2021-05-21 20:37:11 Author: hakin9.org(查看原文) 阅读量:221 收藏
![]() Free Software, requires only free accounts to third part services
Free Software, requires only free accounts to third part services ![]()
Lack of knowledge ... that is the problem.
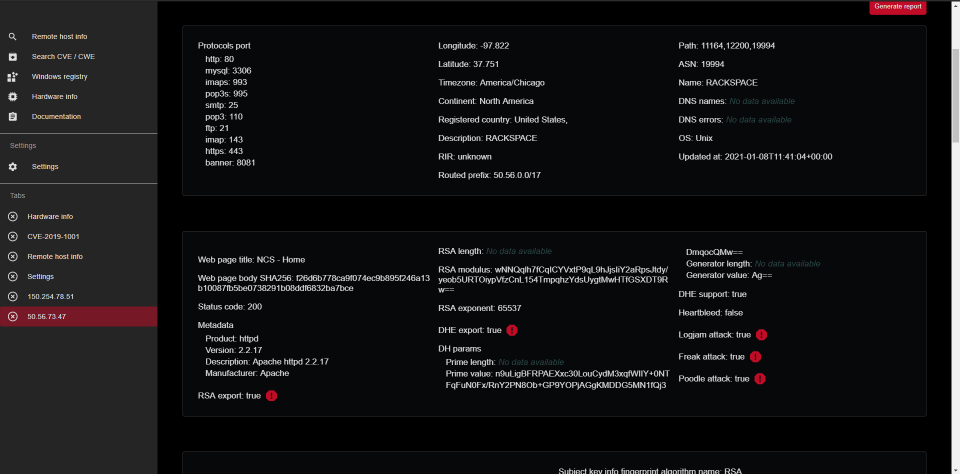
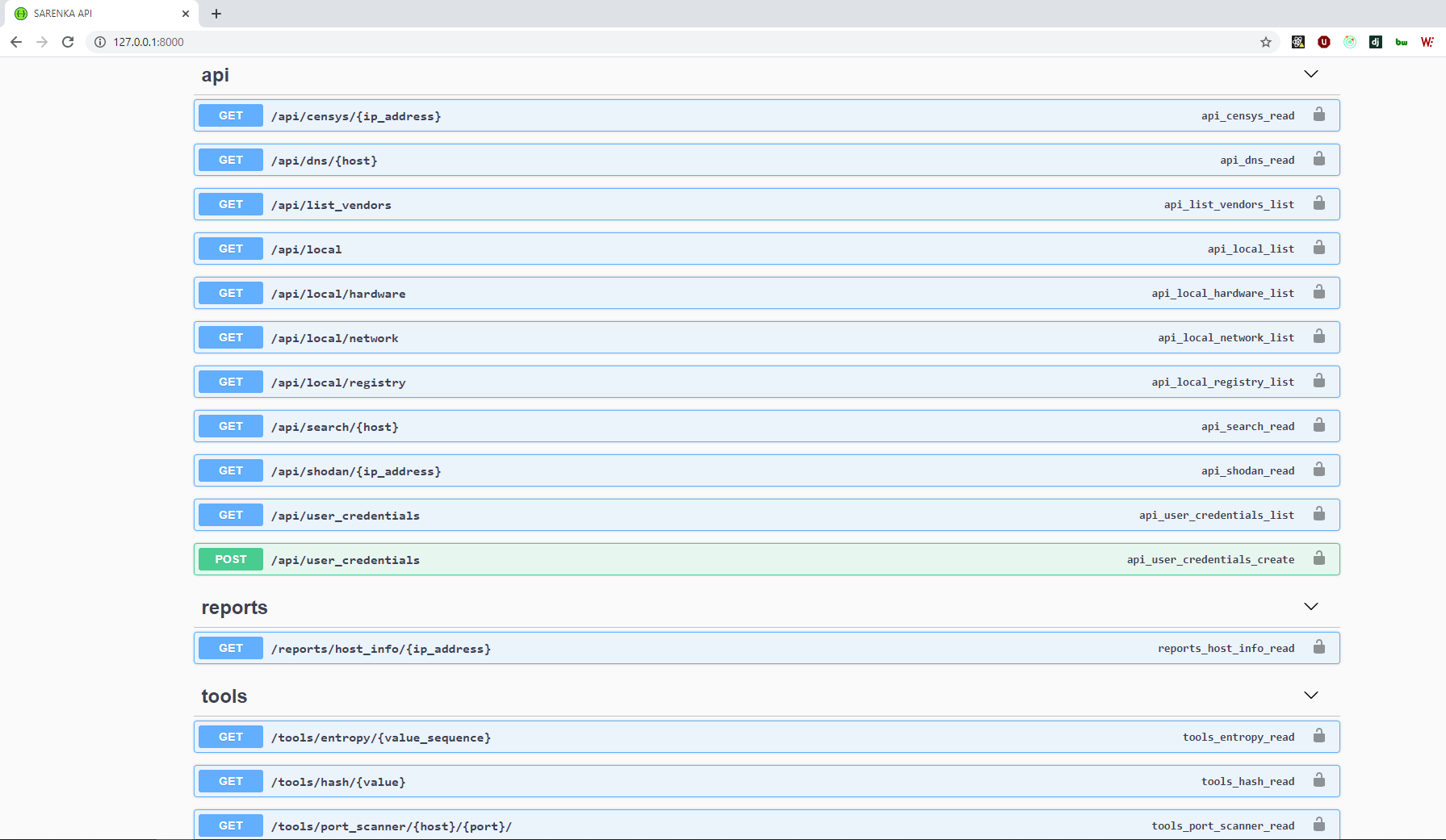
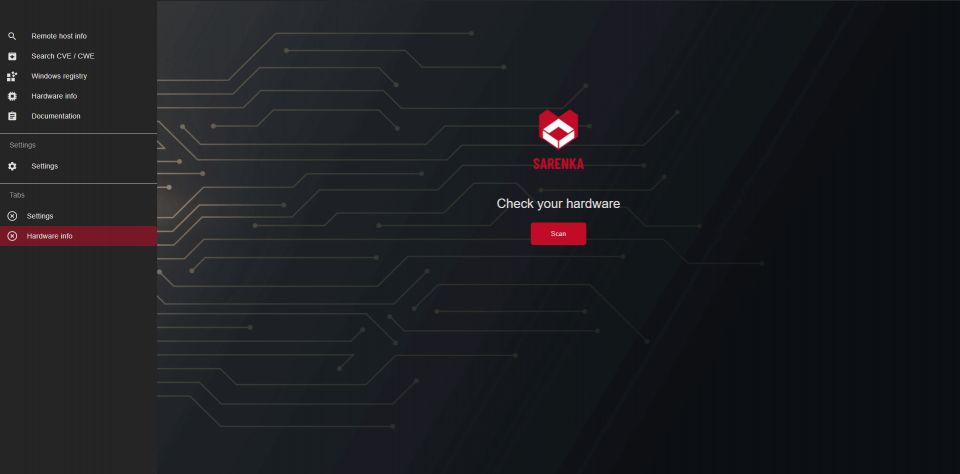
SARENKA is an Open Source Intelligence (OSINT) tool which helps you obtaining and understanding Attack Surface.
