2024-4-18 15:57:30 Author: securityboulevard.com(查看原文) 阅读量:50 收藏
Overview
Recently, NSFOCUS CERT detected that Oracle has released a security announcement and fixed two information disclosure vulnerabilities (CVE-2024-21006/CVE-2024-21007) in Oracle WebLogic Server. Due to the defects of T3/IIOP protocol, unauthenticated attackers can send malicious requests through servers affected by T3/IIOP protocol. Access to sensitive information on the target system. Affected users should take measures for protection as soon as possible.
Reference link:
https://www.oracle.com/security-alerts/cpuapr2024.html
Scope of Impact
Affected Version
- WebLogic Server 12.2.1.4.0
- WebLogic Server 14.1.1.0.0
Note: The above is the product version that Oracle officially supports maintenance at present, and multiple old versions of WebLogic Server such as 10.3.6.0, 11.1.1.9 and 12.1.3.0 have stopped maintenance.
Detection
Local detection
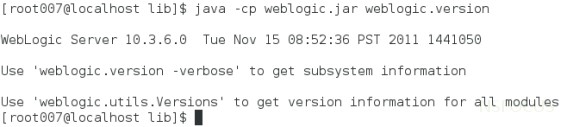
Users can run the following command to check whether the WebLogic version and patch have been installed.
$ cd /Oracle/Middleware/wlserver_10.3/server/lib
$ java -cp weblogic.jar weblogic.version
If no patch installation information is displayed in the output, a risk exists, as shown in the following figure.
T3 protocol detection
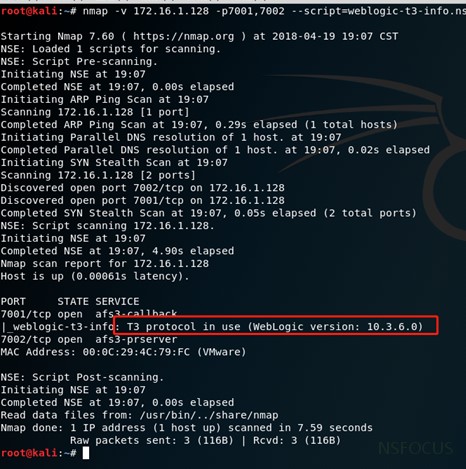
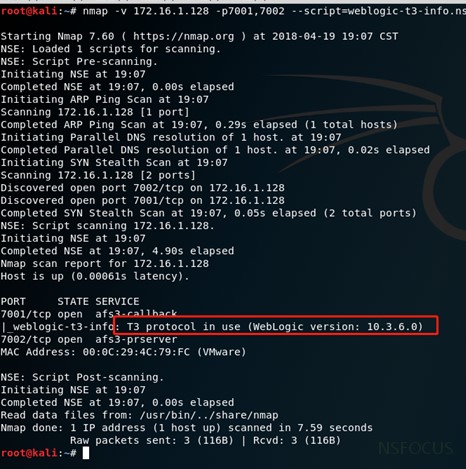
The Nmap tool provides a scanning script for the WebLogic T3 protocol to detect WebLogic hosts that enable the T3 service. The command is as follows:
nmap -n -v -Pn –sV [host or network segment address] -p7001,7002 –script=weblogic-t3-info.nse
As shown in the red mark of the following figure, the target has enabled T3 protocol and WebLogic version is within the affected range. If relevant personnel do not install official security patches, there will be a vulnerability risk.
Mitigation
Patch update
At present, Oracle has released patches to fix the above vulnerabilities. Please refer to the official notice to download the updated patch of the affected product in time, and install the update by referring to the readme file in the patch installation package to ensure long-term effective protection. Download link: https://support.oracle.com/rs?type=doc&id=3011291.2
Temporary Measures
If the user cannot install the update patch temporarily, take the following measures for temporary protection:
Restrict T3 protocol access
Users can temporarily block attacks that exploit T3 protocol vulnerabilities by controlling access to the T3 protocol. WebLogic Server provides a default connection filter named weblogic.security.net.ConnectionFilterImpl, which accepts all incoming connections. Access control can be performed on T3 and T3s protocols through the configuration rules of this connection filter. The detailed operation steps are as follows:
1. Go to the WebLogic console. On the configuration page of base_domain, go to the Security tab page and click Filters to configure connection filters.
