
2020-04-06 22:56:27 Author: wiki.ioin.in(查看原文) 阅读量:833 收藏
Hi there,
I’m a security researcher & bug hunter, but still learning. I want to share how hard it was to find an XSS (Cross-Site Scripting) on such a huge organization and well secured Twitter.com and how I could achieve it with combining another security vulnerability CSP (Content Security Policy) bypass.
Here is the story:
After digging a lot on Twitter’s subdomains, I came across to https://careers.twitter.com/. As you can guess, it is Twitter’s career site, you can search for jobs as an opportunity to work with them, but I search for bugs.
Sometime later, I thought I’ve found a reflection for an XSS on the URL:
https://careers.twitter.com/en/jobs-search.html?location=1" onmouseover=”alert(1)&q=1&start=70&team=
with the location parameter.

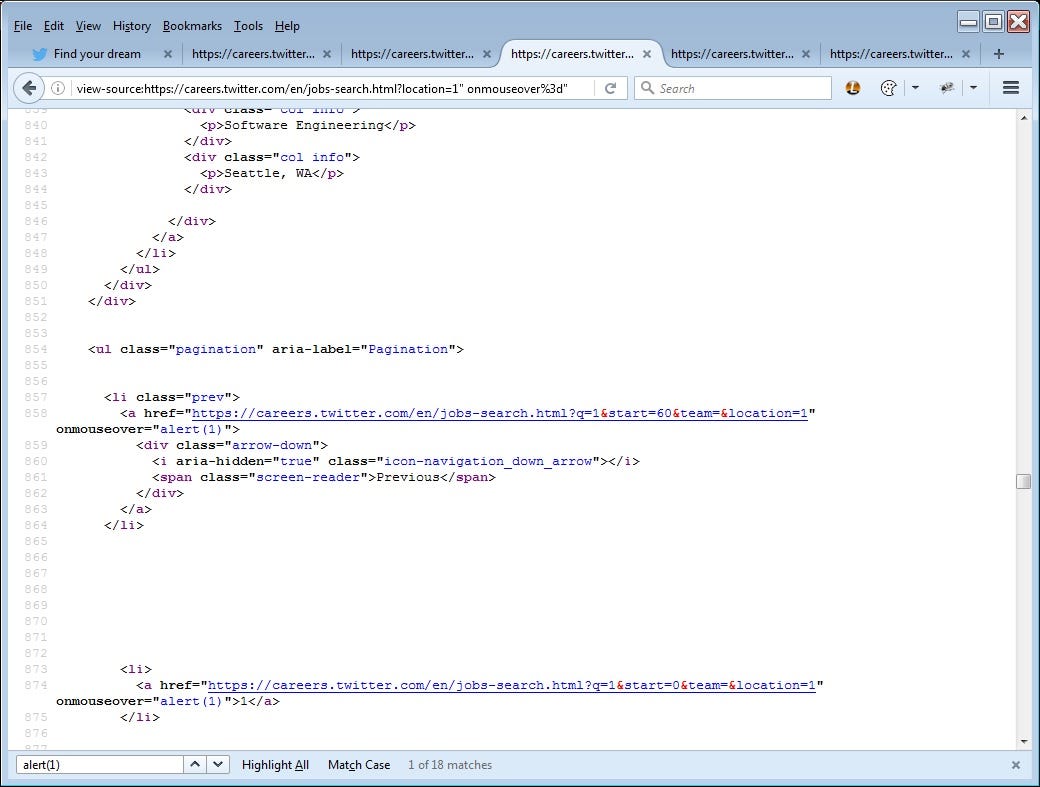
But wait, there was no alert! I couldn’t be able to trigger it! Because they’ve implemented CSP as:
content-security-policy: default-src ‘self’ ; connect-src ‘self’ ; font-src ‘self’ https://*.twimg.com https://*.twitter.com data:; frame-src ‘self’ https://twitter.com https://*.twitter.com [REDACTED] https://*.twitter.com; report-uri https://twitter.com/i/csp_report
and It blocked the javascript alert box to become to scene. So, I was unsuccessful in getting this work, unfortunately. Then I applied to my master @brutelogic as always and asked him that I’ve found some XSS (didn’t share the details nor domain) but I could not be able to get it to work because of the CSP. He advised me to find a way to bypass it! I already remember his saying: “For god’s sake, stop talking and go find a way to bypass the CSP!”. Thanks bro :)
I tried a lot to find the way and gave up that time. After trying a lot and looking for something on other domains, I figured out an URL that’s going under the radar within GET requests hiddenly. URL was:
The response Content-type was application/javascript and what I write as the parameter tpm_cb, it was reflecting on the page!


