
2024-8-19 17:55:19 Author: www.sentinelone.com(查看原文) 阅读量:51 收藏
Executive Summary
- Xeon Sender is a Python script that sends spam through nine different SaaS providers.
- First seen in 2022, Xeon Sender has been repurposed by multiple threat actors branding the tool as their own, a common occurrence in the cloud hacktool scene.
- Xeon Sender is another tool that enables SMS spam and smishing, which are increasingly popular TTPs to execute via cloud and SaaS.
Overview
Xeon Sender (aka XeonV5, SVG Sender) is a cloud attack tool that can be used to send Short Message Service (SMS) messages en masse to conduct spam and phishing (aka smishing) campaigns. Attackers can use Xeon to send messages through multiple software-as-a-service (SaaS) providers using valid credentials for the service providers. There are no weaknesses on the service provider side that are leveraged for these attacks; rather, the tool uses legitimate APIs to enable bulk SMS spam attacks.
The service providers this tool uses include:
- Amazon Simple Notification Service (SNS)
- Nexmo
- Plivo
- Proovl
- Send99
- Telesign
- Telnyx
- TextBelt
- Twilio
We found Xeon Sender being distributed through Telegram–the standard cloud hacktool distribution platform–as well as various smaller hacking forums and sites. There is no apparent relationship between Xeon Sender and the family of Intel processors with the same name.
History & Distribution
The earliest known version of Xeon Sender dates back to at least 2022 in a version that credits handle @darkworld47. Like many other cloud hacktools, Xeon Sender became a victim of its own success, with different actors regularly adding their own handle to the tool credits.
Aside from the tool’s purported author and occasionally the tool name, there are no significant differences across any samples we identified.

One of the older versions gives credit to a Telegram channel known for distributing cracked hacktools and also credited in older versions of the AlienFox cloud infostealer. The most recent version credits the script to a Telegram channel with over 200 members, where the author posts various tools and shares details and screenshots of how the tools work.

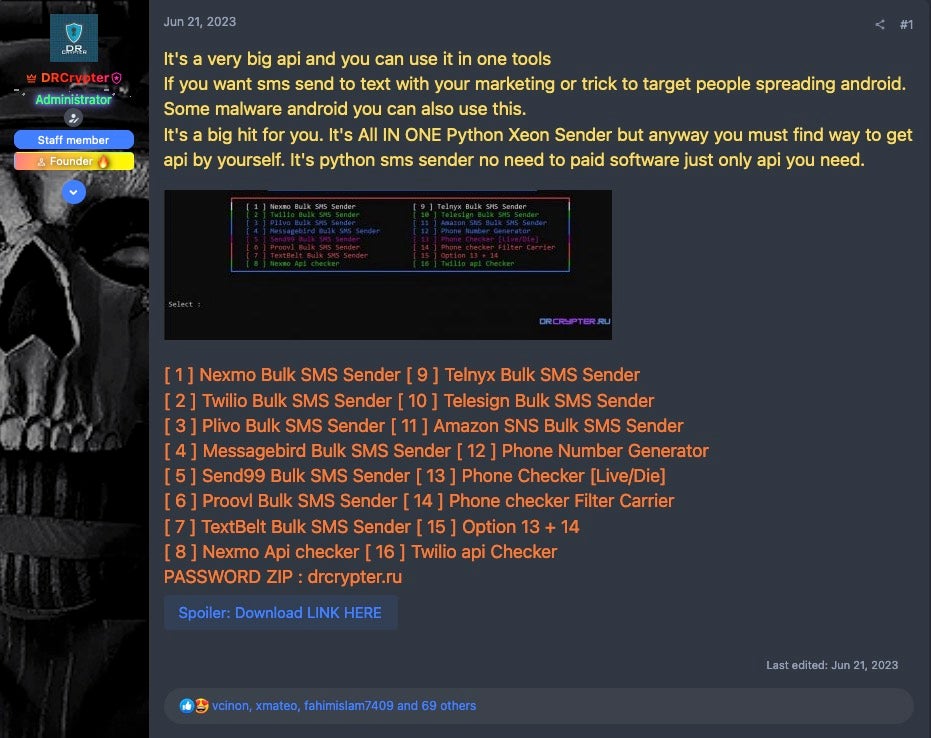
In June 2023, Xeon Sender was posted on a hacktool and cybercrime discussion forum by the administrator. The post received more than 70 user “Likes” and 5 pages of comments.
Another incarnation of the tool is hosted on a webserver with a GUI. This hosting method removes a potential barrier to access, enabling lower skilled actors who may not be comfortable with running Python tools and troubleshooting their dependencies.

We also identified a version called SVG SMS attributed to Savage Benz aka @spamsznon Telegram, marking another alias for this tool.

