- What is Nmap?
- What does Nmap do:
- Download & Install Nmap
- Nmap Commands
- Nmap Cheatsheet
- Nmap Enumeration Command Examples
- Nmap Scan Tuning & Optimisation
- Document Changelog
The following NMAP cheat sheet aims to explain what Nmap is, what it does, and how to use it by providing NMAP command examples in a cheat sheet style documentation format.
What is Nmap?
Nmap (network mapper), the god of port scanners used for network discovery and the basis for most security enumeration during the initial stages of a penetration test. The tool was written and maintained by Fyodor AKA Gordon Lyon.
Nmap displays exposed services on a target machine along with other useful information such as the verion and OS detection.
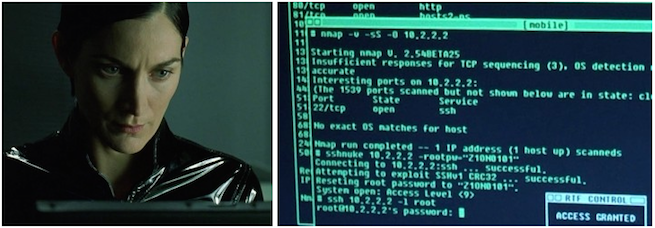
Nmap has made twelve movie appearances, including The Matrix Reloaded, Die Hard 4, Girl With the Dragon Tattoo, and The Bourne Ultimatum.

What does Nmap do:
- Host discovery
- Port discovery / enumeration
- Service discovery
- Operating system version detection
- Hardware (MAC) address detection
- Service version detection
- Vulnerability / exploit detection, using Nmap scripts (NSE)
- Nmap IDS / Portscan Detection & Scan Time Optimisation
Download & Install Nmap
Nmap can be downloaded from nmap.org, however commonly Nmap is installed via your Linux distributions package manager:
Debian / Ubuntu / Kali
How to Install NMAP on Ubuntu, Debian, Kali or other Linux systems using the APT package manager.
apt install nmapNmap RHEL / Fedora
How to Install NMAP on RHEL, Fedora, CentOS, Rocky Linux or other Linux systems using the DNF package manager.
dnf install nmapNmap Windows
Download Nmap for Windows and install: Nmap for Windows
Nmap MacOS
How to install nmap on MacOS using Brew.
brew install nmapNmap Commands
Basic Nmap scanning command examples, often used at the first stage of enumeration.
Agressive scan timings are faster, but could yeild inaccurate results!
T5 uses very aggressive scan timings and could lead to missed ports, T4 is a better compromise if you need fast results.
Nmap scan from file
Nmap Scan all Ports
Nmap output formats
Nmap Netbios Examples
--script-args=unsafe=1 has the potential to crash servers / services
Becareful when running this command.
Nmap Nikto Scan
Nmap + Nikto scanning for specific discovered HTTP ports.
Nmap Cheatsheet
Target Specification
Nmap allows hostnames, IP addresses, subnets.
Example blah.highon.coffee, nmap.org/24, 192.168.0.1; 10.0.0-255.1-254
Host Discovery
Scan Techniques
Port Specification and Scan Order
Service Version Detection
Script Scan
OS Detection
Timing and Performance
Options which take TIME are in seconds, or append 'ms' (milliseconds), 's' (seconds), 'm' (minutes), or 'h' (hours) to the value (e.g. 30m).
Firewalls IDS Evasion and Spoofing
Nmap Scan Output File Options
Misc Nmap Options
Nmap Enumeration Command Examples
The following are real world examples of Nmap enumeration.
Enumerating Netbios
The following example enumerates Netbios on the target networks, the same process can be applied to other services by modifying ports / NSE scripts.
Detect all exposed Netbios servers on the subnet.
Nmap find exposed Netbios servers
root:~# nmap -sV -v -p 139,445 10.0.1.0/24
Starting Nmap 6.47 ( http://nmap.org ) at 2014-12-11 21:26 GMT
Nmap scan report for nas.decepticons 10.0.1.12
Host is up (0.014s latency).
