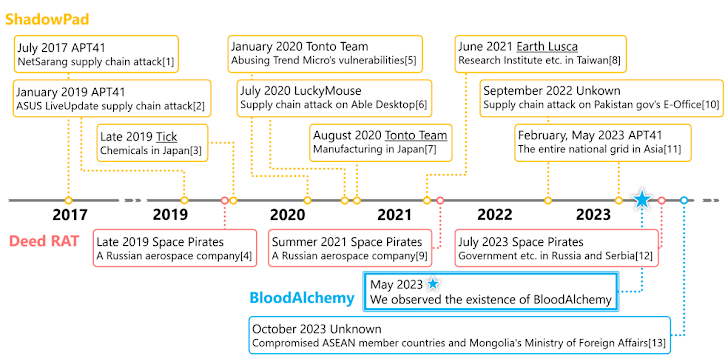
Cybersecurity researchers have discovered that the malware known as BLOODALCHEMY used in attacks targeting government organizations in Southern and Southeastern Asia is in fact an updated version of Deed RAT, which is believed to be a successor to ShadowPad.
"The origin of BLOODALCHEMY and Deed RAT is ShadowPad and given the history of ShadowPad being utilized in numerous APT campaigns, it is crucial to pay special attention to the usage trend of this malware," Japanese company ITOCHU Cyber & Intelligence said.
BLOODALCHEMY was first documented by Elastic Security Labs in October 2023 in connection with a campaign mounted by an intrusion set it tracks as REF5961 targeting the Association of Southeast Asian Nations (ASEAN) countries.
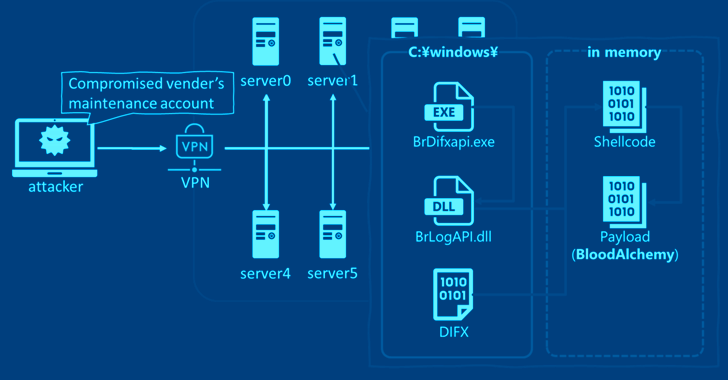
A barebones x86 backdoor written in C, it's injected into a signed benign process ("BrDifxapi.exe") using a technique called DLL side-loading, and is capable of overwriting the toolset, gathering host information, loading additional payloads, and uninstalling and terminating itself.
"While unconfirmed, the presence of so few effective commands indicates that the malware may be a subfeature of a larger intrusion set or malware package, still in development, or an extremely focused piece of malware for a specific tactical usage," Elastic researchers noted at the time.
Attack chains deploying have been observed compromising a maintenance account on a VPN device to gain initial access to deploy BrDifxapi.exe, which is then used to sideload BrLogAPI.dll, a loader that's responsible for executing the BLOODALCHEMY shellcode in memory after extracting it from a file named DIFX.
The malware employs what's called a run mode that determines its behavior, effectively allowing it to evade analysis in sandbox environments, set up persistence, establish contact with a remote server, and control the infected host through the implemented backdoor commands.
ITOCHU's analysis of BLOODALCHEMY has also identified code similarities with Deed RAT, a multifaceted malware exclusively used by a threat actor known as Space Pirates and is viewed as the next iteration of ShadowPad, which in itself is an evolution of PlugX.
"The first remarkably similar point is the unique data structures of the payload header in both BloodAlchemy and Deed RAT," the company said. "Some similarities have been found in the loading process of shellcode, and the DLL file used to read the shellcode as well."
It's worth noting that both PlugX (Korplug) and ShadowPad (aka PoisonPlug) have been widely utilized by China-nexus hacking groups over the years.
The disclosure comes as a China-linked threat actor known as Sharp Dragon (previously Sharp Panda) has expanded their targeting to include governmental organizations in Africa and the Caribbean as part of an ongoing cyber espionage campaign.
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.