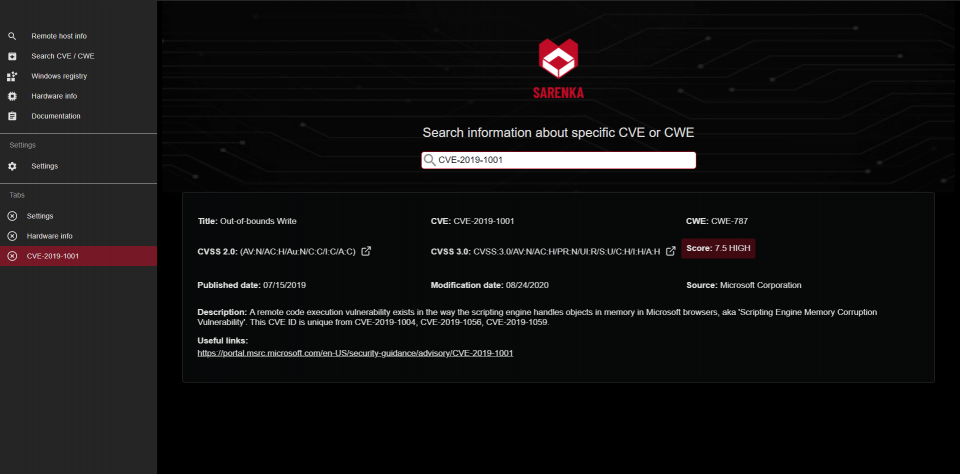
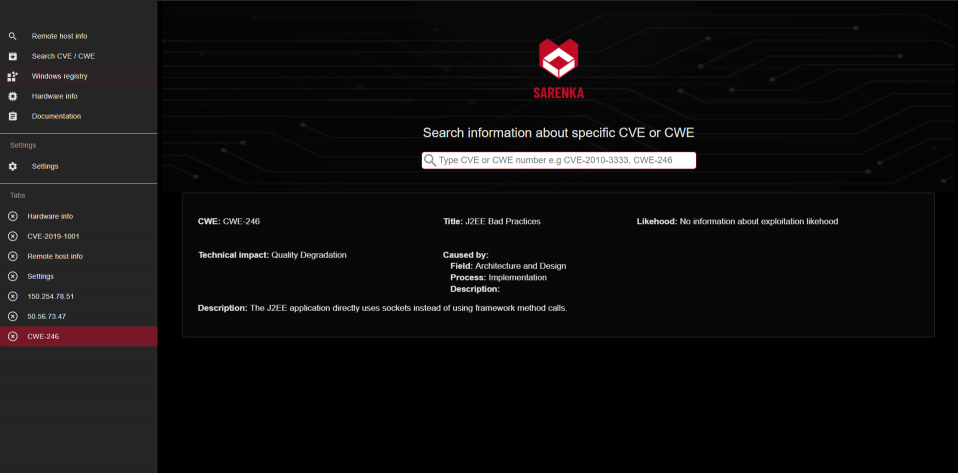
The main goal is gathering information from search engines for Internet-connected devices (https://censys.io/, https://www.shodan.io/). It scraps data about Common Vulnerabilities and Exposures (CVE), Common Weakness Enumeration (CWE) and also has database where CVEs are mapped to CWE.
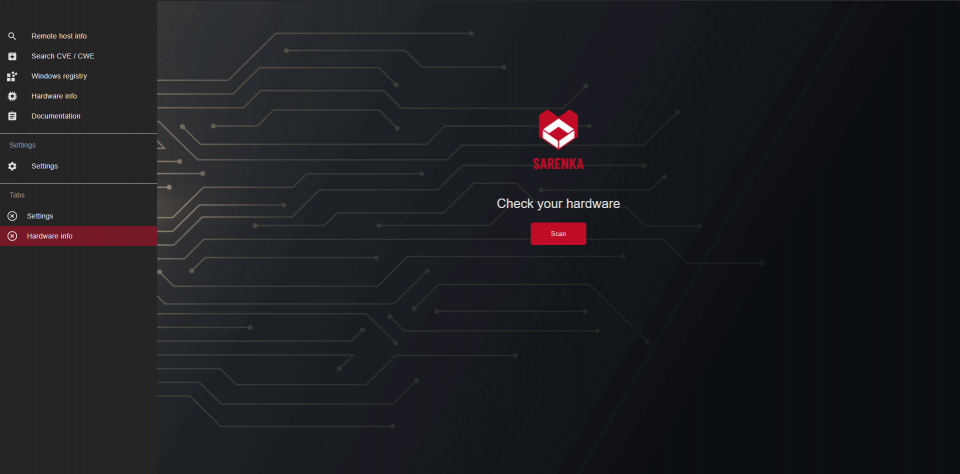
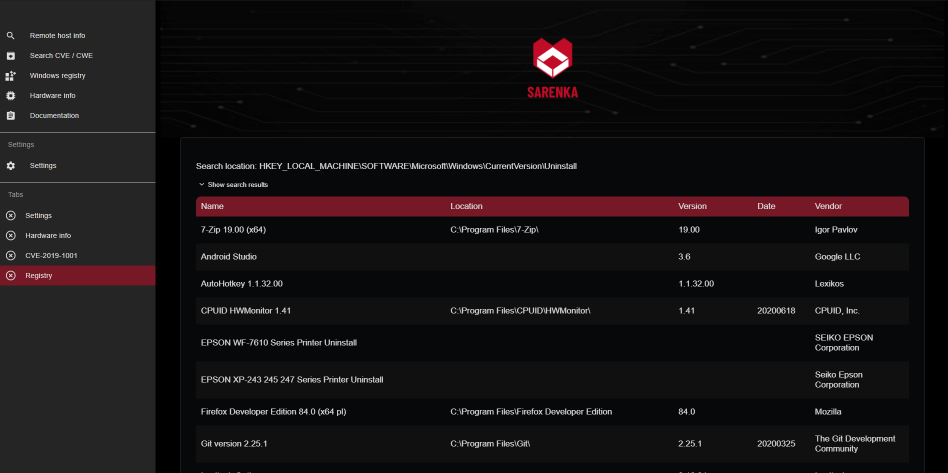
