2024-5-23 21:0:0 Author: www.tenable.com(查看原文) 阅读量:7 收藏
Context is critical in cloud security. In a recent RSA presentation, Tenable's Shai Morag offered ten tips for end-to-end cloud infrastructure security.
At the recent RSA Conference, Shai Morag, SVP and GM of Cloud Security at Tenable, led the session titled “Cloud Security Novice to Native in 10 Steps: A CNAPP Approach,” which delved into what it takes to protect cloud-native applications.
Morag noted that, although it’s been around for a while, the cloud is new to many.

In addition, security professionals are used to protecting on-premises resources. He said that the cloud is more complex than on-prem—especially in multi-cloud environments.
Meanwhile, breaches are happening at a furious pace. In fact, the Tenable 2024 Cloud Security Outlook showed that 95% of organizations reported a cloud security breach. The prevalence of breaches is a clarion call for an approach to cloud security beyond the array of point products that have sprouted in recent years.
Identity is the new perimeter
The rise of CIEM, which helps protect, analyze and govern access, has underscored the importance of managing identity risk and entitlement risk in the cloud.
“Identity is the new perimeter,” he said. “In cloud security, context is critical. When you think about visibility, when you think about prioritizing and assessing risk in your environment, context is king.”
A CNAPP that integrates CIEM functionality takes a holistic view of cloud security, Morag said. CNAPPs help with context, which provides a basis for understanding, analyzing and prioritizing risk.
CNAPP: Discover, manage risk and scale
Morag then dug into the ten steps for end-to-end cloud infrastructure security, divided into three stages: Discover, Manage Risk, and Scale.
1. Discover: All Assets

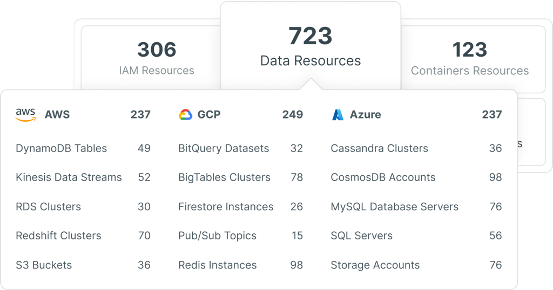
Morag said inventorying all the assets, the resources, the workloads, identities, and data can be hard because most companies utilize more than one cloud.
“You need to do it for your AWS environment, for your Azure environment, for your GCP, for your Ali cloud,” Morag said. “You need to make sure that you discover all assets and understand all the assets that you have.”
2. Discover: All relationships

The second step is about understanding all relationships. Morag said that a CNAPP can provide critical context, such as the relationships between assets, identities and risk.
It can also identify and prioritize remediation of toxic combinations, such as public workloads with critical vulnerabilities and high privileges.
3. Discover: All access to resources

At this step, Morag said it’s critical to discover what resources human and service identities can access. Then, it’s important to understand when the identities have accessed those resources and how long they’ve had access.
4. Manage risk: Understand your compliance and enterprise policy needs

“Before we analyze the risk, you need to understand what compliance and what policies you want to enforce in your cloud environments,” Morag said. “Do you need to support SOC2? Do you need to make sure that you’re PCI compliant? Do you need to make sure that you're SOX compliant?”
5. Manage risk: List all risks and compliance violations

“You need to understand all the risks, where you have risks, where you have violations of your policies, where you have things that don't meet your compliance and your standards that you need to support,” he said. “You need to see from low severity to high severity.”
6. Manage risk: Prioritize based on full-stack context

Morag said that you need to prioritize risks based on a full stack context.
It's very important to understand toxic combinations. A vulnerable machine that is publicly exposed can also assume a privileged identity. The risk adds up. This is only one example of a toxic combination. There are many others.
7. Manage risk: Visualize and deep-dive into findings

“After you prioritize all the risks and all the findings, you want to make sure that when you go to specific findings, you can visualize everything and deep dive into the findings,” Morag said. “Because sometimes it's very hard to understand what's going on and it's important to do so before you remediate.”
8. Manage risk: Remediate and drive least privilege and Zero Trust

Morag said that, when you’re remediating and preventing risk in your cloud, access risk tops the list.
Achieving least privilege ensures that people and machine identities aren’t over privileged.
9. Scale: Integrate findings within CI/CD

Step nine ensures the integration of findings in the CI/CD pipeline.
This shift left approach uncovers and remediates risks that are part of your code before they’re deployed to production.
10. Scale: Automate findings in DevSecOps workflows

At the last step, automation helps DevSecOps remove risk.
If there’s a misconfiguration in your production environment, you understand what's the origin in the code and developers get notifications and the context.
Applying the lessons learned
In closing, Morag advised security professionals on a timeline for evaluating a CNAPP.
- Week one: Discover the teams in your organization that secure your cloud. Then identify the decision-makers and their concerns.
- Three months: Identify whether your teams know who can access what in the cloud and when. Then discover the tools in use and the gaps. Finally, learn if your teams understand and can enforce least privilege.
- Six months: Select a CNAPP with tailored security and compliance automation. Then define priorities toward greater cloud security maturity.
Learn more about cloud security
To get more cloud security insights, attend our webinar "Tenable Shares Its 2024 Cloud Security Outlook: Winning Half the Battle by Understanding Barriers and Priorities," which will cover best practices to reduce the risk of cloud data breaches, ways to strengthen the weakest link in your cloud security environment and more.
如有侵权请联系:admin#unsafe.sh