2024-8-19 04:3:5 Author: hackernoon.com(查看原文) 阅读量:2 收藏
Cryptography comes from Ancient Greek, and it means something like a secret or hidden writing. That’s how this discipline started: someone would write a message for another party but use various techniques to keep it secret from others. For instance, they might change the usual order of letters or words, with the correct order known only to the recipient. Things have evolved a lot from that point, but that’s the gist.
In more modern times, we can define cryptography as the science of securing digital information and communications through complex mathematical techniques, but it's also an intersection with computer science, information security, physics, and even more. It ensures that data (often digital data) remains confidential, authentic, and unaltered.
Practical uses of cryptography in our era include protecting personal information on devices, ensuring the privacy of emails and messages, safeguarding sensitive material, enabling secure access to online accounts, and securing online transactions. As you may imagine, that’s where cryptocurrencies enter this topic.
The “crypto” bit comes from cryptography, because cryptocurrencies are, basically, digital coins made of pure cryptography (complex mathematics). Beyond what we can or need to see, their inner workings are full of algorithms and long alphanumeric strings, sometimes only readable and understandable by machines. In the end, this is the reason why they exist at all.
Public Key Cryptography
There are numerous existing cryptographic techniques, and even new ones being developed right now. Cryptocurrencies use several of those techniques already, but maybe the main one for the absolute majority is public key cryptography or
By "keys" here, we mean long strings of characters typically represented as sequences of bits (binary digits). In cryptocurrencies, private keys are used to sign transactions, and public keys are used to verify the signatures. This ensures that only the owner of a cryptocurrency address can authorize transactions from that address.
Public key cryptography plays a vital role in ensuring the security and integrity of transactions for cryptocurrencies. For instance, when Alice wants to send five coins to Bob, she signs the transaction with her private key, generating a unique digital signature that proves she authorized it. She then broadcasts the signed transaction to the cryptocurrency network. Nodes in the network receive the transaction and use Alice's public key to verify the signature. Once verified, the transaction is added to the chain, reducing Alice’s balance by five coins and increasing Bob’s balance by the same amount. This process prevents unauthorized access and tampering, ensuring the transaction’s security.
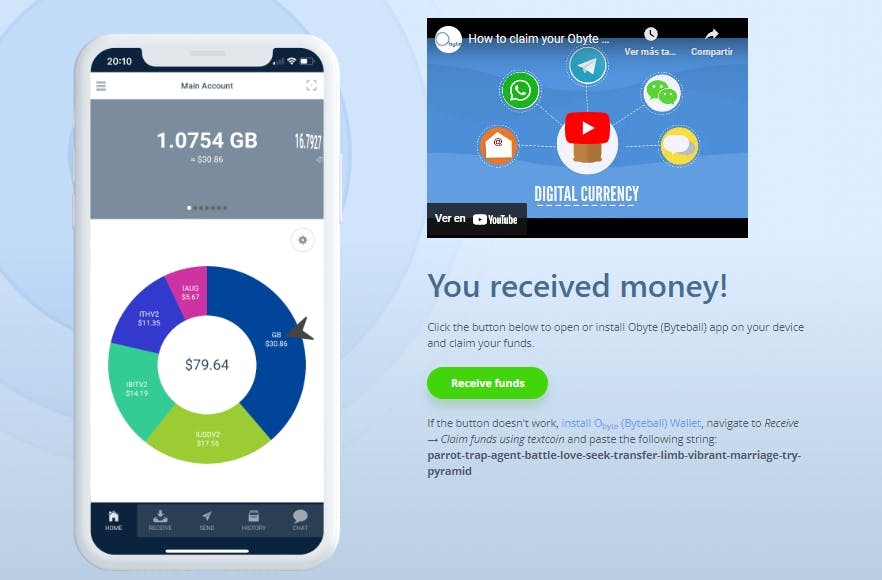
All of this happens in the background, though. Final users see public keys as crypto addresses (shareable with anyone) and private keys in the form of private seeds (strings of random words to keep private and recover wallets). Beneath what we can see in our apps, they both look like long and barely legible alphanumeric strings. Crypto addresses are, let’s say, the shorter version. Even if they still are sort of long and complex.
Simplifying Cryptos
Obyte simplifies cryptography in cryptocurrencies with textcoins, making digital currency accessible without a steep learning curve. Textcoins allow users to send and receive funds through familiar methods like email, instant messaging, or even on paper. A textcoin is essentially a string of twelve random words or a link that contains cryptocurrency. This means someone can carry a piece of paper with these words and redeem the funds later when they have access to the Internet and an
Moreover,
Featured Vector Image by
如有侵权请联系:admin#unsafe.sh

