2024-7-5 19:32:0 Author: securityaffairs.com(查看原文) 阅读量:7 收藏
Polyfill.io Supply Chain Attack: 384,773 hosts still embedding a polyfill JS script linking to the malicious domain

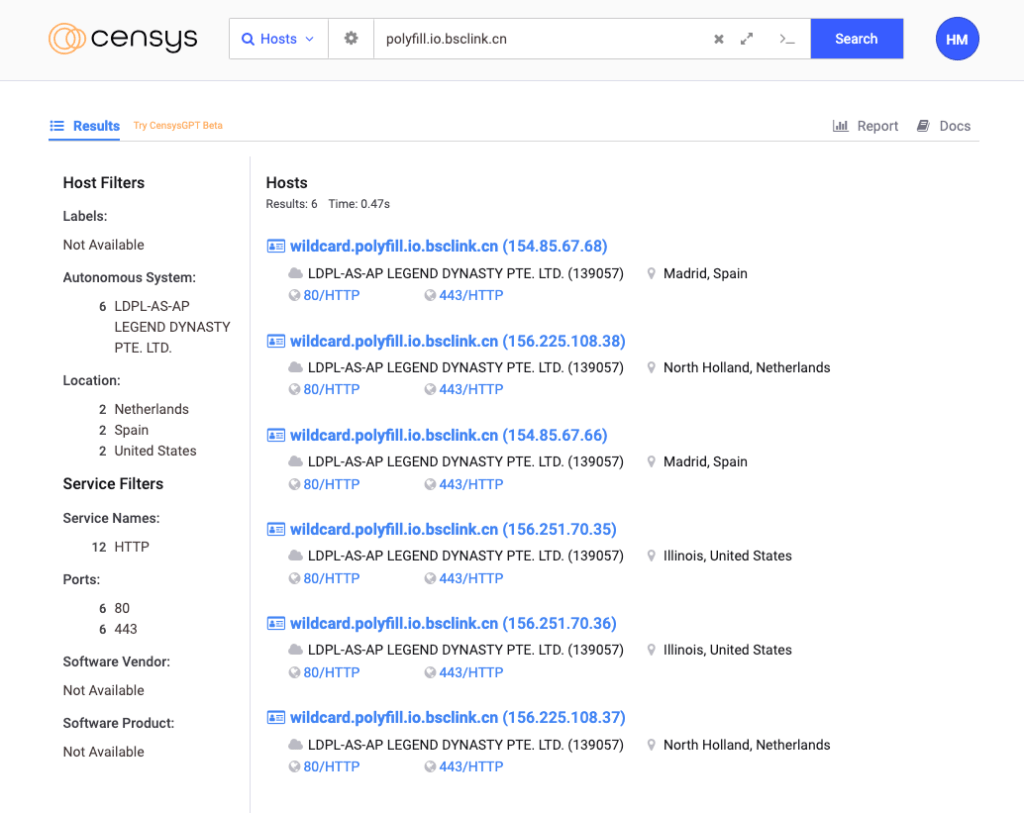
Cybersecurity company Censys has identified over 380,000 hosts that are still referencing the malicious polyfill.io domain.
Censys reported that over 380,000 internet-exposed hosts are still referencing the malicious polyfill.io domain.
The polyfill.io domain was suspended last week following multiple reports of malicious activity. The domain Polyfill.io was used to host JavaScript code that added modern functionality to older browsers that do not support certain web standards.
According to the reports, the domain was used to redirect the visitors of websites embedding polyfill.io code to betting and adult sites.
The experts estimated that over 100,000 websites were impacted.
Your sentence is clear and well-structured. Here is a slightly refined version for smoother readability:
As of July 2, 2024, Censys still detects 384,773 hosts, primarily in Germany, embedding a polyfill JavaScript script that references the malicious polyfill.io domain.
“Censys has identified a significant number of web hosts using the polyfill.io CDN. As of the latest data, 384,773 hosts were found to include references to “https://cdn.polyfill[.]io” or “https://cdn.polyfill[.]com” in their HTTP responses.” reads the report from Censys. “A notable concentration of these hosts, approximately 237,700, are located within the Hetzner network (AS24940), primarily in Germany. This is not surprising – Hetzner is a popular web hosting service, and many website developers leverage it.”
These hosts include websites associated with major platforms, including Hulu, Mercedes-Benz, and WarnerBros. The experts urge website owners to remove any references to polyfill.io and its associated domains from their codebase as a precautionary measure.
Censys also noticed that 182 affected hosts were government (“.gov”) websites using the polyfill.io script.
The experts highlighted that the supply chain attack has had a widespread impact.
“Cloudflare and Fastly have created alternative secure polyfill endpoints for users to mitigate the threat while preventing websites from breaking. Censys has observed 216,504 hosts referencing one of these alternative polyfill endpoints: “polyfill-fastly.io” or “cdnjs.cloudflare.com/polyfill”, an increase from the 80,312 we observed last Friday, June 28.” Censys continues.
Censys also spotted a post published by a Chinese developer on a forum that was warning about a malicious JavaScript file on cdn.bootcss.com, similar to polyfill.io, redirecting users based on geolocation. The experts discovered 1.6 million public-facing hosts referencing these domains, with bootcss.com involved in malicious activity.
“When we dug in Censys Search for any exposed hosts referencing one of the additional suspicious domains, we observed a total of 1,637,160 public-facing hosts combined linking to one of these.” concludes the report. “So far, this domain (bootcss.com) is the only one showing any signs of potential malice. The nature of the other associated endpoints remains unknown, and we avoid speculation. However, it wouldn’t be entirely unreasonable to consider the possibility that the same malicious actor responsible for the polyfill.io attack might exploit these other domains for similar activities in the future.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, supply chain attack)
如有侵权请联系:admin#unsafe.sh