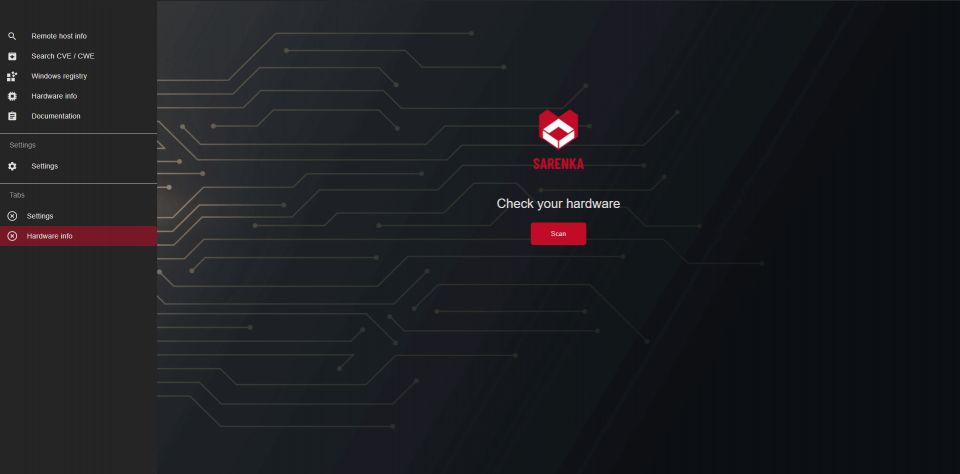
It returns data about the local machine - local installed software (from Windows Registry), local network information (python libraries, popular cmd commads).
For now application has also simple tools like hash calculator, shannon entropy calculator and very simple port scanner. More cryptography-math tools and reconnaissance scripts are planned.
App is alive and has been rewriting from scratch on branch new_master.