2. Enter weblogic.security.net.ConnectionFilterImpl in the connection filter, and configure rules conforming to the actual situation of the enterprise in the connection filter rule by referring to the following writing:
127.0.0.1 * * allow t3 t3s
Local IP ** allow t3 t3s
IP allowed to be accessed * * allow t3 t3s
* * * deny t3 t3s
The connection filter rule format is as follows: target localAddress localPort action protocols, where:
- target specifies one or more servers to filter.
- localAddress can be used to define the host address of the server. (If an asterisk (*) is specified, the returned match will be all local IP addresses.)
- localPort defines the port on which the server is listening. (If an asterisk is specified, the match will return all available ports on the server).
- action specifies the operation to be performed. (Value must be “allow” or “deny”.)
- Protocols is a list of protocol names to be matched. (Must specify one of the following protocols: http, https, t3, t3s, giop, giops, dcom or ftp. If no protocol is defined, all protocols will match one rule.
3. If the rule does not take effect after saving, it is recommended to restart the WebLogic service (restarting the WebLogic service will cause business interruption. It is recommended that relevant personnel assess the risk before proceeding).
Taking the Windows environment as an example, the steps to restart the service are as follows:
Enter the bin directory under the directory where the domain is located, run stopWebLogic.cmd file in Windows system to terminate WebLogic service, and run stopWebLogic.sh file in Linux system.
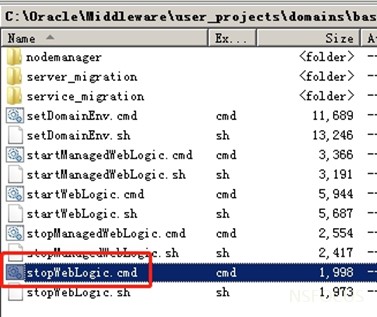
After the termination script is executed, run the startWebLogic.cmd or startWebLogic.sh file to start WebLogic to restart the WebLogic service.
Disable IIOP Protocol
Users can block attacks that exploit IIOP protocol vulnerabilities by disabling the IIOP protocol as follows:
In the WebLogic console, choose Service > AdminServer > Protocol and uncheck Enable IIOP.
Restart the WebLogic project to make the configuration take effect.
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
About NSFOCUS
NSFOCUS, a pioneering leader in cybersecurity, is dedicated to safeguarding telecommunications, Internet service providers, hosting providers, and enterprises from sophisticated cyberattacks.
Founded in 2000, NSFOCUS operates globally with over 4000 employees at two headquarters in Beijing, China, and Santa Clara, CA, USA, and over 50 offices worldwide. It has a proven track record of protecting over 25% of the Fortune Global 500 companies, including four of the five largest banks and six of the world’s top ten telecommunications companies.
Leveraging technical prowess and innovation, NSFOCUS delivers a comprehensive suite of security solutions, including the Intelligent Security Operations Platform (ISOP) for modern SOC, DDoS Protection, Continuous Threat Exposure Management (CTEM) Service and Web Application and API Protection (WAAP). All the solutions and services are augmented by the Security Large Language Model (SecLLM), ML, patented algorithms and other cutting-edge research achievements developed by NSFOCUS.
The post WebLogic T3/IIOP Information Disclosure Vulnerability (CVE-2024-21006/CVE-2024-21007) appeared first on NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks..
*** This is a Security Bloggers Network syndicated blog from NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks. authored by NSFOCUS. Read the original post at: https://nsfocusglobal.com/weblogic-t3-iiop-information-disclosure-vulnerability-cve-2024-21006-cve-2024-21007/
如有侵权请联系:admin#unsafe.sh