Features
Xeon Sender is a tool that lets attackers conduct SMS spam attacks via one of nine bulk SMS providers. The tool provides a simple CLI for the attacker to communicate with the targeted service provider backend using APIs, enabling bulk SMS spam attacks with minimal effort. For the tool to work, the actor must have API keys for the targeted service. Enabling these service providers’ SMS APIs is an arduous task guided by federal regulations in the United States. This means actors are likely to seek credentials belonging to accounts that have already undergone the process.
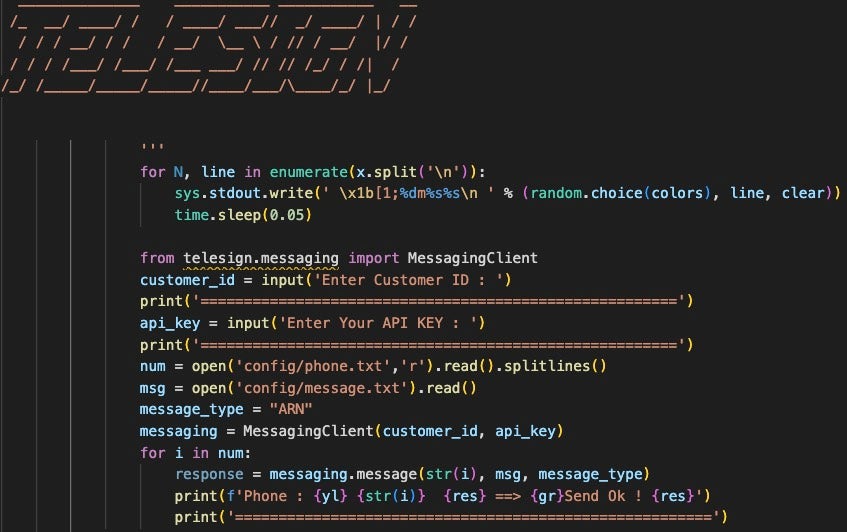
Each service provider-specific action is controlled by a method from the script’s main class. The methods require several values from the operator:
- API Key
- Secret Key
- AWS Region – for AWS Simple Notification Service (SNS) only
- Customer ID – for Telesign only, specifies the Telesign account
- Sender ID – a phone number or name, varies per service provider
- Message contents – stored in tool’s
config/message.txt - List of recipient phone numbers – stored in tool’s
config/phone.txt
With these values, the tool uses the Python requests library to craft an API request to the targeted service using the credentials or a service-specific module, such as Twilio’s twilio.rest or messagebird in the case of Twilio and MessageBird. The exception to this is the Proovl module, which uses a combination of Python’s urllib and manually crafted HTTP headers. The Proovl request is sent with the user-agent string Mozilla/5.0 (Windows NT 6.1; Win64; x64), which is often followed by more details about the client, so it should not be relied on for detection engineering purposes.
In each provider-specific function, the request includes the sender ID and the SMS message contents, and one of the phone numbers from the phone.txt list. The script will loop through the phone.txt list until each phone number has been accessed, taking a 50 millisecond sleep between each iteration.
In addition to the SMS sending methods, there are several related utilities, including:
- Account Checker Tools: Validates credentials for Nexmo and Twilio accounts.
- Phone Number Generator: Takes arguments for the Country Code and Area Code, as well as the length of the phone number. Uses the Python
randommodule to generate a phone number of the given length. - Phone Checker: This method checks a given phone number against the APILayer.com Number Verification API to check if the number is valid.
Xeon Sender lacks the polish that would make the tool have appeal for more professional applications. The script contains some error handling, but there is little clarity with certain API calls. The methods that interact with several SMS providers–including Send99, Plivo, TextBelt, Nexmo–have conditions for error handling and report a status message. However, several providers–including larger providers such as AWS SNS and Twilio–report only a ‘Success’ message regardless of request’s outcome or server response HTTP status code. Further, the developer uses ambiguous variables such as single letters or a letter plus a number, which makes debugging slightly more difficult.
Detection Opportunities
Xeon Sender largely uses provider-specific Python libraries to craft API requests, which presents interesting detection challenges. Each library is unique, as are the provider’s logs. It may be difficult for teams to detect abuse of a given service.
To defend against threats like Xeon Sender, organizations should monitor activity related to evaluating or modifying SMS sending permissions or anomalous changes to distribution lists, such as a large upload of new recipient phone numbers.
For organizations using AWS, this includes calls to the GetSMSAttributes AWS API or changes to existing permissions using calls to SetSMSAttributes. Xeon Sender does not directly handle this, so actors who use Xeon likely use other tools or sources for preliminary reconnaissance and credential validation.
Conclusion
Xeon Sender is another tool that gives defenders insight into how actors attack cloud services to send SMS spam, an ongoing trend highlighted in research on tools like SNS Sender and through similar smishing campaigns. Due to federal regulations and related fees imposed by bulk SMS providers, threat actors are more likely to target accounts belonging to organizations that have already gone through this process than to make accounts independently, not to mention costs for message delivery as a separate financial burden.
Attribution remains open to interpretation in the context of script-based cloud attack tools where one actor can easily put their name inside a tool to replace the previous author. Despite many actors claiming this tool as their own, we have observed no significant deviations between known versions. There are clear improvements that could be made, such as improved status and error handling. Other tools like AlienFox have evolved over time as different actors adapt the tools, often bringing improvements. Actors may ultimately improve on Xeon Sender, or roll features into a multi-tool that covers more attack categories.
Indicators of Compromise
Xeon Sender SHA-1
078e90c959e3290a4f716fbf4e1d09fe46aaa68b
08d7091b7a9907a6f5894f31cd34e3e8e11cc026
3597915cfbbcc7ea135bf889a89bff635c825e0d
4863a15f85cd0f16ad65434de2122324c04a868a
4e6e8b074943c7fab3206ddb0abf571ffaf68523
9b01d82ceb710df3f51e52a1726b0cda85b47672
ac1d71228114bd95647683e842d42e81a6e97a88
bff95ff87e4081386a6ce6b8289e1524a4a4bd47
e0981369347062ac7f3eb32b833eb4264577e073
f192bb0e141c48e5b0bf46083e30823ea58e8bb3
Xeon Sender Archive SHA-1
a19db8716c39454bf363327441dc2e5f46810c30
33c622345804b46d0494f83720fad45ec0df3e97
7a7d57ed5f24772afa07ad24313ace5d84646a49
如有侵权请联系:admin#unsafe.sh