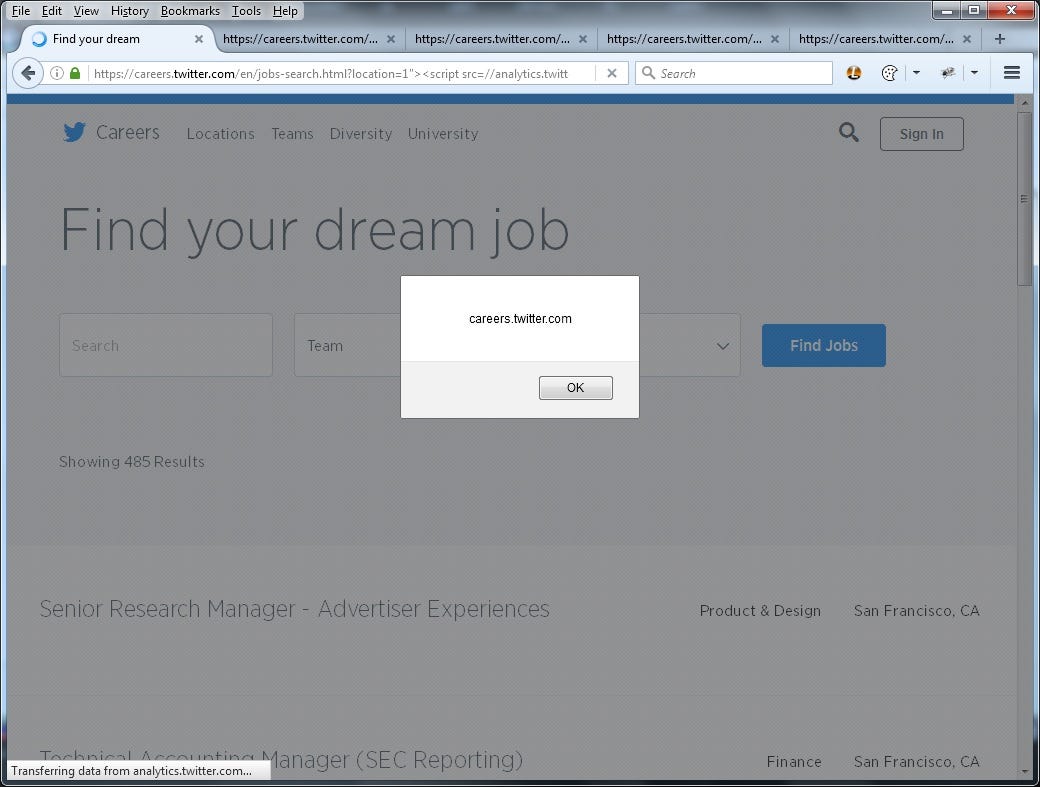
I was lucky this time, and I tried to combine both my findings to make the XSS work. So, I created:
https://careers.twitter.com/en/jobs-search.html?location=1"><script src=//analytics.twitter.com/tpm?tpm_cb=alert(document.domain)>//
willing “><script src= on the XSS reflection will work.
And voila! It worked!

Happy End!
I screamed out in my office and all my colleagues were afraid. Sorry, guys :)
I immediately reported these to Twitter via their bug bounty program on Hackerone, they triaged and rewarded me very quickly. Also, they fixed the XSS on career site but CSP bypass took a long time to fix. But in the end, both sides were satisfied. Thanks to Twitter Security Team and an awesome community Hackerone!
Hope this helps newbies like me to develop themselves. And If you want to share your thoughts, just ping me on Twitter: h1_kenan
Thanks for reading.
如有侵权请联系:admin#unsafe.sh