2024-7-25 18:16:21 Author: therecord.media(查看原文) 阅读量:7 收藏
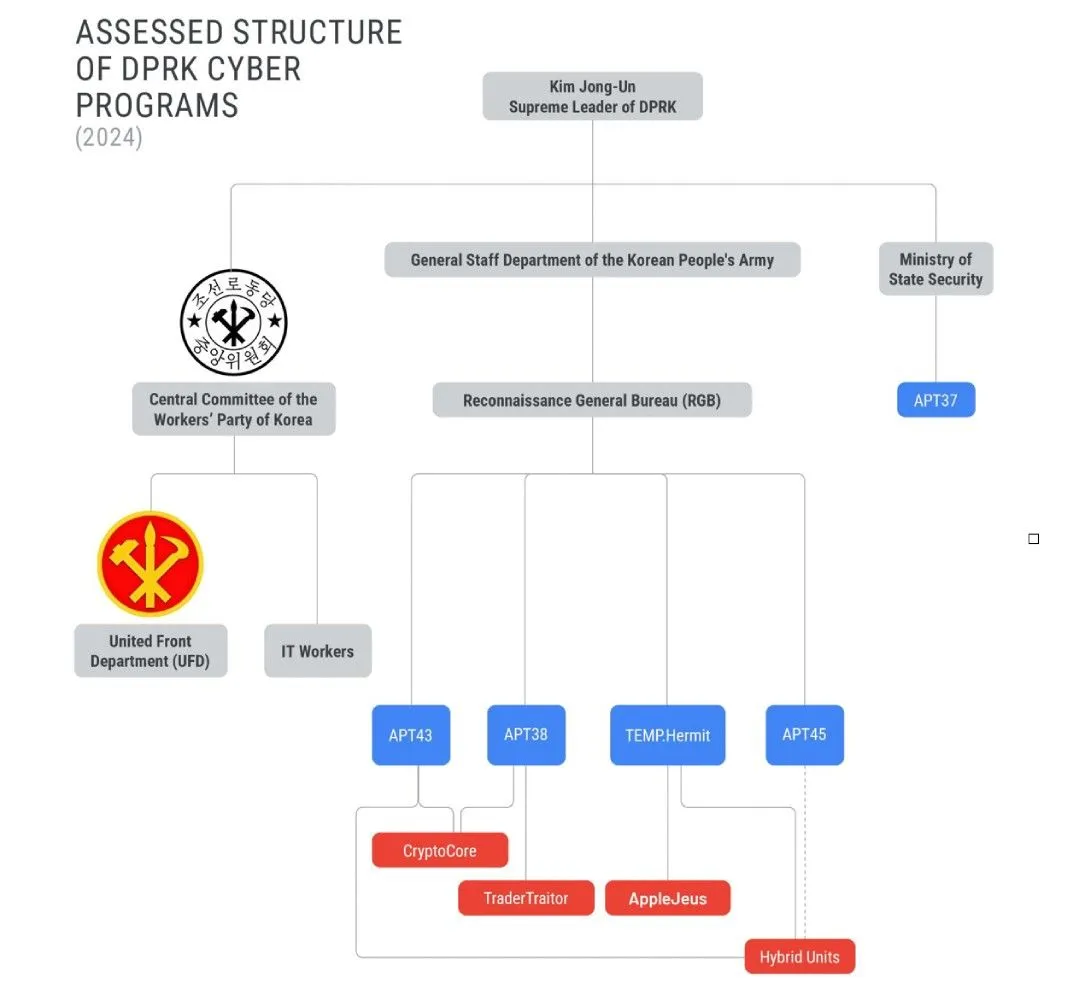
A notorious North Korean hacking group has been accused of stealing sensitive information and blueprints about guns, torpedoes and other weapon systems. Cybersecurity firm Mandiant published on Thursday the results of a two-year investigation into Andariel — a well-known group of hackers U.S. officials believe is tied to North Korea’s intelligence office, the Reconnaissance General Bureau. Researchers said Andariel has launched several large, impactful cyber operations that targeted critical infrastructure — expanding beyond government espionage campaigns into ransomware attacks on hospitals, banks and South Korean defense firms. Michael Barnhart, who leads Mandiant’s North Korean threat-hunting team, told Recorded Future News that many advances in North Korea’s military capabilities in recent years can directly be attributed to the group’s successful espionage efforts against governments and defense organizations around the world. Due to the group’s increasing sophistication, Mandiant said it was giving Andariel an advanced persistent threat (APT) tag of APT45. “When Kim Jong Un demands better missiles, these are the guys who steal the blueprints for him. APT45 isn’t bound by ethical considerations and have demonstrated they’re willing and agile enough to target any entity to achieve their objectives, including hospitals,” Barnhart said. Image: Mandiant “A coordinated global effort involving both public and private sectors is necessary to counter this persistent and evolving threat.” Mandiant said it worked alongside the FBI and other government agencies to track the group’s attacks on healthcare providers, defense contractors and government nuclear facilities around the world. Mandiant said experts and government agencies have been alarmed by APT45’s ability to steal sensitive plans about a range of weapons and tools including: Mandiant said the group’s espionage campaigns date back to 2009 and it has gradually expanded into financially-motivated attacks — its use of ransomware separates it from other North