression on Unix-like operating systems, which is often compared to other common data compression formats such as gzip and bzip2. XZ Utils is a command line tool that contains functionality for both compression and decompression of XZ files and liblzma, a zlib-like API used for data compression and also supports the legacy .lzma format.
How was this backdoor discovered?
On March 29, Andres Freund, a PostgreSQL developer at Microsoft, posted on the Open Source Security Mailing List that he had discovered a supply-chain compromise involving obfuscated malicious code in the XZ package while investigating SSH performance issues. According to both Freund and RedHat, the malicious code is not present in the Git distribution for XZ and only in the full download package.
Which versions of the library are affected?
According to Freund, XZ Utils versions 5.6.0 and 5.6.1 are impacted.
Has this backdoor code been exploited?
No information regarding exploitation has been observed for this backdoor code as of March 29. Because this situation is still developing, we anticipate more information will come to light in the coming days and weeks. We will update this portion of the FAQ once such information is available.
What is the impact of this backdoor?
According to Red Hat, the malicious code modifies functions within the liblzma code, which is part of the XZ Utils package. This modified code can then be used by any software linked to the XZ library and allow for the interception and modification of data used with the library. In the example observed by Freund, under certain conditions, this backdoor could allow a malicious actor to “break sshd authentication,” allowing the attacker to gain access to an affected system.
Is there a CVE assigned for this issue?
Yes, Red Hat assigned CVE-2024-3094 for this issue and it has been given a CVSSv3 score of 10.0.
How was this backdoor inserted into the code?
At the time this blog was published, it’s unclear how this backdoor code was placed into the affected builds of XZ utils. According to Freund, it's likely the individual who made the code commits is directly involved with the XZ project or had their system or developer account compromised.
What Linux distributions are affected?
As of the time this blog was published on March 29, the following distributions are known to be affected:
The following Linux distributions have been confirmed to not be affected:
As this is still a developing situation, we anticipate we will have further clarity for additional Linux distributions soon and will continue to update this blog as necessary.
Are patches or mitigations available?
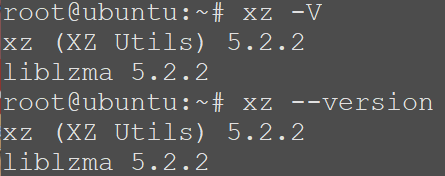
Both developers and users of XZ Utils are advised to downgrade to known, unaffected versions of XZ Utils, such as 5.4.6 Stable. However, in addition to downgrading, it is strongly advised that developers and users conduct incident response to determine if they have been impacted as a result of this backdoor and to share “positive findings” with agencies like the Cybersecurity and Infrastructure Security Agency (CISA). You can check your installed version by running the command ‘xz -V’ or ‘xz –version’.
Has Tenable released any product coverage for these vulnerabilities?
As of March 29, Tenable Research is investigating product coverage. A list of Tenable plugins for this vulnerability can be found on the individual CVE page for CVE-2024-3094 as they’re released. This link will display all available plugins for this vulnerability, including upcoming plugins in our Plugins Pipeline.
Get more information
- Open Source Security Mailing List post by Andres Freund
- Red Hat: Urgent security alert for Fedora Linux 40 and Fedora Rawhide users
- Debian: xz-utils security update
- CISA Alert: Reported Supply Chain Compromise Affecting XZ Utils Data Compression Library, CVE-2024-3094
Join Tenable's Security Response Team on the Tenable Community.
Learn more about Tenable One, the Exposure Management Platform for the modern attack surface.

Satnam Narang
Satnam joined Tenable in 2018. He has over 15 years experience in the industry (M86 Security and Symantec). He contributed to the Anti-Phishing Working Group, helped develop a Social Networking Guide for the National Cyber Security Alliance, uncovered a huge spam botnet on Twitter and was the first to report on spam bots on Tinder. He's appeared on NBC Nightly News, Entertainment Tonight, Bloomberg West, and the Why Oh Why podcast.
Interests outside of work: Satnam writes poetry and makes hip-hop music. He enjoys live music, spending time with his three nieces, football and basketball, Bollywood movies and music and Grogu (Baby Yoda).

Scott Caveza
Scott joined Tenable in 2012 as a Research Engineer on the Nessus Plugins team. Over the years, he has written hundreds of plugins for Nessus, and reviewed code for even more from his time being a team lead and manager of the Plugins team. Previously leading the Security Response team and the Zero Day Research team, Scott is currently a member of the Security Response team, helping the research organization respond to the latest threats. He has over a decade of experience in the industry with previous work in the Security Operations Center (SOC) for a major domain registrar and web hosting provider. Scott is a current CISSP and actively maintains his GIAC GWAPT Web Application Penetration Tester certification.
Interests outside of work: Scott enjoys spending time with his family, camping, fishing and being outdoors. He also enjoys finding ways to break web applications and home renovation projects.
Related Articles
- Exposure Management
Cybersecurity News You Can Use
Enter your email and never miss timely alerts and security guidance from the experts at Tenable.