SARENKA was mentioned here:
- ncybersec
- llllap3xllll
- securityonline.info
- haxf4rall.com
- hackdig.com
- findglocal.com
- 台灣數位國土安全部 - DDHS
- laptrinhx.com
- kitploit.com
- attackware.com
- hacking.land
- cyberfishnews.com
- modernnetsec.io
- spywarenews.com
- cert.europa.eu
- dfir.pro
- iransec.net
- hacker-gadgets.com
- vulners.com
- redpacketsecurity.com
- kali-linuxtr.net
- anonymousmedia.org
- pentesttools.net
- wangshit.xyz
- geekychild.com
- hacker.observer
- nuomiphp.com
- danielonsecurity.com
- haktechs
- cybeseclabs.com
- vk.com
- hacking.reviews
- thehacker.co
- iguru.gr
- en.iguru.gr
- rucore.net
- hackerzzz.com
- my.oschina.net
- kalilinuxtutorials.com
- pintait.com
- osintbrasil.blogspot.com
- gets data from https://censys.io/ by ip
- get data from https://www.shodan.io/ by ip
- get DNS data
- get WHOIS data
- banner grabbing
- find CVEs by CWE
- generatre pdf report
You can also:
- calculate hashes based on user string
- calculate shannon entropy based on user string
- check is port open|closed (instead always use nmap if you can - it is slow)
Team tests application on Windows 10 and Kali Linux with Python 3.8.
SARENKA requires:
Clone repository
$ git clone https://github.com/pawlaczyk/sarenka.git
Go to application directory
Create venv
Activate venv
Powershell
$ ./env/Scripts/Activate.ps1
cmd
$ ./env/Scripts/activate.bat
Install requirements
$ pip3 install -r ./requirements.txt
Build application with sarenka.py script
$ python ./sarenka/sarenka.py
####Please create accounts on services:
Application - default http://localhost:8000/
# go to sarenka/sarenka
$ python backend/manage.py runserver
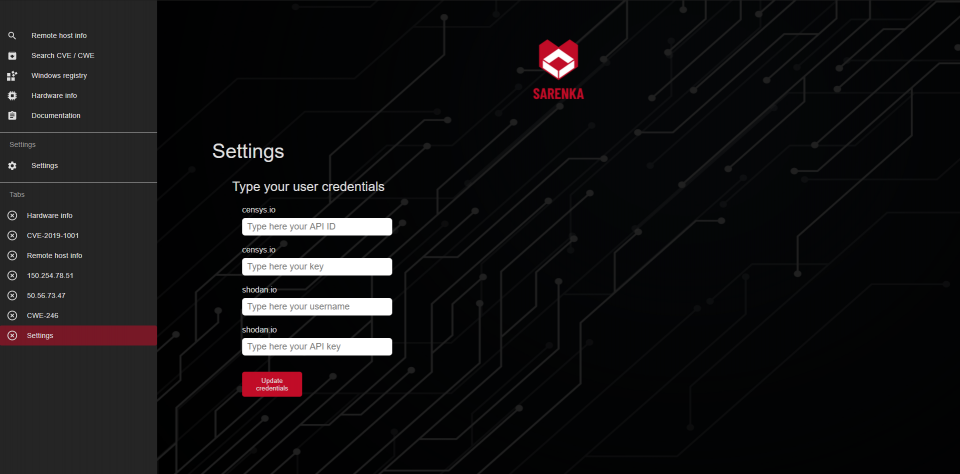
#####Add user credentials at "Settings"
Suggestions are welcome
Databases
Details in documentation.
Tech
And of course SARENKA itself is open source with a public repository on GitHub.
Planned features
- Rewrite documentation in English (end of 2021)
- trello/ github instead of Jira
- Cover 100% code by tests
- typing backend
- document all functions and class
- Docker
- online demo
- Jenkins
- GraphQL
- Selenium Scrapers
- More pentesting tools
- Google Dorks
- Abstract Algebra calculator
- Number Theory calculator
- Server certificate validator
- tests on Linux
- NLP
- d3js visualizations
- alterntive pure version in command lineS
CI/CD Tools
Tested manually
- Kali Linux kali-rolling 2020.2; Python 3.8.2
- Windows 10; Python 3.8.5
Documentation
Till end of March, 2021 documentation will be available only in Polish! The documentation is availabe here.
Contact
SARENKA is licensed under the MIT License.
Original repository: https://github.com/pawlaczyk/sarenka
如有侵权请联系:admin#unsafe.sh