Korean operators. Some strains of malware used by the group are distinct from the toolset used by other groups in the country. In 2019, the group targeted Kudankulam Nuclear Power Plant in India, Mandiant said, adding that other nuclear facilities and power plants were targeted. The group also went after the crop science division of a multinational corporation in 2020 and several healthcare and pharmaceutical verticals over the last four years. Image: Mandiant “APT45 is one of North Korea’s longest running cyber operators, and the group’s activity mirrors the regime’s geopolitical priorities even as operations have shifted from classic cyber espionage against government and defense entities to include healthcare and crop science,” the researchers said. “Financially motivated activity occurring alongside intelligence collection has become a defining characteristic of North Korean cyber operations, and we expect APT45 to continue both missions. As the country has become reliant on its cyber operations as an instrument of national power, the operations carried out by APT45 and other North Korean cyber operators may reflect the changing priorities of the country’s leadership.” The report notes that the group has been tied to the Lazarus Group — another North Korean operation that has conducted dozens of hacks on financial institutions. In December, the Seoul Metropolitan Police accused APT45 of stealing sensitive information about anti-aircraft weapon systems from South Korean companies. South Korea’s government warned in April that the group spent most of 2022 and 2023 infiltrating the networks of 83 South Korean defense companies or their contractors. The group was sanctioned in 2019 by the U.S. Treasury, which said the group “consistently executes cybercrime to generate revenue and targets South Korea’s government and infrastructure in order to collect information and to create disorder.” 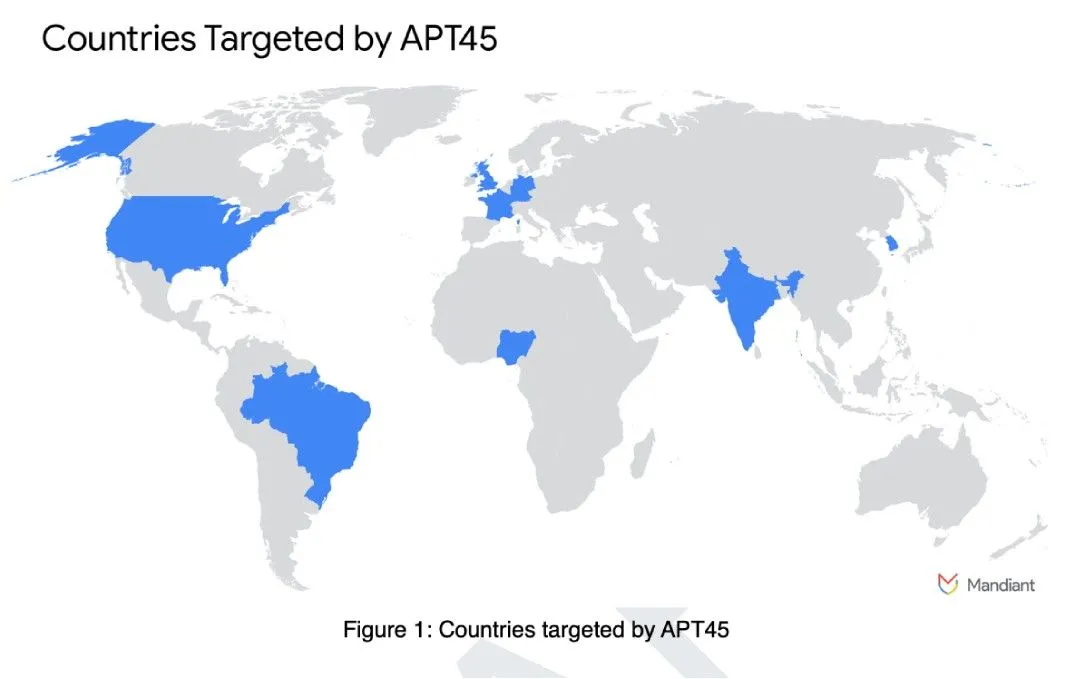
Get more insights with the
Recorded Future
Intelligence Cloud.
No previous article
No new articles
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.
如有侵权请联系:admin#unsafe.sh