PORT STATE SERVICE VERSION
139/tcp open netbios-ssn Samba smbd 3.X (workgroup: MEGATRON)
445/tcp open netbios-ssn Samba smbd 3.X (workgroup: MEGATRON)
Service detection performed. Please report any incorrect results at http://nmap.org/submit/ .
Nmap done: 256 IP addresses (1 hosts up) scanned in 28.74 seconds
</p>
Nmap find Netbios name.
Nmap find exposed Netbios servers
root:~# nmap -sU --script nbstat.nse -p 137 10.0.1.12
Starting Nmap 6.47 ( http://nmap.org ) at 2014-12-11 21:26 GMT
Nmap scan report for nas.decepticons 10.0.1.12
Host is up (0.014s latency).
PORT STATE SERVICE VERSION
137/udp open netbios-ns
Host script results:
|_nbstat: NetBIOS name: STARSCREAM, NetBIOS user: unknown, NetBIOS MAC: unknown (unknown)
Nmap done: 256 IP addresses (1 hosts up) scanned in 28.74 seconds
</p>
NMAP Netbios MS08-067
How to scan a target and identify if it is vulnerable to MS08-067
Nmap check MS08-067
root:~# nmap --script-args=unsafe=1 --script smb-check-vulns.nse -p 445 10.0.0.1
Nmap scan report for ie6winxp.decepticons (10.0.1.1)
Host is up (0.00026s latency).
PORT STATE SERVICE
445/tcp open microsoft-ds
Host script results:
| smb-check-vulns:
| MS08-067: VULNERABLE
| Conficker: Likely CLEAN
| regsvc DoS: NOT VULNERABLE
| SMBv2 DoS (CVE-2009-3103): NOT VULNERABLE
|_ MS07-029: NO SERVICE (the Dns Server RPC service is inactive)
Nmap done: 1 IP address (1 host up) scanned in 5.45 seconds
</p>
The information gathered during the enumeration indicates the target is vulnerable to MS08-067, exploitation will confirm if it’s vulnerable to MS08-067.
Nmap Scan Tuning & Optimisation
Nmap Rate
To speed up your scan increase the rate, be aware that setting a high rate value will result in a less accurate scan.
--max-rate
--min-rate NMAP Parallelism
The maximum or minimum amount of parallel tasks scanned at the same time (in parallel).
TIP: If you have an basic IDS / portscan detection blocking your scans you could lower the –min-parallelism in an attempt to reduce the number of concurrent connections
--min-parallelism
--max-parallelismNMAP Host Group Sizes
The number of hosts scanned at the same time, Note: if you are writing output to a file e.g., -oA you will need to wait for the host group to complete scanning before the nmap output will be written to the file. Therefore if you get a lagging host you will may end up waiting a while for the output file, which brings us on to… host timeout.
--min-hostgroup
--max-hostgroup NMAP Host Timeout
Nmap allows you to specify the timeout, which is the length of time it waits before giving up on the target. Be careful setting this super low, as you may end up with inaccurate results.
The following example would giveup after 50 seconds.
--host-timeout 50 NMAP Scan Delay
An extremely useful option to defeat basic port scan detection (SOHO devices and some IDS) that essentially monitor and block X amount of connects per second (syn flood etc).
--scan-delay 5s For example if you know you can get away with 2 req/sec without getting blacklisted then you could use:
--scan-delay 1.2added 200ms for a buffer
NMAP Disable DNS Lookups
Assuming you do not want domain names being looked up, use the -n flag to dissable resolution and speed up the scan.
NMAP Black List Detection?
- It ussally takes and extemely long time to complete
- Droppped probes nmap will increase the timeout, but it’s likely you are already black listed
- To confirm, recheck a port that you know was open before
As far as I know there is no way of detecting for black listing within nmap natively.
NMAP Optimising Portscans for Targets
Once you have identified a target firewall / IDS you can look up the default settings for the portscan black list by reading the manual and use the nmap command switches above to obtain the best performance without getting black listed.
If you found this Nmap cheat sheet useful, please share it below.
Document Changelog
- Original Post Date: 13/12/2014
- Last Updated: 12/02/2024 (12th of February 2024)
- Author: Arr0way
- Notes: Checked syntax was current for latest version of Nmap.
如有侵权请联系:admin#unsafe.sh