Tenable Vulnerability Management
Enjoy full access to a modern, cloud-based vulnerability management platform that enables you to see and track all of your assets with unmatched accuracy.
Your Tenable Vulnerability Management trial also includes Tenable Lumin and Tenable Web App Scanning.
Tenable Vulnerability Management
Enjoy full access to a modern, cloud-based vulnerability management platform that enables you to see and track all of your assets with unmatched accuracy. Purchase your annual subscription today.
100 assets
Choose Your Subscription Option:
Thank You
Thank you for your interest in Tenable Vulnerability Management. A representative will be in touch soon.
Tenable Vulnerability Management
Enjoy full access to a modern, cloud-based vulnerability management platform that enables you to see and track all of your assets with unmatched accuracy.
Your Tenable Vulnerability Management trial also includes Tenable Lumin and Tenable Web App Scanning.
Tenable Vulnerability Management
Enjoy full access to a modern, cloud-based vulnerability management platform that enables you to see and track all of your assets with unmatched accuracy. Purchase your annual subscription today.
100 assets
Choose Your Subscription Option:
Thank You
Thank you for your interest in Tenable.io. A representative will be in touch soon.
Tenable Vulnerability Management
Enjoy full access to a modern, cloud-based vulnerability management platform that enables you to see and track all of your assets with unmatched accuracy.
Your Tenable Vulnerability Management trial also includes Tenable Lumin and Tenable Web App Scanning.
Tenable Vulnerability Management
Enjoy full access to a modern, cloud-based vulnerability management platform that enables you to see and track all of your assets with unmatched accuracy. Purchase your annual subscription today.
100 assets
Choose Your Subscription Option:
Thank You
Thank you for your interest in Tenable Vulnerability Management. A representative will be in touch soon.
Try Tenable Web App Scanning
Enjoy full access to our latest web application scanning offering designed for modern applications as part of the Tenable One Exposure Management platform. Safely scan your entire online portfolio for vulnerabilities with a high degree of accuracy without heavy manual effort or disruption to critical web applications. Sign up now.
Your Tenable Web App Scanning trial also includes Tenable Vulnerability Management and Tenable Lumin.
Buy Tenable Web App Scanning
Enjoy full access to a modern, cloud-based vulnerability management platform that enables you to see and track all of your assets with unmatched accuracy. Purchase your annual subscription today.
Try Tenable Lumin
Visualize and explore your exposure management, track risk reduction over time and benchmark against your peers with Tenable Lumin.
Your Tenable Lumin trial also includes Tenable Vulnerability Management and Tenable Web App Scanning.
Buy Tenable Lumin
Contact a Sales Representative to see how Tenable Lumin can help you gain insight across your entire organization and manage cyber risk.
Thank You
Thank you for your interest in Tenable Lumin. A representative will be in touch soon.
Request a demo of Tenable Security Center
Please fill out this form with your contact information.
A sales representative will contact you shortly to schedule a demo.
* Field is required
Request a demo of Tenable OT Security
Get the Operational Technology Security You Need.
Reduce the Risk You Don’t.
Request a demo of Tenable Identity Exposure
Continuously detect and respond to Active Directory attacks. No agents. No privileges.
On-prem and in the cloud.
Request a Demo of Tenable Cloud Security
Exceptional unified cloud security awaits you!
We’ll show you exactly how Tenable Cloud Security helps you deliver multi-cloud asset discovery, prioritized risk assessments and automated compliance/audit reports.
See
Tenable One
In Action
Exposure management for the modern attack surface.
See Tenable Attack Surface Management In Action
Know the exposure of every asset on any platform.
Thank You
Thank you for your interest in Tenable Attack Surface Management. A representative will be in touch soon.
Try Tenable Nessus Professional Free
FREE FOR 7 DAYS
Tenable Nessus is the most comprehensive vulnerability scanner on the market today.
NEW - Tenable Nessus Expert
Now Available
Nessus Expert adds even more features, including external attack surface scanning, and the ability to add domains and scan cloud infrastructure. Click here to Try Nessus Expert.
Fill out the form below to continue with a Nessus Pro Trial.
Buy Tenable Nessus Professional
Tenable Nessus is the most comprehensive vulnerability scanner on the market today. Tenable Nessus Professional will help automate the vulnerability scanning process, save time in your compliance cycles and allow you to engage your IT team.
Buy a multi-year license and save. Add Advanced Support for access to phone, community and chat support 24 hours a day, 365 days a year.
Try Tenable Nessus Expert Free
FREE FOR 7 DAYS
Built for the modern attack surface, Nessus Expert enables you to see more and protect your organization from vulnerabilities from IT to the cloud.
Already have Tenable Nessus Professional?
Upgrade to Nessus Expert free for 7 days.
Buy Tenable Nessus Expert
Built for the modern attack surface, Nessus Expert enables you to see more and protect your organization from vulnerabilities from IT to the cloud.
Learn How Tenable Helps Achieve SLCGP Cybersecurity Plan Requirements
Tenable solutions help fulfill all SLCGP requirements. Connect with a Tenable representative to learn more.
如有侵权请联系:admin#unsafe.sh